In this episode of the M365 FM Podcast, the traditional role of the Microsoft 365 admin is challenged. Instead of acting as gatekeepers who manually approve, control, and fix everything, admins must shift toward designing automated systems that govern access, lifecycle, and security at scale. The episode argues that manual control does not scale in modern cloud environments and often creates bottlenecks, risk, and hidden dependencies.
The “death of the admin” isn’t about losing relevance—it’s about evolving into an architect of policies, automation, and guardrails that enable the business to move faster without constant intervention.
Broken workflows in your Power Platform environment can disrupt operations and expose your organization to risk. As you embrace Microsoft 365 and SaaS platforms, you see IT roles shifting from manual oversight toward architecting automated governance solutions, particularly in the realm of Power Platform Governance. Automated guardrails now help you enforce compliance and security while improving efficiency. The M365FM Podcast explores these changes, showing how modern approaches to governance protect your business and enable faster innovation.
| Aspect | Manual Governance | Tool-Based Governance |
|---|---|---|
| SaaS Visibility | Fragmented data in spreadsheets | Centralized live visibility |
| SaaS Compliance | High risk with manual audits | Automated checks, audit-ready |
| SaaS User Automation | Slow and prone to errors | Automated provisioning/deprovisioning |
| SaaS Cost Control | Reactive and limited | Proactive and data-driven |
| Scalability | Not feasible | Highly scalable |
Key Takeaways
- Establish a strong governance model to manage risks and ensure compliance in your Power Platform environment.
- Build a dedicated team, like a Center of Excellence, to oversee governance efforts and bridge IT with business units.
- Assign clear roles and responsibilities to team members to enhance accountability and streamline workflow management.
- Implement strong governance policies to protect data and ensure compliance with regulations like GDPR and HIPAA.
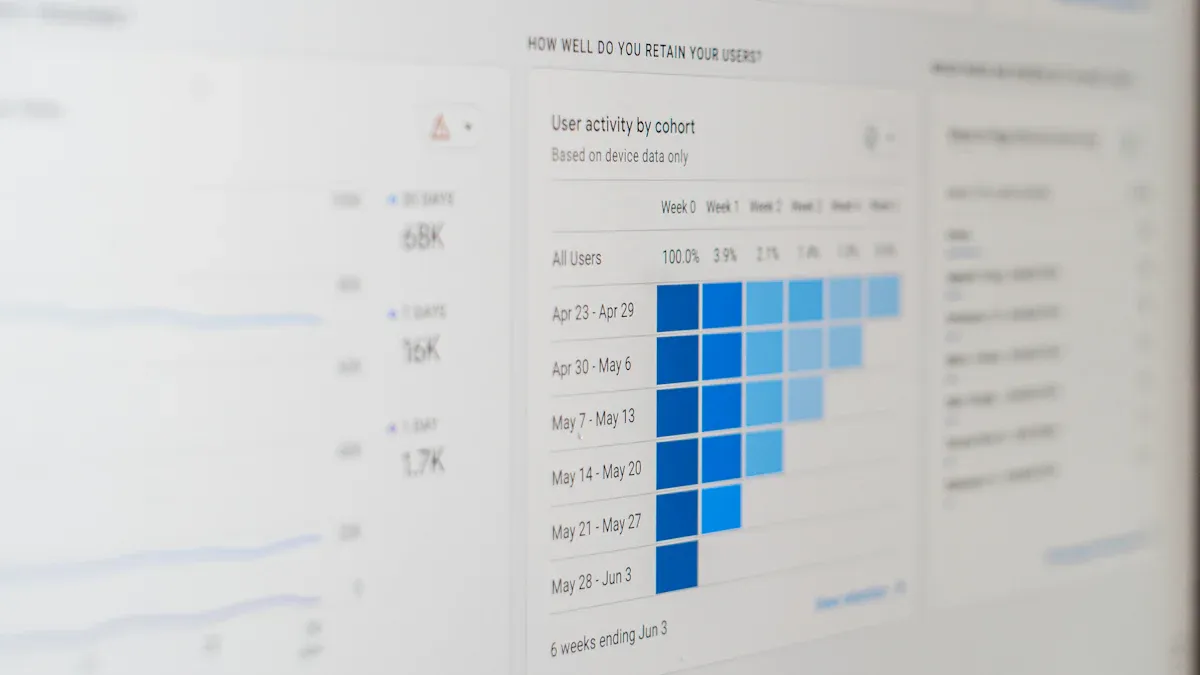
- Use monitoring tools and analytics to track workflow performance and quickly address any issues that arise.
- Set up failure notifications to alert you immediately when workflows encounter problems, allowing for rapid response.
- Regularly review and retire unused workflows to keep your environment organized and reduce security risks.
- Encourage continuous improvement by gathering user feedback and providing ongoing training to keep everyone informed.
Define Your Power Platform Governance Model
A strong power platform governance model sets the foundation for success with low-code tools like Power Apps and Power Automate. You need a clear structure to manage risk, support compliance, and keep your organization secure. The M365FM Podcast highlights the shift from manual to automated governance, showing how a well-defined framework helps you scale power platform management without losing control.
A governance model gives you a roadmap. It helps you decide who does what, how you protect data, and how you keep your apps running smoothly.
Establish Team Structure
You should start by building a team that can guide your governance efforts. Many organizations use a Power Platform Center of Excellence (CoE). This team acts as a bridge between IT and business units. It helps you deliver value quickly while protecting your assets.
| Role | Description |
|---|---|
| CoE Leadership | Oversees the CoE and its initiatives. |
| Governance Architect | Designs governance frameworks and policies. |
| Security Specialist | Ensures compliance and security measures are in place. |
| Training Coordinator | Manages training programs for users and makers. |
| Community Manager | Fosters community engagement and support among users. |
Assign Roles and Responsibilities
Assign clear roles to each team member. The Governance Architect creates policies. The Security Specialist checks that your apps follow security rules. The Training Coordinator helps users learn best practices. The Community Manager supports users and encourages safe innovation. Larger organizations may need more roles, but every team should cover these basics.
Enable Knowledge Transfer
You should make knowledge sharing a priority. Hold regular meetings to discuss new risks and lessons learned. Create guides and templates for app makers. This helps everyone follow the same standards and reduces the chance of mistakes.
Set Governance Policies
You need strong policies to protect your data and meet compliance needs. These policies cover areas like data residency, regulatory requirements, ethical AI, user authentication, and data protection practices.
| Compliance Area | Key Considerations |
|---|---|
| Data Residency | Know where your data lives and if it meets legal rules. |
| Regulatory Requirements | Follow laws like GDPR, HIPAA, and CCPA. |
| Ethical Considerations | Use responsible AI in your workflows. |
| User Authentication | Use secure sign-in methods for all users. |
| Data Protection Practices | Encrypt sensitive data and use role-based access. |
- Use tools like Microsoft Purview DLP to classify and protect data in your apps. Entra ID helps you manage identities and control access. These tools make it easier to enforce policies and reduce manual work.
- Separate environments for development, testing, and production. This lowers the risk of accidental changes and keeps your data safe.
- Integrate Azure Active Directory for identity management. This adds another layer of security and helps you control who can access each app.
A clear governance framework reduces the risk of data breaches and operational problems. It also helps you respond quickly to new threats. By using automated tools and a strong team, you can keep your power platform governance strong and future-ready.
Strengthen Workflow Ownership and Accountability
You need strong ownership and accountability to keep your critical workflow running smoothly in your power platform governance framework. When you assign clear owners to each app and flow, you reduce risk and make your governance model more effective. Owners take responsibility for monitoring, maintaining, and updating workflows. This approach helps you avoid disruptions and ensures your low-code solutions stay reliable.
Assign Workflow Owners
You should assign a dedicated owner for every power automate flow and power apps solution. Owners act as the main point of contact for each app. They track performance, respond to issues, and make sure workflows follow security and compliance standards. When you use Service Principal Names (SPNs) or similar accounts, you gain several advantages:
- Consistency and stability: Workflows keep running even if employees leave or change roles.
- Enhanced security: Owners can set strict permission controls and limit unauthorized actions.
- Scalability: You manage automated tasks across large environments with ease.
- Compliance: You create a clear audit trail for every action taken by the flow.
- Reduced disruptions: Flows are less likely to break due to user account changes.
- Centralized management: You maintain and audit security policies more efficiently.
Tip: Document each owner in your governance framework. Keep a list of owners and their responsibilities. This practice helps you respond quickly to risks and keeps your workflows healthy.
Set Escalation Paths
You need a clear escalation path for every critical workflow. If a workflow fails or faces a risk, the owner must know who to contact for help. Escalation paths outline the steps to follow when issues arise. You can use a simple table to track escalation contacts:
| Workflow Name | Owner | Escalation Contact | Response Time |
|---|---|---|---|
| HR Onboarding Flow | Jane Smith | IT Support Lead | 2 hours |
| Finance Approval | Mark Lee | Compliance Team | 4 hours |
This table helps you manage incidents and reduces downtime. Owners know their responsibilities and can act fast to protect your app and data. You build trust in your governance model by making escalation paths visible and easy to follow.
Strong ownership and clear escalation paths form the backbone of effective power platform governance. You minimize risks, improve security, and keep your low-code workflows running without interruption.
Monitor and Alert for Workflow Health
Keeping your workflows healthy is a key part of power platform governance. You need to know when something goes wrong so you can fix it fast. Monitoring and alerting help you spot problems early and keep your low-code solutions running smoothly. This approach also supports compliance and security by making sure you catch issues before they grow.
Use Analytics and Reporting
You can use analytics and reporting tools in Power Platform to track how your workflows perform. Power Automate gives you run histories, error rates, and usage data. These features help you see which flows work well and which ones need attention. You can also build custom dashboards to focus on the most important metrics for your team.
- Run History: Track which flows succeed and which fail. This helps you spot patterns and fix problems.
- Usage and Performance Metrics: See how often each app runs. This shows you which solutions are most important.
- Error Analysis: Watch for high failure rates. This lets you act before small issues become big ones.
- Customizable Dashboards: Build views that highlight key performance indicators for your workflows.
- Historical Trends: Use Power BI to see long-term patterns. This helps you plan resources and improve reliability.
The analytics and reporting features in Power Platform let you monitor workflow performance, analyze errors, and create dashboards. These tools help you find and fix issues quickly, making your power apps and flows more reliable.
You can also use several monitoring tools to get a full picture of your app health:
| Monitoring Tool | Effectiveness |
|---|---|
| Power Automate Logs | Provides execution details but lacks security context for threat detection. |
| Azure Activity Logs | Captures administrative changes and is essential for compliance and security monitoring. |
| Office 365 Audit Logs | Tracks connector usage and data access patterns, crucial for understanding workflow interactions. |
| Centralized Logging | Enables correlation of logs for comprehensive visibility, essential for incident response and compliance. |
| Baseline Monitoring | Focuses on deviations from normal operations, allowing for proactive identification of potential issues. |
| 24/7 Monitoring | Ensures continuous oversight, as demonstrated by a regional bank achieving zero findings in security reviews. |
Using these tools, you gain better visibility into your workflows and can respond to issues faster.
Set Up Failure Notifications
Setting up failure notifications is a smart way to keep your workflows healthy. Real-time alerts tell you right away when something breaks. This means you can fix problems before they affect users or business processes.
- Real-time awareness keeps you informed about flow issues as soon as they happen.
- Faster response times let you solve problems from anywhere, even if you are not at your desk.
- Proactive maintenance becomes easier because you can track failure patterns and prevent future issues.
You should set up notifications for all critical flows and apps. Use email, Teams messages, or mobile alerts to reach the right people. Make sure each alert includes enough detail so you can act quickly. When you combine monitoring with real-time notifications, you build a strong governance model that protects your business and supports innovation.
Tip: Review your notification settings often. Make sure alerts go to the right owners and escalation contacts. This keeps your response plan up to date and effective.
Enforce Compliance and Security Controls
You must build strong compliance and security controls into your Power Platform governance framework. These controls help you protect sensitive data, reduce risk, and keep your organization in line with regulations. By using the right tools and training, you can prevent common risks and keep your app environment safe.
Apply DLP Policies
Data loss prevention is a key part of any governance strategy. DLP policies in Power Platform work differently from traditional methods. Instead of scanning content after it is created, these policies control which connectors can interact with certain data types. This approach stops risky integrations before they can process regulated data.
DLP policies in Power Platform function differently than traditional DLP — they control which connectors can interact with specific data types rather than scanning content after creation. This prevention-first approach stops risky integrations before they process regulated data.
You can use DLP policies to:
- Control data flow and restrict high-risk connectors, which is crucial for preventing data breaches.
- Safeguard sensitive information and ensure compliance with regulations.
- Segment environments, monitor continuously, and update policies to adapt to new threats.
To set up DLP policies, follow these steps:
- Access the Power Platform Admin Center.
- Go to the Data Policies section to define and enforce rules.
- Create granular policies to block high-risk connectors in sensitive environments.
A strong DLP strategy acts as a guardrail for your app environment. It helps you protect data and meet compliance standards.
Address Security and Compliance Risks
You face many security and compliance risks in Power Platform workflows. These risks can lead to data leaks or unauthorized access if you do not address them.
- Hardcoded secrets within scripts.
- Insecure connectors or shared drives.
- Third-party package vulnerabilities, such as CVE-2023-36019.
- Potential for automation misuse for malicious purposes.
- Lack of visibility and governance in low-code environments.
Best practices for addressing these risks include:
- Implement data loss prevention policies to control data flow and prevent sharing with untrusted services.
- Use role-based access control to assign permissions based on user roles.
- Regularly review and update permissions and sharing settings in Power Apps.
- Enable logging and monitoring to detect suspicious activities and app usage anomalies.
You should also control data connectors, leverage DLP policies, and limit sharing and permissions. These steps help you reduce risk and keep your governance model strong.
Educate Users on Compliance
User education is essential for effective governance and management. When users understand compliance requirements, they make safer choices and help protect your organization.
| Training Method | Description |
|---|---|
| Blended Learning | Combines self-paced, instructor-led, and in-product training for effective learning. |
| In-Product Training | Uses guided walkthroughs and contextual prompts to enhance practical skill acquisition. |
| Governance Framework Training | Focuses on designing and implementing governance frameworks, including DLP policies and security models. |
| Digital Adoption and In-Context Learning | Provides guidance within the app to support just-in-time learning and reduce dependency on support teams. |
You can use blended learning, in-product training, and digital adoption tools to teach users about compliance. Governance framework training helps users understand policies and security models. These methods make it easier for everyone to follow best practices and reduce risks.
By enforcing compliance and security controls, you protect your data, reduce risk, and support a healthy Power Platform environment.
Standardize Workflow Design and Documentation
You can prevent many workflow errors by standardizing how you design and document your Power Platform solutions. When you use clear naming conventions and keep all documentation in one place, you make it easier for everyone to understand, maintain, and improve your apps.
Use Naming Conventions
Naming conventions help you and your team quickly identify the purpose and function of each app, flow, or component. Microsoft recommends using a consistent pattern for names. This practice brings clarity and reduces confusion, especially as your environment grows.
| Naming Convention Type | Example | Description |
|---|---|---|
| Canvas Apps | CA_HR_LeaveRequest | Canvas app for HR leave requests |
| Model-Driven Apps | MD_Sales_OpportunityMgmt | Model-driven app for sales opportunities |
| Flow Names | Send_Report_Email_Scheduled | Scheduled flow that sends report emails |
| Actions and Triggers | Get_Items_From_SharePoint | Action that gets items from SharePoint |
| Variables | v_TotalAmount | Variable for total amount |
Tip: Use prefixes like "CA" for Canvas Apps or "MD" for Model-Driven Apps. This helps you spot the type of solution at a glance.
Naming conventions offer several benefits:
- They provide clarity by making each name show its purpose.
- They create consistency, which helps you manage many components.
- They add context, so you can identify details quickly.
- They support scalability as your organization grows.
- They help you avoid special characters that might cause errors.
When you follow these patterns, you reduce mistakes and make updates easier. You also help new team members learn faster because they can understand what each part does without extra help.
Maintain Centralized Documentation
Centralized documentation acts as a single source of truth for your workflows. You can use an Automation Center or a shared repository to store all details about your apps, flows, and processes. This approach improves power platform management and strengthens governance.
A centralized system gives you:
- Easy access to workflow designs, owners, and change history.
- Real-time monitoring of workflow status and performance.
- Error tracking and quick troubleshooting with direct links to resources.
You also protect your organization from disruptions. When you document ownership with stable, non-human accounts, you avoid problems if someone leaves the company. This practice keeps your workflows running smoothly and reduces downtime.
Centralized documentation transforms your process from reactive to proactive. You can spot issues before they grow and keep your operations resilient. It also helps you onboard new team members. They can review the documentation and understand workflows without long training sessions.
Note: Good documentation and naming standards make your workflows easier to manage, update, and scale. You build a foundation for reliable, error-free automation.
By standardizing workflow design and documentation, you create a clear map for your team. You make troubleshooting faster, reduce errors, and ensure your Power Platform solutions stay healthy as your business evolves.
Manage Workflow Lifecycle and Change
You need to manage the entire lifecycle of your Power Platform workflows to keep your environment secure and efficient. This process includes controlling changes, tracking every update, and removing workflows that no longer serve your business. By following a structured approach, you reduce errors and keep your organization compliant.
Approval and Change Control
You should always use a structured approval process before making changes to any workflow. This step ensures that only the correct versions of documents or processes are published. When you require approvals, you prevent duplicate versions and confusion about which workflow is current. You also create a clear record of who approved each change and when. This is especially important in regulated industries, where compliance is a must.
A typical workflow lifecycle in Power Platform includes these stages:
- Select Workflow as the process category.
- Define triggers for when the workflow should start, such as create, update, or delete.
- Set the scope to decide which records the workflow will affect.
- Choose the execution type, either real-time or background.
- Add workflow steps, like updating fields or sending emails.
- Activate the process so it can run.
By following these steps and using approval controls, you make sure every change is reviewed and documented. This approach supports operational efficiency and reduces the risk of mistakes.
Audit Trails and Versioning
You need to keep a complete history of all changes to your workflows. Audit trails provide a record of what changed, when, and who made the change. This helps you meet compliance requirements and makes it easy to track down issues. Version control keeps a chronological history of every modification. You can see which version is active and who authorized it.
- Audit trails help you stay compliant with regulations.
- Version control documents every change for easy review.
- Integrated approvals and versioning ensure only the most current and validated workflows are in use.
When you use audit trails and versioning, you build accountability into your workflow management. You can quickly answer questions about changes and prove compliance during audits.
Retire Unused Workflows
You should regularly review your workflows and retire those that are no longer needed. Start by auditing workflow ownership to confirm each workflow has a responsible person. Monitor usage patterns to spot workflows that have not been used in a long time. Classify each app as Active, Archived, or Marked for Deletion based on its usage.
| Criteria | Description |
|---|---|
| Ownership Audits | Check who owns each workflow and confirm it is still needed. |
| Usage Monitoring | Track how often each workflow runs and who uses it. |
| App Categorization | Label workflows as Active, Archived, or Marked for Deletion. |
| Archival Triggers | Set rules for archiving or deleting workflows, such as no use in 90 days. |
By retiring unused workflows, you reduce clutter and lower security risks. You also make it easier to manage your environment and keep your governance model strong.
Tip: Schedule regular reviews to keep your workflow inventory up to date. This practice helps you avoid unnecessary costs and keeps your Power Platform environment healthy.
Enhance Visibility and Access Management
You need strong visibility and access management to keep your Power Platform secure and efficient. As your organization grows, you must see who can use each app and control how they use it. This helps you scale safely and avoid risks like Shadow IT or Shadow AI.
Recent trends show that organizations focus on centralized management and enhanced security. You want to see all your digital assets in one place. You also need tools that help you manage innovation and productivity while reducing risk. Centralized management lets you track every app and flow, see who owns them, and spot any orphaned resources. This approach helps you control costs and avoid data exposure.
Audit Permissions
You should audit permissions often to prevent unauthorized access. Regular audits help you find weak spots in your security. You can use tools like Microsoft Sentinel to track what users do and spot any suspicious actions. Role-based access control (RBAC) is a smart way to limit what each user can do. This means users only get the permissions they need, which lowers the chance of mistakes or misuse.
Here are some key steps for auditing permissions:
- Review who has access to each app and flow.
- Remove permissions from users who no longer need them.
- Use RBAC to set the right level of access for each role.
- Monitor user activity for signs of unusual behavior.
Tip: Schedule permission audits every quarter. This keeps your environment safe and up to date.
Segment Environments
Segmenting environments makes your Power Platform easier to manage and more secure. You can create separate spaces for development, testing, and production. This helps you keep sensitive data safe and supports compliance. When you separate environments, you reduce errors in business-critical apps. You also make it easier for teams to innovate in less restrictive settings.
Benefits of segmenting environments include:
- Clear navigation for users and admins.
- Fewer mistakes in important apps.
- Better protection for sensitive data.
- Support for compliance with rules and laws.
- Improved operational efficiency with analytics on app usage.
You should label each environment clearly and set rules for what can happen in each one. For example, only allow real customer data in production. Use analytics to track how each environment performs and make changes as needed.
By focusing on visibility and access management, you build a strong foundation for Power Platform governance. Automated guardrails help you scale without adding manual work. You reduce the risk of Shadow IT and keep your organization secure.
Foster Continuous Improvement in Governance
Continuous improvement keeps your Power Platform governance strong and adaptable. You build a culture that values learning, feedback, and regular review. This approach helps you respond to new challenges and maintain high standards for your app environment.
Encourage Feedback
You should invite feedback from users and stakeholders. Their input reveals how well your governance model works and where you can make it better. When you listen to users, you discover what makes them satisfied and what frustrates them. You also find gaps in your processes and learn how to balance control with flexibility. This balance encourages more people to use your app solutions and follow governance rules.
- User feedback provides insights into satisfaction levels.
- Identifies areas needing improvement in governance processes.
- Helps governance teams balance control and flexibility, enhancing user adoption.
Tip: Set up regular surveys or feedback sessions. Use the results to adjust your governance policies and improve user experience.
Schedule Governance Reviews
You need to schedule governance reviews to keep your framework current. Reviews help you spot risks, measure progress, and update policies. You can use key performance indicators (KPIs) to track how well your governance model works. These KPIs show if your app solutions deliver value and if your team manages resources efficiently.
| KPI | Description |
|---|---|
| Adoption Rate | Measures user engagement with the platform, indicating governance effectiveness. |
| Policy Compliance Rate | Reflects adherence to governance rules, showing alignment between policies and user practices. |
| Environment Utilization | Assesses the efficiency of resource management within the governance model. |
| Security Role Accuracy | Evaluates the correctness of user role assignments, impacting data security and user confidence. |
| Solution Lifecycle Management | Ensures solutions are sustainable and managed throughout their lifecycle, preventing technical debt. |
| Orphaned Resources | Tracks resources without active ownership, indicating gaps in governance processes. |
| Business Value Realization | Measures the actual value generated by solutions, linking governance to organizational goals. |
| Support & Incident Volume | Analyzes governance-related support requests to gauge user experience and governance clarity. |
| Innovation vs. Shadow IT Ratio | Balances controlled innovation with oversight, indicating governance effectiveness. |
| User Satisfaction & Feedback | Provides qualitative insights into user perceptions of governance, essential for continuous improvement. |
Note: Use these KPIs during reviews to guide your decisions and keep your governance model aligned with business goals.
Provide Ongoing Training
You should offer ongoing training to keep everyone up to date with governance best practices. Training helps users and administrators learn new skills and understand changes in the platform. You can use different methods to make learning effective and engaging.
| Training Method | Purpose |
|---|---|
| Instructor-led workshops | In-depth exploration of complex technical topics |
| Self-paced modules | Flexible learning and foundational skills |
| Hands-on sandbox labs | Experimentation without production risks |
| Hackathons and innovation days | Encouragement of creativity and practical application |
| Digital adoption platforms | Ongoing contextual guidance during daily use |
| Continuous learning resources | Keeping skills current and aligned with business objectives |
You build confidence and reduce errors when you invest in training. Users learn how to create and manage app solutions safely. Administrators stay informed about new governance tools and policies.
Tip: Make training a regular part of your governance plan. Update materials often to reflect new features and best practices.
Continuous improvement helps you keep your Power Platform governance strong. You create a resilient environment where your app solutions deliver value and your team stays ready for change.
You can build a resilient Power Platform environment by adopting a modern governance model. These seven tips help you prevent broken workflows, strengthen compliance, and improve security. Use automated guardrails and clear policies to scale with confidence. Listen to the M365FM Podcast for expert insights and explore Microsoft tools like Purview DLP and Entra ID. Stay proactive and adapt your strategy as technology and business needs change. Your organization will stay secure and ready for the future.
FAQ
What is Power Platform governance?
Power Platform governance is a set of rules and processes. You use it to manage, secure, and monitor apps, flows, and data. Good governance helps you reduce risks and keep your environment compliant.
Why do workflows break in Power Platform?
Workflows break for many reasons. Common causes include missing owners, expired credentials, permission changes, or unapproved updates. You can prevent most issues with strong governance and regular monitoring.
How often should you review your workflows?
You should review workflows at least every quarter. Regular reviews help you find unused or risky workflows. This keeps your environment secure and efficient.
Which Microsoft tools help automate governance?
You can use Microsoft Purview DLP for data protection and Entra ID for identity management. These tools help you automate policy enforcement and access control.
How do you handle orphaned workflows?
You should audit ownership often. If you find an orphaned workflow, assign a new owner or retire it. This keeps your environment organized and reduces risk.
What is Shadow IT and why is it risky?
Shadow IT happens when users create apps or flows outside approved processes. This can lead to data leaks or compliance issues. You reduce this risk with clear policies and automated guardrails.
How can you educate users about governance?
You can use blended learning, in-product guides, and regular training sessions. These methods help users understand policies and follow best practices.
What is the role of a Center of Excellence (CoE)?
A CoE leads governance efforts. The team sets standards, trains users, and supports innovation. You build a strong governance culture with a CoE.
🚀 Want to be part of m365.fm?
Then stop just listening… and start showing up.
👉 Connect with me on LinkedIn and let’s make something happen:
- 🎙️ Be a podcast guest and share your story
- 🎧 Host your own episode (yes, seriously)
- 💡 Pitch topics the community actually wants to hear
- 🌍 Build your personal brand in the Microsoft 365 space
This isn’t just a podcast — it’s a platform for people who take action.
🔥 Most people wait. The best ones don’t.
👉 Connect with me on LinkedIn and send me a message:
"I want in"
Let’s build something awesome 👊
1
00:00:00,000 --> 00:00:03,540
you think you're digitally transforming your business, but in reality, you're actually
2
00:00:03,540 --> 00:00:05,120
industrializing chaos.
3
00:00:05,120 --> 00:00:08,960
Most organizations today are wrapping broken manual workflows in shiny power, automate
4
00:00:08,960 --> 00:00:13,080
flows and calling it progress, but speeding up a flawed process doesn't actually fix
5
00:00:13,080 --> 00:00:14,080
the problem.
6
00:00:14,080 --> 00:00:15,520
It just compounds your organizational debt.
7
00:00:15,520 --> 00:00:17,440
This is the 24 month cliff.
8
00:00:17,440 --> 00:00:18,600
Technical debt costs don't just grow.
9
00:00:18,600 --> 00:00:21,160
They triple every two years if you leave them unmanaged.
10
00:00:21,160 --> 00:00:24,480
We're moving from manageable human error to high speed systemic failure.
11
00:00:24,480 --> 00:00:28,040
In the next 20 minutes, I'm showing you the framework to stop scaling in efficiency
12
00:00:28,040 --> 00:00:30,160
and start building structural integrity.
13
00:00:30,160 --> 00:00:34,840
If you want more deep dives into Microsoft's strategy, subscribe to the M365FM podcast.
14
00:00:34,840 --> 00:00:38,080
Let's get into why your automation might be a ticking time bomb.
15
00:00:38,080 --> 00:00:39,360
The mirage of speed.
16
00:00:39,360 --> 00:00:42,760
The fundamental flow in how we approach the power platform is something I call creation
17
00:00:42,760 --> 00:00:43,760
bias.
18
00:00:43,760 --> 00:00:47,800
It's the tendency to prioritize the speed of building a solution over the long term stability
19
00:00:47,800 --> 00:00:48,880
of the outcome.
20
00:00:48,880 --> 00:00:53,440
We celebrate the maker who spins up a flow in an afternoon, but we rarely audit the structural
21
00:00:53,440 --> 00:00:56,000
rot they've just introduced into the tenant.
22
00:00:56,000 --> 00:00:58,480
Social code makes it too easy to digitize a mess.
23
00:00:58,480 --> 00:01:01,440
It leads to what I call the model of unintended consequences.
24
00:01:01,440 --> 00:01:06,120
We mistake faster execution for process improvement, but a fast bad process is just an expensive
25
00:01:06,120 --> 00:01:07,120
liability.
26
00:01:07,120 --> 00:01:09,160
Think about how a typical workflow evolves.
27
00:01:09,160 --> 00:01:11,600
You have a manual process that's a bit clunky.
28
00:01:11,600 --> 00:01:14,840
Maybe it involves three spreadsheets and a lot of back and forth email.
29
00:01:14,840 --> 00:01:18,000
Instead of looking at why those spreadsheets exist, you build a flow to move the data
30
00:01:18,000 --> 00:01:19,000
between them faster.
31
00:01:19,000 --> 00:01:20,520
You've just paved the cow path.
32
00:01:20,520 --> 00:01:21,680
You haven't improved the work.
33
00:01:21,680 --> 00:01:23,920
You've just made the mess invisible to the naked eye.
34
00:01:23,920 --> 00:01:25,560
This is the cost of the mess.
35
00:01:25,560 --> 00:01:29,820
Social workarounds and shadow spreadsheets survive inside your automation, creating quiet
36
00:01:29,820 --> 00:01:32,600
cost centers that drain your team's time.
37
00:01:32,600 --> 00:01:36,360
The reality is that citizen development without guardrails isn't empowerment.
38
00:01:36,360 --> 00:01:40,840
It's actually just distributing risk across your entire Microsoft 365 tenant.
39
00:01:40,840 --> 00:01:45,040
Every unmanaged flow is a potential point of failure that IT doesn't see until it's too
40
00:01:45,040 --> 00:01:46,040
late.
41
00:01:46,040 --> 00:01:48,120
We see this in the paradox of the 19%.
42
00:01:48,120 --> 00:01:52,240
Statistics show that most IT budgets only have about 19% left for actual innovation.
43
00:01:52,240 --> 00:01:54,120
The rest is swallowed by maintenance.
44
00:01:54,120 --> 00:01:58,000
If the tax you pay for legacy debt, if you don't refactor your processes before you automate
45
00:01:58,000 --> 00:02:01,200
them, you are simply signing up for a higher tax rate next year.
46
00:02:01,200 --> 00:02:03,960
We've built hierarchies for a world that no longer exists.
47
00:02:03,960 --> 00:02:05,880
We used to have time to find information.
48
00:02:05,880 --> 00:02:07,280
Now work starts with context.
49
00:02:07,280 --> 00:02:10,000
If your automation doesn't provide that context, it's just noise.
50
00:02:10,000 --> 00:02:13,600
You publish the content and then nobody uses it or worse.
51
00:02:13,600 --> 00:02:14,600
They use it.
52
00:02:14,600 --> 00:02:17,200
And it breaks in a way that creates a data integrity nightmare.
53
00:02:17,200 --> 00:02:18,560
The flow isn't the tool.
54
00:02:18,560 --> 00:02:20,080
Power automate is a world-class engine.
55
00:02:20,080 --> 00:02:23,480
The flow is the assumption that the tool can fix a broken model of work.
56
00:02:23,480 --> 00:02:25,600
When you scale a mess, you don't get efficiency.
57
00:02:25,600 --> 00:02:26,960
You get a bigger, faster mess.
58
00:02:26,960 --> 00:02:29,720
You get a system where errors propagate at the speed of the cloud.
59
00:02:29,720 --> 00:02:33,520
Imagine an invoice approval flow that's built on a flawed logic gate.
60
00:02:33,520 --> 00:02:35,960
In the manual world, a human might catch the error.
61
00:02:35,960 --> 00:02:40,360
In the industrialized world, you process 5,000 incorrect invoices before the first cup of
62
00:02:40,360 --> 00:02:41,360
coffee is finished.
63
00:02:41,360 --> 00:02:43,440
That's the risk of unmanaged scale.
64
00:02:43,440 --> 00:02:46,520
It removes the human friction that used to act as a safety net.
65
00:02:46,520 --> 00:02:49,520
So what's actually happening is that we're building a digital facade.
66
00:02:49,520 --> 00:02:53,320
On the surface, everything looks automated, but underneath, the structural integrity is
67
00:02:53,320 --> 00:02:54,320
controlling.
68
00:02:54,320 --> 00:02:55,320
You're in a meeting.
69
00:02:55,320 --> 00:02:56,320
You need an answer.
70
00:02:56,320 --> 00:02:59,360
But the flow that generates the report is stuck in a loop because a SharePoint list reached
71
00:02:59,360 --> 00:03:00,360
its threshold.
72
00:03:00,360 --> 00:03:02,360
You navigate, you search, you waste time.
73
00:03:02,360 --> 00:03:06,400
The assumption was that the automation would handle it, but because the process wasn't simplified
74
00:03:06,400 --> 00:03:07,400
first.
75
00:03:07,400 --> 00:03:08,400
The automation became the bottleneck.
76
00:03:08,400 --> 00:03:10,920
We need to shift our focus from how fast we can build.
77
00:03:10,920 --> 00:03:12,280
To how well we can sustain.
78
00:03:12,280 --> 00:03:16,280
If your team spends more time babysitting existing flows than creating new value, you've reached
79
00:03:16,280 --> 00:03:17,280
the tipping point.
80
00:03:17,280 --> 00:03:18,280
You aren't innovating anymore.
81
00:03:18,280 --> 00:03:21,080
You're just managing the industrialization of chaos.
82
00:03:21,080 --> 00:03:22,880
And that is a very expensive place to be.
83
00:03:22,880 --> 00:03:26,880
We need a better way to diagnose the rot before it takes down the entire system, because in
84
00:03:26,880 --> 00:03:31,480
reality, the mirage of speed is exactly what's slowing you down.
85
00:03:31,480 --> 00:03:32,920
Diagnosing the structural rot.
86
00:03:32,920 --> 00:03:36,200
To fix a system, you have to look at where it's actually decaying.
87
00:03:36,200 --> 00:03:38,120
We need to talk about the ordered black hole.
88
00:03:38,120 --> 00:03:42,760
This is the dark corner of your Microsoft tenant where flows exist without documentation,
89
00:03:42,760 --> 00:03:45,240
versioning, or any traceable intent.
90
00:03:45,240 --> 00:03:48,440
In most organizations, these are the ghosts in the machine scripts.
91
00:03:48,440 --> 00:03:51,640
They were built to solve a specific problem three years ago by someone who no longer works
92
00:03:51,640 --> 00:03:52,640
there.
93
00:03:52,640 --> 00:03:55,480
When they run, they consume API calls, they move data.
94
00:03:55,480 --> 00:03:56,840
But nobody can tell you why.
95
00:03:56,840 --> 00:03:58,480
This isn't just a management annoyance.
96
00:03:58,480 --> 00:04:01,520
It is a fundamental threat to your operational continuity.
97
00:04:01,520 --> 00:04:03,840
When the logic is hidden, the risk is unquantifiable.
98
00:04:03,840 --> 00:04:06,240
We need a North Star metric to cut through the noise.
99
00:04:06,240 --> 00:04:08,520
Forget about total runs or active users.
100
00:04:08,520 --> 00:04:09,720
Those are vanity numbers.
101
00:04:09,720 --> 00:04:13,960
The metric that matters is the percentage of orphaned or unowned flows in your environment.
102
00:04:13,960 --> 00:04:16,680
This is the ultimate indicator of structural rot.
103
00:04:16,680 --> 00:04:20,800
If a flow has no designated owner, it is a liability waiting to detonate.
104
00:04:20,800 --> 00:04:25,720
It shows that in large environments, over 50% of active flows like any clear ownership
105
00:04:25,720 --> 00:04:26,720
or review cycle.
106
00:04:26,720 --> 00:04:28,680
That is a staggering amount of unmanaged risk.
107
00:04:28,680 --> 00:04:31,360
If no one owns the flow, no one fixes it when it fails.
108
00:04:31,360 --> 00:04:36,400
Eventually, no one will even know it existed until a critical business process simply stops.
109
00:04:36,400 --> 00:04:38,520
You can perform a quick diagnostic check right now.
110
00:04:38,520 --> 00:04:40,600
Look at your last three major flow failures.
111
00:04:40,600 --> 00:04:43,720
Was the remediation time longer than the original build time?
112
00:04:43,720 --> 00:04:46,360
If the answer is yes, you have a structural crisis.
113
00:04:46,360 --> 00:04:49,840
It means your architecture is so brittle and poorly documented that it's actually
114
00:04:49,840 --> 00:04:52,400
easier to start over than to repair what you have.
115
00:04:52,400 --> 00:04:54,240
That is the definition of a failed model.
116
00:04:54,240 --> 00:04:58,480
You are spending your most expensive engineering hours playing detective in a maze of your
117
00:04:58,480 --> 00:04:59,480
own making.
118
00:04:59,480 --> 00:05:03,240
This happens because we treat automation as a set and forget task rather than a living
119
00:05:03,240 --> 00:05:04,240
product.
120
00:05:04,240 --> 00:05:05,800
Then there is the identity blind spot.
121
00:05:05,800 --> 00:05:09,200
This is perhaps the most common way organizations scale their chaos.
122
00:05:09,200 --> 00:05:12,200
We tie critical business logic to individual user accounts.
123
00:05:12,200 --> 00:05:13,760
It seems easy during development.
124
00:05:13,760 --> 00:05:15,560
You just use your own connection, right?
125
00:05:15,560 --> 00:05:17,760
But this creates a ticking time bomb.
126
00:05:17,760 --> 00:05:22,440
And that person leaves the company or changes their password, the entire chain collapses.
127
00:05:22,440 --> 00:05:26,240
I've seen cases where a single lever took the company's entire global approval chain
128
00:05:26,240 --> 00:05:27,240
with them.
129
00:05:27,240 --> 00:05:31,080
One deactivated account triggered a cascade of failures that took days to untangle because
130
00:05:31,080 --> 00:05:34,800
the connections were buried deep inside, unmanaged, undocumented flows.
131
00:05:34,800 --> 00:05:36,520
This isn't just about technical settings.
132
00:05:36,520 --> 00:05:38,520
It's about the lack of a clear operating model.
133
00:05:38,520 --> 00:05:42,080
We deploy policies and labels, but we fail to design the human accountability structures
134
00:05:42,080 --> 00:05:43,080
that sustain them.
135
00:05:43,080 --> 00:05:45,200
You might have a dashboard that looks green.
136
00:05:45,200 --> 00:05:46,840
All your flows are succeeding.
137
00:05:46,840 --> 00:05:48,720
But that is often just compliance theatre.
138
00:05:48,720 --> 00:05:50,560
Beneath the surface, the exposure is growing.
139
00:05:50,560 --> 00:05:53,440
Data is moving through improperly secured connectors.
140
00:05:53,440 --> 00:05:57,280
Sensitive intellectual property is being synced to unmanaged personal folders.
141
00:05:57,280 --> 00:06:00,600
Because there is no life cycle transparency, the rot spreads quietly.
142
00:06:00,600 --> 00:06:04,840
The moment this breaks is usually during a high stakes event, an audit, a security breach,
143
00:06:04,840 --> 00:06:06,800
a major system migration.
144
00:06:06,800 --> 00:06:09,880
That's when you realize that your digital transformation was actually just a series
145
00:06:09,880 --> 00:06:13,680
of ad hoc scripts layered over unresolved legacy problems.
146
00:06:13,680 --> 00:06:17,520
You haven't modernized.
147
00:06:17,520 --> 00:06:20,520
We have to stop looking at flows as isolated tools.
148
00:06:20,520 --> 00:06:25,240
We have to start seeing them as interconnected parts of a unified digital operating layer.
149
00:06:25,240 --> 00:06:29,040
If you continue to govern in silos, optimizing one department while ignoring the aggregate
150
00:06:29,040 --> 00:06:30,760
sprawl, the result is inevitable.
151
00:06:30,760 --> 00:06:32,160
The rot will eventually reach the core.
152
00:06:32,160 --> 00:06:35,720
We need to move past the ad hoc phase and implement a framework that treats structural
153
00:06:35,720 --> 00:06:38,640
integrity as a non-negotiable requirement.
154
00:06:38,640 --> 00:06:41,720
The technical debt ratio, TDR, framework.
155
00:06:41,720 --> 00:06:45,360
To move beyond the ad hoc mess, we need to stop talking about bugs and start talking about
156
00:06:45,360 --> 00:06:47,600
the technical debt ratio.
157
00:06:47,600 --> 00:06:52,040
This is how we move from emotional arguments about clunky tools to hard financial data that
158
00:06:52,040 --> 00:06:53,800
leadership actually respects.
159
00:06:53,800 --> 00:06:57,280
We need a standardized way to quantify the cost of our shortcuts.
160
00:06:57,280 --> 00:06:59,280
The formula is actually quite simple.
161
00:06:59,280 --> 00:07:04,240
TDR equals the cost to fix your automation debt divided by the total automation investment
162
00:07:04,240 --> 00:07:06,000
multiplied by 100.
163
00:07:06,000 --> 00:07:09,520
It's a percentage that tells you exactly how much of your capital is being held hostage
164
00:07:09,520 --> 00:07:10,680
by past mistakes.
165
00:07:10,680 --> 00:07:13,000
If your TDR is under 5% you're in the clear.
166
00:07:13,000 --> 00:07:15,320
You're building clean, modular and sustainable systems.
167
00:07:15,320 --> 00:07:19,680
But if that number climbs over 5%, your automation is no longer delivering value.
168
00:07:19,680 --> 00:07:20,760
It's consuming it.
169
00:07:20,760 --> 00:07:24,000
You're officially in a hole where every new feature you build is actually making the overall
170
00:07:24,000 --> 00:07:26,200
system more expensive to maintain.
171
00:07:26,200 --> 00:07:29,000
Most people ignore this because they only look at the initial build cost.
172
00:07:29,000 --> 00:07:32,000
But the real weight is in the annual productivity cost.
173
00:07:32,000 --> 00:07:35,400
This is the total number of hours your team spends babysitting existing flows instead
174
00:07:35,400 --> 00:07:36,720
of building new ones.
175
00:07:36,720 --> 00:07:38,680
This isn't just maintenance.
176
00:07:38,680 --> 00:07:41,000
It is a drain on your innovation capacity.
177
00:07:41,000 --> 00:07:45,040
If your developers or makers are spending 40% of their week troubleshooting connection failures
178
00:07:45,040 --> 00:07:48,120
or manual data corrections, your APC is through the roof.
179
00:07:48,120 --> 00:07:50,760
You aren't scaling a business, you're scaling a repair shop.
180
00:07:50,760 --> 00:07:53,640
We see this clearly when we measure psychomatic complexity.
181
00:07:53,640 --> 00:07:57,080
This is the number of possible execution parts within a single flow.
182
00:07:57,080 --> 00:08:00,720
Once that number exceeds 15 you've entered the danger zone for maintainability.
183
00:08:00,720 --> 00:08:04,800
At that level of complexity, a human can no longer reliably predict what happens when
184
00:08:04,800 --> 00:08:06,440
a single variable changes.
185
00:08:06,440 --> 00:08:07,920
You've created a black box.
186
00:08:07,920 --> 00:08:12,360
Skipping the process redesign phase carries a hidden 30% to 40% penalty.
187
00:08:12,360 --> 00:08:16,800
When you automate a process exactly as it exists today, you are leaving nearly half of your
188
00:08:16,800 --> 00:08:18,600
projected savings on the table.
189
00:08:18,600 --> 00:08:19,600
Why?
190
00:08:19,600 --> 00:08:21,840
Because you're still carrying the weight of the old manual logic.
191
00:08:21,840 --> 00:08:25,200
You're asking a cloud engine to replicate the limitations of a human brain.
192
00:08:25,200 --> 00:08:28,040
That mismatch creates friction and friction creates debt.
193
00:08:28,040 --> 00:08:30,960
Real ROI doesn't come from doing the same task faster.
194
00:08:30,960 --> 00:08:34,240
It comes from eliminating the task entirely through better architecture.
195
00:08:34,240 --> 00:08:37,640
If you skip that refactoring step, you're just digitizing the friction.
196
00:08:37,640 --> 00:08:41,360
We have to recognize that technical debt behaves exactly like financial debt.
197
00:08:41,360 --> 00:08:45,520
You can ignore the principle, but the interest will eventually bankrupt your agility.
198
00:08:45,520 --> 00:08:50,080
In the Microsoft ecosystem, this interest manifests as prompt, logic, debt and integration
199
00:08:50,080 --> 00:08:51,080
friction.
200
00:08:51,080 --> 00:08:55,640
You take a shortcut today to meet a deadline, but that shortcut becomes a permanent anchor.
201
00:08:55,640 --> 00:09:00,120
By using the TDR framework, you can finally show the board that the quick fix is actually
202
00:09:00,120 --> 00:09:01,880
a long term liability.
203
00:09:01,880 --> 00:09:05,360
You can justify the time needed for refactoring because you can prove that it's cheaper to fix
204
00:09:05,360 --> 00:09:08,880
the foundation now than to rebuild the skyscraper later.
205
00:09:08,880 --> 00:09:12,800
This shift in perspective is what separates a world-class IT organization from one that
206
00:09:12,800 --> 00:09:14,680
is constantly on the verge of collapse.
207
00:09:14,680 --> 00:09:17,840
We need to stop rewarding speed and start rewarding structural health.
208
00:09:17,840 --> 00:09:21,640
Only then can we stop the bleeding and begin to reclaim the innovation budget that is currently
209
00:09:21,640 --> 00:09:24,240
being swallowed by the industrialization of chaos.
210
00:09:24,240 --> 00:09:27,000
If you can't measure the debt, you can't manage the recovery.
211
00:09:27,000 --> 00:09:31,040
It's time to look at the numbers and face the reality of what we've built.
212
00:09:31,040 --> 00:09:33,000
The ESO are gating strategy.
213
00:09:33,000 --> 00:09:36,080
To stop the bleeding, we need a filter before the build.
214
00:09:36,080 --> 00:09:41,520
We have to stop the paving the cow paths, mentality that has plagued enterprise IT for decades.
215
00:09:41,520 --> 00:09:44,960
This is where we move from being reactive builders to strategic architects.
216
00:09:44,960 --> 00:09:48,160
I use a specific gating framework called ESO are.
217
00:09:48,160 --> 00:09:52,160
It stands for eliminate, standardize, optimize, automate and robotize.
218
00:09:52,160 --> 00:09:56,200
Most teams skip straight to the A and wonder why their systems feel heavy.
219
00:09:56,200 --> 00:09:59,160
They are automating things that shouldn't exist in the first place.
220
00:09:59,160 --> 00:10:00,520
You have to be ruthless here.
221
00:10:00,520 --> 00:10:02,920
The first step is the E eliminate.
222
00:10:02,920 --> 00:10:07,120
If a process is redundant, if it serves a legacy requirement that no longer adds value,
223
00:10:07,120 --> 00:10:08,400
don't automate it.
224
00:10:08,400 --> 00:10:09,400
Kill it.
225
00:10:09,400 --> 00:10:12,040
Every flow you don't build is a flow you don't have to govern, secure or repair.
226
00:10:12,040 --> 00:10:15,520
Once you've stripped away the waste, you move into the S and O.
227
00:10:15,520 --> 00:10:16,680
Standardize and optimize.
228
00:10:16,680 --> 00:10:20,400
You must clean the logic before you ever touch the power automate canvas.
229
00:10:20,400 --> 00:10:24,160
If your process has 15 different ways to handle an invoice because five different departments
230
00:10:24,160 --> 00:10:28,400
want their own special flavor, you have a standardization problem, not a technical one.
231
00:10:28,400 --> 00:10:30,960
You cannot build a stable system on top of fractured logic.
232
00:10:30,960 --> 00:10:32,960
You have to force a single optimized path.
233
00:10:32,960 --> 00:10:34,280
This is where the real work happens.
234
00:10:34,280 --> 00:10:38,040
It's about negotiating with stakeholders to simplify the business rules only after the
235
00:10:38,040 --> 00:10:39,720
process is lean and predictable.
236
00:10:39,720 --> 00:10:41,760
Do we move to the final stages?
237
00:10:41,760 --> 00:10:43,240
Automate and robotize.
238
00:10:43,240 --> 00:10:45,480
This is where we finally apply the technology.
239
00:10:45,480 --> 00:10:49,240
By the time you reach this step, the build is easy because the complexity has already been
240
00:10:49,240 --> 00:10:50,920
engineered out of the system.
241
00:10:50,920 --> 00:10:54,360
This shift also requires us to change how we actually construct our flows.
242
00:10:54,360 --> 00:10:58,280
We need to stop building monolithic mega flows that try to do everything in one giant sequence.
243
00:10:58,280 --> 00:11:01,000
These are impossible to test and even harder to debug.
244
00:11:01,000 --> 00:11:04,400
Instead, we need to move toward modular child flow architectures.
245
00:11:04,400 --> 00:11:06,440
This mirrors professional software patterns.
246
00:11:06,440 --> 00:11:11,320
You build a dedicated child flow for a specific task, like sending a standardized notification
247
00:11:11,320 --> 00:11:14,960
or logging an error and you call that flow for multiple parent processes.
248
00:11:14,960 --> 00:11:16,880
This creates a single point of maintenance.
249
00:11:16,880 --> 00:11:21,360
If your notification template changes, you updated once, not 50 times across 50 different
250
00:11:21,360 --> 00:11:22,360
flows.
251
00:11:22,360 --> 00:11:24,640
This is how you build for scale without building for chaos.
252
00:11:24,640 --> 00:11:27,880
We also have to change our mindset regarding the lifecycle of these assets.
253
00:11:27,880 --> 00:11:31,760
The model requires us to treat every flow as a product with a defined beginning, middle
254
00:11:31,760 --> 00:11:32,760
and end.
255
00:11:32,760 --> 00:11:34,160
It is not a set and forget task.
256
00:11:34,160 --> 00:11:37,800
It is a living entity that requires a clear purpose and a deprecation date.
257
00:11:37,800 --> 00:11:41,240
If a flow doesn't have a sunset plan, it will eventually become part of the structural
258
00:11:41,240 --> 00:11:42,800
rod we discussed earlier.
259
00:11:42,800 --> 00:11:46,440
We need to implement gating at the environment level that asks, "Who owns this?
260
00:11:46,440 --> 00:11:47,440
What is the business value?
261
00:11:47,440 --> 00:11:48,440
How long will it run?
262
00:11:48,440 --> 00:11:50,280
And what is the plan for when it fails?
263
00:11:50,280 --> 00:11:53,640
By implementing Esoar, you move from a culture of, "Can we build it?
264
00:11:53,640 --> 00:11:54,640
2.
265
00:11:54,640 --> 00:11:55,640
Should we build it?
266
00:11:55,640 --> 00:11:56,640
3.
267
00:11:56,640 --> 00:12:00,440
Rewarding the volume of flows created and start rewarding the integrity of the ecosystem.
268
00:12:00,440 --> 00:12:05,600
This gating strategy ensures that only the most robust, necessary and optimized processes
269
00:12:05,600 --> 00:12:07,440
make it into your production environment.
270
00:12:07,440 --> 00:12:12,120
It turns your power platform from a wild west of ad hoc scripts into a governed, high-performance
271
00:12:12,120 --> 00:12:13,120
engine.
272
00:12:13,120 --> 00:12:14,480
You aren't just making things faster.
273
00:12:14,480 --> 00:12:15,720
You are making them better.
274
00:12:15,720 --> 00:12:19,400
And that is the only way to win the battle against organizational debt.
275
00:12:19,400 --> 00:12:21,080
Preempting the co-pilot fallacy.
276
00:12:21,080 --> 00:12:24,320
There is a dangerous excuse circulating in boardrooms right now.
277
00:12:24,320 --> 00:12:27,360
It's a comfortable myth that suggests we don't actually need to worry about governance
278
00:12:27,360 --> 00:12:30,640
or structural integrity because AI will eventually clean it up for us.
279
00:12:30,640 --> 00:12:32,640
I call this the co-pilot fallacy.
280
00:12:32,640 --> 00:12:36,640
The assumption is that because generative AI can write the code, it can also manage the
281
00:12:36,640 --> 00:12:39,560
consequences, but in reality.
282
00:12:39,560 --> 00:12:43,240
Co-pilot accelerates creation while doing absolutely nothing to accelerate accountability
283
00:12:43,240 --> 00:12:44,240
or architecture.
284
00:12:44,240 --> 00:12:48,320
If you are using AI to build flows faster on top of an unmanaged foundation, you aren't
285
00:12:48,320 --> 00:12:52,600
solving your debt problem, you are just supercharging the speed at which you accrue it.
286
00:12:52,600 --> 00:12:55,920
It acts as a high-velocity stress test for your existing environment.
287
00:12:55,920 --> 00:13:00,960
It reveals the cracks in your strategy faster than any human developer ever could.
288
00:13:00,960 --> 00:13:04,400
When you ask an AI to build a solution, it looks for the path of least resistance.
289
00:13:04,400 --> 00:13:06,800
It doesn't care about your long-term maintenance window.
290
00:13:06,800 --> 00:13:09,000
It doesn't care about your service account strategy.
291
00:13:09,000 --> 00:13:10,560
It just wants to fulfill the prompt.
292
00:13:10,560 --> 00:13:15,160
This creates a new, invisible category of risk that I call "prompt-logic debt".
293
00:13:15,160 --> 00:13:19,480
These are complex AI-generated patterns that the original creator doesn't actually understand.
294
00:13:19,480 --> 00:13:21,400
They've built a black box inside a black box.
295
00:13:21,400 --> 00:13:23,800
What typically happens is a form of digital hoarding.
296
00:13:23,800 --> 00:13:26,840
A user prompts a flow into existence in 30 seconds.
297
00:13:26,840 --> 00:13:27,840
It works.
298
00:13:27,840 --> 00:13:28,840
They move on.
299
00:13:28,840 --> 00:13:31,840
But because they didn't architect the logic, they can't troubleshoot it when the API
300
00:13:31,840 --> 00:13:33,760
schema changes six months later.
301
00:13:33,760 --> 00:13:37,520
They've traded a few hours of development time for a permanent anchor of technical debt.
302
00:13:37,520 --> 00:13:41,120
We are seeing a massive surge in these ghost flows.
303
00:13:41,120 --> 00:13:45,800
Automations built by AI that perform critical tasks but have zero human legibility.
304
00:13:45,800 --> 00:13:50,040
If the person who typed the prompt can't explain the JSON transformation inside the action,
305
00:13:50,040 --> 00:13:51,800
you are officially flying blind.
306
00:13:51,800 --> 00:13:55,880
The will-clean-it-up later trap is more seductive than ever because AI makes later feel
307
00:13:55,880 --> 00:13:56,960
far away.
308
00:13:56,960 --> 00:14:01,120
But later, arrives the moment you hit 500 flows and realize you've built a tangled web
309
00:14:01,120 --> 00:14:03,680
of prompt-based logic that no one can audit.
310
00:14:03,680 --> 00:14:06,880
You've moved from a world where you had a few messy scripts to a world where you have an
311
00:14:06,880 --> 00:14:09,280
entire ecosystem of unmanaged intelligence.
312
00:14:09,280 --> 00:14:10,640
This is where the model breaks.
313
00:14:10,640 --> 00:14:15,000
AI-native tools are brilliant at execution, but they are terrible at stewardship.
314
00:14:15,000 --> 00:14:18,560
They can replicate your mess at superhuman speed, but they cannot give you the structural
315
00:14:18,560 --> 00:14:20,560
integrity you refuse to build at the start.
316
00:14:20,560 --> 00:14:23,320
We need to shift our perspective on what these tools are for.
317
00:14:23,320 --> 00:14:27,160
We have to stop viewing AI as a builder that replaces the need for governance.
318
00:14:27,160 --> 00:14:32,520
Instead, we must treat AI as an orchestrator that operates strictly within a governed framework.
319
00:14:32,520 --> 00:14:35,880
This means you don't let Copilot touch the production canvas until you've established
320
00:14:35,880 --> 00:14:36,960
the guardrails.
321
00:14:36,960 --> 00:14:38,440
You need prompt versioning.
322
00:14:38,440 --> 00:14:41,760
You need human reviewers who actually understand the code being generated.
323
00:14:41,760 --> 00:14:45,800
You need automated publishing restrictions that prevent AI-generated assets from going
324
00:14:45,800 --> 00:14:48,680
live without a verified owner and a clear deprecation plan.
325
00:14:48,680 --> 00:14:53,360
If you ignore this, you are simply industrializing your chaos at a higher frequency.
326
00:14:53,360 --> 00:14:58,280
You are using the most advanced technology on the planet to scale your existing failures.
327
00:14:58,280 --> 00:15:00,760
Power Automate with Copilot is a power tool.
328
00:15:00,760 --> 00:15:03,320
In the hands of an architect, it builds a skyscraper.
329
00:15:03,320 --> 00:15:07,640
In the hands of someone ignoring the foundation, it just helps the building collapse faster.
330
00:15:07,640 --> 00:15:09,400
Stop waiting for the AI to fix your mess.
331
00:15:09,400 --> 00:15:12,360
The AI is the reason you need to fix the mess right now.
332
00:15:12,360 --> 00:15:15,720
Accountability cannot be outsourced to a large language model.
333
00:15:15,720 --> 00:15:17,200
Accountability starts with you.
334
00:15:17,200 --> 00:15:19,320
The two-week automation redesign sprint.
335
00:15:19,320 --> 00:15:21,400
We need to move from observation to action.
336
00:15:21,400 --> 00:15:23,680
You can't audit your way out of a structural collapse.
337
00:15:23,680 --> 00:15:25,160
You have to refactor your way out.
338
00:15:25,160 --> 00:15:28,720
I recommend starting what I call a two-week automation redesign sprint.
339
00:15:28,720 --> 00:15:32,480
This is a concentrated burst of activity designed to flip the script on your technical debt.
340
00:15:32,480 --> 00:15:35,640
It's not about fixing every single flow in your tenant.
341
00:15:35,640 --> 00:15:38,560
It's about securing the foundation of your most critical operations.
342
00:15:38,560 --> 00:15:41,480
You are shifting from a reactive posture to a proactive one.
343
00:15:41,480 --> 00:15:43,280
Week one is about ruthless prioritization.
344
00:15:43,280 --> 00:15:47,720
You need to pull a list of your top 20 flows based on business impact and risk.
345
00:15:47,720 --> 00:15:51,280
These are your high stakes assets, the ones that would cause the most pain if they stopped
346
00:15:51,280 --> 00:15:52,280
today.
347
00:15:52,280 --> 00:15:53,600
You aren't just looking at run counts.
348
00:15:53,600 --> 00:15:56,480
You're looking at data sensitivity and cross-departmental impact.
349
00:15:56,480 --> 00:16:00,040
You're asking, if this flow fails at two in the morning, who gets the phone call?
350
00:16:00,040 --> 00:16:02,680
If the answer is nobody knows, that's your first target.
351
00:16:02,680 --> 00:16:04,840
Once you have that list, hunt for the orphans.
352
00:16:04,840 --> 00:16:08,120
Any flow on that list without a named active owner is a priority.
353
00:16:08,120 --> 00:16:11,560
You are identifying the cracks in the hull before the ship takes on more water.
354
00:16:11,560 --> 00:16:14,840
You're looking for where the logic has drifted from the actual business requirement.
355
00:16:14,840 --> 00:16:17,640
You investigate the trigger conditions and the connection health.
356
00:16:17,640 --> 00:16:20,280
You document the why behind every single step.
357
00:16:20,280 --> 00:16:22,960
Week two is where you roll up your sleeves and refactor.
358
00:16:22,960 --> 00:16:26,080
You apply professional software patterns to these top 20 assets.
359
00:16:26,080 --> 00:16:29,960
This means implementing standardized logging so you actually have a searchable audit trail.
360
00:16:29,960 --> 00:16:33,880
It means configuring robust retry logic with exponential back-off so transient errors
361
00:16:33,880 --> 00:16:35,080
don't kill the process.
362
00:16:35,080 --> 00:16:37,640
You move beyond the basic success of failure labels.
363
00:16:37,640 --> 00:16:42,120
You build in error handling blocks that catch exceptions and root them to a centralized monitoring list.
364
00:16:42,120 --> 00:16:45,040
You replace hard-coded values with environment variables.
365
00:16:45,040 --> 00:16:48,800
This makes your flows portable and easier to manage across different environments.
366
00:16:48,800 --> 00:16:52,640
Most importantly, it means migrating these flows to service account ownership.
367
00:16:52,640 --> 00:16:56,240
You are decoupling your business logic from individual human identities.
368
00:16:56,240 --> 00:17:00,360
This creates a resilient layer that survives password resets and personnel changes.
369
00:17:00,360 --> 00:17:04,520
You are essentially turning a collection of scripts into a professional application portfolio.
370
00:17:04,520 --> 00:17:07,920
During the sprint, you must implement life cycle transparency.
371
00:17:07,920 --> 00:17:09,680
Every flow you touch needs three things.
372
00:17:09,680 --> 00:17:13,840
A clear owner, a documented purpose, and a hard deprecation date.
373
00:17:13,840 --> 00:17:17,440
If you can't define when a flow should be retired, you haven't finished the design.
374
00:17:17,440 --> 00:17:19,560
This isn't just a technical cleanup exercise.
375
00:17:19,560 --> 00:17:20,560
It is a wedge.
376
00:17:20,560 --> 00:17:24,800
You are using this two week window to change the organizational culture around automation.
377
00:17:24,800 --> 00:17:28,120
You are proving that a governed flow is more valuable than a fast one.
378
00:17:28,120 --> 00:17:31,280
Once the sprint is over, take those results to your leadership.
379
00:17:31,280 --> 00:17:35,360
For them the reduction in failure rates, show them the time reclaimed by the team.
380
00:17:35,360 --> 00:17:38,200
Use that momentum to secure a permanent governance budget.
381
00:17:38,200 --> 00:17:40,000
You aren't asking for permission to slow down.
382
00:17:40,000 --> 00:17:43,600
You're asking for the resources to move faster with total confidence.
383
00:17:43,600 --> 00:17:45,080
Power Automate is a mirror.
384
00:17:45,080 --> 00:17:46,440
It doesn't create chaos.
385
00:17:46,440 --> 00:17:49,840
It simply reflects and scales the systems you already have in place.
386
00:17:49,840 --> 00:17:52,840
If you scale a mess, you will inevitably inherit a larger mess.
387
00:17:52,840 --> 00:17:56,760
But if you choose to scale integrity, you create a massive competitive advantage.
388
00:17:56,760 --> 00:18:00,600
You build a business that is agile, resilient, and truly ready for the AI era.
389
00:18:00,600 --> 00:18:02,640
No homework for this week is simple.
390
00:18:02,640 --> 00:18:05,800
Find your orphaned flows and run that TDR calculation I showed you.
391
00:18:05,800 --> 00:18:09,680
If this changed how you think about automation, connect with me, Mirko Peters on LinkedIn.
392
00:18:09,680 --> 00:18:12,600
Please leave a review for the M365FM podcast.
393
00:18:12,600 --> 00:18:14,680
It helps other leaders find the signal in the noise.

Founder of m365.fm, m365.show and m365con.net
Mirko Peters is a Microsoft 365 expert, content creator, and founder of m365.fm, a platform dedicated to sharing practical insights on modern workplace technologies. His work focuses on Microsoft 365 governance, security, collaboration, and real-world implementation strategies.
Through his podcast and written content, Mirko provides hands-on guidance for IT professionals, architects, and business leaders navigating the complexities of Microsoft 365. He is known for translating complex topics into clear, actionable advice, often highlighting common mistakes and overlooked risks in real-world environments.
With a strong emphasis on community contribution and knowledge sharing, Mirko is actively building a platform that connects experts, shares experiences, and helps organizations get the most out of their Microsoft 365 investments.









