Conditional Access for Service Accounts in Microsoft Entra ID: The Essential Guide
If you’re in charge of security in Microsoft Entra ID, getting Conditional Access right for service accounts isn’t just another checkbox—it’s the backbone of controlling who (or what) gets into your cloud services. This guide walks you through how Conditional Access policies apply to service accounts, identity-centric controls, crucial prerequisites, and advanced risk reduction. Expect practical steps for configuration, tuning, and long-term policy upkeep.
You’ll learn how to protect non-human identities and secure everything from Microsoft 365 to Azure workloads—even in hybrid setups with on-prem connections. Whether you’re wrangling service principals, managed identities, or old-school accounts, we’ll cover what it really takes to build strong, reliable access governance. Ready to tighten the reins? Let’s dig in and give your organization the access control clarity it’s missing.
Understanding Identity Infrastructure and Security Principles for Service Account Access
Every security journey in the Microsoft cloud starts with your identity infrastructure. With so many services talking to each other, service accounts quickly become the silent workhorses behind the scenes. But when left unchecked, these powerful non-human identities turn into major security liabilities.
Identity-centric protection means you treat the identity itself—service account or human user—as the primary control point. Strong authentication, like certificate-based or secure secret storage, isn’t negotiable. You apply least privilege: only assign what the service account needs, nothing more. If a spreadsheet-processing bot needs OneDrive, it shouldn’t have SharePoint admin rights.
But that’s just the basics. Consistent identity management is what keeps businesses out of the headlines for the wrong reasons. When service accounts pile up without clarity, or their privileges go unreviewed, you risk “identity debt” and unpredictable security policies. Real-world incidents have shown that attackers love to piggyback on neglected service accounts with outdated secrets or wide-open access.
Your goal is clear: put identity at the center, enforce strong access policies, and maintain good governance. A solid strategy means you reduce risk, gain control, and can answer the tough questions when auditors—or attackers—come knocking. If you want deeper insights into how identity sprawl and exceptions can create fragile security, check out this practical breakdown on identity as the control plane.
Want more about how data ownership and continual access reviews tie into good governance? This look at Microsoft 365 data access and governance will help you build sustainable, risk-resistant access strategies from the ground up.
Securing Service Accounts Versus Service Principals: Non-Human Identities in Focus
Not all non-human accounts are created equal—knowing the difference between a traditional service account and a service principal in Entra ID will save you headaches (and maybe a breach or two). Traditional service accounts are full user objects, often with passwords or static secrets, while service principals are app representations with more granular controls in Azure AD (now Microsoft Entra ID).
Conditional Access policies hit these two differently. Service principals are usually laser-focused for app-to-app permissions, and Conditional Access works best here, isolating what an app can do. Regular service accounts can be trickier—they might get caught in broader rules or skip modern authentication altogether. For anyone on a Zero Trust journey, this is a big deal.
If you’re wondering which route is safer, take a minute to explore why workload identities are the next step for locking down non-human access. The differences matter—and so does getting the right fit for your cloud strategy.
Prerequisites and Planning for Conditional Access Policies
Setting Conditional Access for service accounts isn’t as simple as switching on a feature—it’s about understanding what you need ahead of time so you’re not left scrambling mid-deployment. From licensing and technical boundaries to deciding which admins steer the ship, planning prevents nasty surprises.
You need to be sure your organization meets minimum requirements. Maybe you’re missing a specific Entra ID or Microsoft 365 license, or you’re not set up to handle protocol limitations for some legacy service accounts. Mistakes here result in policies that look good on paper but never actually work in production.
Roles and permissions come next. Picking the right folks to design, test, and adjust these policies isn’t just bureaucracy—it’s your frontline defense against privilege creep and unauthorized changes. Finally, groundwork around identifying and categorizing service accounts means you apply protection where it’s actually needed, not just where it’s convenient.
Want to cut out the guesswork and avoid those “how did this get through” moments? The coming sections give you checklists and breakdowns for each stage: from prerequisites and admin access to shaping a lifecycle plan for your service accounts. And if trust issues, exclusions, and rollout strategies keep you up at night, see how an inclusive, monitored policy approach helps lock down the gaps.
Prerequisites, Limitations, and Setup Requirements for Conditional Access
- Licensing: You’ll need Entra ID Premium P1 or P2 (formerly Azure AD) for Conditional Access features. Microsoft 365 E3/E5 may also be required for full support.
- Eligible Identities: Conditional Access supports cloud-only or hybrid Azure AD accounts, but struggles with some on-prem, legacy, or non-browser protocols (like basic authentication).
- Protocol Constraints: Legacy authentication (e.g., POP, IMAP, SMTP) often bypasses Conditional Access. Modern authentication and OAuth2 are preferred for enforcement.
- Tenant Setup: Verify your Entra ID tenant is configured correctly—you need synced accounts via Azure AD Connect if you’re in hybrid mode.
- Pitfalls: Beware of policy sprawl or piling on exceptions, which create “identity debt” and open the back door to attackers.
Admin Roles, Permissions, and Access Controls for Policy Management
- Global Administrator: Full control but best reserved for break-glass or initial setup; use least privilege whenever possible.
- Conditional Access Administrator: The go-to for policy creation, modification, and management specific to Conditional Access in Entra ID.
- Privileged Role Administrator: Helps manage assignments and enforces separation of duties with Privileged Identity Management (PIM).
- Security Reader: For monitoring and auditing—keeps an eye on logs and verifies changes without making policy edits.
- Best Practice: Limit permanent privileged access; assign time-bound or approval-based admin permissions to cut down risk exposure.
Planning Your Service Account Strategy and Lifecycle
- Account Identification: Inventory every service account and principal—tag each with purpose and owner up front.
- Categorization: Group accounts by risk, privilege, and connection (cloud-only, hybrid, app, automation, etc.) for easier policy targeting.
- Lifecycle Planning: Map each account’s journey—creation, usage, rotation, review, and decommissioning.
- Recertification: Schedule periodic reviews of permissions and necessity—kill off or reduce access for unused or overprivileged accounts.
- Automation: Use scripts or governance platforms to help flag stale, orphaned, or misconfigured service accounts before they turn into audit problems.
Configuring Conditional Access Policies for Service Accounts
Now that the foundations are set, the real work begins. Building Conditional Access policies for service accounts in Entra ID isn’t just about turning features on—it’s about clear, precise scoping and making sure your rules do what you expect, where you expect, without blowing up core service integrations.
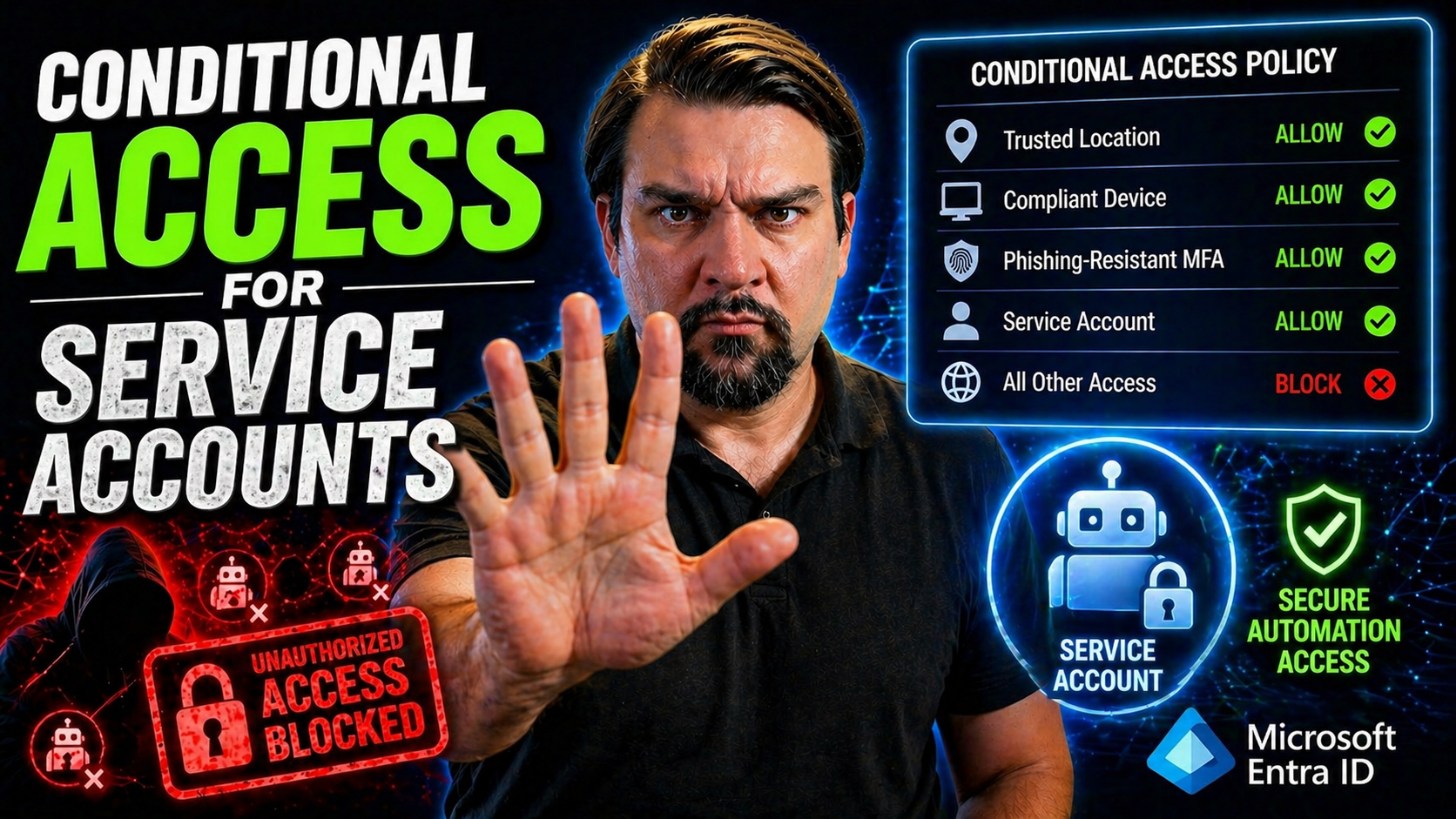
Here, you’ll move from planning to hands-on setup. First, you’ll pick who and what gets targeted with a policy—such as specific service accounts or Azure app registrations, and the precise cloud apps those identities access. Next, you fine-tune access controls: defining when to block, when to prompt for stronger proof, and when to allow access under strict conditions. And to reduce exposure? That’s where location-based restrictions and approved IP ranges come into play.
Whether locking down headless automation or the keys to your SharePoint castle, each subsection ahead breaks down actionable configuration steps. By the end, you’ll have policies that not only work, but also hold up against compliance demands and evolving threats.
Policy Assignments and Cloud App Configuration Steps
- Select Accounts or Groups: Assign Conditional Access directly to specific service accounts, service principal objects, or well-defined groups for granular control.
- Scope Cloud Apps: Choose which cloud apps (like Microsoft 365, SharePoint Online, or custom APIs) the policy will apply to, allowing for targeted enforcement.
- Verify Assignments: Cross-check that user accounts, automation principals, and managed identities all fall within desired policy boundaries.
- Staged Rollout: Test policy impact with “report-only” mode, then gradually roll out to your production environment to avoid service disruption.
- Update as You Grow: Periodically review and extend/restrict assignments as your service account landscape changes.
Access Controls, Block Rules, and Grant Conditions for Service Account Access
- Block Untrusted Sign-Ins: Set rules to block access for any service account sign-ins from unknown locations or high-risk scenarios.
- Enforce MFA Where Feasible: For service accounts that support interactive sign-in, require multi-factor authentication before granting access.
- Grant Conditions: Use “require compliant device” or “require hybrid Azure AD join” for accounts tied to infrastructure or endpoints that support device compliance.
- Scope Based on Risk: For privileged or sensitive service accounts, combine stricter grant conditions and “sign-in risk” policies for layered defense.
- Balance Security vs. Uptime: Adjust rules for essential “break glass” accounts to prevent accidental lockouts, but still monitor them closely.
Using Named Locations and IP Address Restrictions: Setup Allowed Addresses and Data Centers IPs
- Define Named Locations: Add trusted on-premises IP ranges or data center public IPs as “named locations” in Entra ID, limiting service account logins to safe zones.
- Geo Restrictions: Use country-based or region-based blocks for service accounts expected to operate only in specific regions (e.g., U.S.-based workloads).
- Allow-List Management: Regularly update allowed address lists as networks or third-party service providers change.
- Policy Enforcement Testing: Use simulation tools or “report only” modes to confirm only intended pathways are approved for critical service account sign-ins.
- Protect Against Misconfiguration: Set up alerts or automation to catch if a named location is accidentally removed or misapplied.
Advanced Security Measures and Risk-Based Access for Service Accounts
Service accounts may not click phishing emails, but attackers hunt for them anyway—often because they offer persistent, high-privilege access. To close those cracks, you need to move beyond basic Conditional Access and think in terms of ongoing monitoring, risk detection, and integrated controls across Microsoft’s ecosystem.
This section explores how to recognize and react to the warning signs that a service account is out of line. By blending Conditional Access with risk-based identity protection, you can detect unusual sign-ins, shut down suspicious activity, and keep a record of every access attempt for audit. Real-world attackers look for the forgotten and rarely watched—proper audit trails and behavioral baselines stop them cold.
It’s not just about locking the door, but also about knowing when someone tries to jiggle the handle. If you want to dig deeper into continuous compliance monitoring and how tools like Microsoft Defender for Cloud can prevent policy drift, check out this practical dive on compliance automation and risk management in cloud environments.
Blocking High-Risk Sign-Ins and Compromised Service Account Activity
- Enable Sign-In Risk Policies: Use Entra ID’s risk detections to automatically block or challenge sign-ins from service accounts flagged as high risk.
- Integrate with Identity Protection: Set rules that trigger when risky behaviors (impossible travel, location anomalies) are detected for non-human identities.
- Monitor with Logs: Regularly review sign-in logs to spot uncommon patterns—like sign-ins from unexpected IPs or at odd times.
- Set Alerts for Sensitive Accounts: Create custom alerts in Azure Monitor or Sentinel for any unusual activity involving privileged service accounts.
- Immediate Block upon Compromise: Configure auto-block rules so compromised accounts are cut off the second a red flag is raised.
Implementing Audit Tracking for Service Account Policies
- Leverage Azure Monitor: Use Azure Monitor to track Conditional Access policy hits and verify enforcement on service accounts.
- Integrate with Azure Sentinel: Centralize logs for advanced searching and alerting—spot trends, anomalous behavior, or unauthorized access fast.
- Review Built-in Audit Logs: Entra ID provides searchable logs of sign-ins and policy outcomes—schedule regular reviews for compliance reports.
- Automate Compliance Checks: Set up scripts or automation jobs to validate current policy coverage and spot policy drift or misconfiguration.
- Go Deeper with Microsoft Purview: Need full forensic visibility? Microsoft Purview Audit covers extended activity tracking, especially for high-risk environments.
Best Practices for Securing and Managing Service Accounts in Microsoft Entra ID
Even with detailed Conditional Access rules in play, your cloud is only as strong as your weakest service account. Long-term security comes down to managing secrets, reviewing permissions, and testing policies on an ongoing basis—not just at setup, but throughout the life of every non-human identity you maintain.
In this section, you’ll find strategies that go beyond quick fixes: start with secure secret storage (no more passwords in code or shared spreadsheets), then layer on regular review, rotation, and recertification. Don’t forget to test those access policies for edge-case conflicts and exceptions that crop up as environments evolve, especially during business growth or mergers.
This isn’t just compliance homework. It’s about building a stable, future-proof foundation so your operations stay safe even as the Microsoft 365 and Azure landscape keeps changing. For a broader perspective on why governance—and not just documentation—is critical for controlling policy drift and maintaining security at scale, dig into the details on enforced Azure governance strategies.
Azure Vault Secure Credential Storage for Service Accounts
- Centralize Credentials: Store all secrets, keys, and tokens for service accounts in Azure Key Vault instead of hard-coding them in scripts or configs.
- Automate Secret Rotation: Set policies to rotate credentials at regular intervals, preventing stale secrets from being exploited.
- Control Access: Use RBAC and access policies within Key Vault to tightly restrict who can view, change, or retrieve secrets.
- Enable Monitoring: Enable logging for all access to secrets—get alerts for unusual or unauthorized attempts.
- Integrate with Apps: Shift applications to programmatically pull credentials from Key Vault, eliminating secret sprawl across environments.
Building Lifecycle Processes and Recertifying Service Account Permissions
- Document Ownership: Each service account should have a clear owner responsible for reviewing access and permissions.
- Regular Recertification: Schedule quarterly or annual permission reviews to catch overprovisioned and stale accounts.
- Automate Deprovisioning: Use scripts or identity governance tools to flag and remove unused or orphaned accounts.
- Set Duration Limits: For temporary service accounts, apply expiration dates and automatic disablement after project end.
- Adopt Automated Recertification: Use tools that kick off periodic recertification campaigns for sensitive or privileged service accounts.
Resolving Conflicts and Testing the Policy for Service Accounts
- Simulate Policy Impact: Use Entra ID’s “report-only” mode or custom scripts to test Conditional Access effects on service accounts without blocking real traffic.
- Troubleshoot Blockages: Investigate failed sign-ins in audit logs, focusing on overlapping or conflicting policy assignments.
- Refine Policy Scopes: Adjust policy assignments and exceptions to avoid accidental service disruptions during upgrades or migrations.
- Monitor for Unintended Access: Run scheduled or automated tests that flag accounts with more access than intended as environments evolve.
- Establish Validation Workflows: Implement a regular policy validation cadence, reporting findings to stakeholders for accountability and compliance.
Exclusions, Policy Refinement, and Maintenance for Service Account Access
Even the most airtight Conditional Access policies need a safety valve—especially when business-critical apps rely on specific service accounts. That’s where exclusions and ongoing refinement come into play. These aren’t shortcuts for convenience but tools to keep your essential services online while minimizing security exceptions to only what’s truly necessary.
To apply exclusions the right way, start by identifying truly essential accounts—think emergency break-glass users or legacy services with unique protocol needs. Tune exclusions tightly: set conditions based on required properties (like only from secured locations or during maintenance windows) to shrink the attack surface. Always document reasons for each exclusion and revalidate regularly.
As the environment evolves, so should your rules. Review client and app-specific requirements, especially when new integrations or acquisitions enter the picture. Watch out for outdated protocol dependencies; where Conditional Access can’t fully protect you, lean on network segmentation or app-layer controls as backstops. Fine-tuning is never one-and-done: schedule reviews so that what works this quarter won’t catch you off-guard the next.
Keeping that balance between lock-tight security and reliable uptime means you avoid the risk of accidental lockouts, service outages, or shadow admin accounts flying under the radar. Policy refinement is what takes good governance and makes it sustainable—year after year.
Summary, Next Steps, and Further Reading on Conditional Access
- Master Identity-Centric Access: Put identity at the center for every service account—only then do Conditional Access policies hold up under scrutiny.
- Get Your Prerequisites Right: Double check licensing, role assignments, and policy scoping before rollout to avoid costly gaps and missteps.
- Deploy, Test, Refine: Use report-only modes and continuous audit tracking to validate that your rules work as intended, then refine as your needs change.
- Never Stop Improving: Make periodic policy reviews and recertifications a part of your operational routine, not just a compliance box.
- Go Deeper: For more on tackling Conditional Access sprawl and building robust, monitored frameworks, see this policy trust issues guide and the must-listen Entra ID Conditional Access podcast.
Your Privacy, Cookies, and Content Recommendations
Your privacy matters, so we take steps to protect your data and give you control over cookie settings while you explore our site. Cookies are used for basic site performance, security, and personalized content recommendations—never for selling your information or invading your privacy.
If you want more information about privacy policies, cookie management, or your digital rights, our privacy notice offers clear, easy-to-understand guidance. While you’re here, don’t forget to check out our recommended reads on Microsoft Entra ID, cloud governance, and secure authentication strategies. We keep your browsing confidential while pointing you toward the topics that matter most for building first-class, cloud-first identity security.











