Copilot Security Misconfigurations to Avoid: Essential Risks and Remedies
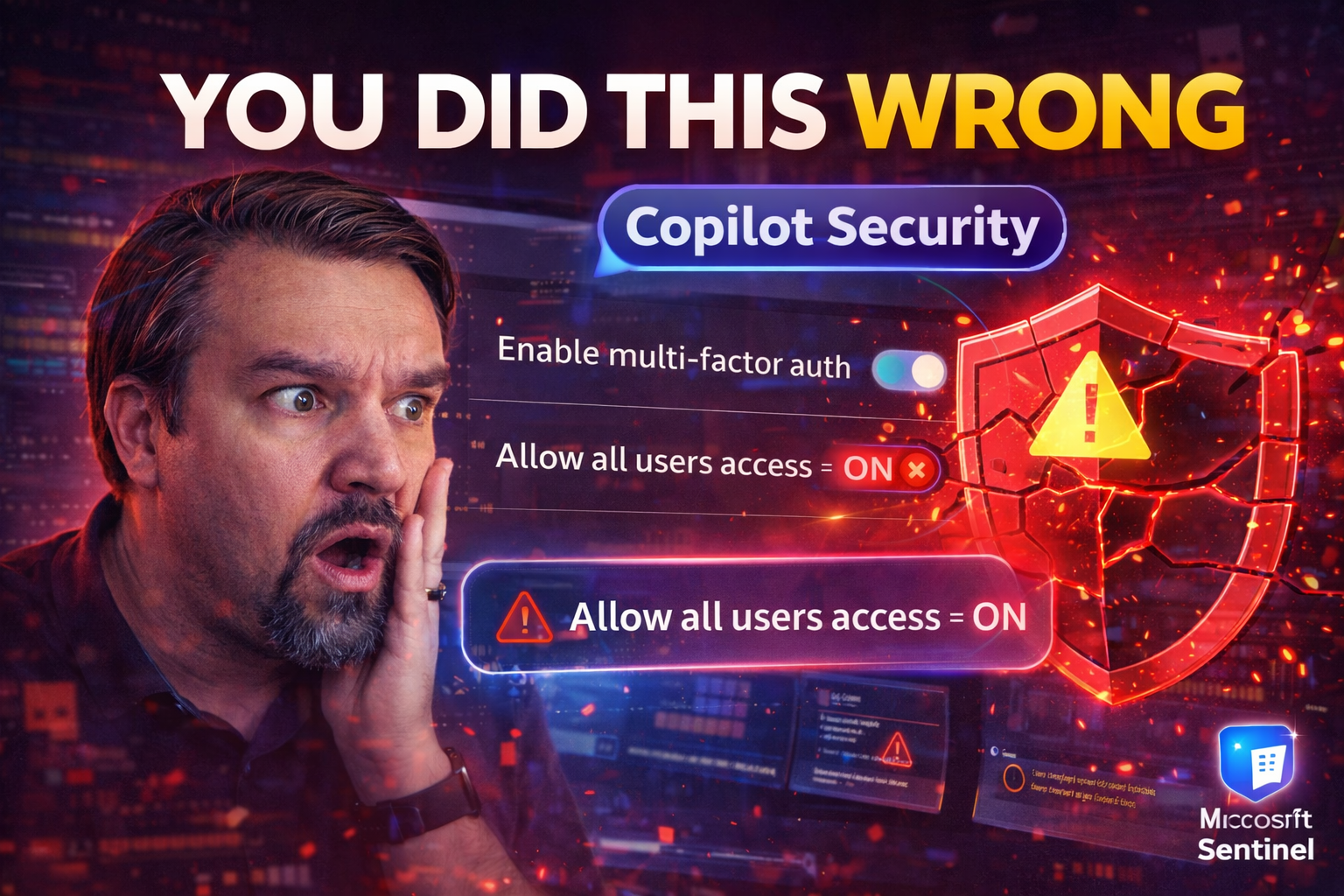
With Microsoft Copilot becoming a household name in enterprise collaboration and automation, security teams have their work cut out for them. These AI-powered tools can amplify productivity—but a single security misstep can expose sensitive data or open doors to attackers that you’d never want invited in. That’s why understanding and avoiding Copilot security misconfigurations isn’t just a technical checkbox—it’s mission critical.
The landscape is shifting fast. As Copilot weaves into SharePoint, Teams, and your broader Microsoft 365 estate, old permission models and oversight strategies just don’t cut it. This guide covers the main minefields: misconfigured permissions, weak authentication, excessive agent sharing, and sneaky, advanced attack vectors unique to Copilot’s world. The risks can be subtle, but the fallout is anything but.
If you want your Copilot deployment to be secure—not just another project with good intentions but bad outcomes—stick with us. We’ll break down both the obvious gotchas and hidden gotchas lurking in Copilot, so you can keep pace with both foundational and emerging threats.
Top Copilot Security Misconfigurations and How to Detect Them
If you’re managing Copilot in any serious way, knowing about everyday misconfigurations is half the battle. It's not just about ticking off a technical checklist—it’s about understanding how mistakes happen and how to spot them before they put you on the front page for all the wrong reasons.
With complex AI tools like Copilot, “set it and forget it” just isn’t an option. Tiny oversights—like accidentally sharing agents too broadly or missing a rogue setting—can create big holes in your defenses. Attackers love finding these gaps, and even low-skilled folks can stumble across exposed data if your controls are loose or your detection isn’t tuned to Copilot’s unique risks.
Up next, we’ll break down what high-risk Copilot configurations look like in real life, and we’ll get into the specifics of why sharing agents with broad groups (or even your whole org) can quickly spiral into a security headache. You'll see what warning signs to watch for and how to stay one step ahead with practical detection tips and real-world scenarios.
Detecting High-Risk Copilot Configurations and Potential Security Threats
- Unusual Agent Sharing Patterns: Watch for Copilot agents shared with “Everyone,” large security groups, or even external users. These broad shares are classic red flags and can be detected by reviewing your agent directory for overprovisioned agents, especially those with access to sensitive or regulated data.
- Agents Running With Excessive Privileges: Look for agents—especially those using Model Context Protocol (MCP) tools—that have Graph API permissions like Sites.Read.All or Mail.Read. Excessive permissions often mean an accidental bridge to inboxes, document libraries, or broader organizational secrets.
- Lack of Monitoring on Agent Activity: Many Copilot events don’t show up in standard audit logs. Make sure you’re using advanced monitoring (e.g., Microsoft Purview and Sentinel) to track agent-triggered actions. Pay attention to blind spots such as outbound HTTP requests, automated file access, or unlogged agent behaviors. For a deeper dive into filling these gaps, check out this guide on least-privilege Graph enforcement and AI-driven monitoring.
- Unusual Data Access Patterns: Sudden spikes or off-hours data pulls can signal misuse or compromised agents. Baseline normal agent behavior, then flag outliers using automated anomaly detection.
- Unmonitored Third-Party Integrations: Pay special attention to agents connected to external APIs or tools. Unvetted or overly broad connections can leak data and often evade your traditional M365 controls.
Combining technical reviews with behavioral monitoring is your best shot at catching these before they turn into newsworthy incidents.
Risks When Agents Are Shared With Broad Groups or the Entire Organization
- Unintended Data Exposure: When Copilot agents are available to large groups or the whole company, sensitive or confidential data can be surfaced to people who never had business seeing it. Copilot can aggregate and present docs, emails, and transactions pulled from sprawling access rights. One wrong query, and you’ve got widespread, silent leaks.
- Permission Sprawl and Audit Complexity: The more widely agents are shared, the tougher it becomes for admins to track and audit who actually has access—or what they’re able to do. Permission sprawl makes it easy for oversight to slip through the cracks, especially as org structures and personnel change over time. For more on the dangers of sprawl and a framework to regain control, see this practical piece on governance collapse and agent outpacing.
- Shadow Automations and Policy Blind Spots: Agents shared too broadly often trigger shadow processes—workflows and automations no one is actually monitoring. This creates operational chaos, unpredictable results, and legal exposures. Effective governance requires clear agent identities and contract enforcement to prevent identity drift and data mishandling.
- External and Supply Chain Risk: It’s not just insiders. Agents accessible by vendors, contractors, or integrated apps can escalate a minor misconfiguration into a vendor data breach or bring sensitive info into the crosshairs of supply chain attacks.
- Risk of Loss of Accountability: Broadly shared agents dilute accountability. When everyone can access or trigger an agent, no one feels ownership for what it retrieves, posts, or changes—making clean-up and forensics a pain after something goes wrong.
To keep agent access under control, set and periodically review agent sharing boundaries, leverage role-based access controls, and act quickly on audit findings. Build a governance model that prevents broad exposure before you have to mop up the aftermath.
Critical Authentication and Authorization Failures in Copilot Agents
Even the slickest Copilot deployment can unravel fast if authentication and authorization aren’t airtight. With agents acting autonomously, any hole in their design or management can spell disaster—giving attackers or careless insiders a straight shot at sensitive information.
The real trouble starts with agents that skip proper authentication or embed static secrets, which attackers can easily harvest or reuse. It gets worse if these agents inherit “maker” or author-level privileges by default—especially when using MCP tools or poorly scoped Graph API permissions. All this adds up to an agent doing a lot more than it should be allowed, and you might not even know until it’s too late.
In each scenario ahead, we’ll break down the root of these misconfigurations and the ways they can open doors to unauthorized data access or privilege escalation. By understanding these pitfalls, you’ll be better equipped to set up strong controls, avoid common mistakes, and put real teeth behind your Copilot governance. If you want to see how contract-driven controls and technical enforcement come together, dig into these hands-on governance strategies for Copilot.
Scenario: Agents Without Proper Authentication Increase Breach Risks
- Open Entry Points: Agents that don’t enforce user authentication allow anyone (internal or sometimes even external) to trigger actions, access business data, or perform automated tasks—no questions asked.
- Untraceable Data Exfiltration: Attackers can exploit unauthenticated agents to extract sensitive documents or send information to outside accounts, often without triggering traditional security alerts.
- Ease of Misuse: Non-technical users—or malicious insiders—can accidentally or intentionally run agents they should have no business accessing, greatly increasing insider risk.
- Mitigation: Always enforce authentication and role checks on all agents, and regularly audit access patterns for suspicious triggers.
Scenario: Hardcoded Credentials and Secrets Embedded in Agent Logic
- Static Secrets Exposure: API keys or passwords baked directly into agent logic can be discovered via code review, configuration leaks, or even by end users, making them easy targets.
- Credential Theft and Lateral Movement: Once attackers find hardcoded credentials, they can jump to systems with broader access, sometimes bypassing MFA and other frontline defenses. For a real-world analog with OAuth abuse, review how attackers exploit Entra ID consent loopholes.
- Best Practice: Store secrets in secure environments (e.g., Azure Key Vault), use managed identities, and rotate keys regularly to prevent stale or reused credentials from becoming attack vectors.
Scenario: Agents Using Author Authentication and Model Context Protocol (MCP) Tools
- Privilege Escalation via Maker Permissions: Agents that inherit the creator's (maker’s) permissions can access far more data and perform wider actions than necessary—especially if the maker is an admin. Overprovisioned Graph API scopes (like Mail.Read or Sites.Read.All) are prime culprits.
- Undocumented Access Paths: MCP tools often enable agents to side-step documented policies, creating undocumented access routes to data no one expected. This is a textbook way that controls get bypassed during rapid buildouts and “citizen developer” initiatives.
- Oversight Failure: During reviews, these agents are often rubber-stamped since they appear “internal” or “trusted.” In reality, their blast radius is much larger and more ambiguous than most realize.
- Long-Lived Tool Permissions: When MCP tool authorizations outlive the original maker (think promoters who left or changed roles), these agents retain powerful keys—keeping backdoors open for attackers or accidental misuse. To learn how to tame this tiger in citizen-development environments, see these best practices for Power Platform governance.
- Recommended Controls: Enforce least-privilege permission assignments, restrict MCP tool authorizations to tight scopes, and use automated workflows to review and revoke stale permissions or abandoned tools.
Data Exposure Risks From Poor Access Controls and Oversharing
Let’s be real—Microsoft 365 is already a labyrinth of files, chats, folders, and channels. Throw Copilot into the mix, and those weak spots in your access controls can go from “hidden hazard” to headline news overnight. When Copilot draws from SharePoint, OneDrive, and Teams, any missteps in permission boundaries or data residency blow up your attack surface.
Inadequate controls let Copilot surface files and messages you never meant to show, sometimes bleeding internal information outside the walls of your organization. That’s not just a breach waiting to happen—it’s a direct line to compliance debt and regulatory trouble if that data crosses borders or lands in the wrong hands.
The next sections break down how these access control mistakes play out specifically in SharePoint, OneDrive, and Teams. You’ll get the lowdown on real-world oversharing issues, plus a closer look at compliance nightmares tied to residency and data classification failures. Want a jumpstart on disciplined Microsoft 365 governance and why it matters now more than ever? Tune in to the advice on enforcing structures and permissions early in SharePoint and Power Platform, and learn how to use Data Loss Prevention checks in DLP best practices for automation environments.
Data Oversharing and Residency Issues in SharePoint, OneDrive, and Teams
- Default Permissions Are Too Broad: Many Teams channels and SharePoint document libraries default to “Everyone” or “All Company” access, which means Copilot can pull and surface files that were never meant for broad consumption. It only takes one misplaced folder for sensitive data to be one search away.
- Unmonitored External Sharing: Users sometimes share OneDrive or SharePoint folders with external partners, but those links can persist and allow Copilot to fetch content from beyond your intended boundaries. Enhanced tenant-level auditing is a must—here’s a framework to catch blind external sharing in real time.
- Poor Data Residency Hygiene: Files stored on the wrong regional servers can land you in trouble, especially when Copilot bridges data from one region to another, running afoul of regulatory lines.
- SharePoint List Governance Collapse: When SharePoint Lists or other repositories lack structured governance, you get sprawl, throttling, and accidental exposure—especially when used as a data backend for automations. For why Dataverse beats SharePoint Lists for sensitive data, see the case for Dataverse in secure Power Platform scenarios.
- Lack of Permission Reviews: Without regular reviews and proactive monitoring, old ad hoc shares persist indefinitely, and Copilot keeps surfacing them in unexpected (and risky) ways.
The top fix? Harden your permission boundaries, review where your sensitive assets actually live, and automate audits so risky shares don’t go unnoticed.
Compliance and Regulatory Risks From Unchecked Data Access
- Cross-Border Data Residency Violations: If Copilot/agents pull data from outside compliant regions (e.g., EU vs US), you’re open to regulatory penalties and headaches.
- Unclassified or Unlabeled Sensitive Data: When files lack DLP or sensitivity labels, Copilot can expose confidential info to unapproved users or agents—putting organizations under HIPAA, GDPR, or financial sector rules at extra risk.
- Audit/Reporting Failures: Without continuous compliance monitoring, data changes made by agents go untracked. Check how to close these gaps in real-time compliance automation guidance and get the truth about hidden policy drift in this deep dive on compliance drift.
- Proactive Strategies: Deploy automated labeling, align with regulatory boundaries, and implement real-time compliance monitoring for ongoing coverage.
Orphaned, Dormant, and Unmonitored Agents: Hidden Security Risks
It’s wild how fast Copilot agents can multiply—then get forgotten in the corners of your tenant. Orphaned or dormant agents and old, unused connections are like keys hanging by the front door; it’s only a matter of time before someone uses them, and maybe not the way you intended.
Without active ownership or monitoring, these agents become tasty entry points for attackers. Orphaned agents linger on long after their creators exit the company, sometimes with access to goldmines of sensitive data. Dormant, misconfigured automations can be reactivated by threat actors or simply exploited as silent levers for internal mistakes and external breaches.
Coming up, we’ll map out the top risks when agents aren’t actively managed—including what happens when you let ownership and inventory slip through the cracks. We’ll also give you a playbook for treating all agents (even unused ones) as production assets deserving regular review. To understand how shadow agents and lack of governance open you up to disaster, tune into Agentageddon – where agents outpace governance.
Orphaned Agents With No Ownership: Top 10 Hidden Risks
- Unmonitored Data Access: Orphaned agents retain their access—often elevated—and can be triggered intentionally or accidentally, surfacing data that should be locked down.
- Silent Policy Drift: Policy updates or new labeling don’t apply, because the agent’s configuration is frozen in time, opening blind spots in compliance.
- Stale Credential Storage: Old agents use historic secrets, maker credentials, or authorizations that should be revoked—prime bounty for attackers.
- Lack of Forensic Trails: No assigned owner means no clear point of contact during incident response or breach investigation, causing forensic dead ends.
- Bypassed Access Reviews: Orphaned agents escape regular access reviews; their permissions persist long after relevance.
- Automations Gone Wild: Without stewardship, these agents often trigger legacy automations or unmanaged processes, which can cause operational mayhem or compliance violations.
- Easy Targets for Attacker Pivoting: Threat actors (external or insider) can hijack orphaned agents to move laterally or escalate privileges undetected.
- Sensitive Configuration Sprawl: Orphaned agents often have complex, undocumented setups—hidden cross-system access becomes easy to miss.
- Audit Gaps: With no accountable owner, orphaned agents may never be flagged in access reviews or security audits.
- Compliance Breakdown: Regulations typically require assigned data/process owners. Orphaned agents put you straight into noncompliance land. For practical steps on enforcing ownership and preventing shadow IT, read more at Microsoft 365 Data Access Ownership Governance and Shadow IT Governance.
Dormant Agents and Unused Connections as Long-Term Attack Vectors
- Untracked Attack Surface: Dormant agents offer attackers hidden, persistent doors into your organization, sometimes surviving security upgrades or cleanups for years.
- Credential Time Bombs: Unused connections may retain valid tokens, secrets, or OAuth grants, allowing reactivation by attackers even after user departure.
- Bypassing Security Monitoring: Security ops tend to monitor what’s active and lively—not what’s dormant and gathering dust. Attackers exploit these gaps with patience.
- Reactivation Scenarios: Threat actors (or even new employees) accidentally discover and reactivate these agents, leveraging them for data exfiltration or business email compromise.
- Escalation Paths: Many dormant agents are tied to privileged makers or contain legacy certificates/keys. Breaching them can open up admin-level lateral movement.
- Data Drift: Unused agents may hold, move, or log sensitive data in unexpected places, making incident response and forensics messy.
- Blind Spots for Compliance: These agents rarely appear in compliance reports—until regulators or auditors come knocking.
- Resilience in Shadow IT: Dormant agents can outlast hygiene sprints and purge campaigns, continuing to operate in the shadows especially in platforms like Microsoft Foundry or custom SaaS hooks (why Foundry presents new risks).
- Recommended Actions: Treat dormant agents as live production assets—review your agent inventory, rotate credentials, and use Microsoft Purview Audit Premium for deep, continuous monitoring and incident readiness.
Proactive Mitigation and Governance Strategies for Secure Copilot Deployment
So, you know the minefields—now it’s time to make sure you never step in them. Smart organizations don’t rely on luck; they set up proactive governance, put robust policies in place, and act fast when Copilot misconfigurations are spotted. The key is building security steps into every part of your Copilot journey, from agent setup to ongoing review.
Effective mitigation requires more than reactively fixing what’s broken. You need a living playbook, ready to detect risky agents and configurations, audit regularly, and close out missteps before they become full-blown incidents. Combine technical controls—like DLP and tenant isolation—with governance measures, such as least-privilege access, role separation, and regular stewardship check-ins.
Coming up, we’ll outline how to build an operational playbook, set up solid governance, and dodge the classic pitfalls that trip up unwary Copilot rollouts. For advanced approaches, study how DLP and Purview transform Copilot agent governance and the real-world mandate for Governance Boards in controlling AI risk.
Building a Mitigation Playbook for Copilot Security Findings
- Inventory and Baseline Agents: Start by mapping all active, dormant, and orphaned agents. Know what’s out there, what data they touch, and who owns each. Use automated inventory scans if your environment is complex.
- Review Permissions and Connections: Audit agent permissions for least-privilege compliance and scrutinize external integrations. Look for agents with broad Graph API access, excessive data scope, or unvetted third-party connectors.
- Monitor Access and Activity: Set up logging for agent-triggered actions using Purview Audit, Sentinel, and custom alerts. Look for spikes, off-hours triggers, and patterns that don’t fit your normal business rhythm. If you’re missing real-time controls, see why separating experience and control planes is essential.
- Remediate Misconfigurations: Remove broad shares, rotate static credentials, and revoke unused or excessive authorizations. Follow up with user notifications for changes that impact service.
- Document, Communicate, Repeat: Keep clear documentation of findings, owner assignments, and remediations. Make security reviews and audits a recurring calendar item—not a one-time event.
Establishing Copilot Governance and Least-Privilege Access Permissions
- Define Clear Governance Policies: Write down who can deploy, manage, and approve Copilot agents. Spell out boundaries for agent functionality, access, and third-party integrations. Combine people, process, and technology—automated controls alone aren’t enough (debunk the governance illusion).
- Enforce Least-Privilege by Default: All agents and connectors should start with minimal permissions—grant access for what’s needed, and nothing more. Use scoped roles and separation of duties to cut off privilege creep.
- Segment and Monitor Sensitive Agents: Separate high-risk agents (those touching PII, finance, HR) from lower-risk ones. Apply advanced monitoring and DLP controls, leveraging tools like Microsoft Purview and Defender. Conditional access policies and environment segmentation help (see these essential security settings and monitoring steps).
- Regular Reviews and Training: Make least-privilege reviews recurring, with evidence trails. Offer governance training for both IT and the business, keeping everyone aligned as features evolve.
Avoiding the Most Common Copilot Rollout and Implementation Problems
- Don’t Treat Copilot Like a Simple Plugin: Copilot is a power tool, not an add-on. Skipping setup, governance design, or user training leaves you wide open for security and operational mistakes (read up on hidden risks in Copilot Notebooks).
- Include Security, Not Just Admins: Too often, Copilot rollouts bypass security teams. Get security folks involved from day one, not as an afterthought.
- Assess and Upgrade, Don’t Band-Aid: Review your current environment and anticipate upgrades needed for secure Copilot ops, not just basic compatibility.
- Practice Rollout Empathy and Tailored Enablement: Understand business needs—don't force a one-size-fits-all approach. Different teams require different Copilot access and controls.
- Monitor Outputs as Well as Inputs: Treat AI-generated data as first-class content—label and protect it with governance policies. For more on this, delve into advanced governance for Copilot outputs.
Advanced Threats and Emerging Vulnerabilities in AI-Powered Copilot
The move to AI-powered Copilot amps up the threat landscape with novel attack vectors and some pretty sneaky techniques. It’s not just about accidentally sharing data—attacks now come in forms you might have never seen before. Threat actors are leveraging prompt injection, zero-day exploits, and silent exfiltration channels far beyond what classic security teams expect.
AI agents can be manipulated to leak sensitive info via prompt injections, while misconfigured actions (like outbound HTTP requests or bulk email sends) give attackers covert data-leak routes. Even worse, zero-click exploits like EchoLeak allow for compromise with no user interaction at all—meaning your risk surface is growing whether you see it or not.
The next few sections dive into how these AI-specific threats play out. You’ll get a clear definition of prompt injection, see how agents are used for covert data exfiltration, and learn about real-world zero-click vulnerabilities. For a live breakdown of modern Microsoft 365 attack chains—including consent phishing and token abuse—read this in-depth breach analysis and actionable detection tips.
Prompt Injection Attacks and Manipulating Copilot Queries
Prompt injection attacks occur when a user or attacker sneaks malicious instructions into Copilot’s input prompt, causing it to ignore controls or leak confidential data. In this attack, Copilot is tricked into revealing more information than it should, either by inserting special strings or exploiting weak filter logic in the prompt. Real-world cases include extracting sensitive SharePoint files or manipulating agent workflows to bypass intended restrictions. The best defense is layered prompt sanitization and constant tuning of your detection and logging controls as Copilot evolves.
Data Exfiltration via Email and HTTP Request Actions in Agents
- Outbound Email Leak Paths: Agents misconfigured to send emails can be co-opted to route sensitive files or summaries to personal or external accounts—often slipping past traditional DLP unless outbound patterns are closely audited.
- HTTP Request Exploitation: Some agents can issue raw HTTP requests. Without strict rules, attackers (or careless configurations) can send internal reports, datasets, or PII straight to unknown external services.
- Detection Strategies: Establish alerts for agents triggering outbound comms or network requests—match volume, destinations, and time-of-day for quick anomaly detection. For proactive DLP governance, check these connector classification strategies to prevent silent, agent-driven leaks.
Dealing With EchoLeak and Zero-Click Vulnerabilities in Copilot
- Silent Compromise Risks: EchoLeak and similar zero-click vulnerabilities allow attackers to exploit Copilot environments without any user action. Infections are invisible and don’t require convincing someone to click a bad link.
- Incident Example: An unmonitored Copilot agent with broad Graph API permissions is targeted by an actor who exploits a protocol-level flaw to gain access to organizational files and emails, leaking data before anyone even notices.
- Detection and Mitigation: Enable advanced Entra and Sentinel analytics, restrict app consent, and bind tokens to device/user pairs where possible. Policies alone are not enough—proactive monitoring and binding controls offer the best defense. For detailed attack chain walkthroughs, reference this breakdown of M365 real-world attacks.
- Response Playbook: Treat Copilot and its agents as critical assets, and ensure that every security incident review looks for zero-click indicators—even if there’s no suspicious activity in traditional user logs.
Conclusion and Key Takeaways for Securing Microsoft Copilot
All the advice, warnings, and examples boil down to one thing: Copilot needs a disciplined approach to security. The stakes are high and the attack surface is broad, especially as AI-driven automation spreads across your Microsoft 365 environment. Security teams can’t afford to let old habits or incomplete controls drag them down when it comes to Copilot deployments.
Remember, Copilot’s risks aren’t limited to rogue insiders or external hackers. Simple misconfigurations, ignored agent inventories, or lax permission models can do just as much damage as any intentional attack. The best way to protect your environment? Blend proactive technical defenses, policy controls, and human oversight every step of the way.
In the next list, we’ll run through the essential takeaways for boosting your Copilot security posture—plus point you to deeper, advanced resources to keep your edge. Whether you’re new to Copilot or wrangling a complex, multi-team deployment, you’ll want these must-dos at the top of your weekly checklist.
Key Takeaways and Immediate Steps for Copilot Security
- Audit Your Agents: Inventory active, dormant, and orphaned Copilot agents now. Assign clear owners and review permissions—don’t wait for a breach.
- Enforce Least-Privilege Everywhere: Restrict agent permissions to only what’s absolutely required. Lock down Graph API scopes, connectors, and third-party integrations.
- Monitor and Alert: Turn on advanced monitoring tools (Purview, Sentinel) and set alerts for unusual agent actions, not just user behavior.
- Label and Protect AI-Generated Data: Treat Copilot’s outputs with the same governance controls as sensitive files—apply labels, track sharing, and limit downstream exposure.
- Keep Learning: Build an internal Copilot Learning Center to drive adoption, reduce support chaos, and align on security and compliance goals (see an example here). For mature risk playbooks and advanced safe governance, study these proven best practices.
Insecure Third-Party Integrations in Copilot Agents
Plugging Copilot into external APIs, SaaS platforms, and third-party integrations opens up a fresh box of risks. You’re not just dealing with your own misconfigurations anymore—now you’re responsible for how outside systems handle and protect your organization’s data.
Unvetted or poorly scoped connections can create data highways straight out of your Microsoft 365 estate, often bypassing DLP and classic audit controls. Worse, most organizations aren’t logging these flows or monitoring the health and security posture of their entire integration chain. That means a supply chain breach or misstep on a partner platform can rapidly become your problem.
The following sections spotlight how these risks play out—from agents with wild, unchecked permissions to gaps in cross-platform logging and reporting. For forward-thinking guidance on taming AI-powered shadow IT and regaining visibility, check out the evolving strategy for controlling agent-driven integrations.
Risks of Unvetted External API Connections and Data Flows
- Over-scoped Permissions: Agents granted excessive rights to external APIs allow more data to flow out than intended, often unnoticed by traditional controls.
- Unvetted Vendor Integrations: Plugging Copilot into CRMs, payment platforms, or marketing tools without review can surface confidential data in external systems that have weaker security postures.
- Supply Chain Vulnerability: Breaches or bugs in partner systems can lead to lateral movement, with attackers using those systems to pivot back into your Copilot environment.
- Quick Fixes: Always vet the scope and purpose of third-party integrations. Limit API permissions and use conditional monitoring to flag unexpected data flows.
Lack of Monitoring for Cross-Platform and SaaS Data Sharing
- Unlogged Data Transfers: Most audit logs focus on native M365 actions, missing outbound data flows to SaaS or external APIs. Key Copilot events may simply vanish from your reporting, making it hard to spot leaks.
- Lack of Real-Time Alerting: Without real-time monitors on agent actions, external data sharing goes unnoticed until after the damage is done—if it’s noticed at all.
- Operational Blind Spots: SaaS platforms may not have health or risk alerts integrated into your security tools, so cross-platform threats fester in the background.
- Closing the Gap: Deploy advanced monitoring, pull logs from both Copilot and integrated SaaS APIs, and use solution-aware environments to trace agent-driven transfers. For more strategy, dive into AI agent governance for third-party and SaaS integration risks.
Copilot Security Misconfigurations: Risk Comparison











