How to Turn Threat Analytics into Actual Security (Instead of Pretty Reports)

In today's cybersecurity landscape, threat analytics can significantly enhance your security posture by turning insights into decisive actions. However, many organizations fall into the trap of merely collecting data without translating it into operational responses. Recent studies reveal a critical disconnect between the data gathered and the actions taken, with many agencies lacking necessary capabilities for effective network security. To truly protect your assets, you must focus on actionable steps rather than just impressive dashboards and reports.
Key Takeaways
- Transform insights from threat analytics into actionable steps to enhance security.
- Avoid the illusion of security; dashboards alone do not protect your organization.
- Prioritize key threats to allocate resources effectively and create clear action plans.
- Assign ownership for threat response to ensure accountability and effective action.
- Automate responses to reduce incident response times and minimize impact.
- Continuously monitor threats and integrate real-time data to improve detection.
- Reduce alert fatigue by filtering out noise and focusing on genuine threats.
- Measure response metrics like Mean Time to Detect (MTTD) to track security effectiveness.
The Action Problem in Threat Analytics
The Illusion of Security
Many organizations mistakenly believe they are secure simply because they have implemented threat analytics tools. Dashboards filled with colorful graphs and alerts create a false sense of security. You might feel reassured by the data presented, but this perception can be misleading. The reality is that these tools often fail to translate insights into meaningful actions.
Consider the following points:
- Longer response times occur as analysts sift through noise to find true positives.
- Critical alerts may get buried in clutter, increasing the risk of missing vital information.
- Analyst burnout can result from the overwhelming volume of alerts, leading to attrition and decreased effectiveness.
These factors contribute to a dangerous illusion. You may think your organization is well-protected, but without effective action, vulnerabilities remain.
Why Seeing Threats Isn’t Enough
Simply seeing threats does not equate to effective security. Many organizations rely on outdated infrastructure and manual processes, which limit their ability to respond in real time. High volumes of alerts can lead to alert fatigue, overwhelming your security teams and causing them to miss critical threats.
Here are some common reasons why threat analytics fail to result in actionable security improvements:
- Reliance on outdated infrastructure hampers timely remediation.
- Overwhelming alert volumes reduce the ability to respond effectively.
- Lack of integration makes it difficult to prioritize findings.
- Absence of clear remediation guidance leaves issues unaddressed.
- False positives divert attention from genuine threats.
Moreover, dashboards often lack a clear narrative. They present dense collections of data that do not align with the questions you need to answer. Analysts may struggle to quickly identify anomalies or determine next steps. This disconnect can lead to delayed detection, where attacks are identified only after damage has occurred.
To bridge the gap between insight and action, organizations must focus on operationalizing their threat analytics. This means transforming data into actionable steps that enhance security rather than relying solely on impressive dashboards.
Why Threat Analytics Feels Useless
Retrospective Analysis Limits
Many organizations rely on retrospective analysis in their threat analytics, but this approach has significant limitations. You may find yourself analyzing past incidents without gaining insights into current threats. Here are some key drawbacks of this method:
- Lack of detection alerts can create blind spots, leaving you unaware of the full scope of an attack.
- Insufficient historical data retention means you often work with incomplete information.
- Missing historical network visibility can delay incident response and complicate compliance efforts.
These limitations hinder your ability to understand risks fully. As a result, you may become uninformed about potential threats, increasing the likelihood of financial loss, operational disruptions, and damage to your organization's reputation.
Disconnected Insights and Operations
Disconnected insights and operations present another challenge in threat analytics. When security insights fail to reach operational teams, the effectiveness of your security measures diminishes. Consider the following statistics that highlight the consequences of this disconnect:
| Statistic | Percentage |
|---|---|
| Increased compliance risk | 62% |
| Lack of context for cross-functional tasks | 54% |
| Lack continuous visibility into data | 49% |
| Spend too much time tracking requests | 55% |
| Face repeated internal follow-ups | 45% |
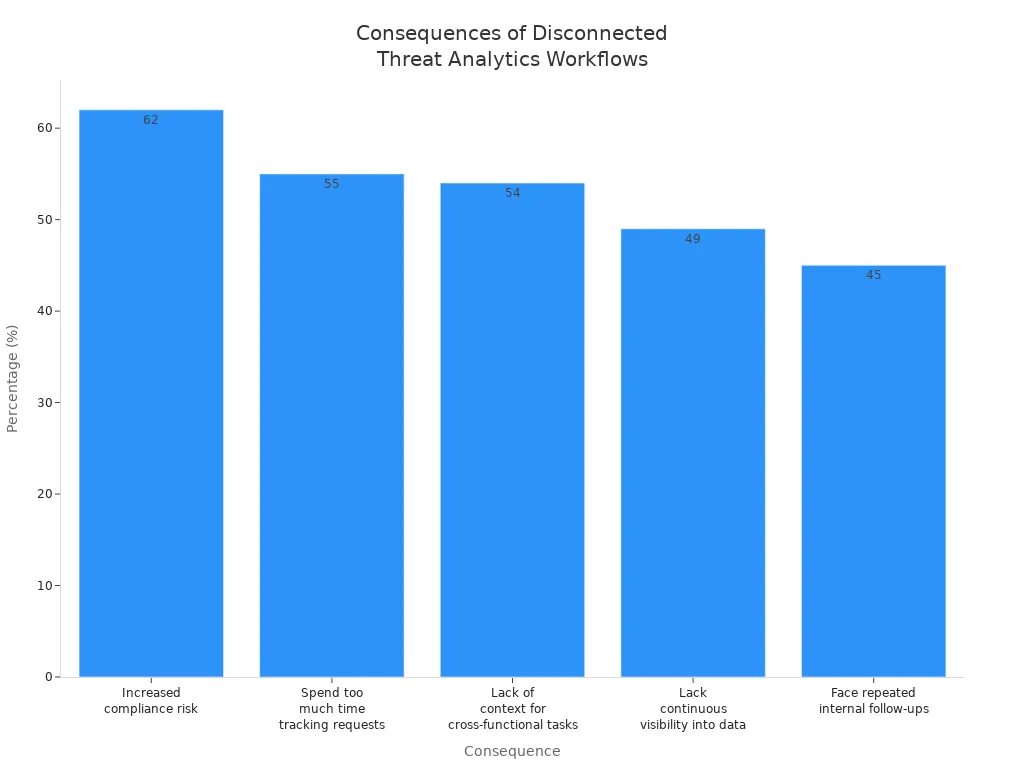
These figures illustrate how disconnected workflows can lead to inefficiencies and missed opportunities for proactive risk management. Without a seamless connection between insights and operations, your organization struggles to prioritize and respond to threats effectively.
Lack of Ownership and Accountability
A lack of ownership and accountability in threat analytics processes further exacerbates the problem. Many organizations do not designate a dedicated security leader to oversee the lifecycle of threat analytics. This absence leads to inconsistent execution and stalled remediation efforts.
To address this issue, formalized governance is essential. You must ensure that risks are actively owned, funded, and tracked as part of your corporate strategy. Without clear ownership, your organization may struggle to implement effective incident management strategies, leaving you vulnerable to emerging threats.
Operationalizing Threat Analytics for Security
Mapping Insights to Actions
To enhance your security posture, you must transform insights from threat analytics into concrete actions. This process involves mapping the data you collect to specific security measures. A self-driven architecture for real-time cloud threat detection can automate the detection of threats, prioritize risks, and execute remediation actions. This approach ensures that you do not merely observe threats but actively respond to them.
Consider these steps to effectively map insights to actions:
- Identify Key Threats: Focus on the most prevalent threats facing your organization. This prioritization allows you to allocate resources effectively.
- Develop Action Plans: For each identified threat, create a clear action plan that outlines the steps your team should take. This plan should include roles, responsibilities, and timelines.
- Integrate with Existing Systems: Ensure that your threat analytics tools work seamlessly with your existing security infrastructure. This integration enhances the speed and effectiveness of your responses.
Assigning Clear Ownership
Assigning clear ownership for threat analytics-driven actions is crucial for accountability and effective response. When you designate specific individuals or teams to manage risks, you transform abstract concepts into real responsibilities. This structured ownership fosters a culture of shared responsibility and aligns security efforts with business outcomes.
Here’s how to establish clear ownership:
| Evidence | Description |
|---|---|
| Accountability | Assigning ownership transforms risks from abstract concepts into real responsibilities. |
| Confidence | Consistent monitoring and communication of risks build confidence among teams. |
| Clarity | Connecting risks to specific capabilities prevents confusion and prioritizes mitigation. |
| Structured Ownership | Deliberate risk ownership fosters a culture of shared responsibility. |
| Organizational Resilience | Effective risk ownership promotes a proactive risk management culture. |
By implementing these strategies, you can ensure that your security team is prepared to act swiftly and decisively when threats arise.
Automating Responses
Automation plays a vital role in operationalizing threat analytics. By automating responses to identified threats, you can significantly reduce response times and minimize the impact of incidents. Automation allows your security team to focus on strategic initiatives rather than getting bogged down by repetitive tasks.
Here are some examples of how automation can enhance your security:
- Conditional Access: Automatically restrict access when risky sign-ins are detected.
- Session Revoke: Instantly revoke sessions when impossible travel patterns are identified.
- Auto Investigation: Trigger automated investigations for suspicious activities, allowing your team to respond faster.
However, organizations often face challenges when operationalizing threat analytics. Common issues include data overload, lack of context, and insufficient resources to manage threat data. To overcome these challenges, you must filter out noise from signal and ensure that your security tools are configured to act on relevant threat intelligence.
By focusing on these strategies, you can effectively operationalize threat analytics, turning insights into decisive actions that enhance your overall security posture.
Leveraging Real-Time Threat Analytics
Continuous Monitoring Techniques
Real-time threat analytics relies heavily on continuous monitoring to detect and respond to threats swiftly. By implementing effective monitoring techniques, you can significantly enhance your security posture. Here are some key strategies to consider:
- Threat Intelligence Integration: Incorporate up-to-date threat intelligence feeds to correlate with real-time data. This approach reduces false positives and helps identify genuine risks.
- Behavioral Analysis and Anomaly Detection: Establish baselines of normal activity to detect deviations that may indicate security threats. This technique is crucial for identifying sophisticated attacks.
- Automated Response and Remediation: Enable predefined actions in response to threats. This capability significantly reduces response time and the impact of incidents.
- Alert Management and Reporting: Ensure relevant personnel are informed about threats and incidents while filtering out false positives. This process helps maintain focus on critical issues.
By employing these continuous monitoring techniques, you can create a robust framework for real-time threat monitoring that enhances your organization's security.
Automated Real-Time Responses
Automated real-time responses are essential for effective security programs. They enhance human expertise by providing context and allowing security teams to focus on strategic initiatives. Here’s how automation impacts your threat mitigation efforts:
- Accelerated Detection and Response: Automation speeds up the detection and response process, minimizing damage during incidents. This capability allows your team to manage incidents more effectively with a reduced manual workload.
- Faster Root Cause Identification: Automating incident triage and investigation leads to quicker identification of the root cause. This efficiency allows your team to spend less time on manual tasks and more time on strategic responses.
- Improved Overall Efficiency: With less time spent on repetitive tasks, your incident response teams can operate more efficiently. This improvement translates to better outcomes in managing security incidents.
The average reduction in incident response time when leveraging real-time threat analytics is significant. For instance, non-MDR clients spent an average of 19 hours per incident for Business Email Compromise (BEC), while MDR clients reduced this time to just 2 hours. This reduction indicates a nearly 90% decrease in time to resolution, showcasing the power of real-time insights.
Reducing Noise and Measuring Impact
Aggressive Noise Reduction
Alert fatigue remains one of the biggest challenges in cybersecurity today. Security teams often face thousands of alerts daily, with many being false positives or low-priority signals. This overload can cause you to miss real cyber threats and delay critical decisions. To improve your security posture, you must aggressively reduce noise in your threat analytics.
Start by enriching alerts with contextual information from multiple sources. Combine threat intelligence, such as known malicious IP addresses, with asset sensitivity and metadata like MITRE ATT&CK techniques. This enriched context helps you prioritize alerts based on actual risks to your organization. When you understand the business impact behind each alert, you can focus on genuine threats and reduce distractions.
Treat your detection mechanisms like software that requires continuous tuning. Regularly test and refine your detection rules to adapt to evolving cyber threats and changes in your environment. This iterative approach minimizes false positives and sharpens your threat detection capabilities.
Automation plays a critical role in noise reduction. Use security orchestration tools to handle routine tasks automatically. For example, automatically block confirmed malicious IPs or disable compromised accounts without manual intervention. This automation frees your team to concentrate on complex attacks and strategic security measures, improving overall efficiency.
Measuring Time to Action and Prevention
Measuring your security program’s effectiveness requires focusing on response metrics rather than just detection volume. Tracking how quickly you detect and respond to threats provides clearer insights into your operational success.
Key metrics to monitor include:
- Dwell Time: How long an attacker remains undetected in your system.
- Breakout Time: The time it takes for an attacker to move laterally after initial access.
- Mean Time to Detect (MTTD): The average time from attack start to detection.
- Mean Time to Respond (MTTR): The average time from detection to remediation.
| Metric | Description |
|---|---|
| Mean Time to Detect | Measures how fast you identify a security threat. |
| Mean Time to Respond | Measures how quickly you act to contain and resolve attacks. |
Reducing MTTD and MTTR directly improves your security posture by limiting the window attackers have to cause damage. Real-time threat detection and continuous monitoring help you lower these times, enabling faster decisions and actions.
Focus on measuring the time between key events: when an attack occurs, when you detect it, when you respond, and when you resolve the incident. This timeline highlights gaps in your security measures and guides improvements.
By aggressively reducing noise and tracking meaningful response metrics, you transform your threat analytics from a passive tool into an active driver of security. This shift helps you prevent breaches, reduce risks, and strengthen your cybersecurity defenses.
In cybersecurity, you enhance your security posture not by merely seeing more threats but by acting faster. Smart threat intelligence empowers you to respond quickly, reducing risks and boosting confidence in your security measures. Operationalizing threat analytics is crucial; it transforms insights into decisive actions.
Consider these practical steps to close the gap between insight and action:
- Map insights to specific actions.
- Assign clear ownership for threat response.
- Automate responses to streamline incident response.
By implementing these strategies, you can significantly improve your organization's security outcomes.
FAQ
What is threat analytics?
Threat analytics involves collecting and analyzing data to identify potential security threats. It helps organizations understand risks and respond effectively to incidents.
How can I operationalize threat analytics?
You can operationalize threat analytics by mapping insights to actions, assigning ownership, and automating responses. This approach ensures timely and effective security measures.
Why is real-time monitoring important?
Real-time monitoring allows you to detect threats as they occur. It enables swift responses, reducing the potential impact of security incidents.
What are common challenges in threat analytics?
Common challenges include alert fatigue, disconnected insights, and lack of ownership. These issues can hinder effective threat detection and response.
How can I reduce alert fatigue?
You can reduce alert fatigue by filtering out false positives, enriching alerts with context, and automating routine tasks. This helps prioritize genuine threats.
What metrics should I track for security effectiveness?
Track metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). These metrics provide insights into your incident response efficiency.
How does automation improve security?
Automation speeds up threat detection and response, allowing your team to focus on strategic initiatives. It minimizes human error and enhances overall efficiency.
Why is ownership crucial in threat analytics?
Ownership ensures accountability and effective response to threats. Designating specific individuals or teams fosters a culture of responsibility and proactive risk management.