Troubleshooting DLP Policy Delay Issues in Microsoft 365: Causes, Impacts, and Solutions
DLP policy delay issues in Microsoft 365 are more than just a technical headache—they can quickly snowball into critical compliance and productivity problems if left unchecked. This guide is designed to walk you through what really causes these delays, highlighting the nuts and bolts of policy execution, common rollout mistakes, user impact, and proven ways to keep your data protections running smoothly.
We’re breaking down the full journey: from the first policy deployment in Exchange Online, Teams, or Outlook, through real-world troubleshooting steps, and onto the strategic moves that set your organization up for lasting success. You’ll also see how user workflow and trust are directly tied to DLP responsiveness. Whether you’re knee-deep in technical configurations or steering policy direction, you’ll find actionable insights and best practices to ensure your DLP controls keep pace with business demands—and never leave your team (or your data) hanging.
Understanding DLP Policy Delays in Microsoft 365
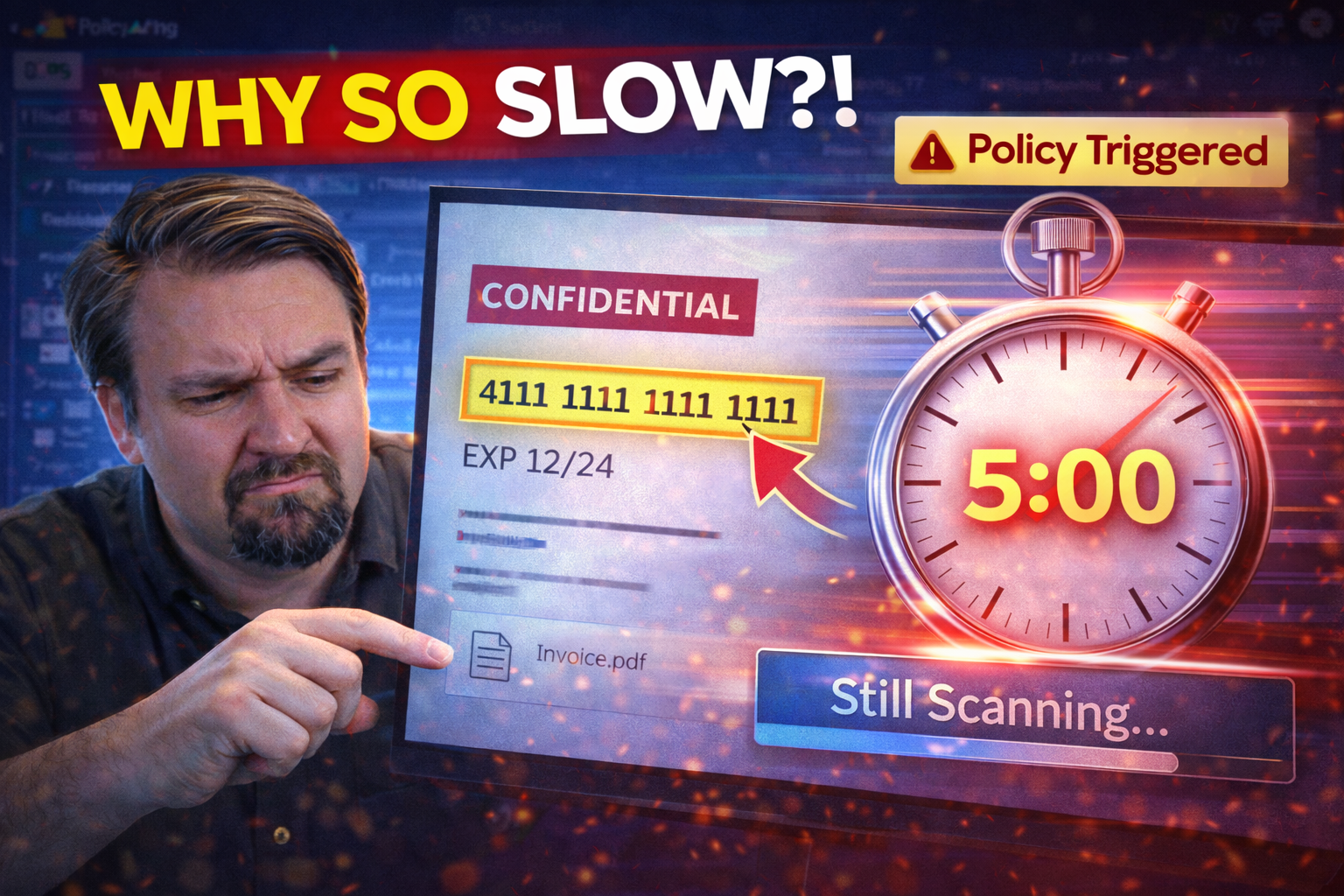
When you set up Data Loss Prevention (DLP) policies in Microsoft 365, the expectation is for real-time protection—spotting and stopping sensitive data leaks before they happen. But the reality sometimes feels a few steps behind, with alerts or warnings showing up too late to make a difference. In heavily regulated industries, every minute of delay can mean exposure to compliance risk or accidental data leaks.
Microsoft 365 DLP applies policies across core services: Exchange Online for email, Teams for collaboration, and Outlook as the main communication tool for most knowledge workers. For these policies to do their job, they rely on a complex web of configurations, client capabilities, and enforcement engines. Even small mistakes in setup or overlooked deployment details can lead to delays in enforcement, impacting everything from email tip speed to file-sharing controls in real time.
Immediate enforcement is critical. Imagine a user sending an email with sensitive HR or financial data; if the DLP warning arrives after the message is sent, the safeguard is all but useless. Understanding why these delays occur—and what stands in the way of instant detection—helps you prioritize fixes and ensures your data stays right where it should.
We’ll dig deeper into the most frequent configuration slip-ups, how Outlook and MailTips contribute to slowness, and how premium DLP features can bring speed and reliability to your notifications. By getting clear on these root issues, you’ll be able to focus your attention on what makes the biggest difference in keeping your data safe—and your users moving.
Common Configuration Errors Leading to DLP Policy Enforcement Delays
- Improper File-System or Outlook Configuration: If Outlook isn’t set up with the configurations supported for DLP, or if the file-system setup doesn’t match Microsoft’s requirements, DLP policies may not evaluate on time—or at all.
- Invalid Data Entries in Policy Rules: Policy rules using unsupported expressions, or referencing non-existent domains or data types, can cause enforcement delays as policies fail to match accurately.
- Prerequisites Not Met: Failing to enable required DLP connectors or missing schema updates in Exchange Online often stalls policy rollout. Always match your environment against Microsoft’s prerequisites before going live.
- Overlooked Environment Strategy: As discussed in this M365 FM episode, treating environments and connector governance as isolated afterthoughts—rather than an integrated effort—creates loopholes where DLP can get “stuck.”
By checking each of these, IT teams can quickly pinpoint most delay triggers and roll out policies with confidence.
Client MailTips and Outlook Limitations Slowing DLP Tip Delivery
MailTips in Outlook are a crucial component for delivering DLP policy warnings directly to users as they work. When “mailtips enabled” isn’t properly set, or if users are using outdated Outlook versions, DLP tips may not appear instantly—or sometimes, not at all. This can leave users unaware of risky data actions until it’s too late.
For DLP tips to show up immediately, your Outlook client must match the configurations Microsoft supports for proactive tip delivery. Issues like disabled client MailTips or unsupported builds can choke the flow of notifications. As a result, messages containing sensitive data may be sent without any visible warning if the underlying infrastructure isn’t fully aligned.
Missing or delayed MailTips and DLP notifications directly affect user experience, eroding the intended protective layer that DLP policies are meant to provide. Staying current with supported versions and ensuring that all necessary features are switched on across your environment is key to truly “real-time” DLP enforcement.
DLP Tips Premium Features and Their Impact on Notification Speed
DLP Tips Premium is an advanced feature available through specific Microsoft 365 licensing tiers. Unlike standard DLP tips, which may deliver generic or delayed alerts, premium DLP tips bring several advantages: much faster feedback, richer context, and greater consistency across web and desktop Outlook clients.
With Premium DLP Tips, policies can display context-aware warnings the moment a user interacts with sensitive information. These features leverage more granular policy evaluation engines, reducing the latency between user action and policy notification. For organizations with complex data flows or strict compliance requirements, this can be a game-changer—ensuring users receive feedback in real time, across both Exchange Online and the wider Microsoft 365 suite.
Upgrading to this Premium option means fewer gaps in protection, fewer missed warnings, and a smoother, more predictable user experience when handling sensitive company data.
Deployment Mistakes Leading to DLP Policy Performance Issues
Getting DLP up and running isn’t just about flipping a switch and hoping for the best. How you deploy—the steps you take in the pilot phase, the way you approach organization-wide rollout—can have massive effects on policy performance and speed. Miss a step, and you might find your well-intentioned protections rolling out slowly or behaving unpredictably out in the wild.
Deployment mistakes often start small, like an overlooked connector or a forgotten compatibility check. But they can snowball into major headaches, leading to DLP lag times, inconsistent user feedback, or even outright policy failures. The consequences aren’t limited to technical trouble, either—poor deployments can create compliance risks and derail end-user productivity.
That’s why deployment deserves as much attention as the policies themselves. A thoughtful, risk-aware approach—one that involves security teams, business stakeholders, and IT configurations in equal measure—is crucial to keeping delays at bay. Avoiding pilot-phase missteps and ensuring clear business justification before a full rollout helps sidestep the most common traps.
The next sections will dig into the biggest deployment mistakes seen in the field, as well as how to strike the right balance between airtight security and user-friendly workflows. With the right groundwork, you can reduce the chance of new DLP rollouts slowing your business to a crawl and ensure your policies consistently deliver fast, reliable protection.
Mistakes Deploying DLP: Risk Factors and Potential Consequences
- Missed Requirement Checks: Skipping environment prerequisites or connector classifications, as highlighted in this guide for Power Platform developers, often causes DLP to silently fail or introduce delays.
- Challenges Scaling DLP: Deploying policies that work in pilot but grind to a halt in production usually comes down to not testing with real user data or high traffic volumes.
- Lack of Proactive Governance: Failing to treat DLP as an ongoing architectural element (with continual testing and policy updates) can leave policies out of sync with business realities, slowing enforcement or increasing false positives.
- Ignoring Well-Thought-Out Deployment: Rushing rollouts without thorough business or security alignment can lead to immediate technical issues and long-term trust problems with both IT and end users.
All of these mistakes risk compliance gaps, system bottlenecks, and avoidable productivity loss across the business.
Balancing Security and Usability During DLP Policy Design
Striking a balance between security and usability is critical in DLP policy design. Overly strict or complex policies can grind systems to a halt, causing slowdowns and a flood of false alarms that frustrate staff and lower productivity. This friction often leads to users finding workarounds—or ignoring alerts entirely.
On the flip side, policies that are too loose leave sensitive data exposed and increase risk. Effective DLP design means looping in both technical teams and business leaders to review real-world data flows and common use cases. Policies should evolve from business needs, not just technical requirements.
Techniques like prioritizing high-risk rules, limiting overlapping triggers, and tuning alerts for real scenarios—similar to the “adaptive, risk-aware” concepts shared in this Zero Trust M365 podcast—can keep the right balance between protection and productivity.
Technical Diagnostics for DLP Policy Delay Troubleshooting
When DLP starts lagging in Microsoft 365, the question isn’t just “what’s broken,” but “where is it getting stuck?” This is where hands-on diagnostics come into play. From poking around logs and network traces to reviewing client configurations, technical troubleshooting helps you zero in on the specific causes behind DLP delays.
These diagnostics go a step beyond just guessing at root causes—they give you a trail of evidence showing whether the bottleneck lies in your Exchange Online service, your Outlook setup, or even your file-system configuration. Using proper tools and capturing the right traces are crucial, since the sources of delay can range from invalid policy data to sluggish policy tip evaluations on client devices.
Technical diagnostics arm your IT and security teams with data, not just hunches. By knowing how to systematically investigate with tools like Fiddler and event logs, you can resolve issues efficiently and ensure users get the right notifications, exactly when they need them.
Next, we'll cover practical steps for tracing policy tip delivery and resolving configuration issues. These approaches make troubleshooting less of a guessing game and more of a precise, step-by-step process for keeping DLP on track in your Microsoft 365 ecosystem.
Using GetDlpPolicyTip Fiddler Trace and Logs for Issue Resolution
A GetDlpPolicyTip Fiddler trace is a diagnostic process that records network traffic between Outlook and Exchange Online to track the delivery and evaluation of DLP policy tips. By launching Fiddler and recording while a user attempts to trigger a DLP policy, administrators can capture communication details that reveal bottlenecks or errors.
During analysis, focus on requests and responses tied to the DLP policy tip API. Watch for HTTP errors, long response times, or “invalid data” entries in log content. These signals usually point to mismatch between client and server, or configuration gaps holding up policy evaluation.
If the trace shows missing or malformed data, check for out-of-date Outlook builds, unsupported add-ins, or incorrect policy entries that could be causing timeouts. Invalid schema references, outdated connectors, or disabled mailtips will also surface here as silent delay factors. Even the order in which rules are processed or heavy queue backlogs can become visible when studying Fiddler output closely.
Treat Fiddler traces and Exchange/Outlook logs as complementary sources. Logs will highlight long-running or failed DLP operations, with event details giving more context. A typical troubleshooting path combines a Fiddler session with log review, allowing admins to match user-facing slowness with backend causes in real time. Thorough tracing is the foundation for moving from “DLP seems slow” to “Here’s exactly what’s causing the stall—and how to fix it.”
Resolving File-System and Outlook Configuration Bottlenecks
Resolving policy evaluation delays often starts with making sure both file-system configuration and Outlook are up to Microsoft’s supported standards. Common sticking points involve running Outlook builds that are no longer supported for DLP, or file systems that block access to DLP policy logic.
Step one: verify your Outlook version and ensure “mailtips enabled” is set on every client that needs real-time DLP. Unsupported or outdated software can leave users waiting for policy tips that never arrive. Next, review file-system configurations—policy templates and rule updates need seamless write/read access to function without interruption.
If issues crop up, Microsoft provides comprehensive DLP setup and optimization tips, like those in this M365 FM podcast episode. Their insights not only help secure sensitive data but also optimize productivity across departments by reducing routine troubleshooting work. Keeping everything up-to-date and in line with Microsoft’s technical requirements is key for fast, reliable DLP notifications.
Enhancing DLP Policy Performance with Modern Tools and Strategies
Modern DLP protection is about more than just hitting the on-switch. It’s about leveraging the latest features, from premium policy engines to AI-powered integrations, so users get fast, accurate feedback any time they interact with sensitive data. As Microsoft 365’s built-in capabilities grow, external platforms now offer even more ways to close the gap between user action and policy enforcement.
Premium DLP tips play a starring role in speeding up notification delivery, making sure that warnings are visible exactly when they’re needed. They work hand in hand with client configurations to reduce lags that can slow users down or leave compliance holes open.
Third-party platforms like Metomic are also bringing new levels of intelligence and automation to DLP, using AI to detect policy risks in real time and give security teams the granular control needed for modern, cloud-based workflows. These tools don’t just patch weaknesses—they actively transform the DLP operating model, improving both speed and relevance of protection.
The next sections cover how to set up your policies for rapid, user-friendly responses using premium DLP features and explore how AI and privacy platforms help push DLP from a reactive safety net into a proactive, business-aligned guardrail for sensitive data.
Accelerated User Feedback with Premium DLP Tips and Configurations
Premium DLP tips make a significant difference in how quickly and clearly users are warned about sensitive data actions in Microsoft 365. These tips, available with advanced licensing, give users context-sensitive prompts as soon as they start composing or sharing protected information—reducing the window for accidental data loss.
Optimized configurations in Outlook and Exchange Online are essential for these features to deliver instant feedback. Premium tips support greater granularity in policy definitions, letting admins target specific scenarios and user groups for ultra-precise enforcement. This approach minimizes noise and helps users understand, in real time, exactly what’s risky about their actions.
For real-world strategies to maximize DLP value—especially in Power Platform environments—see these insights on environment strategy and connector governance. By integrating smart environment controls and connector hygiene, premium tips turn DLP into a seamless, high-speed user safety net.
Using Metomic Privacy Platform and AI for Real-Time DLP Protection
The Metomic Privacy Platform and the Melody: Brain platform tackle DLP delays by using AI to assess data flows and deliver real-time, actionable warnings—well before sensitive information leaves the organization. Unlike traditional setups that rely on manual rule tweaking, these platforms automatically adapt to changing data, users, and workflows.
Melody’s notification engine, for example, overcomes the “granularity headache” by pinpointing specific risks and alerting users with contextual guidance, no matter where the data lives. Security teams can tune Melody’s logic with business-aligned policies—reducing both overblocking and costly delays.
This approach mirrors guidance from experts emphasizing intentional M365 governance: simply having DLP controls isn’t enough; real value comes from integrating people, process, and smart technology for timely, reliable protection. Platforms like Metomic ensure DLP isn’t just fast, but also business-aware and easy to manage at scale.
Strategic Planning and Risk Assessment for Reliable DLP Rollouts
All the technical fixes in the world won’t save you from DLP delays if the foundation isn’t solid. Strategic planning and risk assessment are the backbone of a truly reliable DLP program. Before policies go live, a clear-eyed evaluation of your business processes, user groups, and risk landscape sets the table for rapid and error-free enforcement.
Proactive risk assessment helps spot potential enforcement delays caused by process gaps or overlooked dependencies. This strategy involves more than just IT—business stakeholders bring crucial insight on where data flows, how sensitive content moves, and what operational realities shape user behavior.
Only by embedding risk-based thinking into policy design and rollout do you prevent slowdowns and ensure that DLP integrates with business rhythms, not against them. The goal is to make enforcement cycles nearly invisible to users, with security running quietly (and quickly) behind the scenes.
We’ll explore next how to accurately assess risk before deployment and how aligning technical and business perspectives creates a streamlined, delay-proof DLP foundation that stands up under pressure.
How Risk Assessment Prevents DLP Policy Delay Issues
Conducting a thorough risk assessment before DLP policy deployment is the most effective way to sidestep enforcement delays and compliance headaches. By mapping out your organization’s sensitive data locations, business processes, and user workflows, you can predict where bottlenecks might occur.
This process highlights any missing prerequisites or incompatible technology before policies disrupt operations. Leveraging tools like Microsoft Purview Audit, as detailed in this guide, strengthens your ability to pinpoint risks and gather audit evidence of DLP readiness. The outcome is faster, error-free policy rollouts and more reliable ongoing protection.
Technical Tweaking with Business Alignment to Reduce Delays
The secret to fast, accurate DLP enforcement is technical tweaking guided by real business input. By involving stakeholders in deployment planning, you surface rule redundancies, unnecessary complexity, and process misalignments before policies are set in stone.
Rationalizing rules and streamlining configurations prevents processing slowdowns and flurries of false positives. Reference points like user activity audit frameworks reinforce how oversight and continuous refinement deliver consistently fast and trustworthy protection. Every policy should have a clear business justification—when technical and business teams pull together, DLP delays become far less likely.
DLP Policy Delay Impact on End-User Productivity and Workflow
DLP policy delays aren’t just a behind-the-scenes problem—users feel them front and center in their daily work. Waiting on a delayed DLP warning, or never receiving a needed tip at all, interrupts the flow of email, document handling, and team collaboration. Even minor slowdowns can push users to find risky workarounds, or to give up on a task entirely.
The impact is easy to quantify: every second waiting on a warning is a second lost from productive work. Over time, these small interruptions add up, taxing both employee morale and business performance. Frustration can mount when users perceive security as a barrier, not a benefit—especially if the same issues repeat without explanation.
Companies need more than technical fixes; they need an honest look at how DLP delays impact dwell time on tasks, abandonment rates when actions stall, and end-user confidence in the entire security context. Addressing these human factors is essential for balancing protection with operational efficiency.
In the coming sections, we’ll break down how to measure the true cost of DLP delays and why consistent, timely feedback is key to fostering lasting security awareness among users.
Measuring User Dwell Time and Abandonment Rates From DLP Prompts
User dwell time is the total amount of time users spend waiting for DLP warnings, tips, or restrictions to appear after attempting sensitive actions. High dwell times mean users sit idle—waiting for a “go,” “stop,” or “you might want to check that” message—causing frustration and slowdowns.
Action abandonment rates measure how often users drop a task or move to another tool if DLP warnings don’t appear promptly. These metrics can be monitored through application logs, user analytics, or feedback surveys. By tracking these numbers, IT and business partners can target optimizations that reduce friction and keep security invisible, except when it matters most.
How Delayed Warnings Affect End-User Trust in Security Systems
When DLP warnings arrive late, inconsistently, or not at all, users start to lose faith in the underlying security system. This can lead to “warning fatigue,” where users ignore or dismiss tips—even when the message is valid—because their experience has taught them not to trust the timing or accuracy of DLP alerts.
Inconsistent or slow feedback erodes a compliance-first culture, increasing the chance that risky actions slip by unnoticed. Reliable, timely warnings build user trust—not just in DLP, but in the entire security stack—reinforcing the idea that data protection is effective, present, and user-centric every step of the way.
Conclusion and Best Practices for Minimizing DLP Policy Delays
Wrapping up, one thing’s clear: DLP policy delays aren’t solved by chance—they need a proactive blend of technical know-how, strategic planning, and ongoing feedback from both users and business leaders. We’ve covered the gamut: technical missteps, deployment pitfalls, diagnostics, user impact, and the big-picture moves that keep your protections lean and lightning-fast.
Best practices aren’t “set and forget”—they’re about continuous review, optimization, and business alignment. Every new app, workflow, or user group brings new wrinkles and demands agility in both policy design and enforcement. Whether tuning legacy rules or piloting premium features, start with the basics, ask tough questions about real-world user impact, and keep refining until delays are the rare exception, not the norm.
Looking ahead, the organizations that put user trust, speedy enforcement, and clear business logic at the core of their DLP efforts won’t just avoid delays—they’ll turn their data protection programs into genuine business enablers. So, whether you’re wrestling DLP into shape or future-proofing your compliance game, these lessons will serve you well.
Key Points for Preventing and Resolving DLP Policy Delays
- Validate All Prerequisites: Double-check Outlook, Exchange, and file-system configurations against Microsoft’s latest requirements.
- Iterate with User Feedback: Track and tune DLP impact on real workflows to minimize user friction and abandonment.
- Invest in Premium Features: Upgrade to DLP Tips Premium for faster, more actionable user warnings.
- Monitor Policy Effectiveness: Use periodic audit checks like those described in this DLP strategy guide to catch slowdowns early.
- Align with Business Needs: Treat DLP as a holistic effort—policy, people, and process all matter for lasting improvement.
What We Actually Believe About the Future of DLP Performance
The next wave of DLP improvement will be powered by smarter AI policy engines and a cultural shift towards truly business-driven security. Lessons learned from years of “DLP hired hands” point to automation, granular controls, and real-time auditing—think Copilot, Purview, and Sentinel integration, as covered in this Copilot governance guide—as the key levers for speed and reliability.
As policy evaluation becomes both more intelligent and company-specific, organizations that align their security teams, business workflows, and cultural expectations will see DLP delays shrink and trust expand. The future is fast, automated, and deeply connected to both compliance requirements and everyday business success.












