Stop Buying Security Tools: The Shocking ROI of One XDR Timeline
Drowning in alerts across M365, endpoints, and cloud apps? This video shows why your hybrid security stack is a Rube Goldberg machine that screams and still misses real attacks. You’ll see the four blind spots in Microsoft 365, identities, endpoints, and SaaS, and how attackers live in the gaps between your tools. Then we show how Microsoft Defender XDR fuses email, identity, device, and cloud telemetry into one incident story and one timeline, slashing dwell time, false positives, and audit pain. If you’re tired of swivel-chair investigations, alert fatigue, and paying three times for the same breach, this breakdown shows how consolidation flips Defender XDR from expense to savings.
In today's digital landscape, hybrid security falls short in effectively addressing modern threats. Organizations often struggle with fragmented tools that create complexity and confusion. This disjointed approach leads to missed threats and inadequate protection. You need a solution that seamlessly integrates various security measures. Microsoft Defender XDR offers a comprehensive answer. By unifying security tools and providing real-time threat detection, it empowers you to respond swiftly and effectively to evolving challenges.
Key Takeaways
- Hybrid security models create complexity and confusion, making it hard to manage multiple tools effectively.
- Organizations often miss threats due to alert fatigue, with many alerts going unaddressed daily.
- Defender XDR offers a unified solution that integrates various security tools, improving visibility and response times.
- Real-time detection in Defender XDR allows for quicker identification and containment of threats, reducing potential damage.
- Automating responses with Defender XDR minimizes manual work, allowing security teams to focus on strategic tasks.
- Transitioning to Defender XDR can lead to significant cost savings by reducing breach risks and improving operational efficiency.
- A unified security strategy enhances efficiency and yields a higher return on investment compared to fragmented solutions.
- Regularly updating security policies and training teams is essential to adapt to evolving threats and maximize Defender XDR's benefits.
Flaws of Hybrid Security
Complexity and Silos
Multiple Dashboards
Hybrid security models often lead to operational complexity. You may find yourself managing multiple dashboards from various vendors, each presenting different data formats and capabilities. This fragmentation complicates your security posture. The need to unify these siloed tools creates significant challenges. For instance, hybrid environments require you to extend security controls across both on-premises and cloud infrastructures. This dual responsibility can overwhelm your security teams, as they must enforce consistent policies and manage integration gaps.
- Integration Complexity: Unifying numerous security tools from different vendors can be technically demanding. Each tool has unique APIs and data formats, making it difficult to create a cohesive security platform.
- Visibility Gaps: Inconsistent telemetry formats can delay threat detection and response. A significant majority of organizations (75%) are expected to adopt hybrid cloud strategies by 2026, yet only 23% report having full visibility across their cloud environments.
Fragmented Tools
The reliance on siloed tools in hybrid security models increases the likelihood of inconsistent policies. This inconsistency can lead to missed threats and delayed incident responses. When security tools do not communicate effectively, you risk creating blind spots in your defenses. The complexity of managing these tools can result in a lack of comprehensive visibility, allowing attacks to exploit gaps between different domains.
Missed Threats
Alert Fatigue
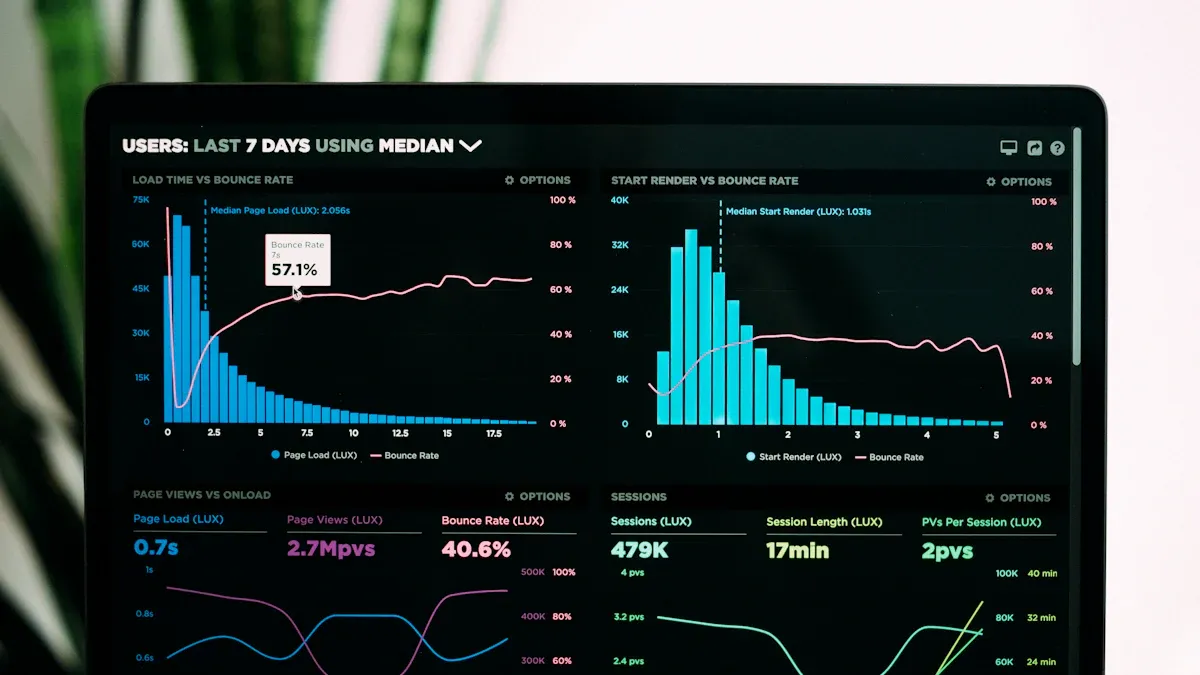
Alert fatigue is a critical issue in hybrid security setups. Organizations receive an average of nearly 3,000 security alerts daily. Despite a decline in alert volume over recent years, 63% of alerts still go unaddressed. This overwhelming volume can cause your security operations center (SOC) analysts to miss real threats. Research indicates that alert fatigue leads to increased mean time to detect (MTTD) and mean time to respond (MTTR), raising the risk of breaches.
- Impact on Response: Alert fatigue results in billions in triage costs and analyst burnout. As organizations deploy more detection tools, the problem worsens, creating exploitable security gaps.
Lack of Visibility
The lack of visibility in hybrid environments directly contributes to missed threats. Fragmented visibility increases the likelihood of inconsistent policies and delayed incident response. The reliance on multiple security tools can lead to difficulties in managing security across hybrid cloud environments. A recent report highlighted that organizations often struggle with overlapping functionalities and manual processes, which can result in missed threats.
| Evidence Type | Statistic |
|---|---|
| Insider Threat Frequency | 74% of organizations report an increase in insider attacks. |
| Damage Severity | Insider threats cause 20 times more damage than external threats. |
| Average Breach Cost | $4.5 million per breach. |
Why Defender XDR is Essential
Unified Security Solution
Integration of Tools
Defender XDR provides a unified security solution that integrates various security domains, addressing the gaps created by siloed tools. By consolidating email, identity, endpoints, and cloud applications, Defender XDR ensures that you have a cohesive approach to security. This integration allows you to manage threats more effectively across your entire digital landscape.
- Key Benefits of Integration:
- Eliminates gaps in protection across different security domains.
- Enhances visibility into potential threats, allowing for quicker detection and response.
- Reduces complexity by providing a single interface for monitoring and managing security.
Defender XDR's unified dashboard allows you to monitor the entire digital environment from one interface. This holistic view is crucial for effective incident tracking, enabling you to quickly identify and respond to threats without the distraction of switching between multiple dashboards.
| Feature | Benefit |
|---|---|
| Centralized Visibility | Provides a unified view of threats across all access points, improving detection accuracy. |
| Automated Investigation | Responds to threats at machine speed, significantly reducing response times. |
| Streamlined Incident Management | Eliminates the need to switch between multiple platforms, optimizing workflows for faster response. |
Comprehensive Incident Management
With Defender XDR, incident management becomes more efficient. The platform allows you to streamline workflows and customize responses to fit your organization's needs. This flexibility helps you tailor automated responses, whether you choose immediate isolation of threats or alerts for further investigation.
- Advantages of Comprehensive Management:
- Customizable workflows enhance the efficiency of incident response.
- Automated actions minimize manual intervention, allowing your team to focus on strategic tasks.
- Real-time protection ensures that threats are addressed promptly, reducing the risk of breaches.
Proactive Threat Response
Automated Actions
Defender XDR automates threat response by integrating data from various security sources. This capability allows for rapid containment and remediation actions, significantly reducing the need for manual intervention. In contrast to traditional hybrid security models, which often operate in isolation, Defender XDR streamlines the response process, making it more efficient.
- Impact of Automation:
- Rapid response times lead to fewer successful attacks.
- Automation reduces the burden on security teams, allowing them to allocate resources more effectively.
Real-Time Detection
Real-time detection is a cornerstone of Defender XDR's capabilities. The platform continuously monitors your environment, identifying threats as they emerge. This proactive approach enables you to respond swiftly, minimizing potential damage.
- Case Study Insights:
Case Study Detection Tool Initial Detection Time Containment Time No. of Endpoints Affected Ransomware Attack EDR 20 mins 2 hrs 150 Ransomware Attack XDR 10 mins 30 mins 50 Insider Threat EDR 15 mins 1 hr 2 GB Insider Threat XDR 5 mins 20 mins 0 GB
These statistics illustrate the effectiveness of Defender XDR in reducing detection and containment times, showcasing its superiority over traditional models.
Cost Implications of Hybrid Security
Hidden Costs
Inefficiencies in Response
Hybrid security environments often lead to hidden costs that can significantly impact your budget. Inefficiencies in response can arise from various factors, including the complexity of managing multiple tools and the need for constant monitoring. Research shows that 94% of organizations report waste in their public cloud spending. Nearly half estimate that over 25% of their budget is lost to inefficiencies.
- Common Inefficiencies:
- Hidden costs associated with cloud services, such as egress fees and API request fees, often go unnoticed.
- Managing hybrid environments requires multiple network connections, which can increase operational expenses.
| Hidden Cost | Description |
|---|---|
| Scalability Challenges | As security needs grow, traditional systems often require significant investments in additional hardware and complex configurations to expand, leading to unforeseen costs. |
| Ongoing Maintenance | Maintaining traditional systems incurs continuous costs for upkeep, data management, and potential upgrades, which can accumulate over time. |
| Employee Monitoring Expenses | The need for staff to monitor feeds increases labor costs and diverts resources from other tasks, adding to the overall expense of maintaining security. |
| Cybersecurity Concerns | Ensuring the security of traditional systems requires ongoing monitoring and updates, which can be costly and complex, contributing to higher operational expenses. |
| Software Licensing Fees | Traditional systems often involve recurring costs for software upgrades and additional features, which can significantly impact the total cost of ownership. |
Resource Drain
The resource drain associated with hybrid security can be substantial. Organizations often find themselves allocating more personnel and financial resources to manage disparate systems. This diversion can hinder your ability to focus on strategic initiatives.
- Key Statistics:
- 62% of IT leaders exceeded their cloud storage budgets in the past year, with 49% of total cloud object storage bills spent on fees rather than storage capacity.
- Organizations running multiple cloud services often face operational inefficiencies, leading to increased costs.
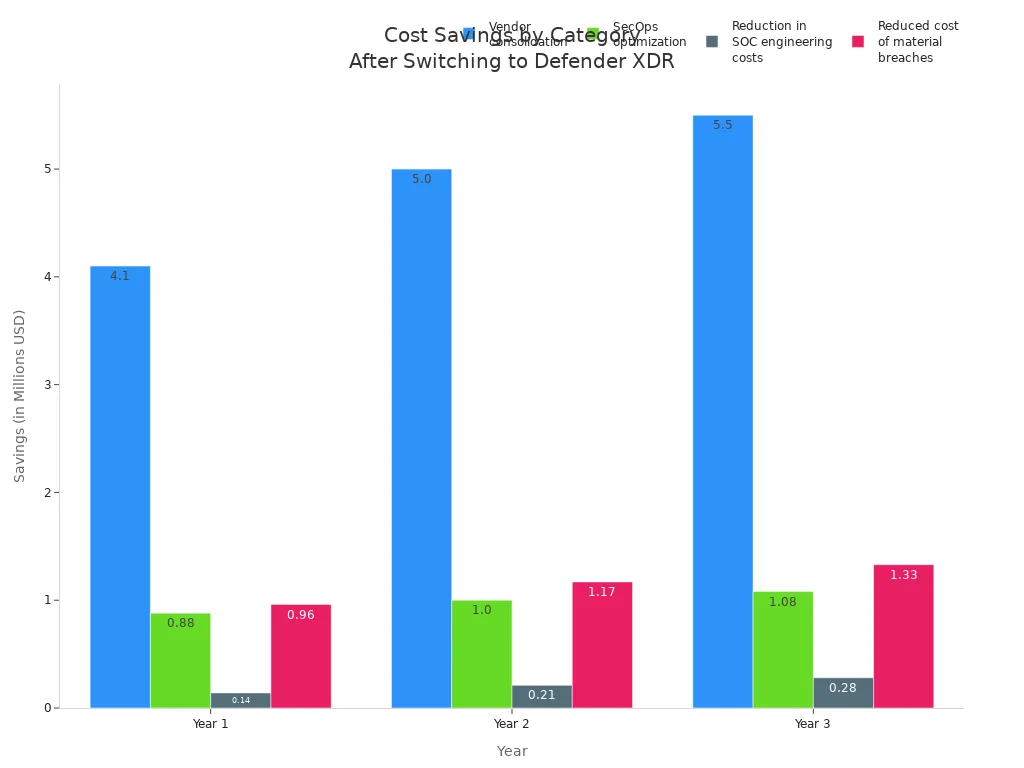
Savings with Defender XDR
Reduced Breach Risks
Switching to Microsoft Defender XDR can lead to significant savings by reducing breach risks. The platform's real-time detection capabilities allow for faster identification and containment of threats. This proactive approach minimizes the financial impact of security incidents.
| Contribution Aspect | Explanation |
|---|---|
| Faster MTTD/MTTR | AI-driven correlation and automated containment help detect and contain threats before they escalate. |
| Lower breach and ransomware risk | Early detection of anomalies limits lateral movement and reduces the impact of attacks. |
| Higher ROI on existing tools | XDR connects existing security platforms, enhancing their effectiveness without additional costs. |
Organizations that have transitioned to Defender XDR report substantial cost savings. Over three years, they realize a total risk-adjusted present value of approximately $17.8 million.
| Cost Saving Category | Year 1 Savings | Year 2 Savings | Year 3 Savings | Total Savings | Present Value |
|---|---|---|---|---|---|
| Vendor consolidation | $4.1M | $5.0M | $5.5M | $14.6M | $12.0M |
| SecOps optimization | $0.88M | $1.0M | $1.08M | $3.0M | $2.44M |
| Reduction in SOC engineering costs | $0.14M | $0.21M | $0.28M | $0.63M | $0.51M |
| Reduced cost of material breaches | $0.96M | $1.17M | $1.33M | $3.47M | $2.84M |
| Total | $6.1M | $7.4M | $8.2M | $21.7M | $17.8M |
Improved Efficiency
Defender XDR enhances operational efficiency by streamlining security processes. Automation reduces the need for manual intervention, allowing your team to focus on strategic tasks rather than routine monitoring. This shift not only saves time but also reduces the overall cost of security management.
- Benefits of Improved Efficiency:
- Organizations can achieve capabilities similar to larger enterprises without needing more staff.
- Automation allows for faster response times, leading to fewer successful attacks.
Success Stories with Defender XDR
Real-World Implementations
Industry Examples
Organizations across various sectors have successfully implemented Microsoft Defender XDR, showcasing its versatility and effectiveness. For instance, a leading financial institution transitioned from a fragmented security setup to Defender XDR. This shift allowed them to consolidate their security tools and streamline their incident response processes. Similarly, a healthcare provider reported significant improvements in threat detection and response times after adopting Defender XDR.
Measurable Benefits
The measurable benefits of implementing Defender XDR are compelling. Organizations have reported a remarkable Return on Investment (ROI) of 242% over three years. The Net Present Value (NPV) reached $12.6 million, demonstrating the financial advantages of this unified security solution.
| Benefit Description | Value |
|---|---|
| Return on Investment (ROI) over three years | 242% |
| Net Present Value (NPV) | $12.6 million |
| Mean Time to Acknowledge (MTTA) | Reduced from 30 minutes to 15 minutes |
| Mean Time to Resolve (MTTR) | Reduced from up to 3 hours to less than 1 hour |
| Total benefits to the business over three years | $17.8 million |
| Cost savings from vendor consolidation | Up to $12 million |
| Savings from SecOps optimization | $2.4 million |
| Reduced cost of material breaches | $2.8 million |
| Average time to payback on investment | Less than 6 months |
Lessons Learned
Common Pitfalls
Organizations transitioning to Defender XDR have encountered several common pitfalls. One major issue is the reluctance to replace legacy solutions. Many hesitate to move away from outdated security tools, which can lead to vulnerabilities. Concerns about secure integration with existing systems also pose challenges. Resource constraints can hinder effective deployment and management of new security tools.
| Common Pitfalls | Description |
|---|---|
| Reluctance to replace legacy solutions | Organizations often hesitate to move away from outdated security tools, which can lead to vulnerabilities. |
| Concerns about secure integration | There may be fears regarding how well new solutions will integrate with existing systems securely. |
| Resource constraints | Limited resources can hinder the effective deployment and management of new security tools. |
Best Practices
To maximize the benefits of Defender XDR, organizations should adopt best practices. Consolidating tools allows for budget reallocation towards innovation and hiring more analysts. A unified approach yields a higher ROI compared to fragmented solutions. Streamlined operations lead to reduced incident response efforts, saving approximately $2.4 million in SecOps labor over three years.
- Key Best Practices:
- Embrace a unified security strategy to enhance efficiency.
- Invest in training for security teams to leverage the full capabilities of Defender XDR.
- Regularly review and update security policies to align with evolving threats.
Future of Cybersecurity: Beyond Hybrid Models
Evolving Threat Landscape
Complexity of Attacks
The threat landscape continues to evolve, presenting significant challenges for hybrid security models. Cybercriminals now employ sophisticated techniques that traditional defenses struggle to counter. For instance, autonomous AI agents conduct multi-stage cyberattacks with minimal human intervention. These agents perform reconnaissance, discover vulnerabilities, and execute exploits at machine speed. As a result, organizations face an increasing number of attacks that bypass conventional security measures.
- Key Trends in Attack Complexity:
- AI-generated phishing campaigns have surged, with a 46% increase in AI-generated content.
- Ransomware attacks now often include data exfiltration and double extortion tactics.
- Advanced Persistent Threats (APTs) utilize tactics that traditional firewalls cannot detect.
Role of AI
AI plays a dual role in the evolving threat landscape. While it enhances security measures, it also empowers attackers. Organizations report that 72% face increased cyber risks linked to AI. This highlights the need for robust security solutions that can adapt to these new challenges.
| Statistic Description | Percentage | Year |
|---|---|---|
| Businesses experiencing frequent insider attacks | 48% | 2024 |
| Organizations reporting increased cyber risks linked to AI | 72% | 2024 |
| Companies that increased employee training efforts | 51% | 2024 |
Embracing Comprehensive Solutions
Importance of Integration
To combat the complexities of modern threats, organizations must embrace comprehensive security solutions. A unified approach, such as Microsoft Defender XDR, consolidates signals from various products, providing a comprehensive view of security across endpoints, identities, and cloud applications. This integration enhances detection and response capabilities, allowing you to respond to threats more effectively.
- Benefits of Integration:
- Centralized management improves visibility into security activities.
- Cross-product incident correlation enhances threat analysis.
- Automation of attack containment streamlines response efforts.
Continuous Improvement
Continuous improvement is essential in the face of evolving threats. Organizations must regularly review and update their security policies to adapt to new challenges. The Zero Trust Architecture (ZTA) exemplifies this approach by operating on the principle of "never trust, always verify." This framework ensures that every interaction is scrutinized, providing robust security in a distributed landscape.
- Key Considerations for Continuous Improvement:
- Address alert fatigue and blind spots caused by multiple security tools.
- Focus on operational efficiency to reduce wasted time and resources.
- Ensure compliance with regulations across hybrid environments.
By adopting a proactive stance and integrating comprehensive solutions, you can enhance your security posture and effectively navigate the complexities of the modern threat landscape.
Hybrid security models present significant challenges that hinder effective protection against modern threats. The complexity and fragmented visibility of these systems create vulnerabilities that attackers can exploit. Key issues include inconsistent policies and a shared responsibility model that complicates accountability. In contrast, adopting Defender XDR offers a unified solution that integrates threat data, automates responses, and provides comprehensive visibility. As Ulrike Baier emphasizes, true real-time protection is only achievable with Defender XDR. Transitioning to this advanced platform not only enhances your security posture but also delivers measurable ROI, making it a necessary step for organizations aiming to safeguard their assets effectively.
FAQ
What is Defender XDR?
Defender XDR is a unified security solution from Microsoft that integrates various security tools. It provides real-time threat detection and automated incident response, enhancing your organization's security posture.
How does Defender XDR improve incident response?
Defender XDR streamlines incident response by automating actions and providing a centralized dashboard. This integration allows your security team to respond quickly and effectively to threats.
Can Defender XDR reduce alert fatigue?
Yes, Defender XDR reduces alert fatigue by consolidating alerts from multiple sources into a single view. This helps you prioritize real threats and minimizes the chances of missing critical incidents.
Is Defender XDR suitable for hybrid environments?
Absolutely! Defender XDR is designed to work seamlessly across hybrid environments, integrating security measures for both on-premises and cloud infrastructures.
How does Defender XDR enhance visibility?
Defender XDR enhances visibility by providing a comprehensive view of security incidents across all domains. This integration allows you to track threats more effectively and respond promptly.
What are the cost benefits of using Defender XDR?
Using Defender XDR can lead to significant cost savings by reducing breach risks and improving operational efficiency. Organizations report a high return on investment after transitioning to this solution.
How can I implement Defender XDR in my organization?
To implement Defender XDR, assess your current security tools, plan for integration, and train your security team. Microsoft provides resources and support to facilitate a smooth transition.
What industries benefit most from Defender XDR?
Defender XDR benefits various industries, including finance, healthcare, and retail. Any organization facing complex security challenges can leverage its capabilities for enhanced protection.
🚀 Want to be part of m365.fm?
Then stop just listening… and start showing up.
👉 Connect with me on LinkedIn and let’s make something happen:
- 🎙️ Be a podcast guest and share your story
- 🎧 Host your own episode (yes, seriously)
- 💡 Pitch topics the community actually wants to hear
- 🌍 Build your personal brand in the Microsoft 365 space
This isn’t just a podcast — it’s a platform for people who take action.
🔥 Most people wait. The best ones don’t.
👉 Connect with me on LinkedIn and send me a message:
"I want in"
Let’s build something awesome 👊
1
00:00:00,000 --> 00:00:04,440
You've got six dashboards, three vendors, and a color-coded incident spreadsheet.
2
00:00:04,440 --> 00:00:09,600
Congrats, you built a Rube Goldberg machine that alerts loudly and catches little.
3
00:00:09,600 --> 00:00:12,520
Hybrid security isn't more tools.
4
00:00:12,520 --> 00:00:16,360
It's two overlapping attack surfaces pretending to be one.
5
00:00:16,360 --> 00:00:18,200
Here's what most people miss.
6
00:00:18,200 --> 00:00:21,200
Your silos hide four blind spots.
7
00:00:21,200 --> 00:00:25,720
M365 endpoints, identities, and cloud apps.
8
00:00:25,720 --> 00:00:31,320
I'll show you how attackers live in those gaps and how Defender XDR closes them by turning
9
00:00:31,320 --> 00:00:34,040
chaos into a single incident story.
10
00:00:34,040 --> 00:00:38,800
There's one capability that flips Defender XDR from expense to savings.
11
00:00:38,800 --> 00:00:40,200
Hold that thought.
12
00:00:40,200 --> 00:00:44,840
First, let's talk about why the silo habit keeps burning you.
13
00:00:44,840 --> 00:00:48,320
Why siloed security fails in hybrid environments?
14
00:00:48,320 --> 00:00:49,360
Foundation?
15
00:00:49,360 --> 00:00:50,680
Hybrid isn't new.
16
00:00:50,680 --> 00:00:52,040
It's just messier.
17
00:00:52,040 --> 00:00:57,480
You've got on-prem AD still limping along Azure AD doing the real work.
18
00:00:57,480 --> 00:01:03,080
Laptops phoning in from questionable Wi-Fi and SAS apps approved by someone who swears
19
00:01:03,080 --> 00:01:05,120
they ask security.
20
00:01:05,120 --> 00:01:09,480
That's four lanes of traffic, no stoplights, and you're shocked there are collisions.
21
00:01:09,480 --> 00:01:12,160
Now the part nobody likes to say out loud.
22
00:01:12,160 --> 00:01:15,320
Every separate tool creates context debt.
23
00:01:15,320 --> 00:01:18,600
Email sees a fish, identity flags, an odd sign in.
24
00:01:18,600 --> 00:01:21,320
Endpoint notices a weird power shell chain.
25
00:01:22,320 --> 00:01:26,480
Cloud app security waves at a rogue O-auth consent.
26
00:01:26,480 --> 00:01:28,600
Individually they look low.
27
00:01:28,600 --> 00:01:34,200
Together it's an active intrusion but your tools don't share memory so your team becomes
28
00:01:34,200 --> 00:01:40,800
the RAM, copying, pasting, reconciling timestamps, guessing which alert came first.
29
00:01:40,800 --> 00:01:42,800
That's where dwell time blooms.
30
00:01:42,800 --> 00:01:45,760
Alert fatigue isn't a feeling, it's attacks.
31
00:01:45,760 --> 00:01:49,920
When your SOC pivots between consoles you multiply toil.
32
00:01:49,920 --> 00:01:54,000
This burn cycles correlating what should already be fused.
33
00:01:54,000 --> 00:01:57,720
Sender to user to token to device to app.
34
00:01:57,720 --> 00:01:59,280
That manual stitching?
35
00:01:59,280 --> 00:02:03,000
Slow, inconsistent and easy to get wrong at 2am.
36
00:02:03,000 --> 00:02:04,560
The attacker needs one gap.
37
00:02:04,560 --> 00:02:06,960
You hand them forward, you think the fix is more data.
38
00:02:06,960 --> 00:02:09,280
No, the fix is one timeline.
39
00:02:09,280 --> 00:02:12,920
Silo tools are great at telling you something happened.
40
00:02:12,920 --> 00:02:18,000
They're terrible at telling you what happened in which order across domains.
41
00:02:18,000 --> 00:02:19,480
Sequence is the detection.
42
00:02:19,480 --> 00:02:22,560
Outed you're left with vibes and a backlog.
43
00:02:22,560 --> 00:02:24,520
Here's the financial part.
44
00:02:24,520 --> 00:02:30,400
Fragmentation inflates response time which inflates blast radius, which inflates cost.
45
00:02:30,400 --> 00:02:34,360
Meanwhile compliance turns into scavenger hunt theatre.
46
00:02:34,360 --> 00:02:37,640
Exporting CSVs from five places to prove you did anything.
47
00:02:37,640 --> 00:02:39,680
That's not security.
48
00:02:39,680 --> 00:02:42,600
That's paperwork.
49
00:02:42,600 --> 00:02:47,600
Everything clicked for me when I realized we aren't under resourced, we're over-fragmented.
50
00:02:47,600 --> 00:02:49,200
You don't need another console.
51
00:02:49,200 --> 00:02:53,000
You need one incident graph that understands relationships.
52
00:02:53,000 --> 00:02:55,760
The mailbox rule that hid the fish.
53
00:02:55,760 --> 00:02:58,600
The consent grant that gave persistence.
54
00:02:58,600 --> 00:03:01,480
The token that bypassed MFA.
55
00:03:01,480 --> 00:03:07,560
The endpoint process that pulled payloads and the cloud session that exfiltrated data all
56
00:03:07,560 --> 00:03:12,600
tied to the same user and device end to end.
57
00:03:12,600 --> 00:03:15,480
Now you might say we have smart analysts.
58
00:03:15,480 --> 00:03:16,480
Sure.
59
00:03:16,480 --> 00:03:20,560
So does the attacker and they aren't reconciling your alert IDs.
60
00:03:20,560 --> 00:03:24,800
They're moving laterally while you argue over which timestamp is UTC.
61
00:03:24,800 --> 00:03:30,480
Back in my day, Exchange 2003 taught us about hidden rules the hard way.
62
00:03:30,480 --> 00:03:33,200
Today it's the same trick with better marketing.
63
00:03:33,200 --> 00:03:36,200
Oauth consent instead of com add-ins.
64
00:03:36,200 --> 00:03:38,160
Different sticker, same mess.
65
00:03:38,160 --> 00:03:40,640
Market reality reflects this.
66
00:03:40,640 --> 00:03:44,320
XDR didn't show up because vendors needed a new acronym.
67
00:03:44,320 --> 00:03:49,000
It showed up because multi-tool correlation failed at human speed.
68
00:03:49,000 --> 00:03:53,640
Organizations learned the hard way that you can't manually glue identities, email endpoints
69
00:03:53,640 --> 00:03:57,440
and cloud apps and expect real-time detection.
70
00:03:57,440 --> 00:04:00,440
The growth in XDR adoption isn't hype.
71
00:04:00,440 --> 00:04:03,200
It's the penalty for ignoring causality.
72
00:04:03,200 --> 00:04:04,680
Here's the weird part.
73
00:04:04,680 --> 00:04:07,800
Silo teams mirror silo tools.
74
00:04:07,800 --> 00:04:10,960
Email team quarantines a message and moves on.
75
00:04:10,960 --> 00:04:13,880
Identity team lowers a risk state and moves on.
76
00:04:13,880 --> 00:04:16,320
One point team clears an alert and moves on.
77
00:04:16,320 --> 00:04:17,320
Nobody owns the narrative.
78
00:04:17,320 --> 00:04:23,040
So, the incident survives because the system that should be telling the story doesn't
79
00:04:23,040 --> 00:04:24,200
write one.
80
00:04:24,200 --> 00:04:28,120
What this actually means day to day, your containment isn't.
81
00:04:28,120 --> 00:04:30,640
You pulled the email but left the token alive.
82
00:04:30,640 --> 00:04:34,160
You cleaned the device but left the Oauth grant intact.
83
00:04:34,160 --> 00:04:37,640
You reset the password but kept the malicious mailbox rule.
84
00:04:37,640 --> 00:04:40,040
That's how reinfection loops happen.
85
00:04:40,040 --> 00:04:42,160
You feel haunted because you are.
86
00:04:42,160 --> 00:04:45,880
By artifacts you never saw in one place.
87
00:04:45,880 --> 00:04:49,040
Defender XDR treats hybrid as one organism.
88
00:04:49,040 --> 00:04:50,920
Not perfect but closer to the truth.
89
00:04:50,920 --> 00:04:57,200
It fuses signals from Microsoft 365, identity endpoints and cloud apps into a single incident
90
00:04:57,200 --> 00:04:58,200
with a causal chain.
91
00:04:58,200 --> 00:05:01,280
Okay, so basically it stops making you be the bus.
92
00:05:01,280 --> 00:05:06,440
The platform does the stitching, presents the sequence and this is key.
93
00:05:06,440 --> 00:05:10,520
Executes response across domains from the same pain.
94
00:05:10,520 --> 00:05:12,400
So IR isn't magic.
95
00:05:12,400 --> 00:05:16,840
Its policy-driven muscle memory you wish your tier ones had at 3am.
96
00:05:16,840 --> 00:05:22,520
I'm think of siloed security like guarding a building with four dormant who never speak.
97
00:05:22,520 --> 00:05:24,240
Each sees a piece.
98
00:05:24,240 --> 00:05:32,360
A forged ID, a propped door, a delivery to the wrong floor, a badge swipe at midnight.
99
00:05:32,360 --> 00:05:36,400
None of them calls it in because each event alone is me.
100
00:05:36,400 --> 00:05:39,600
An XDR is the radionet and the floor plan.
101
00:05:39,600 --> 00:05:45,080
Suddenly it's obvious there's an intruder on level 3 and you lock the elevators.
102
00:05:45,080 --> 00:05:46,480
Here's what most people miss.
103
00:05:46,480 --> 00:05:48,440
The cost of tooling is visible.
104
00:05:48,440 --> 00:05:50,920
The cost of correlation isn't.
105
00:05:50,920 --> 00:05:52,840
Until the breach report.
106
00:05:52,840 --> 00:05:57,960
You pay for dwell time, for overtime, for audits, for misdetections.
107
00:05:57,960 --> 00:06:00,520
Then you pay again to rip and replace.
108
00:06:00,520 --> 00:06:03,360
Or you consolidate the story up front.
109
00:06:03,360 --> 00:06:05,560
We'll get into the four blind spots next.
110
00:06:05,560 --> 00:06:12,160
M365 identities endpoints and cloud apps and I'll show you where attackers live rent free
111
00:06:12,160 --> 00:06:15,640
and how defender XDR evics them by default.
112
00:06:15,640 --> 00:06:19,520
And yes, that expense to savings switch.
113
00:06:19,520 --> 00:06:23,320
It turns on when incidents finally have one timeline.
114
00:06:23,320 --> 00:06:25,040
Blind spot one.
115
00:06:25,040 --> 00:06:31,800
Microsoft 365, email and collaboration telemetry without identity fusion.
116
00:06:31,800 --> 00:06:35,880
Let's start where most break and still begin, mail and collaboration.
117
00:06:35,880 --> 00:06:38,320
Fish lands, user clicks.
118
00:06:38,320 --> 00:06:42,000
You quarantine the message and pat yourself on the back.
119
00:06:42,000 --> 00:06:44,400
Except nothing meaningful changed.
120
00:06:44,400 --> 00:06:48,480
Because the blast moved from the mailbox to identity the moment the user handed over
121
00:06:48,480 --> 00:06:49,880
a token.
122
00:06:49,880 --> 00:06:50,880
Email is the door.
123
00:06:50,880 --> 00:06:51,880
The keys are elsewhere.
124
00:06:51,880 --> 00:06:54,200
Here's what most people miss.
125
00:06:54,200 --> 00:07:01,200
Microsoft 365 throws off great telemetry, delivery events, safe links, verdicts, mailbox
126
00:07:01,200 --> 00:07:07,560
rule changes, teams file shares, useful but in a silo it's just noise.
127
00:07:07,560 --> 00:07:13,520
You see fish delivered to five users, you yank it and declare containment.
128
00:07:13,520 --> 00:07:20,960
Meanwhile, one user consented to calendar assistant pro that wants red right across graph.
129
00:07:20,960 --> 00:07:25,800
The mailbox is quiet, but the attacker is now living on OAuth.
130
00:07:25,800 --> 00:07:31,000
Quarantine isn't containment, it's house cleaning after the thief left with your badge.
131
00:07:31,000 --> 00:07:35,280
Okay, so basically the simple version is you need the email story stitched to the sign
132
00:07:35,280 --> 00:07:37,320
in story and the device story.
133
00:07:37,320 --> 00:07:40,400
Defender XDR builds one incident out of that mess.
134
00:07:40,400 --> 00:07:46,080
The fish that hit outlook it shows up on the same timeline as the Azure AD sign in spike.
135
00:07:46,080 --> 00:07:51,360
The token issuance, the end point spawning a suspicious office child process and the cloud
136
00:07:51,360 --> 00:07:56,680
app session that started scraping files, same user, same device.
137
00:07:56,680 --> 00:08:01,920
One causal chain instead of four unrelated lows.
138
00:08:01,920 --> 00:08:03,520
Here's the weird part.
139
00:08:03,520 --> 00:08:09,280
In a classic setup, the mailbox team kills the message but never sees that the accounts
140
00:08:09,280 --> 00:08:12,560
refresh token is still valid.
141
00:08:12,560 --> 00:08:18,960
Identity flags, risky sign in, lowers it after a password reset and calls it a day.
142
00:08:18,960 --> 00:08:24,120
End point removes a macro dropper but has no clue the user's inbox now forwards invoices
143
00:08:24,120 --> 00:08:26,960
to an external Gmail via a hidden rule.
144
00:08:26,960 --> 00:08:29,160
You just built a re-infection loop.
145
00:08:29,160 --> 00:08:32,120
Clean device, dirty identity and vice versa.
146
00:08:32,120 --> 00:08:36,200
Defender XDR stops that loop because response spans domains.
147
00:08:36,200 --> 00:08:41,960
Auto IR can isolate the device that ran the unsigned office power shell chain, revoke
148
00:08:41,960 --> 00:08:49,000
the user's active sessions and tokens, kill the malicious OAuth consent and roll back mailbox
149
00:08:49,000 --> 00:08:52,760
rules without you playing swivel chair.
150
00:08:52,760 --> 00:08:57,360
The analysis is bound with the approvals where you want them but fast.
151
00:08:57,360 --> 00:09:03,080
The analyst clicks into the incident, sees the process tree, the email header, the sign
152
00:09:03,080 --> 00:09:10,520
in IPs, the consent details and the file activity it's not magic, it's a single memory of what
153
00:09:10,520 --> 00:09:12,000
happened.
154
00:09:12,000 --> 00:09:13,880
Think of it like this.
155
00:09:13,880 --> 00:09:18,520
Email only tools or bouncers who throw out the flyer, not the guy who already slipped
156
00:09:18,520 --> 00:09:25,520
inside.
157
00:09:25,520 --> 00:09:29,840
Same event, different outcome because sequence and scope are known.
158
00:09:29,840 --> 00:09:32,520
ROI isn't hand-wavy here.
159
00:09:32,520 --> 00:09:39,160
When email identity and endpoint are fused, false positives drop because weird email, without
160
00:09:39,160 --> 00:09:42,240
weird login, stays alo.
161
00:09:42,240 --> 00:09:46,920
Trish time shrinks because you aren't guessing which alert came first.
162
00:09:46,920 --> 00:09:52,520
But it's stop being scavenger hunts because the incident record already shows mailbox actions,
163
00:09:52,520 --> 00:09:57,160
token revocations and device containment with timestamps.
164
00:09:57,160 --> 00:10:01,080
MicroStory you've lived, quarantined fish but the token lived.
165
00:10:01,080 --> 00:10:07,280
User keeps getting hit, you rotate passwords, wipe the laptop and the unknown app still hoovers
166
00:10:07,280 --> 00:10:09,480
mail via graph.
167
00:10:09,480 --> 00:10:14,120
With Defender XDR, the same incident flags the consent shows who granted it and offers
168
00:10:14,120 --> 00:10:21,120
one click revoc plus session kill, session dies, persistence dies, device isolates if needed.
169
00:10:21,120 --> 00:10:22,960
The ghost stops knocking.
170
00:10:22,960 --> 00:10:28,040
Email is the door sure, but without identity fusion and endpoint context, you're guarding
171
00:10:28,040 --> 00:10:32,520
the foyer while the data walks out the loading dock.
172
00:10:32,520 --> 00:10:37,080
Defender XDR ties the handles together and locks the loading dock too.
173
00:10:37,080 --> 00:10:38,920
Blindspot 2.
174
00:10:38,920 --> 00:10:43,640
Identities AAD signals without endpoint and app context.
175
00:10:43,640 --> 00:10:47,480
Identities are the keys and attackers don't brute force the lock anymore.
176
00:10:47,480 --> 00:10:50,480
They borrow the keys and make copies.
177
00:10:50,480 --> 00:10:57,480
Consent grants, token theft, MFA fatigue, quiet, durable, annoying to unwind if you only stare
178
00:10:57,480 --> 00:10:59,680
at Azure AAD risk.
179
00:10:59,680 --> 00:11:06,120
Here's what most people miss as your AAD will dutifully flag risky sign-ins.
180
00:11:06,120 --> 00:11:12,680
Impossible travel, new device, anonymous IP, useful but alone its half a sentence.
181
00:11:12,680 --> 00:11:18,640
As the device healthy, did office spawn power shell, did a productivity app just get graph
182
00:11:18,640 --> 00:11:21,880
red, right from the same account?
183
00:11:21,880 --> 00:11:26,040
In a silo, you reset a password and pat yourself on the back.
184
00:11:26,040 --> 00:11:31,720
Except refresh tokens live, OAuth consent lives and the attacker lives right along with them.
185
00:11:31,720 --> 00:11:38,240
Okay, so basically, the simple version is identity without endpoint and app context lies
186
00:11:38,240 --> 00:11:39,560
to you.
187
00:11:39,560 --> 00:11:43,640
You see, user risk lowered, but you didn't kill active sessions.
188
00:11:43,640 --> 00:11:48,200
You see MFA satisfied, but the token was stolen from a compromised device that still runs
189
00:11:48,200 --> 00:11:50,200
unsigned binaries at Logan.
190
00:11:50,200 --> 00:11:54,880
You see new app consented, but you don't tie it to yesterday's fish that dropped a malicious
191
00:11:54,880 --> 00:11:56,680
calm add-in.
192
00:11:56,680 --> 00:12:01,560
You get the picture, clean score, dirty reality.
193
00:12:01,560 --> 00:12:06,720
Defender XDR fuses the stream so the identity story finally has a plot.
194
00:12:06,720 --> 00:12:11,920
The risky sign in isn't just a blip, it's stitched to device posture, process lineage,
195
00:12:11,920 --> 00:12:14,360
and cloud app behavior.
196
00:12:14,360 --> 00:12:21,000
The same incident shows, suspicious token issuance, the endpoint that handled it, the process tree
197
00:12:21,000 --> 00:12:26,040
that harvested the browser cookie and the OAuth app that immediately started scraping
198
00:12:26,040 --> 00:12:31,920
SharePoint, one timeline, one user, one device, no guessing.
199
00:12:31,920 --> 00:12:37,160
This is the weird part, most orgs try to fix identity by tightening conditional access
200
00:12:37,160 --> 00:12:39,000
and calling it a day.
201
00:12:39,000 --> 00:12:42,480
Good, except it's a gate, not a cleanup crew.
202
00:12:42,480 --> 00:12:48,560
If the tokens are already minted, policy changes are future-facing, the mess is present tense.
203
00:12:48,560 --> 00:12:55,080
Defender XDR closes the gap with automatic token revocation, session invalidation, and
204
00:12:55,080 --> 00:13:00,200
when policy allows, device isolation, all from the same incident pain.
205
00:13:00,200 --> 00:13:06,560
You don't pray the sign in risk drops, you force it to by removing the attacker's oxygen.
206
00:13:06,560 --> 00:13:12,480
Specific example, you get impossible travel at 0214 and a Windows device executes an unsigned
207
00:13:12,480 --> 00:13:17,120
binary at 0216 tied to the same user context.
208
00:13:17,120 --> 00:13:23,480
In a silo, two consoles, two teams endless slack with XDR, those correlate instantly.
209
00:13:23,480 --> 00:13:29,320
Auto IR can revoke the refreshed token, kill active sessions, mark the user risky, suggest
210
00:13:29,320 --> 00:13:33,040
conditional access hardening and contain the device pending review.
211
00:13:33,040 --> 00:13:38,680
The mailbox rules and OAuth consents tied to that account appear in the same view.
212
00:13:38,680 --> 00:13:43,000
You clear persistence in one pass, not three.
213
00:13:43,000 --> 00:13:48,400
Think of identity only tools like a security guard watching badge swipes on a screen.
214
00:13:48,400 --> 00:13:49,400
Useful.
215
00:13:49,400 --> 00:13:55,080
But if they never see the camera feed from the stairwell or the shipping dock logs, they'll
216
00:13:55,080 --> 00:13:57,880
keep waving through a cloned badge.
217
00:13:57,880 --> 00:14:01,560
Defender XDR is the shared feed plus the intercom.
218
00:14:01,560 --> 00:14:06,440
You see the badge clone, the stairwell movement, and the door wedge on level 4, and you lock
219
00:14:06,440 --> 00:14:08,440
the doors in the right order.
220
00:14:08,440 --> 00:14:12,240
ROI shows up as fewer wild goose chases.
221
00:14:12,240 --> 00:14:18,800
A lone, risky sign in that doesn't correlate to device anomalies stays low.
222
00:14:18,800 --> 00:14:21,400
Quietly, auto resolved.
223
00:14:21,400 --> 00:14:23,120
A real blast.
224
00:14:23,120 --> 00:14:29,600
Risky sign in plus browser token theft plus suspicious OAuth activity jumps to the top,
225
00:14:29,600 --> 00:14:32,400
already packaged with recommended actions.
226
00:14:32,400 --> 00:14:40,000
Fewer tickets, shorter timelines, clean evidence for audits without exporting half the tenant.
227
00:14:40,000 --> 00:14:43,440
You don't solve identity by yelling at users about MFA.
228
00:14:43,440 --> 00:14:49,360
You solve it by collapsing identity, device, and app into one narrative and cutting power
229
00:14:49,360 --> 00:14:53,040
to the attacker's session, not just changing the password.
230
00:14:53,040 --> 00:14:59,600
That's the identity fusion defender XDR forces, and it stops the reinfection loop cold.
231
00:14:59,600 --> 00:15:01,240
Blind spot 3.
232
00:15:01,240 --> 00:15:02,240
Endpoints.
233
00:15:02,240 --> 00:15:06,320
EDR events without SAS and identity context.
234
00:15:06,320 --> 00:15:09,000
Endpoints are where the mess gets loud.
235
00:15:09,000 --> 00:15:10,000
Ransomware.
236
00:15:10,000 --> 00:15:11,320
LOL bins.
237
00:15:11,320 --> 00:15:14,240
Unsigned binaries doing yoga at startup.
238
00:15:14,240 --> 00:15:16,040
EDR is good at that noise.
239
00:15:16,040 --> 00:15:17,480
But here's the catch.
240
00:15:17,480 --> 00:15:22,680
An endpoint can look clean, while the identity in SAS layer are filthy.
241
00:15:22,680 --> 00:15:24,400
You reinstall windows.
242
00:15:24,400 --> 00:15:27,920
The attacker keeps the refresh token in the OAuth foothold.
243
00:15:27,920 --> 00:15:30,200
You start the loop again next Tuesday.
244
00:15:30,200 --> 00:15:33,400
OK, so basically, processes don't tell the whole story.
245
00:15:33,400 --> 00:15:39,640
EDR sees command prompt, spawning power shell, power shell touching LSS.
246
00:15:39,640 --> 00:15:42,080
Maybe a suspicious scheduled task.
247
00:15:42,080 --> 00:15:43,080
Useful.
248
00:15:43,080 --> 00:15:46,840
Except it doesn't tell you the blast started with a fish, escalated through a consent grant
249
00:15:46,840 --> 00:15:50,000
and pivoted to SharePoint with a live browser token.
250
00:15:50,000 --> 00:15:53,640
Without SAS and identity context, you're treating symptoms.
251
00:15:53,640 --> 00:15:55,080
The infection lives upstream.
252
00:15:55,080 --> 00:15:57,080
Here's what most people miss.
253
00:15:57,080 --> 00:16:00,320
EDR alerts are often the middle of the movie.
254
00:16:00,320 --> 00:16:04,200
The opening scene is the user clicking "Except" on a two-friendly app.
255
00:16:04,200 --> 00:16:10,560
The ending is data walking out through cloud APIs, while your agent congratulates itself for
256
00:16:10,560 --> 00:16:11,920
killing a DLL.
257
00:16:11,920 --> 00:16:15,280
In a silo, you close the EDR ticket and celebrate.
258
00:16:15,280 --> 00:16:21,440
Meanwhile, the attacker reuses the token on a different machine, with the same identity
259
00:16:21,440 --> 00:16:24,040
and your logs look normal.
260
00:16:24,040 --> 00:16:27,040
Defender XDR drags the whole plot into one window.
261
00:16:27,040 --> 00:16:34,160
The unified incident graph ties process events to the user, the token, the mailbox rules,
262
00:16:34,160 --> 00:16:35,800
and the cloud sessions.
263
00:16:35,800 --> 00:16:41,560
That unsigned binary, you see it on the same timeline as the risky sign in the graph calls
264
00:16:41,560 --> 00:16:43,480
and the team's file access.
265
00:16:43,480 --> 00:16:47,940
Now you know if the endpoint event is a fire or just smoke from a fire that already moved
266
00:16:47,940 --> 00:16:48,940
upstairs.
267
00:16:48,940 --> 00:16:50,840
Here's the counter-intuitive part.
268
00:16:50,840 --> 00:16:54,120
Sometimes the right move isn't to keep hammering the endpoint.
269
00:16:54,120 --> 00:16:58,400
It's to cut the oxygen at identity and SAS first.
270
00:16:58,400 --> 00:17:04,840
With XDR, auto-IR can revoke refresh tokens, kill active sessions, and revoke a shady
271
00:17:04,840 --> 00:17:09,120
OAuth grant before you even finish reading the process tree.
272
00:17:09,120 --> 00:17:12,000
Then you contain the device, order matters.
273
00:17:12,000 --> 00:17:19,080
You stop the reinfection loop by breaking the session state, not just deleting the executable.
274
00:17:19,080 --> 00:17:20,880
Specific example you'll recognize.
275
00:17:20,880 --> 00:17:25,560
EDR flags office spawning power shell with encoded commands.
276
00:17:25,560 --> 00:17:28,080
In isolation you block isolate scan.
277
00:17:28,080 --> 00:17:34,160
But in XDR, that event correlates with yesterday's calendar helper 365 consent and a sudden spike
278
00:17:34,160 --> 00:17:37,720
in SharePoint download activity that's not a drive-by macro.
279
00:17:37,720 --> 00:17:39,640
That's an established persistence channel.
280
00:17:39,640 --> 00:17:45,560
From the same incident pane, you revoke consent, kill sessions, rollback mailbox rules, and
281
00:17:45,560 --> 00:17:48,200
quarantine the files that left the machine.
282
00:17:48,200 --> 00:17:52,200
The device goes into containment while identity gets cleaned.
283
00:17:52,200 --> 00:17:55,240
One pass, no swivel chair.
284
00:17:55,240 --> 00:17:59,280
Think of EDR only like listening to footsteps in one hallway.
285
00:17:59,280 --> 00:18:02,120
You hear noise, you chase it, you silence it.
286
00:18:02,120 --> 00:18:07,240
But the burglar is using the elevator and the roof access you never monitored.
287
00:18:07,240 --> 00:18:11,120
The XDR hands you the floor plan and the elevator controls.
288
00:18:11,120 --> 00:18:12,880
You don't sprint room to room.
289
00:18:12,880 --> 00:18:16,480
You lock floors, stop the lift, then clear the hall.
290
00:18:16,480 --> 00:18:19,040
ROI shows up fast.
291
00:18:19,040 --> 00:18:24,480
Cross domain correlation means fewer critical device alerts that are actually benign without identity
292
00:18:24,480 --> 00:18:25,480
anomalies.
293
00:18:25,480 --> 00:18:30,880
Your cue shrinks because the platform dedupes the same root cause across 10 machines into
294
00:18:30,880 --> 00:18:32,440
one incident.
295
00:18:32,440 --> 00:18:37,120
And audits stop asking for screenshots from six consoles.
296
00:18:37,120 --> 00:18:43,120
The incident record already shows token revocations, session kills, device containment, and file
297
00:18:43,120 --> 00:18:46,160
governance in sequence.
298
00:18:46,160 --> 00:18:47,520
Clean endpoint.
299
00:18:47,520 --> 00:18:50,200
Dirty identity was yesterday's headache.
300
00:18:50,200 --> 00:18:55,040
With Defender XDR you clean both in order so it stays clean.
301
00:18:55,040 --> 00:18:56,480
Endpoints aren't islands.
302
00:18:56,480 --> 00:18:58,040
They're bridges.
303
00:18:58,040 --> 00:19:02,160
Close the bridge at both ends and the attacker finally runs out of road.
304
00:19:02,160 --> 00:19:03,160
Blind spot for.
305
00:19:03,160 --> 00:19:08,280
Cloud apps, SAS and shadow it, without endpoint identity linkage.
306
00:19:08,280 --> 00:19:09,560
Now the highway.
307
00:19:09,560 --> 00:19:10,560
Cloud apps.
308
00:19:10,560 --> 00:19:16,240
SAS is where your data actually lives and where shadow IT multiplies like rabbits the
309
00:19:16,240 --> 00:19:19,720
minute finance discovers a freemium export button.
310
00:19:19,720 --> 00:19:25,560
You think you're watching it because your TSB spits out oothle alerts and file shares.
311
00:19:25,560 --> 00:19:29,120
Accept it's yelling into a void if it can't touch identity and devices.
312
00:19:29,120 --> 00:19:33,320
That's how X-Fill happens at noon while everyone's staring at a green dashboard.
313
00:19:33,320 --> 00:19:35,000
Here's what most people miss.
314
00:19:35,000 --> 00:19:39,120
Caspi alone sees the permission, not the person.
315
00:19:39,120 --> 00:19:44,640
It flags high risk oothle grant, but doesn't know the token came from a machine with a sketchy
316
00:19:44,640 --> 00:19:49,360
browser extension and an unsigned binary at Logon.
317
00:19:49,360 --> 00:19:54,120
It sees unusual download rate from SharePoint, but can't tell you it started five minutes
318
00:19:54,120 --> 00:19:58,040
after a fish and coincided with a refreshed token mint.
319
00:19:58,040 --> 00:20:03,400
You end up writing a stern email about responsible app usage while data walks out through graph
320
00:20:03,400 --> 00:20:05,480
politely with keys you issued.
321
00:20:05,480 --> 00:20:11,920
OK, so basically cloud telemetry without identity and endpoint context is a fun house mirror.
322
00:20:11,920 --> 00:20:17,080
The simple version is you need to tie app sessions to the user, the device posture and the
323
00:20:17,080 --> 00:20:20,200
identity session state in one incident.
324
00:20:20,200 --> 00:20:24,940
Defender XDR does that because defender for cloud apps lives inside the same incident
325
00:20:24,940 --> 00:20:26,420
graph.
326
00:20:26,420 --> 00:20:32,300
No-auth consent session governance file activity, they're not separate alerts, they're nodes
327
00:20:32,300 --> 00:20:37,220
on the same chain with the token, the sign in and the process tree.
328
00:20:37,220 --> 00:20:42,420
Here's the weird part, the fastest win in cloud security isn't another discovery scan.
329
00:20:42,420 --> 00:20:44,060
Its response in the right order.
330
00:20:44,060 --> 00:20:50,900
With Defender XDR, you can revoke the malicious app consent, kill active sessions, and if the
331
00:20:50,900 --> 00:20:55,460
source device is dirty, isolate it all from the incident pane.
332
00:20:55,460 --> 00:21:00,420
In quarantine or label the files that already left, you don't draft a ticket for three teams.
333
00:21:00,420 --> 00:21:06,860
You pull the plug in one place, specific example, a time tracking app asks for offline access
334
00:21:06,860 --> 00:21:08,460
and files.
335
00:21:08,460 --> 00:21:10,220
Read right to all.
336
00:21:10,220 --> 00:21:17,100
In a silo, CASB flags it, someone promises to review and nothing changes.
337
00:21:17,100 --> 00:21:23,660
In XDR, that consent is linked to last night's odd sign in and a device running an unsigned
338
00:21:23,660 --> 00:21:27,380
helper in the user profile.
339
00:21:27,380 --> 00:21:35,500
AutoIR suggests revoke consent, kill sessions, mark the user risky and contain the device.
340
00:21:35,500 --> 00:21:37,220
You click "Approve."
341
00:21:37,220 --> 00:21:44,260
The falsehood closes before you debate the app's business value, Shadow IT, same story.
342
00:21:44,260 --> 00:21:49,500
A user wires up a third party storage connector to export monthly reports.
343
00:21:49,500 --> 00:21:52,060
In isolation it's productivity.
344
00:21:52,060 --> 00:21:58,100
In XDR, you see it correlates with abnormal download spikes and a browser token lifted
345
00:21:58,100 --> 00:22:00,420
from a machine with a bad extension.
346
00:22:00,420 --> 00:22:04,940
You revoke the connector's token and force session controls and quarantine the exported
347
00:22:04,940 --> 00:22:06,700
files pending review.
348
00:22:06,700 --> 00:22:10,980
No swivel chair, no hunting for which admin portal owns the problem.
349
00:22:10,980 --> 00:22:16,340
Think of CASB only, like watching the loading dock with no badge list and no camera on the
350
00:22:16,340 --> 00:22:17,620
hallway.
351
00:22:17,620 --> 00:22:19,220
You see boxes leaving.
352
00:22:19,220 --> 00:22:21,620
You don't know who carried them or if they had keys.
353
00:22:21,620 --> 00:22:26,420
Defender XDR gives you the badge list, the hallway camera and the lock controls.
354
00:22:26,420 --> 00:22:28,580
You don't lock the theft, you stop it live.
355
00:22:28,580 --> 00:22:35,140
ROI shows up as fewer connectors, say no training and audits that stop chewing your weekends.
356
00:22:35,140 --> 00:22:40,660
One platform, one incident record, OAuth grants documented sessions killed, devices contained
357
00:22:40,660 --> 00:22:45,740
files governed with timestamps, toolsprongles downs, sodas your blood pressure.
358
00:22:45,740 --> 00:22:51,500
The ROI equation, consolidation beats complexity, proof and payback.
359
00:22:51,500 --> 00:22:54,980
Here's the boring math that actually decides budgets.
360
00:22:54,980 --> 00:22:58,220
Toolsprong burns money in three places.
361
00:22:58,220 --> 00:23:00,820
People plumbing and panic.
362
00:23:00,820 --> 00:23:04,580
Defender XDR pays back by collapsing all three.
363
00:23:04,580 --> 00:23:08,180
People, one console, one incident story.
364
00:23:08,180 --> 00:23:11,900
Analysts stop copy pasting across vendors and start closing cases.
365
00:23:11,900 --> 00:23:14,820
Alert to dop and correlation, cut the cue.
366
00:23:14,820 --> 00:23:17,260
Auto IR handles the muscle memory.
367
00:23:17,260 --> 00:23:20,140
Lean teams suddenly look staffed.
368
00:23:20,140 --> 00:23:21,140
Plumbing.
369
00:23:21,140 --> 00:23:25,660
Native Microsoft integrations mean fewer connectors stitched together with three scripts
370
00:23:25,660 --> 00:23:26,860
and a prayer.
371
00:23:26,860 --> 00:23:28,180
Less maintenance.
372
00:23:28,180 --> 00:23:29,900
Faster onboarding.
373
00:23:29,900 --> 00:23:33,260
Training shrinks from six products to one stack.
374
00:23:33,260 --> 00:23:34,340
Panic.
375
00:23:34,340 --> 00:23:40,380
When an incident already shows the causal chain and offers actions, revoke tokens, kill sessions,
376
00:23:40,380 --> 00:23:43,940
isolate device, roll back mailbox rules.
377
00:23:43,940 --> 00:23:47,100
You shrink response time and blast radius.
378
00:23:47,100 --> 00:23:51,340
That's real money.
379
00:23:51,340 --> 00:23:59,820
If you're already paying for Microsoft 365 and Azure, you're halfway there.
380
00:23:59,820 --> 00:24:05,820
Consolidation removes duplicate licenses, CM gymnastics for basics and the weekly scavenger
381
00:24:05,820 --> 00:24:08,180
hunt for audit artifacts.
382
00:24:08,180 --> 00:24:13,980
Typical payback lives in the 12 to 18 month window, not heroic, just cause and effect.
383
00:24:13,980 --> 00:24:20,420
The expense to saving switch flips on native cross domain incident correlation.
384
00:24:20,420 --> 00:24:23,980
One timeline replaces four tickets and three meetings.
385
00:24:23,980 --> 00:24:29,380
That's the dividend, handling objections without the drama, counter arguments resolved.
386
00:24:29,380 --> 00:24:30,380
Vendor lock in.
387
00:24:30,380 --> 00:24:35,660
Sure, you're already locked into M365 for identities, mail and files.
388
00:24:35,660 --> 00:24:37,660
Native beats, glue code.
389
00:24:37,660 --> 00:24:42,500
XDR still feeds Sentinel or Splunk for compliance and forensics.
390
00:24:42,500 --> 00:24:43,500
We have a seam.
391
00:24:43,500 --> 00:24:44,500
Great.
392
00:24:44,500 --> 00:24:45,500
Keep it.
393
00:24:45,500 --> 00:24:48,660
Let XDR do real time detection and response.
394
00:24:48,660 --> 00:24:52,900
Stop forcing seam to impersonate an EDR plus KSP plus SOAR.
395
00:24:52,900 --> 00:24:56,820
To complex, complexity is the silos.
396
00:24:56,820 --> 00:25:00,540
Pre-built connectors, one console, Auto IR with approvals.
397
00:25:00,540 --> 00:25:02,980
Fewer moving parts.
398
00:25:02,980 --> 00:25:05,220
We'll lose control.
399
00:25:05,220 --> 00:25:07,260
Automation is policy bound.
400
00:25:07,260 --> 00:25:11,220
You choose what auto executes and what asks first.
401
00:25:11,220 --> 00:25:13,220
We can't afford it.
402
00:25:13,220 --> 00:25:14,500
You're already paying.
403
00:25:14,500 --> 00:25:19,980
Alert fatigue, staffing churn, breach cleanup, audit overtime.
404
00:25:19,980 --> 00:25:22,980
Consolidation trims the mess and the bill.
405
00:25:22,980 --> 00:25:28,260
The mandatory correction, hybrid security fails when your tools don't talk.
406
00:25:28,260 --> 00:25:34,140
Defender XDR forces one incident language with one timeline and cross domain actions.
407
00:25:34,140 --> 00:25:35,140
That's the fix.
408
00:25:35,140 --> 00:25:39,660
If you want compliance depth without giving up real time speed, watch the breakdown on
409
00:25:39,660 --> 00:25:42,780
wiring defender XDR into your seam.
410
00:25:42,780 --> 00:25:46,020
Sentinel, Splunk, whatever you already run.
411
00:25:46,020 --> 00:25:51,340
Subscribe so you don't get stuck rebuilding the same wet cardboard stack next quarter.
412
00:25:51,340 --> 00:25:52,860
Pick structure over entropy now.

Founder of m365.fm, m365.show and m365con.net
Mirko Peters is a Microsoft 365 expert, content creator, and founder of m365.fm, a platform dedicated to sharing practical insights on modern workplace technologies. His work focuses on Microsoft 365 governance, security, collaboration, and real-world implementation strategies.
Through his podcast and written content, Mirko provides hands-on guidance for IT professionals, architects, and business leaders navigating the complexities of Microsoft 365. He is known for translating complex topics into clear, actionable advice, often highlighting common mistakes and overlooked risks in real-world environments.
With a strong emphasis on community contribution and knowledge sharing, Mirko is actively building a platform that connects experts, shares experiences, and helps organizations get the most out of their Microsoft 365 investments.