Microsoft Fabric domains are quickly becoming one of the most important pillars of governance and organization inside the Fabric ecosystem, and in this episode we break down exactly how they work and why they matter. You’ll learn how domains create logical groupings of workspaces and data assets, how they support a true data mesh architecture, and how they give organizations a clean, scalable way to manage ownership, access, and compliance across business units. We explore how Fabric domains tie into tenant-level governance, how domain admins and contributors manage their own data products, and how tools like the Purview-powered data map and OneLake help organizations discover, classify, and govern data across every domain. You’ll also see how Power BI fits into the model, how to plan domain structures effectively, how to avoid common pitfalls like inconsistent workspace organization, and what future governance trends are emerging as Fabric evolves. If you want to understand how Fabric domains bring clarity, structure, and federated governance to your data platform, this episode gives you the complete roadmap for building a well-organized, future-ready Fabric environment.
You want a solution that brings order to your organization’s data. Microsoft Fabric Domains give each business unit real ownership and control, so your teams can manage their information without waiting for IT. This structure improves data discovery and governance while adapting as your company grows. Think about the challenges you face with scattered data and unclear responsibilities—imagine how much smoother your work could be with clear roles and a central hub.
Key Takeaways
- Microsoft Fabric Domains give teams control over their data, allowing them to manage information without waiting for IT.
- Organizing data into domains improves data discovery and governance, making it easier for teams to find what they need.
- Each domain can set its own rules, balancing freedom for teams with overall data security and oversight.
- Using domains helps large organizations streamline data management and improve efficiency across departments.
- Microsoft Fabric integrates with tools like Power BI, allowing for seamless reporting and data visualization.
- A federated governance model empowers teams to create high-quality data products that meet their specific needs.
- Setting up domains involves planning your structure, assigning roles, and applying governance settings to ensure compliance.
- Regularly monitor and adjust your domain structure as your organization grows to maintain efficiency and security.
8 Surprising Facts About Microsoft Fabric Domains
- Microsoft Fabric domains let organizations present friendly, branded URLs for workspaces and artifacts, not just raw tenant IDs—so users often see company-branded addresses when accessing notebooks, dashboards, and reports.
- Adding a custom domain to Microsoft Fabric typically requires DNS TXT verification, but once verified it can streamline SSO and improve user trust across Fabric services.
- Domains are more than cosmetic: they can influence governance and sharing boundaries. Administrators can use domain membership to shape who can publish, share, or discover artifacts within Fabric.
- Fabric supports multi-domain scenarios, enabling a single Fabric tenant to recognize and work with users from several verified domains—useful for merged companies or multi-brand organizations.
- Linking a custom domain does not automatically move data or change where compute runs; domain configuration is about identity and addressing, while storage and compute regions remain governed by Fabric storage and capacity settings.
- Domain names used in Fabric can simplify lifecycle management of artifacts: URLs retain readable domain components that help with audit trails and external collaboration compared with opaque service-generated links.
- Because domains tie into identity, misconfigured or unverified domains can silently block expected SSO behavior or cause sharing failures—making DNS and verification steps a common operational surprise for admins new to Fabric.
- Fabric domain configuration interoperates with other Microsoft identity controls (Azure AD, Conditional Access, and external collaboration settings), so domain changes can have ripple effects across sign-in policies and external guest access.
Are Microsoft Fabric Domains Useful?
Value Proposition
You want your organization to move faster and make better decisions. Microsoft Fabric Domains help you do this by organizing your data into logical groups that match your business structure. You can give each team control over its own domain, which means they can manage their data without waiting for central IT. This approach makes data access management easier and helps you keep your platform secure.
Industry analysts say that Microsoft Fabric Domains simplify data management and bring advanced analytics and AI together in one place. You can break down barriers that slow your teams and speed up your time to market. When you use domains, you align your data engineering and business goals. You also make it easier for everyone to find and use the data they need.
You can see the value in how domains support a federated governance model. Each domain can set its own rules and controls, but you still keep an overall view of your data. This model helps you balance freedom and oversight. You can trust that your data stays safe while your teams stay productive.
Tip: When you group your data by business function, you make it easier for users to find what they need and for admins to enforce the right policies.
Who Benefits
You will see the most benefit from Microsoft Fabric Domains if you work in a large or growing organization. Teams that handle lots of data, such as BI, engineering, and management, can use domains to stay organized and efficient. Here are some examples of who gains the most:
- A multinational retail company with hundreds of BI users used Microsoft Fabric to modernize its analytics. They reduced the time it took to get insights and made data governance simpler.
- Teams that want to migrate slowly can start with a small group of power users. This way, you build skills without disrupting your current work.
- Any group that needs to centralize data and improve data engineering will find domains helpful.
You can also look at the roles that benefit from domains. The table below shows how different administrators use the model:
| Role | Scope | Description |
|---|---|---|
| Fabric administrator | Tenant | Manages tenant settings and overall governance in the Fabric portal. |
| Capacity administrator | One capacity | Oversees workspaces and workloads, ensuring the health of a Fabric capacity. |
| Data gateway administrator | One gateway | Manages data source configurations and user assignments related to the gateway. |
| Workspace administrator | One workspace | Handles settings and access for specific workspaces. |
If you want a more integrated experience, Microsoft Fabric connects with Power BI and other services. You do not need to switch between tools or manage separate systems. You get a single platform that supports your data engineering, BI, and management needs.
- Microsoft Fabric offers a more integrated experience with services like Power BI and Synapse.
- You can choose domains to match your business units, making it easier to manage data and users.
- If you want a managed solution from Microsoft, you will find Fabric Domains fit well with your goals.
You can use domains to give each team the right level of control. You keep your data secure and make sure everyone can work efficiently. This model helps you grow and adapt as your business changes.
Microsoft Fabric Domains Overview
Core Concepts
You can think of Microsoft Fabric Domains as logical groupings that organize your data by business area. These domains help you manage, govern, and secure your data in a way that matches how your company works. When you use domains, you create clear boundaries for data access management and responsibility. This approach supports a decentralized data architecture, often called a data mesh. You can set up domains for different departments, such as Sales or Marketing, and each workspace inside a domain inherits its attributes. This makes it easier for you to find and manage data that matters to your team.
Note: Domains let you filter content in the OneLake catalog, so you can quickly discover the right data for your needs.
How Domains Work
Structure and Boundaries
Domains in Microsoft Fabric give you a way to group workspaces and data assets by business function. For example, you might have a Sales domain with workspaces for Sales Reports, Customer Insights, and Leads Pipeline. A Finance domain could include Budgeting, Forecasting, and Expenses Dashboard workspaces. This structure keeps your data organized and aligns with how your teams operate.
| Domain | Example Workspaces |
|---|---|
| Sales Domain | Sales Reports, Customer Insights, Leads Pipeline |
| Finance Domain | Budgeting, Forecasting, Expenses Dashboard |
Each domain sets its own boundaries. You decide which workspaces belong to which domain, and you control who can access and manage the data inside. This model supports both security and flexibility.
Subdomains
You can create subdomains within a main domain to reflect more detailed business areas. For example, under a Marketing domain, you might set up subdomains for Digital Marketing and Events. Subdomains help you scale your data organization as your business grows. They also make it easier to delegate management and keep responsibilities clear.
Setup and Management
Setting up Microsoft Fabric Domains starts in the Admin Portal. You log in, select Domains, and create a new domain with a unique name and description. Assign Azure AD Groups as Domain Admins to manage the domain. Domain Admins then assign Domain Contributors, who can link workspaces to the domain. You can set access controls for adding or removing workspaces, making sure only the right people have control.
Here are some best practices for managing domains:
- Plan your domain structure by function, product, or region to keep things manageable.
- Involve both business and IT stakeholders to agree on ownership and responsibilities.
- Apply governance settings with delegated controls and enable audit logs.
- Use clear naming conventions and define ownership from the start.
- Monitor and adjust your domain structure as your organization changes.
This model gives you a federated governance approach. You delegate control to domain admins, but you still keep an overall view of your data. Microsoft Fabric Domains integrate with tools like Azure AD, Purview, and OneLake, supporting strong data governance and a modern data mesh. You empower your teams to manage their own data, improve data engineering, and keep your platform secure and organized.
Key Features for Governance
Federated Governance
You want your teams to manage their own data without losing control over the platform. Microsoft Fabric Domains use a federated governance model that gives each business unit ownership of its data. This approach helps you align governance with your business structure. You can trust your teams to create high-quality data products because they understand their own needs best.
- Business-aligned teams own and manage their data.
- Each domain creates data products that meet the needs of data consumers.
- Domains stay accountable for the quality and lifecycle of their data assets.
- Governance frameworks match enterprise standards but allow each domain to work independently.
This model supports agility. You can respond quickly to changes in your business. Unlike centralized models, federated governance lets you balance oversight with flexibility. You give your teams the freedom to innovate while keeping your data secure.
Note: Data mesh principles in Microsoft Fabric Domains help you decentralize data management and give each domain control over its data products.
Security and Access
You need strong security to protect sensitive information. Microsoft Fabric Domains provide advanced security features that help you manage data access management and keep your platform safe.
| Security Feature | Description |
|---|---|
| Real-time Threat Detection | Monitors for suspicious activities and responds automatically to potential threats. |
| Role-Based Access Control (RBAC) | Manages user permissions based on roles, ensuring only authorized users can access sensitive data. |
| Multi-Factor Authentication (MFA) | Requires multiple verification methods to enhance security against unauthorized access. |
| Private Links | Provides VNet-only access, isolating resources from public internet exposure. |
| Conditional Access | Configures access policies based on various conditions, enhancing security for sensitive environments. |
| Encryption (AES-256, TLS 1.2) | Protects data at rest and in transit using strong encryption standards. |
| Compliance with Regulations | Supports adherence to global standards like GDPR and HIPAA, ensuring data privacy and protection. |
| Data Resilience | Ensures data availability through geo-redundant storage and disaster recovery options. |
| Identity Management | Centralized identity controls via Microsoft Entra ID for consistent access management. |
| Audit Logs | Tracks user activity and access to sensitive data for compliance and monitoring purposes. |
Role-Based Controls
You can use role-based access control to limit who can see or change data. This feature lets you assign roles to users, so only the right people can access sensitive information. You can also use multi-factor authentication to add another layer of security. Conditional access policies help you set rules based on location or device, making your environment even safer.
Delegation to Admins
You do not have to manage everything yourself. Microsoft Fabric Domains let you delegate admin rights to trusted team members. Domain admins can manage access, monitor usage, and enforce policies. This model supports both security and efficiency. You can focus on strategy while your admins handle day-to-day management.
Compliance and Auditing
You must meet strict regulations in many industries. Microsoft Fabric Domains help you stay compliant with global standards. The platform supports certifications like HIPAA BAA, ISO/IEC 27017, ISO/IEC 27018, ISO/IEC 27001, and ISO/IEC 27701. You can use Purview Audit to track user activity and generate audit logs for investigations.
| Feature | Description |
|---|---|
| Auditing | Track user activity using Purview Audit, which is essential for meeting regulatory requirements. |
| Certifications | Holds compliance certifications to meet industry standards. |
| Data Security | Teams can apply data-level controls to manage access to specific data elements. |
| Information Protection | Sensitivity labels from Microsoft Purview Information Protection help classify and protect data, even when exported. |
| Data Loss Prevention | Purview DLP policies detect sensitive information and provide audit logs for compliance monitoring. |
You can apply sensitivity labels and data loss prevention policies to protect your data. These tools help you meet requirements for privacy and security. You can also use audit logs to monitor access and ensure your teams follow best practices.
Tip: Use the compliance and auditing features in Microsoft Fabric Domains to build trust with your customers and regulators.
Collaboration and Integration
Cross-Team Collaboration
You want your teams to work together without barriers. Microsoft Fabric Domains make this possible by grouping workspaces and data assets in a way that matches your business structure. This approach helps you manage data and encourages teams from different departments to share information. When you use domains, you give every group a clear space for their work while keeping everything connected through the platform.
The unified data architecture in Microsoft Fabric brings all your workloads into OneLake. This central data hub means everyone can access the same datasets. You do not need to worry about teams using outdated or different versions of data. Real-time collaboration becomes easy because everyone works with the same information. This setup supports cross-functional projects and helps you create data products that serve the whole organization.
| Collaboration Feature | Benefit |
|---|---|
| Grouping of workspaces | Promotes governance and cross-functional development |
| Real-time collaboration | Increases agility and better decision-making |
| Centralized data management | Ensures unified access and governance |
You can expose data to a wider audience, making it easier for end-users to find what they need. This model supports both data engineering and business intelligence teams.
Power BI Integration
You need strong reporting and visualization tools to turn data into insights. Microsoft Fabric Domains integrate with Power BI, giving you a seamless experience for building dashboards and reports. You can connect Power BI directly to data in OneLake or Fabric warehouses. This connection speeds up reporting cycles and ensures that everyone uses the same trusted data.
With this integration, you can improve your data modeling. Shared semantic models reduce confusion and help you avoid duplicate work. You can set up centralized governance, so your data access policies stay consistent across all reports. This makes it easier for you to manage security and compliance.
- Improved data modeling through shared semantic models
- Faster reporting with direct access to data
- Centralized governance for consistent policies
For example, a retail company can combine sales and inventory data to create dashboards that reveal trends and improve stock management. Healthcare providers can centralize patient records for efficient reporting. Financial services firms can analyze real-time data for quick decisions. You can scale your reporting as your business grows, making sure your platform supports both current and future needs.
Data Mesh Architecture
You want your organization to stay agile and scalable. Microsoft Fabric Domains support data mesh architecture by giving each domain ownership of its data. This means teams can manage their own workspaces and data products, reducing the need for central IT to handle every request. You can delegate responsibilities and let domain teams focus on their own development and management.
| Data Mesh Principle | Microsoft Fabric Alignment |
|---|---|
| Domain-Oriented Decentralized Ownership | Teams manage their own data and workspaces |
| Data as a Product | Shared access to high-quality data through OneLake Shortcuts |
| Self-Serve Data Infrastructure | Platform tools for independent data engineering and analytics |
| Federated Computational Governance | Role-based access and cataloging for compliance |
This workspace design lets you treat data as a product. You can use semantic models and metadata-rich catalogs to make sure everyone understands the data. The platform gives you the tools for self-service analytics, so teams can build and share their own solutions. You support both innovation and strong governance with this model.
Tip: Use domains to align your data engineering and business goals. This approach helps you stay organized and ready for growth.
Real-World Use Cases

Enterprise Governance
You can use Microsoft Fabric Domains to strengthen enterprise governance across your organization. Domains help you align data policies with business requirements and regulatory standards. You gain control over data access and ownership, which improves accountability. Many organizations have seen measurable improvements after adopting this model. For example, a healthcare client reduced audit failures by 45% by aligning Fabric policies with HIPAA requirements. You can see the impact of domains in the table below:
| Example Description | Impact |
|---|---|
| A healthcare client reduced audit failures by 45% after aligning Fabric policies with HIPAA requirements. | 45% reduction in audit failures. |
| Organizations using Data Fabric (Microsoft) report 30% faster compliance auditing and a 40% reduction in redundant storage. | 30% faster compliance auditing, 40% reduction in storage. |
You can use domains to streamline compliance auditing and reduce redundant storage. This approach helps you build a strong governance model that supports both data engineering and business intelligence.
Departmental Data Management
You can empower departments to manage their own data with Microsoft Fabric Domains. Teams gain the ability to set up their own pipelines and governance rules. This decentralized model encourages each department to treat data as a product, which improves quality and relevance. You can see several benefits when you use domains for departmental data management:
- Departments embrace decentralized data ownership, managing their own pipelines and governance rules.
- The architecture promotes treating data as a product, ensuring high-quality data for various teams.
- A self-serve infrastructure enables teams to access and manage their data products independently, reducing reliance on IT and improving workflow efficiency.
- Federated governance maintains standardization and compliance across domains, preventing fragmented data sets.
You can support managed self-service bi by giving teams the tools to build and share their own solutions. This model helps you maintain consistency while allowing departments to innovate.
Regulatory Compliance
You can achieve regulatory compliance more easily with Microsoft Fabric Domains. The platform gives you a unified space for data governance, security, and real-time monitoring. You can track compliance-related KPIs and gain insights into violations and associated costs. This information helps you justify investments in compliance. In regulated industries, Microsoft Purview automates the tagging of sensitive data, ensuring consistent handling and reducing risks. You can generate compliance reports for audits with less effort. Purview also enables you to identify sensitive data types and apply persistent sensitivity labels. These features simplify audit processes and help you maintain compliance. You can rely on domains to support your data management and regulatory needs.
Tip: Use domains to automate compliance tasks and reduce manual effort. This approach helps you stay ahead of regulatory changes.
Mergers and Integration
You face many challenges when your company goes through a merger or acquisition. You need to bring together different teams, tools, and systems. Microsoft Fabric Domains help you manage this process by giving you a clear way to organize and control your data. You can use domains to group data from each business unit or legacy system. This makes it easier to keep track of what you have and who owns it.
When you merge two companies, you often find that each group has its own data model and reporting tools. You can use domains to map these models to a single platform. This helps you avoid confusion and makes your data more reliable. You can also use domains to set up clear rules for data access and security. This keeps your information safe during the transition.
Tip: Start by creating a domain for each legacy business unit. Assign domain admins who know the data and can help with the integration.
You can use Microsoft Fabric Domains to support both data engineering and business intelligence teams. Data engineering teams can move data from old systems into the new platform. BI teams can build reports using trusted data from each domain. This approach helps you keep your data organized and makes it easier to share insights across the new company.
Here is a simple table to show how you might use domains during a merger:
| Legacy Company | Domain Name | Main Data Assets | Admin Role |
|---|---|---|---|
| Company A | Sales_A | Sales Orders, Customers | Sales Manager |
| Company B | Sales_B | Sales Leads, Accounts | BI Lead |
| Combined | Unified_Sales | All Sales Data | Integration Admin |
You can use this model to keep track of which data comes from which source. Over time, you can combine domains or create new ones as your business changes. This flexible model supports ongoing management and growth.
You also need to think about compliance and auditing. Microsoft Fabric Domains let you apply the same rules to all data, no matter where it comes from. You can use audit logs to track who accesses data during the integration. This helps you meet legal requirements and build trust with your teams.
Comparing Alternatives
Traditional Workspace Models
You may have used traditional workspace models for your data projects. These models often create silos. Each team manages its own workspace, which can lead to confusion and extra work. You might find it hard to scale your platform or keep your data secure. Manual processes slow down your delivery speed and make governance less effective.
Here is a table that shows how Microsoft Fabric Domains compare to traditional platforms:
| Feature | Microsoft Fabric | Traditional Platforms |
|---|---|---|
| Scalability | Unified experience, centralized governance | Siloed processes, manual effort |
| Governance | Centralized metadata model, automation | Manual processes, less efficient |
| Delivery Speed | Faster, safer, and more consistent | Often slower and inconsistent |
With Microsoft Fabric, you get a unified experience. You can manage your data and domains from one place. The platform brings together data engineering, warehousing, real-time analytics, and BI. This design helps you scale as your needs grow. You also improve security and performance because the architecture separates workloads.
Manual Governance
Manual governance can make your work harder. You may need to track data access, set permissions, and monitor compliance by hand. This process takes time and increases the risk of mistakes. You might miss important changes or fail to apply the right rules. Manual governance often leads to inconsistent policies across teams.
Microsoft Fabric Domains automate many governance tasks. You can set up rules once and apply them across all domains. The platform uses a centralized metadata model, which makes it easier to manage data. Automation helps you keep your data secure and compliant without extra effort. You spend less time on manual work and more time using your data for insights.
Tip: Automation in Microsoft Fabric Domains reduces errors and helps you keep up with changing business needs.
Competing Platforms
You may wonder how Microsoft Fabric Domains compare to other platforms. Many competing platforms offer domain management, but they may not provide the same level of integration. With Microsoft Fabric, you can track data lineage from different source systems. This feature helps you see where your data comes from and how it changes over time.
You can also analyze the impact of changes to your data model or metrics. Microsoft Fabric makes this process precise and clear. The platform includes automation features, such as auto-generating documentation and applying sensitivity tags. These tools may not be as strong in other platforms.
Here are some ways Microsoft Fabric Domains stand out:
- End-to-end lineage tracking for better data management
- Precise impact analysis for schema and metric changes
- Automation for documentation and sensitivity tagging
You get a complete solution for data engineering, BI, and governance. Microsoft Fabric Domains help you manage your data efficiently and keep your platform ready for growth.
Improvements Over Past Models
You have seen how older data platforms often create confusion. Teams struggle with unclear ownership and scattered information. Microsoft Fabric Domains change this story. You now get a clear structure for your data. This structure helps you avoid chaos and makes your work easier.
You can treat domain adoption as a strategic architectural decision. This means you plan how to group your data from the start. You do not just add domains as an afterthought. You make sure every team knows its responsibilities. This approach improves consistency across your organization.
Here are some ways Microsoft Fabric Domains improve over past models:
- You use workspace tags to align assets with business domains. These tags help you find and manage data quickly.
- Enhanced metadata management gives you better control. You can see who owns each dataset and how it is used.
- Integration with Azure Key Vault lets you manage credentials securely. You do not need to worry about unsafe password storage.
- Advanced governance features, powered by Purview and AI, help you handle complex environments. You can address unclear ownership and keep your data safe.
- The OneLake Catalog Search API gives you better visibility. You can search for datasets and reduce blind spots in your governance.
You benefit from these improvements every day. You can find the right data faster. You can trust that your data is secure. You can see who is responsible for each part of your platform. This makes your data engineering and management tasks much simpler.
Let’s look at the main steps that show how Microsoft Fabric Domains move beyond older models:
- You start with a clear plan for domain adoption. This step ensures your data aligns with your business needs.
- You tag workspaces and assets. This tagging helps you organize and discover data.
- You use catalog search tools to find datasets. This reduces time spent looking for information.
- You apply strong governance and security controls. This keeps your data safe and compliant.
You also get better support for BI and data engineering teams. These teams can work together in a unified platform. You do not need to switch between tools or worry about missing data. The model supports both innovation and control.
Tip: Use workspace tags and catalog search to keep your data organized and easy to find.
You can see that Microsoft Fabric Domains give you a modern, flexible way to manage your data. You move away from old, siloed models and step into a future-ready platform.
Limitations and Concerns
Complexity
You may find that Microsoft Fabric domains introduce new layers of complexity to your data platform. As you organize data into domains, you need to coordinate across teams and tools. Sometimes, teams use different Fabric features in inconsistent ways. This can create silos and make it harder to share data. You might see integration friction if you do not manage dependencies well or if you use inefficient configurations. These issues can lead to brittle pipelines and slow down your projects.
You also need to pay attention to governance. If you apply security and data quality rules unevenly, you could face compliance risks. To reduce complexity, you should:
- Define target data architecture patterns for all projects.
- Set clear guidelines for when to use each Fabric item.
- Enforce consistent data modeling practices before you scale up.
By following these steps, you help your teams avoid confusion and keep your data engineering efforts on track.
Workflow Integration
Integrating Microsoft Fabric domains into your existing workflows can present challenges. You may notice that workflow integration issues create silos, which complicate governance and make data management less efficient. Problems like schema drift and inconsistent data layers can appear. These problems often require extra work to fix and can slow down your progress.
When you do not have a unified approach, you may find that domains do not deliver their full value. You can address these challenges by standardizing your data layers and making sure all teams follow the same model. This helps you reduce rework and improve adoption across your organization.
Cost Factors
You should consider the cost factors when you implement Microsoft Fabric domains. The platform uses various pricing models, which can include hidden costs. You may need to choose from multiple capacity tiers, and this can lead to higher expenses. Storage costs start at $0.023 per GB per month, with extra charges for certain features. Licensing fees, such as per-viewer charges, can add up quickly. If you transfer data across regions, you pay $0.02 per GB. Idle capacity also incurs costs, even when you are not using it. Development and testing environments require separate capacity, which increases your total spend. Training your teams on multiple subject areas can also raise costs.
Here is a table that compares key cost factors for Microsoft Fabric domains and alternatives:
| Cost Factor | Microsoft Fabric Domains | Alternatives (e.g., Definite) |
|---|---|---|
| Pricing Models | Various pricing models with hidden costs | Simpler pricing structures |
| Capacity Tiers | Multiple tiers leading to potential high costs | More predictable costs |
| Storage Costs | $0.023/GB/month plus additional charges | Generally lower storage costs |
| Licensing Fees | Per-viewer fees can escalate costs | No per-viewer fees |
| Data Egress Charges | $0.02/GB for cross-region transfers | Typically lower or included in pricing |
| Idle Capacity Costs | Charges apply even when not in use | More flexible pricing options |
| Development/Testing Environments | Separate capacity needed, increasing costs | Often included in a single pricing model |
| Learning Curve and Training Costs | High training costs for multiple subject areas | Generally lower training costs |
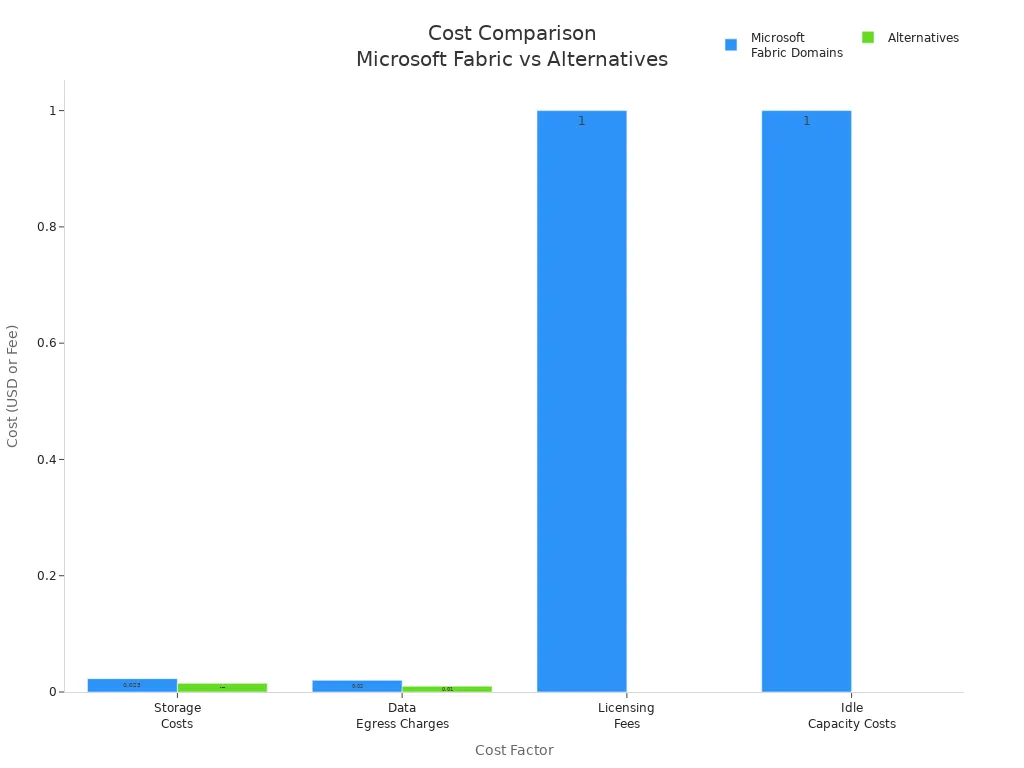
You can manage costs by monitoring usage, right-sizing your capacity, and planning your training needs. Careful management helps you get the most value from your data platform while keeping expenses under control.
Gaps and Workarounds
You may notice that even with Microsoft Fabric domains, some gaps can appear in your data platform. These gaps often come from early decisions about workspace structure and governance. If you do not plan your domains and data management from the start, you might see duplicated datasets, unclear ownership, and even conflicting data models. This can make your data estate feel chaotic, especially as your organization grows.
To address these challenges, you should focus on a few key workarounds:
Curate Business-Ready Data Layers
You can provide a platinum layer of data for self-service analytics. This ensures that users access high-quality, trusted data without affecting your ETL pipelines. Avoid exposing raw data (bronze layer) for self-service, as this can lead to inconsistent insights.Limit Access to Semi-Processed Data
You should apply strict governance to the silver layer of data. This prevents misuse and keeps your data engineering efforts focused on quality.Design a Clear Workspace Strategy
Many users find that initial workspace strategies lead to duplicated pipelines and models. You can solve this by combining platform and domain layers. For example, use platform workspaces for ingestion, domain workspaces for business areas, and consumption workspaces for analytics and BI. This approach gives you clear ownership and reusable data products.Use OneLake Shortcuts and Direct Lake Mode
You can avoid data duplication and enable real-time analytics by using OneLake shortcuts and Direct Lake mode. This keeps your data accessible and up to date.Implement Role-Based Access and Cataloging
Assign roles carefully and use Microsoft Purview for cataloging, lineage, and sensitivity labeling. This helps you track data ownership and maintain compliance.Adopt Version Control in Notebooks and Pipelines
Use Git workflows to keep your data engineering accountable. This makes it easier to review changes and maintain high standards.Encourage Composite Models
Composite models let you balance self-service flexibility with strong governance. You can align datasets with business domains and assign domain ownership, following a data mesh approach.
| Common Gap | Workaround You Can Use |
|---|---|
| Duplicated datasets and pipelines | Plan workspace structure and assign clear ownership |
| Unclear data ownership | Use domain-based management and cataloging tools |
| Inconsistent data models | Curate platinum data layer and limit access to raw data |
| Temporary permissions not reviewed | Regularly audit roles and use version control |
Tip: Make your first 90 days count. Define your domains, set up your workspace structure, and embed governance early. This will help you avoid technical debt and keep your data platform organized.
By following these steps, you can close operational gaps and make the most of Microsoft Fabric domains. You will see better data management, improved data engineering, and a more reliable platform for BI and analytics.
Adoption Guidance
Decision Criteria
You need to choose the right approach before you adopt Microsoft Fabric domains. Start by looking at who will own and manage your data. Decide if your teams or departments will take responsibility for their content. This choice shapes your governance model and affects how you set up your platform.
You should also think about the scope of content delivery. Ask yourself if you want to deliver data for personal use, teams, departments, or your whole enterprise. The range you choose will guide your governance and security needs.
Consider the subject area of your data. Sensitive information needs stricter controls. If your data is critical for decision-making, you must use a strong governance model. The table below shows key decision criteria you should review:
| Decision Criteria | Description |
|---|---|
| Ownership and Management of Data | Determines who is responsible for data and BI content, impacting governance requirements. |
| Scope of Content Delivery | Defines the range of content delivery (personal, team, departmental, enterprise) affecting governance. |
| Data Subject Area | Considers the sensitivity of data, requiring stricter controls for sensitive information. |
| Criticality of Data and BI Solutions | Identifies if data is essential for decision-making, leading to stricter governance for critical data. |
Tip: Review these criteria with your data engineering and BI teams to make sure your domains fit your business needs.
Readiness Assessment
You should check your readiness before you roll out domains. Start by reviewing your current data management practices. Make sure your teams understand the new model and have the skills to manage their own domains. You need clear roles for data owners, admins, and users.
Ask these questions to assess your readiness:
- Do you have a clear data governance policy?
- Are your teams trained in the new model?
- Can you support decentralized management?
- Is your data catalog up to date?
If you answer yes to most questions, you are ready to move forward. If not, plan for extra training and support.
Rollout Steps
You can follow a simple plan to roll out Microsoft Fabric domains:
- Define your domain structure based on business units or functions.
- Assign domain admins and train them on data management and governance.
- Set up your domains in the platform and link workspaces to each domain.
- Apply your governance model, including access controls and auditing.
- Monitor usage and adjust your domains as your organization grows.
Note: Start with a pilot project in one area. This helps you test your model and fix any issues before a full rollout.
You will see better data management, stronger governance, and more efficient data engineering when you follow these steps. Your teams will gain control over their data, and your organization will stay secure and organized.
You have seen how Microsoft Fabric Domains help you organize, secure, and govern your data. These domains give you clear ownership and make collaboration easier. If you want to improve control and efficiency, you should consider adopting this model. Start by reviewing your current structure and train your teams. For more details, visit Microsoft’s official documentation or join a Fabric community group.
Microsoft Fabric Domains Checklist
Microsoft Fabric Domains — Extended FAQ
What is a Microsoft Fabric Domain?
A domain groups workspaces and data assets by business function. You use domains to organize your data platform and align it with your company’s structure.
How do you set up a domain in Microsoft Fabric?
You create a domain in the Admin Portal. Assign domain admins and link workspaces. Use Azure AD groups for access control and delegate management to trusted team members.
Who manages a domain?
Domain admins manage domains. You assign them to oversee access, monitor usage, and enforce governance policies. This gives your teams control and keeps your platform secure.
Can you use Power BI with Microsoft Fabric Domains?
Yes, you connect Power BI directly to data in domains. This integration lets you build dashboards and reports using trusted, governed data.
How do domains improve data security?
Domains use role-based access control, multi-factor authentication, and conditional access. You set rules for who can view or edit data, keeping sensitive information safe.
What is federated governance in Microsoft Fabric Domains?
Federated governance means each domain manages its own data. You delegate control to domain admins, but you keep an overall view for compliance and oversight.
Can you create subdomains?
You can create subdomains to reflect detailed business areas. Subdomains help you scale your data organization and delegate management as your company grows.
How do you monitor compliance in domains?
You use audit logs and sensitivity labels. Microsoft Purview tracks user activity and helps you meet regulatory requirements. You build trust with customers and regulators.
What are microsoft fabric domains and why use them?
Microsoft Fabric domains are logical containers within Microsoft Fabric that let teams organize and manage data, govern access, and assign workspaces to the domain. Domains help departments to manage their data, create a data mesh in fabric, and ensure that data is governed consistently across assigned workspaces and OneLake data hub locations.
How do I create and edit domains in microsoft fabric?
Creating domains in Microsoft Fabric is done from the admin or domain settings area where you provide a domain name, optional domain image, color to represent your domain, and specify domains and subdomains if needed. After creating domains, you can edit domain-level settings like default domain membership, domain-level policies, and which workspaces are assigned to the domain.
What is a domain admin and how do I assign domain admins?
A domain admin is a user or group delegated to the domain level with permissions to manage that specific domain's content, settings, and assigned workspaces. You assign domain admins and domain contributors when configuring domain settings; these admins can be given authority to approve changes, manage data items, and organize and manage that data within their specific domain.
Can admins override workspace assignments and how does that work?
Yes, Microsoft Fabric supports workflows where domain admins or tenant admins can override workspace assignments in specific scenarios. You can allow tenant and domain admins to override workspace assignments so that admins can move a workspace to a relevant domain or resolve conflicts when a workspace is already associated with another domain.
How do I assign workspaces to the domain and what is workspace domain assignments?
Assign workspaces to the domain by navigating to workspace domain assignments in the Fabric admin UI and selecting the domain for each workspace. The workspace name and its default domain are displayed; you can change the workspace domain assignment to reflect the correct data domain and ensure the domain's data items they're seeing are governed properly.
What happens if a workspace is already associated with another domain or parent domain?
If a workspace is already associated with another domain, you must either remove it from the current domain or use admins to override workspace assignments if allowed. Some policies require approval from domain admins and domain contributors or tenant admins before moving the workspace to another domain or subdomain to prevent data governance conflicts.
How does the domain level affect data governance and data mesh in fabric?
Domains in Fabric create a domain level of governance that supports a data mesh in Fabric by delegating ownership and management to domain admins. This lets departments manage their data, ensures data is governed consistently, and makes it easier to organize data in a logical way across the OneLake data hub and across domains and subdomains.
Who can delete domains and what should I consider before I delete the domain?
Domain admins and tenant admins with appropriate permissions can delete domains, but you should first reassign or remove any workspaces and data items assigned to a domain. Deleting a domain removes the domain-level policies and associations, so check for workspaces that are assigned to the domain and any data items delegated to the domain before you delete domains.
How do I plan for creating domains and planning and creating domains in microsoft fabric?
Planning and creating domains involves mapping departments to relevant domains, deciding on domain or subdomain hierarchies, defining default domain settings, and identifying domain admins. Consider how to assign workspaces, what data items belong to each data domain, and whether admins and the specific domain should be allowed to override workspace assignments to maintain flexibility.
Can domain admins and domain contributors manage content by domain and control access to the domain?
Yes, domain admins and domain contributors can manage content by domain, control access to the domain, and organize content such as data items, catalogs, and shared assets. Permissions can be delegated to the domain level so that specific domain admins have authority over who gets access and how data is presented in the domain's data hub.
How do I represent domains visually with a domain image or color to represent your domain?
You can set a domain image and choose a color to represent your domain during create and edit domains steps in the admin UI. Visual cues like a domain image and color help users identify a specific domain quickly, especially when multiple domains and subdomains exist across the organization.
What should I know about default domain and domain is selected during workspace creation?
A default domain can be configured so that when users create new workspaces, the domain is selected automatically. This simplifies governance by ensuring new workspaces inherit the correct domain policies and assignments unless a user or admin explicitly assigns another domain during creation.
How do delegated domain admins to override workspace assignments interact with tenant admins?
Delegated domain admins can manage domain-level resources, but tenant admins retain broader control. If you allow tenant and domain admins the ability to override workspace assignments, tenant admins can intervene across domains while domain admins focus on their assigned domains. Policies should balance local control with central governance to prevent conflicts.
🚀 Want to be part of m365.fm?
Then stop just listening… and start showing up.
👉 Connect with me on LinkedIn and let’s make something happen:
- 🎙️ Be a podcast guest and share your story
- 🎧 Host your own episode (yes, seriously)
- 💡 Pitch topics the community actually wants to hear
- 🌍 Build your personal brand in the Microsoft 365 space
This isn’t just a podcast — it’s a platform for people who take action.
🔥 Most people wait. The best ones don’t.
👉 Connect with me on LinkedIn and send me a message:
"I want in"
Let’s build something awesome 👊
Admins, remember when Power BI Premium felt like your biggest headache? Overnight, you’re suddenly a Fabric Administrator, staring at domains, capacities, and tenant configs like a set of IKEA instructions written in Klingon. Microsoft says this makes things “simpler.” Our experience shows it just means fifty new moving parts you didn’t ask for.
By the end, you’ll know what to lock down first, how to design workspaces that actually scale, and how to avoid surprise bills when capacity goes sideways. Subscribe to the M365.Show newsletter so you get our Fabric survival checklist before chaos hits.
Let’s start with domains. Microsoft says they “simplify organization.” Reality: prepare for sprawl with fancier nametags.
Domains Aren’t Just New Labels
Domains aren’t just another batch of Microsoft labels to memorize. They change how data, people, and governance collide in your tenant—and if you treat them like renamed workspaces, you’ll spend more time firefighting than managing.
On the surface, a domain looks tidy. It’s marketed as a logical container: HR gets one, Finance gets one, Marketing gets one. Sounds neat until you realize each domain doesn’t just sit there quietly—it comes with its own ownership, policies, and permission quirks. One team sees it as their sandbox, another sees it as their data vault, and suddenly you’re refereeing a brawl between groups who have never once agreed on governance rules.
The scope is bigger too. Workspaces used to be about reports and maybe a dataset or two. Now your Marketing domain doesn’t just hold dashboards—it’s sucking in staging pipelines, raw data ingests, models, and random file dumps. That means your business analyst who just wanted to publish a campaign dashboard ends up sharing space with a data engineer pushing terabytes of logs. Guess who dominates that territory? Not the analyst.
Then comes the permission puzzle. You’re not just picking Viewer, Contributor, or Admin anymore. Domains bring another layer: domain-level roles and domain-level policies that can override workspace rules. That’s when you start hearing from users: “Why can’t I publish in my own workspace?” The answer is buried in domain settings you probably didn’t know existed when you set it up. And every one of those support pings ends up at your desk.
Here’s the metaphor that sticks: setting up domains without governance is like trying to organize your garage into “zones.” You put tools on one wall, bikes in another corner, boxes on shelves. Feels under control—until the neighbors dump their junk in there too. Now you’re tripping over someone else’s lawnmower trying to find your screwdriver. That’s domains: the illusion of neat order without actual rules. The punchline? Domains are an opportunity for chaos or control—and the only way you get control is by locking a few things in early.
So what do you lock? First 30 days: define your domain taxonomy. Decide whether domains represent departments, projects, or purposes. Don’t let people invent that on the fly. First 60 days: assign single ownership with a clear escalation path. One team owns structure, another enforces usage, and everybody else knows where to escalate. First 90 days: enforce naming rules, then pilot policies with one team before rolling them out everywhere. That gives you a safe zone to see how conflicts actually surface before they become tenant-wide tickets.
And what do you watch for along the way? Easy tells that a domain is already misconfigured: multiple near-identical domains like “Sales,” “Sales Reporting,” and “Sales 2025.” Owners you’ve never heard of suddenly holding keys to sensitive data. Users reporting mysterious “can’t publish” errors that resolve only when you dig into domain policies. Each of these is a canary in the coal mine—and if you ignore them, the sprawl hardens fast.
We’ve seen domain sprawl happen quickly when teams can create domains freely. It’s not hypothetical—it only takes one unchecked department creating a new shiny container for their project, and suddenly you’ve got duplicates and silos sprouting up. The mess builds quicker than you think, and unlike workspaces, a domain is bigger by design, which means the fallout stretches further.
The fix isn’t abandoning domains. Done right, they actually help carve order into Fabric. But doing it right means starting boring and staying boring. Naming conventions aren’t glamorous, and ownership charts don’t impress in a slide deck. But it’s exactly that unsexy work that prevents months of renaming, re-permissioning, and explaining to your boss why Finance can see HR’s data warehouse.
Domains don’t magically simplify anything. You’ve got to build the scaffolding before they scale. When you skip that, Microsoft’s “simpler organization” just becomes another layer of chaos dressed up in clean UI. And once domains are running wild, the next layer you’ll trip over isn’t naming—it’s the foundation everything sits on: workspace architecture. That’s where the problems shift from labels to structure, and things start looking less like Legos and more like a Jenga tower.
Workspace Architecture: From Lego to Jenga
Now let’s dig into workspace architecture, because this is where admins either set order early or watch the entire tenant bend under its own weight. Old Power BI workspaces were simple—few reports, a dataset, done. In Fabric, that world is gone. Workspaces are crammed with lakehouses, warehouses, notebooks, pipelines, and the dashboards nobody ever stopped building. Different teams—engineering, analysts, researchers—are all piling their work into the same bucket, and you’re supposed to govern it like it’s still just reporting. That mismatch is where the headaches start.
The scope has blown up. Workspaces aren’t just about “who sees which report” anymore. They cover ingestion, staging, analysis, and even experimentation. In the same space you’ve got someone dumping raw logs, another team tuning a model, and another trying to prep board slides. Mixing those roles with no structure means unstable results. Data gets pulled from the wrong copy, pipelines overwrite each other, performance sinks, and you’re dealing with another round of help desk chaos.
The trap for admins is assuming old rules stretch to this new reality. Viewer and Member aren’t enough when the question is: who manages staging, who protects production, and who keeps experiments from knocking over production datasets? Workspace roles multiply risk, and if you manage them like it’s still just reports, you’re courting failure.
Here’s what usually happens. Someone spins up a workspace for a “simple dashboard.” Six months later, it’s bloated with CSV dumps, multiple warehouses mislabeled, a couple of experimental notebooks, and datasets pointing at conflicting sources. Analysts can’t tell staging from production, someone presents the wrong numbers to leadership, and the blame lands on you for letting it spin out of control.
Microsoft’s advice is “purpose-driven workspaces.” Good guidance—but many orgs treat them like folders with shinier icons. Need Q4 content? New workspace. Need a sandbox? New workspace. Before long, you’ve got dozens of abandoned ones idling with random objects, still eating capacity, and no clear rules holding any of it together.
So how do you cut through the chaos? Three rules—short and blunt. Separate by function. Enforce naming and lifecycle. Automate with templates. That’s the backbone of sustainable Fabric workspace design.
Separate by function: Staging, production, and analytics don’t belong in the same bucket. Keep them distinct. One workable pattern: create a staging workspace managed by engineering, a production workspace owned by BI, and a shared research space for experiments. Each team knows their ground, and reports don’t pull from half-built pipelines.
Enforce naming and lifecycle: Don’t trust memory or guesswork. Is it SALES_PROD or SALES_STAGE? Tagging and naming stop the mix-ups. Pair it with lifecycle—every space needs an owner and expiry checks, so years from now you aren’t cleaning up junk nobody remembers making.
Automate with templates: Humans forget rules; automation won’t. Build a workspace template that locks in owners, tags, and naming from the start. Don’t try to boil the ocean—pilot with one team, smooth the wrinkles, then expand it.
Admins always want a sanity check: how do you know if you’ve structured it right? Run three quick tests. Are production reports separated from experiments? Can an experimenter accidentally overwrite a production dataset? Do warehouses and pipelines follow a naming convention that a stranger could recognize in seconds? If any answer is “no,” your governance won’t scale.
The payoff is practical. When staging blows up, it doesn’t spill into production. When executives need reporting, they aren’t pulling test data. And when workloads start climbing, you know exactly which spaces should map to dedicated capacity instead of scrambling to unpick the mess later. Architecture isn’t about controlling creativity, it’s about making performance and governance predictable.
Done right, architecture sets you up to handle the next big challenge. Because once multiple workspaces start hammering workloads, your biggest strain won’t just be who owns what—it’s what’s chewing through your compute. And that’s where every admin who thinks Premium still means what it used to gets a rude surprise.
Capacities: When Premium Isn’t Premium Anymore
Capacities in Fabric will test you in a way Premium never did. What used to feel like a horsepower upgrade for reports is now a shared fuel tank that everything taps into—reports, warehouses, pipelines, notebooks, and whatever else your teams spin up. And once everyone starts running at the same time, the rules you thought you knew collapse fast.
Here’s the blunt truth: your old Premium setup does not map directly to Fabric. Don’t assume your reporting SKUs translate neatly into compute resources here. Measure, don’t assume. Because suddenly it’s not just about snappy dashboards—your neatly tuned report is competing against an engineer running a giant pipeline job or a scientist who left a warehouse humming in the background all week. That’s not a fair fight.
I’ve seen organizations migrate under the assumption they could lift and shift old Premium footprints unchanged. Within days, complaints hit: reports stalling, scheduled refreshes delayed, and users thinking the “upgrade” was actually a slowdown. It wasn’t the reports themselves—they hadn’t ballooned in size—it was the new competing workloads chewing cycles from the same capacity pool without anyone realizing it.
Think of it like this. Old Premium was dessert delivery—pay more and the cake shows up fast. Fabric is the buffet table where every course goes on the same tray. Warehouses, pipelines, notebooks, dashboards—everyone piles on. If you want dessert later, you’d better hope the buffet isn’t already cleared out. Capacity doesn’t care who you are, it just gets eaten until it’s gone.
So how do you keep that buffet from collapsing? Three steps: Identify critical workloads first—those dashboards executives expect instant access to every morning. Put them on dedicated capacity if possible, so they don’t drown when experimental projects crank up compute. Then steer experimental and “learning” workloads to shared or budget-limited pools. That’s how you stop your CEO’s dashboard from waiting in line behind twenty test notebooks.
That’s strategy, but you still need immediate action. As soon as you migrate, run a triage audit. Capture at least a week of peak-hour usage. Make sure you’re logging which workloads consume the most compute. Then set alerts for sudden drains on capacity so you don’t find out through trouble tickets. Once you’ve mapped the top consumers, walk the results to finance—yes, finance—because budgeting has to change.
Here’s the line you can use in that meeting: “Think of capacity as a shared compute budget. Critical business reports need their own dedicated slots, otherwise everyone else’s work eats their lunch.” That’s plain language leadership understands. It frames the cost not as another license tax but as protecting the data your business actually runs on.
Monitoring matters too. The old Power BI workspace usage views won’t tell you the story anymore. Use Fabric-provided monitoring and metrics views—they’ll at least show you what categories of workloads are burning cycles. It’s not perfect, but it gives you the ammunition to separate culprits from victims when people start pointing fingers.
Bottom line: stop thinking Premium history gives you a head start. This is a different economy. Reports, warehouses, and pipelines all behave differently, and they all spike differently. Treat capacity not as a switch you’ve paid for but as a budget that multiple stakeholders spend from—some responsibly, some recklessly.
And just when you feel like you’ve tamed that shared budget, you realize capacity isn’t the only thing that can blow a hole in your governance model. There’s another layer waiting—settings buried at the tenant level that look harmless but can undo all the guardrails you built if defaults stay untouched. That’s where we head next.
Tenant Configs: The Silent Breakers
Tenant configs are where the real accidents happen. Microsoft frames them as “just a few new settings,” but one careless toggle can undo years of governance in a single afternoon. It’s less like managing policy and more like living with a breaker box that isn’t labeled—and when you hit the wrong switch, you don’t just lose a lightbulb, you take out the entire kitchen.
Back in the Power BI days, tenant settings were limited and predictable. You had a handful of controls on sharing, exporting, and labeling. It wasn’t perfect, but at least you knew the edges. Fabric changes that by dragging in whole new surfaces—warehouses, lakehouses, notebooks, pipelines—and each of them comes with tenant-level controls you probably haven’t reviewed yet. The danger isn’t obvious failure; the danger is that these defaults don’t match the guardrails you thought were already in place.
Here’s the catch: don’t assume your old Power BI defaults carry forward. They don’t. When Fabric lights up new features, Microsoft often sets them with “helpful” defaults that lean heavily toward self-service. That means end users may suddenly have the power to build objects you never scoped, move data outside your compliance model, or rack up compute charges no one budgeted for. From the user’s perspective, it works. From your perspective, it’s a time bomb.
So how do you keep from stepping on those silent breakers? First task: run a tenant settings audit. And I mean step by step. Export your current tenant settings. Document which toggles are Fabric-specific. Compare them against your existing governance baseline. Then flag the ones that allow uncontrolled self-service—things like users freely creating their own warehouses, lakehouses, or notebooks. This is the boring work that saves you from explaining to leadership why half the finance department stood up duplicate data stores without tagging them.
Once you’ve mapped the hazards, you move to action. Disable self-service features where the risk outweighs the value. Require approval before new warehouses or lakehouses spin up. And for every new object type Fabric introduces, tie it into your sensitivity labeling policies at creation. Don’t treat this as optional. If you let people create without labels, you guarantee you’ll spend months chasing data already out in the wild.
One survival tip: never reconfigure these toggles blindly across the tenant. Pilot them. Use a subset of users, or even a test tenant if you have one, to check impact. And log every change you make so you can roll it back if something breaks. It’s basic risk management, but it will save your weekends when someone’s “quick toggle change” cuts off a whole department’s access.
Also, don’t try to memorize all this from a podcast. For the exact toggle names and their current behavior, check Microsoft’s documentation or confirm with your account rep. They’re the only ones who can give you the definitive list, since Fabric is still evolving and defaults have been known to shift between rollouts. What I’m giving you here are the principles: audit, lock down risky toggles, enforce labels, test changes, and keep a rollback.
Think of tenant configs as the skeleton holding Fabric upright. If you don’t check the bones, the whole thing can wobble no matter how good your workspace or domain design is. And the problem isn’t going away—because every new Fabric feature adds one more lever in that breaker box. If you’re not auditing them regularly, governance will slip quietly before you ever see smoke.
Bottom line: inherited trust from Power BI doesn’t cover Fabric. Defaults are not your ally. Tenant settings need deliberate oversight, or they’ll happily unravel years of security policy without you noticing until the auditors show up. Run the audit, align the toggles back to your governance baseline, and keep that cycle alive as new features hit.
And here’s the bigger picture. If tenant configs already stretch your governance playbook, you can imagine what happens when you try to manage all these services together under Microsoft’s “unified” branding. The label says one thing, but the reality feels very different.
Unified Analytics or Unified Headaches?
Unified analytics sounds like a dream until you’re the one running it. Microsoft positions Fabric as that clean, unified surface where everything lines up under one roof. But when you wear the admin badge, it doesn’t feel unified at all—it feels like juggling five separate products while pretending they’re one.
On the marketing slide, Fabric looks simple. OneLake in the middle, then warehouses, lakehouses, pipelines, notebooks, and Power BI orbiting around it like tidy planets. In practice, each of those planets comes with its own rules, gravity, and orbit speed. You’re the one trying to keep them aligned while Microsoft insists it’s all one neat universe.
They call it a “single admin surface.” The reality? You’re still stitching metrics, settings, and logs across services yourself. OneLake demands storage policies. Warehouses need capacity management. Pipelines need scheduling and retry rules. Power BI still depends on workspace and dataset discipline. That’s four operational headaches before you even look at notebooks or dataflows. Unified? Maybe in branding—certainly not in your day-to-day tasks.
Here’s a real scar from my own tenant. We had a clean Power BI model—sensitivity labels, role-based policies, dev and prod neatly separated. Felt solid. Then Fabric rolled in. Within a week, a data scientist dropped CSVs in a lakehouse, slapped together a notebook, and blazed past the very rules we’d enforced in BI. Leadership noticed because they saw numbers in an email screenshot that didn’t match official dashboards. It wasn’t sabotage. It was simply Fabric’s services operating under different guardrails. And it put us on the back foot instantly. The fix? We had to extend the same security baseline—labels, ownership, separation—into every new Fabric surface, not just dashboards.
This is why admins feel like Fabric piles the job higher. You sign up to manage reporting, and suddenly you’re dealing with storage access, pipeline behavior, and runtime governance for notebook workloads. The role creep is real. Admins who came from BI are now knee-deep in data engineering governance, whether they asked for it or not.
Think about it like a Swiss Army knife missing instructions. Yes, it’s one tool. But every blade opens differently, some are dull, and every other one cuts your fingers when you grab it wrong. That’s “unified analytics.” The pieces live in the same handle, but it’s you who has to figure out how to carry, sharpen, and not get sliced.
How do you survive it? You don’t wait for Microsoft to hand you a true single pane. Instead, you build administrative unification yourself. Start with shared governance principles that apply to every surface: clear naming rules, dev/prod separation, and ownership accountability. Deploy workspace and domain templates so teams don’t improvise structure. Centralize your logs—whatever Fabric gives you, plus anything you can export—into a single reporting store, even if it means pushing them into a warehouse or SIEM. And most importantly, write a simple runbook for cross-surface incidents: if a pipeline eats capacity and breaks reports, who gets paged and where do you look first?
That’s your “admin pane of glass”—not a product feature, but a pattern you put in place. And before you ask, yes, monitoring support varies. Some tenants have access to consolidated APIs, some need extra tooling. Always verify your own environment and lean on your architecture docs or partners to see what’s exposed. Don’t assume the overview dashboard will tell the full story—it won’t.
The mantra I teach my team is simple: unified billing does not equal unified governance. Say it out loud, because that line will save you disappointment. Fabric puts every cost under one line item, but the governance work is still yours to design and enforce.
If you take nothing else away, remember this: Fabric won’t shrink your workload. What it does is stack complexity in new shapes under a single logo. The only way through it is to treat governance like a system you own end to end. That’s what keeps it consistent when marketing promises don’t line up with reality.
And once you truly accept that, you stop waiting for Fabric to “get simpler.” You start treating it as complicated by nature—and you prepare to manage noise instead of chasing the dream of easy mode. That perspective is what sets you up to stay ahead the next time Microsoft rebrands the same toolbox and calls it something new.
Conclusion
So what’s the takeaway? Fabric won’t get simpler, but you can make it survivable if you act with discipline instead of hope. Three moves keep you sane: First: Audit tenant defaults and lock down risky self-service. Secound: Design a workspace taxonomy and enforce it with templates. Last: Map capacity to business‑critical workloads and set alerts before finance calls about the bill.
If you only have 15 minutes today, do one thing: check a single tenant toggle or run a naming audit on one domain.
Subscribe at m365.show for the Fabric survival checklist and live MVP sessions. Stay sharp.
This is a public episode. If you'd like to discuss this with other subscribers or get access to bonus episodes, visit m365.show/subscribe

Founder of m365.fm, m365.show and m365con.net
Mirko Peters is a Microsoft 365 expert, content creator, and founder of m365.fm, a platform dedicated to sharing practical insights on modern workplace technologies. His work focuses on Microsoft 365 governance, security, collaboration, and real-world implementation strategies.
Through his podcast and written content, Mirko provides hands-on guidance for IT professionals, architects, and business leaders navigating the complexities of Microsoft 365. He is known for translating complex topics into clear, actionable advice, often highlighting common mistakes and overlooked risks in real-world environments.
With a strong emphasis on community contribution and knowledge sharing, Mirko is actively building a platform that connects experts, shares experiences, and helps organizations get the most out of their Microsoft 365 investments.