Why Role Sprawl Undermines Your Security Framework
Role sprawl occurs when organizations create excessive user roles, leading to a complex web of access permissions. This complexity can significantly undermine your security framework. You may find that having too many roles creates vulnerabilities, operational inefficiencies, and increased risks. For instance, employees often spend up to 9% of their workday switching between various applications due to overlapping functions. This not only drains productivity but also complicates compliance efforts, resulting in higher operational costs. Understanding and addressing role sprawl is vital for maintaining a robust security posture.
Key Takeaways
Role sprawl happens when too many user roles create confusion and security risks.
Excessive roles increase attack surfaces, making data breaches and privilege abuse more likely.
Managing many roles slows down employees and wastes resources, hurting productivity.
Alert fatigue from too many security warnings can cause missed threats and analyst burnout.
Use the principle of least privilege to give users only the access they need.
Design roles based on business functions and keep exceptions minimal to avoid complexity.
Regularly audit and clean up roles to maintain security and simplify compliance.
Reducing role sprawl saves money, improves efficiency, and strengthens long-term security.
What Is Role Sprawl?
7 Surprising Facts About Role Sprawl
Understanding why role sprawl undermines your security framework helps prioritize remediation. Below are seven surprising facts that reveal how pervasive and damaging role sprawl can be.
- Excess privileges often outnumber users: In many environments there are more distinct privileged roles than actual privileged users, creating a complex attack surface that explains why role sprawl undermines your security framework.
- Inactive roles remain exploitable: Roles assigned for temporary projects or testing are frequently left in place; attackers and misconfigurations can exploit these dormant roles long after their intended use.
- Role names lie: Descriptive names can be misleading—roles labeled “read-only” or “developer” often contain hidden permissions, making audits unreliable unless permissions are reviewed directly.
- Cross-system inconsistencies multiply risk: Different platforms handle role inheritance and scope differently, so a role that is safe in one system may be overly permissive in another, increasing why role sprawl undermines your security framework.
- Automation accelerates sprawl: Automated provisioning and IaC templates can propagate overly broad roles at scale, embedding privilege bloat across environments before anyone notices.
- Least privilege is hard to prove, easy to lose: Even organizations with a least-privilege policy often lack continuous measurement; without behavioral and access analytics, privileges drift back toward excessive access.
- Cleanup yields immediate security ROI: Removing or refining a small subset of overly broad roles often reduces privileged exposure far more than expensive perimeter controls, demonstrating why role sprawl undermines your security framework and why targeted role hygiene pays off quickly.
Definition and Causes
Role sprawl refers to the excessive creation of user roles within an organization. This phenomenon often occurs when companies develop overly specific or overlapping roles instead of utilizing broader, job-based roles. As a result, you may find yourself managing a complex web of access permissions that can lead to confusion and inefficiencies.
Several factors contribute to role sprawl:
Organizational Growth: As your organization expands, the need for more roles can arise. New projects and teams often lead to the creation of roles that may not align with existing structures.
Lack of Standardization: Without clear guidelines, teams may create roles independently, resulting in inconsistencies.
Overlapping Responsibilities: When roles overlap, it becomes challenging to determine who has access to what, leading to unnecessary complexity.
Role Explosion and Audit Complexity
Role explosion occurs when the number of roles in your system becomes unmanageable. This situation arises because organizations create new roles for every unique combination of access requirements. Consequently, you may face significant challenges during security audits.
Here are some ways role explosion complicates audits:
Complex Role Structure: A bloated role system makes it difficult to maintain consistent access rights. You may struggle to ensure that users have the appropriate permissions.
Inconsistent Roles: When roles lack standardization, security gaps can emerge. This inconsistency can lead to unauthorized access or data breaches.
Administrative Burden: Managing a large number of roles creates an endless cycle of maintenance and documentation. You may find that reviewing access rights becomes a daunting task.
Moreover, when audit tools do not communicate effectively, chaos can ensue during the audit preparation process. This disjointedness complicates documentation and data integrity, ultimately increasing the complexity of audits. In fact, 92% of organizations rely on three or more tools to gather audit evidence, yet only 39% of this process is automated. This reliance on manual tasks can lead to inefficiencies and errors.
Role Sprawl Impacts
Security Vulnerabilities
Role sprawl creates significant security vulnerabilities for your organization. When you have too many roles, you increase the attack surface, making it easier for malicious actors to exploit weaknesses. Each role can potentially grant access to sensitive data, and when roles overlap, unauthorized access becomes a real risk.
Increased Attack Surfaces
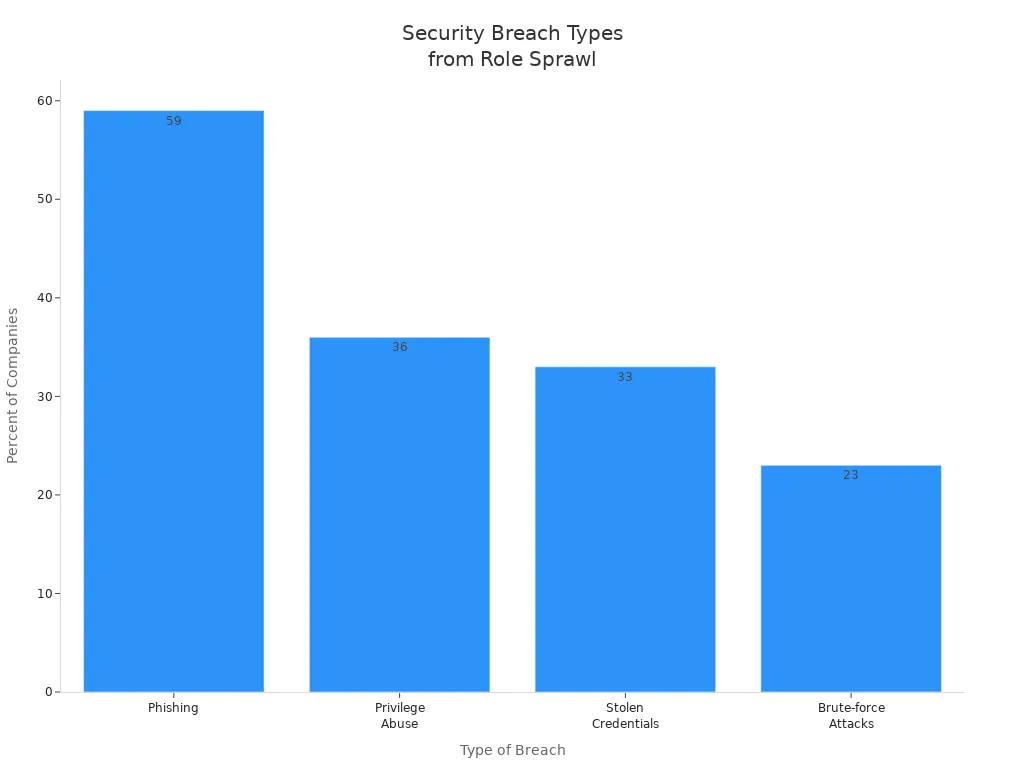
Data shows that unmanaged role sprawl leads to various types of breaches. For instance, 59% of companies report phishing attacks, while 36% face privilege abuse. The table below illustrates the percentage of companies affected by different types of breaches related to role sprawl:
Type of Breach | Percentage of Companies Affected |
|---|---|
Phishing | 59% |
Privilege Abuse | 36% |
Stolen Credentials | 33% |
Brute-force Attacks | 23% |
Case Studies of Breaches
Consider the case of a major financial institution that suffered a data breach due to excessive permissions granted to employees. Attackers exploited identities with excessive permissions, escalating their privileges and navigating through the cloud environment. This incident highlights how role sprawl can turn a minor compromise into a major breach, affecting not only the organization but also its customers.
Operational Inefficiencies
Role sprawl also leads to operational inefficiencies. When you manage too many roles, you create confusion and delays in decision-making. This fragmentation can hinder productivity and waste valuable resources.
Productivity Loss
Employees often struggle to navigate overlapping roles, leading to lost productivity. Research indicates that operational inefficiencies arise from:
Fragmentation and lack of integration between multiple tools or roles.
Siloed data and communication breakdowns.
Duplicated efforts and delays in decision-making.
These issues can overwhelm IT teams, making it difficult to manage systems effectively.
Resource Allocation Issues
When roles are not clearly defined, essential security functions may be overlooked. Teams might assume others are managing specific controls, leading to unclear escalation paths during incidents. This lack of clarity can slow down incident response times significantly.
Alert Fatigue
Another critical impact of role sprawl is alert fatigue among security teams. As the number of alerts increases, analysts may struggle to keep pace, leading to burnout and missed threats.
Overwhelming Security Alerts
Statistics reveal that 70% of SOC analysts experience burnout due to overwhelming alerts. Analysts often spend their shifts clearing low-value alerts, which leads to a cycle of reaction rather than analysis. The mental load increases as alerts pile up, creating confusion and inefficiencies.
Consequences of Desensitization
Alert fatigue directly undermines the goals of security tools. When analysts cannot keep pace with incoming alerts, genuine threats can slip through unnoticed. The tools may detect attacks, but human bandwidth becomes the bottleneck. This situation results in longer response times and missed critical alerts.
The table below summarizes the impacts of alert fatigue:
Impact of Alert Fatigue | Description |
|---|---|
Missed threats | Real attacks hide among false positives and get ignored. |
Delayed response | Growing queues extend time between alert generation and investigation. |
Inconsistent triage | Overwhelmed analysts make rushed decisions based on workload. |
Reduced investigation depth | Time pressure prevents thorough analysis of suspicious activity. |
Burnout and turnover | Chronic overload drives experienced analysts to leave security roles. |
Tool distrust | Teams lose confidence in products that generate more noise than signal. |
Mitigating Role Sprawl
Best Practices for Role Management
To effectively manage user roles and prevent role sprawl, you should adopt several best practices. These practices help streamline access management and enhance security. Here are some key strategies:
Best Practice | Description |
|---|---|
Adopt the Principle of Least Privilege | Grant users only the minimum permissions necessary for their tasks. This approach avoids over-permissioning and reduces security risks. |
Separate users, roles, and permissions | Treat permissions as individual units and roles as collections of permissions. This separation allows for flexibility and helps prevent role sprawl. |
Design roles around business functions | Create roles based on stable business functions rather than job titles. This design maintains consistency during organizational changes and reduces confusion. |
Plan for role exceptions, but minimize them | Anticipate edge cases and document exceptions. Strive to keep exceptions minimal and consolidate them back into standard roles whenever possible. |
Automate to reduce human error | Implement automation in role-based access control (RBAC) processes. Automation minimizes manual mistakes and operational overhead, enhancing both security and efficiency. |
Implementing Role-Based Access Control
Implementing role-based access control (RBAC) is a crucial step in mitigating role sprawl. Follow these key steps to create an effective RBAC system:
Dynamic roles that simplify and automate access assignment.
Attribute-Based Access Control (ABAC) to assign access dynamically based on user attributes.
Policy-Based Access Control (PBAC) to tie entitlements to business rules, ensuring that access aligns with organizational policies.
Periodic role review and clean-up to prevent the buildup of unnecessary roles over time.
Fundamental redesign of access models where legacy sprawl makes fixes impossible.
By implementing these steps, you can create a more manageable and secure access environment.
Regular Audits and Reviews
Conducting regular audits and reviews is essential for maintaining a secure access environment. Here are some recommendations for effective auditing:
Perform role audits at least annually. Organizations in higher-risk sectors should conduct audits more frequently.
Companies with high employee turnover may need to increase the frequency of audits to ensure permissions remain accurate.
Establish regular maintenance processes for access recertification. Schedule role audits to verify that permissions are both accurate and secure.
Regular audits not only help you identify and rectify role sprawl but also enhance compliance with security regulations. RBAC simplifies auditing by providing a clear audit trail of user access, which is vital for regulations like HIPAA, GDPR, and PCI DSS.
By following these strategies, you can effectively mitigate role sprawl and strengthen your security framework.
Streamlining Security Frameworks
Benefits of Reducing Role Sprawl
Reducing role sprawl offers numerous benefits that enhance your organization's security framework. A streamlined approach simplifies access management and minimizes risks. Here are some key advantages:
Cost Savings: By minimizing role sprawl, you can significantly reduce IT operational costs. A complex role structure often leads to unnecessary expenses, such as multiple license fees and maintenance costs. The table below illustrates how reducing role sprawl can save money:
Cost Factor | Explanation |
|---|---|
License Fees | Organizations often pay for multiple licenses due to tool sprawl, leading to unnecessary expenses. |
Maintenance Costs | More tools require higher maintenance, increasing overall operational costs. |
Redundant Functionalities | Overlapping features across tools complicate operations and inflate costs. |
Integration Overhead | Additional systems create complex integration challenges, consuming a large portion of IT budgets. |
Employee Productivity Losses | Technology friction leads to significant productivity losses, costing organizations thousands annually. |
Enhanced Efficiency: A streamlined security framework reduces operational inefficiencies. You can allocate resources more effectively, allowing your team to focus on critical tasks rather than managing a tangled web of roles.
Improved Compliance: Simplifying your role structure makes it easier to comply with regulations. A clear and concise framework helps you maintain accurate records and ensures that access rights align with compliance requirements.
Long-Term Security Posture Improvement
A streamlined security framework not only addresses immediate concerns but also strengthens your long-term security posture. By effectively managing roles, you enhance your resilience against emerging cyber threats. The NIST Cybersecurity Framework (CSF) 2.0 emphasizes several key enhancements that support this goal:
Key Enhancements in NIST CSF 2.0 | Description |
|---|---|
Supply Chain Risk Management (SCRM) | Emphasizes managing risks across the entire supply chain, addressing the rise of supply chain attacks. |
Identity Management and Access Control | Provides enhanced guidelines for managing identities and access, crucial for securing infrastructure. |
Measurement and Metrics | Offers improved guidelines for measuring cybersecurity effectiveness, aiding continuous assessment and enhancement. |
Integration with Privacy Framework | Aligns with NIST’s Privacy Framework for a holistic approach to security and privacy risks. |
Improved Guidance on Implementation Tiers | Clarifies guidance on implementation tiers for better assessment and goal setting. |
By adopting these enhancements, you can create a more resilient security framework. However, challenges may arise when streamlining your security framework. Common issues include operational inefficiencies, increased costs, and skill gaps among security staff. Addressing these challenges is crucial for maintaining a robust security posture.
Managing role sprawl is crucial for maintaining a strong security framework. You must recognize that excessive roles can lead to vulnerabilities and inefficiencies. Effective role management supports your security posture in several ways:
Benefit | Explanation |
|---|---|
Enforces least privilege | Ensures users have only the access required for their duties, minimizing potential damage. |
Reduces attack surface | Limits permissions to necessary roles, closing off entry points for attackers. |
Eases auditing and compliance | Simplifies proof of access controls, aiding in compliance with regulations like HIPAA and GDPR. |
Increases operational efficiency | Centralizes permissions, reducing manual work and speeding up response during security incidents. |
Lower administrative costs | Streamlines access management, leading to significant cost savings for organizations. |
By streamlining your security framework, you enhance your organization’s resilience against cyber threats.
Checklist: Handle Role Sprawl with Entra ID
Purpose: Prevent and remediate role sprawl to strengthen your identity and access management—why role sprawl undermines your security framework and how to address it with Entra ID.
- Inventory current roles and assignments
- Action: Export all built-in and custom roles, including Azure AD, Azure RBAC, and privileged roles.
- Why: Establish baseline for detecting sprawl and orphaned permissions.
- Owner: IAM/Admin Team | Priority: High | Status: ☐
- Map roles to business functions and least privilege
- Action: For each role, document the business purpose and required permissions; identify over-permissioned roles.
- Why: Ensure roles reflect actual job needs and enforce least privilege.
- Owner: Application Owners | Priority: High | Status: ☐
- Consolidate and rationalize duplicate or overlapping roles
- Action: Merge similar roles or remove unused/custom roles; replace with well-scoped roles where possible.
- Why: Reduces complexity and attack surface caused by role sprawl.
- Owner: IAM/Admin Team | Priority: Medium | Status: ☐
- Adopt role naming and classification standards
- Action: Define naming conventions, classification tags (e.g., admin, read-only, temp), and documentation requirements.
- Why: Makes roles discoverable and governance easier.
- Owner: Identity Governance Lead | Priority: Medium | Status: ☐
- Use Privileged Identity Management (PIM) for elevated roles
- Action: Require eligible assignment with approval, just-in-time activation, and time-bound access for all privileged roles.
- Why: Limits standing privileges and reduces persistent over-privilege.
- Owner: Security/IT Ops | Priority: High | Status: ☐
- Implement role-based access reviews
- Action: Schedule periodic access reviews in Entra ID for privileged and critical roles; involve owners and managers.
- Why: Regular reviews catch role creep and stale assignments.
- Owner: Resource Owners | Priority: High | Status: ☐
- Enforce entitlement management and access packages
- Action: Use Entra ID entitlement management to define cataloged access packages with approval workflows and expiration.
- Why: Centralizes access requests and prevents ad-hoc role proliferation.
- Owner: IAM/Admin Team | Priority: Medium | Status: ☐
- Automate provisioning and deprovisioning
- Action: Integrate HR systems and identity lifecycle automation to grant, modify, and revoke role assignments based on attributes and events.
- Why: Reduces manual role assignment errors and orphaned access.
- Owner: Identity Engineering | Priority: High | Status: ☐
- Monitor role assignment changes and anomalous activations
- Action: Configure diagnostic logs, alerts, and Sentinel analytics for role creation, assignment, and activation events.
- Why: Detects suspicious role sprawl activities early.
- Owner: Security Operations | Priority: High | Status: ☐
- Apply conditional access and separation of duties
- Action: Combine role controls with conditional access policies and enforce separation of duties for critical actions.
- Why: Mitigates risk even when roles are broad; prevents collusion and misuse.
- Owner: Security Architecture | Priority: High | Status: ☐
- Set expiration on temporary roles and access
- Action: Require all temporary or emergency role assignments to have automatic expiration and review triggers.
- Why: Prevents perpetual elevated access and accumulative sprawl.
- Owner: IAM/Admin Team | Priority: High | Status: ☐
- Enforce role change approval workflows
- Action: Require documented justification and multi-party approvals for creating or modifying roles.
- Why: Controls proliferation of custom roles and enforces governance.
- Owner: Change Control Board | Priority: Medium | Status: ☐
- Document and publish role usage policies
- Action: Maintain accessible documentation on role purpose, owners, and usage guidelines; train stakeholders.
- Why: Encourages responsible assignment and reduces ad-hoc role creation.
- Owner: IAM Governance | Priority: Medium | Status: ☐
- Perform periodic role entitlement and permissions reviews
- Action: Review role definitions for excessive permissions and update role scopes to minimize privilege.
- Why: Prevents role creep where roles gain permissions over time.
- Owner: Security/Audit | Priority: Medium | Status: ☐
- Establish KPIs and reporting on role sprawl
- Action: Track metrics: number of roles, unused roles, % of privileged accounts with permanent access, time-to-remediate findings.
- Why: Provides measurable progress on reducing role sprawl and improving security posture.
- Owner: Security Metrics | Priority: Low/Medium | Status: ☐
- Run simulated attack and cleanup exercises
- Action: Periodically simulate privilege escalation and conduct cleanup sprints to remove unnecessary roles and assignments.
- Why: Validates controls and uncovers hidden sprawl risks.
- Owner: Red Team/Blue Team | Priority: Medium | Status: ☐
Completion tips: start with a roles inventory, enforce PIM and entitlement management, automate lifecycle events, and monitor continuously—addressing why role sprawl undermines your security framework by design. Use this checklist to plan, assign owners, and track status until role sprawl is under control.
FAQ: cybersecurity tool sprawl and the cost of tool sprawl
What is role sprawl and how does it undermine your security framework?
Role sprawl occurs when users accumulate permissions beyond what their job requires, often because many organizations add new security products, new tools or ad hoc access instead of consolidating workflows. This increases the attack surface and creates security gaps, reduces visibility and control, complicates governance, and makes it harder for security teams to detect threats, thereby weakening the organization’s security posture.
How does role sprawl interact with cybersecurity tool sprawl and vendor sprawl?
Role sprawl and cybersecurity tool sprawl compound each other: many tools and vendors lead to fragmented identity and access policies across the security stack, and every new tool often introduces its own roles and permissions. That fragmentation makes it difficult to centralize governance, increases complexity of managing access across the enterprise security environment, and can lead to serious security risks and compliance failures.
Can role sprawl increase the cost of tool sprawl for my organization?
Yes. Role sprawl drives hidden costs by forcing SOC and security operations center teams to spend more time on manual access reviews, remediation, and incident investigations across many security products. Organizations find themselves paying for overlapping capabilities and duplicate licenses while losing cyber resilience and detection and response effectiveness, raising the overall cost of tool sprawl.
What visibility and control issues arise from role sprawl?
Role sprawl erodes visibility and control because it obscures who has access to what. When roles are inconsistent across tools, security teams cannot easily map endpoints, user privileges, or threat detection coverage, reducing the ability to detect lateral movement or privilege abuse. This lack of centralized visibility weakens detection and response and increases the likelihood of security breaches.
How does role sprawl affect compliance and governance efforts?
Role sprawl complicates compliance by making it harder to demonstrate least-privilege enforcement, segregation of duties, and consistent access policies across the security infrastructure. Fragmented roles across many security tools and vendors make audit trails incomplete or inconsistent, increasing the risk of non-compliance and regulatory penalties unless consolidation and governance improvements are applied.
What practical steps reduce role sprawl and improve overall security?
Start by inventorying roles across the security stack and mapping them to business workflows; retire redundant roles when consolidating tools or centralizing identity and access management. Implement role-based access control, automate provisioning and deprovisioning, and prioritize fewer tools that integrate well. These measures reduce cybersecurity tool sprawl, simplify threat detection and response, and strengthen the organization’s security posture.
How does automation help prevent role sprawl and improve detection and response?
Automation enforces consistent role assignments and removes manual errors that create sprawl. Automated identity lifecycle management, access reviews, and policy propagation across integrated security platforms reduce the number of manual changes that lead to sprawl for analysts, speed up response times in the SOC, and free cybersecurity professionals to focus on high-value threat detection and remediation.
When is consolidation or a move to a security platform the right approach?
Consolidation is appropriate when many tools overlap in function, causing fragmentation, vendor sprawl, and higher costs. Moving to a unified security platform or reducing the number of security products can restore visibility, reduce complexity of managing access and threats, and deliver real security outcomes like improved cyber resilience, faster detection and response, and better governance.
How should organizations evaluate new tools to avoid worsening role sprawl?
Evaluate whether a new tool integrates with existing identity and access controls, supports centralized provisioning, and reduces the number of tools in your security stack. Assess whether the tool fills an unmet need or duplicates capabilities, and require clear role and permission models. Prioritizing integration, fewer tools, and automation helps prevent sprawl in cybersecurity and reduces the impact of every new tool on the organization’s security posture.








