Hybrid Identity Security Risks: Identifying Hidden Gaps in On-Premises and Cloud Environments
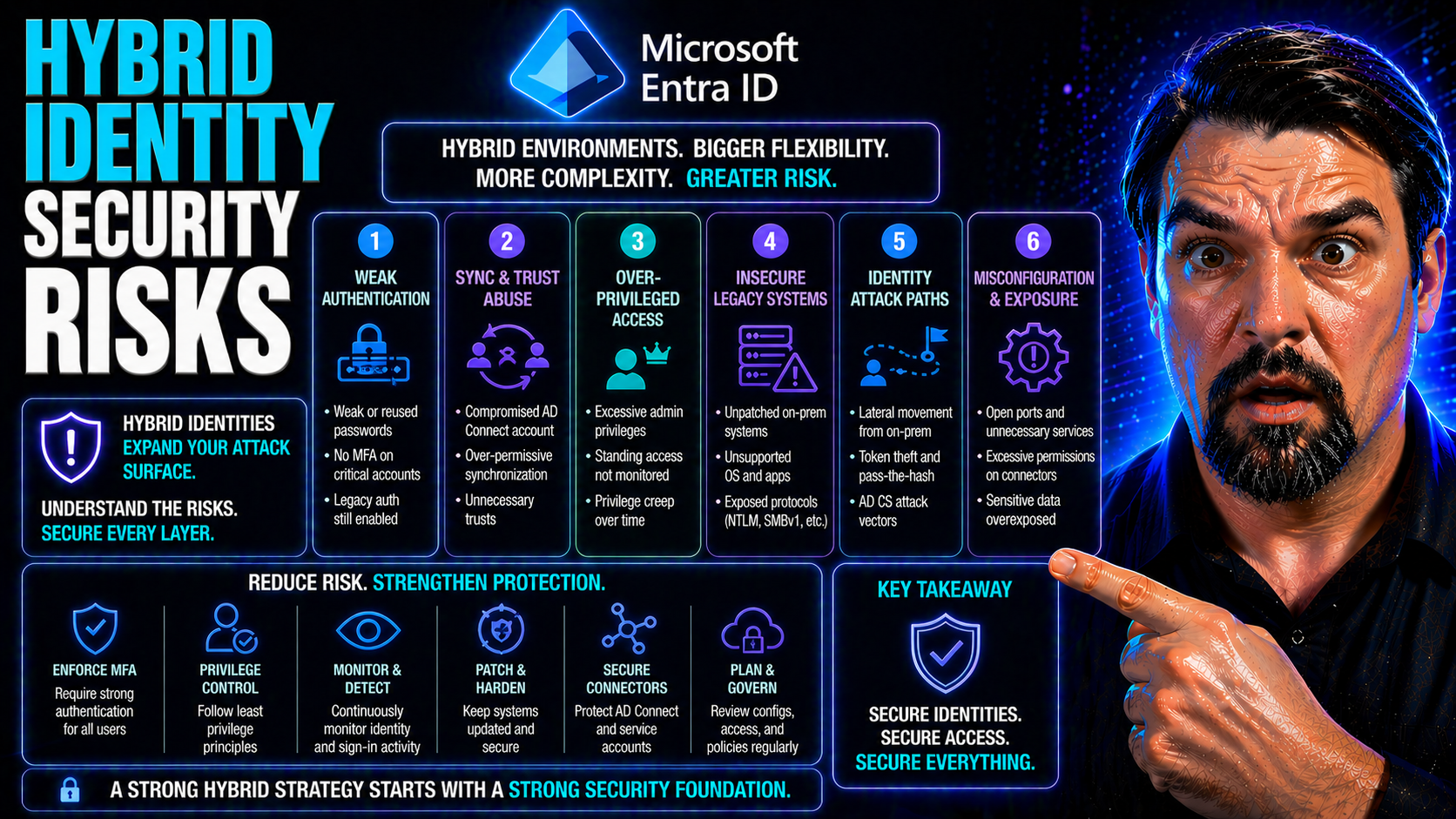
Hybrid identity security is now a frontline issue for organizations that blend on-premises Active Directory with cloud-based identities like Microsoft Entra ID. As companies shift to hybrid IT, their attack surface grows, connecting legacy systems with modern cloud services. This broader surface introduces new complexities—the more interconnected your environment, the more likely misconfigurations, identity drift, and overlooked privileges will create invisible vulnerabilities.
Mistakes in deploying or managing hybrid identity systems can have real-world consequences. Attackers know how to exploit the weakest connections between your on-prem and cloud directories, often moving laterally until they reach sensitive data or high-value accounts. Understanding these risks is essential, especially as hybrid environments become the default for organizations using Microsoft 365 and Azure. Solid identity security is no longer just an IT problem—it's foundational for protecting your business from modern threats.
Understanding Hybrid Identity Security Risks and Their Real-World Impact
When you bring together on-premises Active Directory and cloud-based services like Microsoft Entra ID, identity management becomes far more complicated than running each silo separately. Hybrid identity setups promise seamless access and single sign-on, but they also weave a complex web where even minor configuration issues can have major consequences. Each component—directory synchronization, authentication methods, and privileges—must align perfectly to avoid dangerous blind spots.
Why does this matter? Attackers have evolved to exploit both technical gaps and operational oversights unique to hybrid identity. From a distance, a hybrid approach can seem robust, but underneath, latent misconfigurations and unsynchronized accounts often undermine your defenses. Real-world incidents frequently begin with identity compromise on-premises and spill over to cloud apps, or vice versa. The technical bridge that hybrid identity provides—intended to simplify business—also becomes an avenue for lateral movement if not secured properly.
As you navigate the world of hybrid identity, understanding these foundational risks is critical. By recognizing the interplay between on-premises and cloud systems, you’ll be better equipped to protect against emerging threats and ensure business continuity. In the sections ahead, you'll learn how attackers spot and exploit hidden vulnerabilities, and how continuous monitoring and well-architected controls can help close these gaps before they are breached.
The Hidden Dangers of Hybrid Identity Misconfigurations for MSPs
Hybrid identity misconfigurations are among the most dangerous risks for managed service providers (MSPs) and IT teams overseeing multiple clients or tenants. When connecting on-premises Active Directory to cloud platforms like Microsoft Entra ID, small setup mistakes can introduce significant vulnerabilities. Common issues include incomplete synchronization, mismatched account policies, and insufficient administrative separation between environments.
One key pain point for MSPs is the struggle to enforce consistent security identity hybrid controls across both legacy and cloud systems. These inconsistencies often result in overlooked accounts, duplicate privileges, and shadow permissions that attackers can exploit. If privileged accounts aren't tightly governed, a breach in one system can allow attackers to pivot across hybrid boundaries undetected.
Modern environments need more than default security. When MSPs and their clients rely only on surface-level policies, it’s easy for governance to fall behind the rapid changes in both human and AI-driven automation. AI technologies like Microsoft Copilot and Power Automate can outpace governance, contributing to silent risk accumulation. For practical strategies, conversations like those in this episode about governance and agent risk can help clarify how visible, enforceable controls are essential to regain compliance and keep configuration drift in check.
OAuth consent also requires vigilant management—misconfigured consent processes in Entra ID can allow attackers to bypass multifactor authentication and maintain persistent access, even after a password reset. This detailed analysis of OAuth consent attacks underscores why it’s necessary to lock down user consent and enforce strict admin oversight, helping MSPs avoid the dangers that come with unchecked hybrid growth.
Real-World Risks: Identity, Cloud, and Network Attack Paths
Hybrid environments are fertile ground for attackers, particularly when identity controls are misaligned across on-premises and cloud systems. Attackers frequently begin by harvesting compromised credentials—sometimes from a legacy Active Directory environment—and use those footholds to explore network paths leading to your most valuable cloud apps like Microsoft 365.
Breach scenarios often play out with startling speed. For example, a single phishing email might compromise a user’s on-premises account, but if synchronization is loosely managed, that compromise can propagate to cloud resources. Sophisticated attackers chain weaknesses—like stale passwords and over-permissioned cloud apps—creating seamless "path identity" bridges for lateral movement. Continuous monitoring and cross-platform policies are often the only lines of defense against these paths.
Real-world Microsoft 365 attack chains provide clear warning signs. Consent phishing, adversary-in-the-middle (AiTM) token theft, and OAuth abuse are being used to bypass even strong multifactor authentication setups. Advanced detection methods, including deep Entra logs and proactive consent governance, are now essential. For a closer look at how these breaches unfold and how organizations can defend against them, this in-depth breakdown of Microsoft 365 attack chains is highly instructive. These insights show that your security posture is only as strong as the weakest link—in both identity and network controls.
Continuous Monitoring for Lateral Movement Across Hybrid Environments
Attackers consistently aim to move laterally between your on-premises AD and cloud identities, looking for pathways to escalate privileges quietly. That's why continuous monitoring is non-negotiable in any hybrid environment. Instead of relying on manual audits or periodic checks, real-time insights and automated alerts are needed to detect anomalous login attempts, unusual access patterns, or failed credential reuse before attackers gain control.
Continuous monitoring tools—such as Microsoft Defender for Cloud—offer automation and actionable reporting across multi-cloud environments. By integrating insights into tools like Power BI and maintaining unified compliance frameworks, organizations can identify configuration drift and rapidly respond to silent threats. For practical details on building continuous compliance monitoring, this guide explains the end-to-end process using Microsoft Defender and Power BI to enhance early detection and ongoing risk management.
Critical Identity Risks: Passwords, MFA, and Privileged Accounts
The security of your hybrid environment ultimately hinges on how well you manage the classic—but still vital—risks of passwords, multifactor authentication (MFA), and privileged accounts. Hybrid models bring extra challenges, as credentials and privileges span different systems that don’t always keep up with one another. Old passwords might survive unsynchronized in the cloud, or privileged accounts could fly under the radar after a staff change or failed deprovisioning task.
Attackers love to exploit these weak points. Whether it’s a poorly rotated password, a misconfigured MFA rule, or a forgotten high-risk account, the most persistent threats begin with lax identity hygiene. Modern cloud controls promise protection, but without firm policies and regular reviews, gaps will inevitably form—especially at the intersection of on-prem and cloud.
In the sections below, you’ll see how identity drift, privileged access sprawl, and half-measures in authentication can become springboards for breaches. The key is proactive defense: strong credential lifecycle management, robust and phishing-resistant MFA, and strict monitoring of all privileged roles. These practices don’t just address technical risk—they provide the discipline your hybrid identity system needs to withstand evolving attack methods.
Identity Drift and Password Staleness: How Hybrid Setups Go Stale
Identity drift is what happens when the state of your accounts and credentials gets out of sync between on-premises Active Directory and the cloud. Stale passwords and outdated credentials are especially common in hybrid environments where password hash synchronization, or regular cached credentials update, is unreliable or misconfigured.
This drift creates silent vulnerabilities. For example, a user’s on-prem password might be changed, but if that change doesn’t synchronize immediately to Entra ID, an attacker could use the old hash to access cloud resources. Orphaned or unsynchronized accounts become attractive targets because their activity isn’t tracked end-to-end. Regular credential rotation and automated synchronization mechanisms are critical in minimizing these risks.
Failures in account lifecycle management—like forgetting to disable access after staff departure, or issues with hybrid sync—can leave open doors. Detection tools should not only monitor for direct changes, but also look for unauthorized adjustments and unexplained credential reuse. You can see analogies to this issue in compliance drift within Microsoft 365 retention policies, as explored in this episode that discusses the hidden impact of drift in behavioral patterns. The message: to secure hybrid environments, you must measure, monitor, and remediate drift before it invites disaster.
Privileged Roles: Why High-Access Accounts Are Risky
Highly privileged accounts—whether service accounts, admins, or even rarely used legacy admin roles—are top targets for attackers in hybrid identity setups. The risk is amplified because these accounts can exist across both on-premises AD and cloud services, often with overlapping or poorly defined permissions.
Mismanagement is a key issue. Privileged accounts may be created for temporary tasks but never properly disabled, or they may collect excessive permissions as users change roles. Attackers use compromised privileged identities for escalation, persistence, and often for launching further attacks across the hybrid environment.
Effective security starts with rigorous application of least privilege: giving each account only the access it absolutely needs, and monitoring for privilege creep. Accountability and intentional governance are essential, as described in this discussion about the illusion of automatic governance in Microsoft 365. Without deliberate design, policy enforcement, and regular review, privileged accounts will always introduce unacceptable risk.
Strengthening MFA and Authentication Methods for Hybrid Identity
Traditional password-only approaches no longer meet the bar for hybrid identity security. Attackers easily bypass simple authentication, so deploying strong, phishing-resistant multi-factor authentication (MFA) is now critical. But just enabling MFA as a checkbox isn't enough: the methods and policy scope matter.
Modern MFA approaches in hybrid environments must accommodate on-prem users and cloud-first applications, sometimes requiring fallback protocols for legacy systems. The choice of factors—push notifications, FIDO2 hardware tokens, biometrics—can make a significant difference in attack resistance. Weaknesses in exception management or device compliance can undermine the whole system, so it's important to minimize exclusions and adopt baseline policies that protect every identity, not just the most obvious ones.
Conditional Access, when used with discipline, can enforce clear authentication journeys and limit risky sign-ins. This episode on the Conditional Access security loop provides practical strategies for reducing identity debt and achieving scalable, predictable access controls. Complementary guidance on inclusive policies and rollout planning, as shared in this detailed look at Conditional Access trust issues, rounds out the safeguards needed for hybrid authentication. Ultimately, robust MFA layered with consistent access policies is your best defense against evolving identity threats.
Monitoring, Detection, and Response in Hybrid Environments
Monitoring and incident response are foundational elements in today’s hybrid identity defense playbook. With threats moving faster and crossing boundaries between on-premises AD and cloud identity providers like Entra ID, security teams need to rethink their strategies. Traditional logs and periodic audits can’t keep pace—continuous, integrated monitoring is critical to spot and block attacks before they escalate.
The modern approach relies on signal correlation across multiple platforms, blending identity logs, audit trails, and behavioral analytics into a single risk picture. Automated policy enforcement, rather than just manual oversight, closes gaps quickly and reduces the chance for human error. This evolution is driven by more advanced attack methods—attackers now chain exploits across systems, taking advantage of overlooked signals and delayed remediation.
In the next sections, we’ll dig into practical methods for anomaly spotting, privilege misuse detection, and automated controls that act as essential guardrails. You’ll see why proactive detection and rapid response form the backbone of resilient hybrid identity security, and how aligning people and technology can dramatically reduce your organization’s risk exposure.
Monitor Hybrid Identity to Detect Anomalies and Prevent Lateral Attacks
Continuous monitoring is your best defense against attackers attempting to misuse credentials or move laterally across hybrid environments. By actively monitoring for anomalous access patterns, failed login attempts, and unusual privilege escalation, you can catch threats before they become incidents. In large, dynamic enterprises, spotting subtle behavioral changes is vital to early detection.
Telemetry sources play a huge role in building your monitoring visibility. These can include identity logs from both on-prem AD and Entra ID, cloud app analytics, conditional access events, and even endpoint signals. By correlating this data, your security operations center can establish detection guardrails that quickly highlight account misuse or credential replay attempts.
To go beyond basic reporting, you can leverage audit tools like Microsoft Purview. As explained in this practical guide on Microsoft Purview auditing, comprehensive tenant-wide logging and forensic trails enable precise tracking of user activity, support compliance needs, and empower effective incident investigation. Upgrading to premium tiers for enterprise-grade retention and richer insights is highly recommended in regulated or high-risk sectors.
Guardrails for Hybrid Identity: Automated Controls You Need to Watch
Automated policy enforcement forms the backbone of resilient hybrid identity management. By implementing automated provisioning, deprovisioning, and centralized access policies, organizations can minimize the risk of human error and configuration drift. These guardrails ensure that every change—from user onboarding to permission updates—is governed by pre-defined security rules.
Building in automation at every layer of the identity lifecycle not only strengthens security but also streamlines operational overhead. With consistent, enforceable controls, your team is freed to focus on anomaly investigation and strategy. Integrating with multi-cloud compliance frameworks enhances both visibility and agility, so you can address threats as they arise—rather than after gaps have been exploited.
Microsoft Entra ID and Hybrid Identity: Risks, Synchronization, and Hardening
Microsoft Entra ID sits at the center of most hybrid identity architectures, serving as the bridge between on-premises Active Directory and cloud-based Microsoft 365 services. While this bridge offers critical business agility and access convenience, it also introduces unique risk factors. Synchronization between AD and Entra ID, implicit permissions, and the complexity of hybrid configuration—each of these can become a source of vulnerability if not managed with care.
Synchronization, for example, isn’t just about copying accounts and passwords. It’s about making sure the right identities, privileges, and policies flow correctly in both directions—without leaving gaps attackers can exploit. Implicit permissions sometimes arise unintentionally, granting more access than intended or exposing administrative features not monitored by legacy systems.
The following sections will walk you through how these risks emerge and what hardening steps you can take for Microsoft 365 and Azure AD. Actionable guidance helps ensure you’re leveraging the best security mechanisms available and not falling into common traps that can expose your hybrid environment.
The Bridge: How Entra ID Synchronization Introduces Hidden Risks
Microsoft Entra ID Connect is the key technology enabling hybrid synchronization between on-premises AD and cloud directories. This process, however, can create unsuspected risk points. For example, when permissions are not explicitly scoped during sync setup, implicit admin or service roles might be granted by default—much broader than intended. Attackers actively look for these hidden privileges when targeting hybrid environments.
Misconfigurations in sync agents, such as using legacy protocols with weaker authentication or enabling unneeded synchronization objects, are among the top problems reported in hybrid breaches. When attackers compromise an on-prem account with hybrid sync enabled, they can seamlessly access cloud resources as that user—even if password resets or multifactor authentication are enforced later. This persistence is well documented in attacks exploiting OAuth consent and token grants, as dissected in this exploration of Entra ID OAuth consent abuse.
Real-world incidents frequently involve attackers granting themselves enduring app permissions or exploiting zombie tokens that outlive password policy changes. Strictly limiting consent rights, requiring verified publishers, and reviewing admin workflows in Entra ID are among the top ways to mitigate consent-based persistence and close the bridge to adversaries.
Hardening Microsoft 365 and Azure AD in Hybrid Setups
Securing Microsoft 365 and Azure AD in a hybrid setup means taking a layered, intentional approach to identity defense. Conditional Access should serve as your first line of enforcement—building clear, organization-wide boundaries and eliminating overbroad exclusions that create invisible risk. Periodic password audits and the proof-of-concept model help spot and resolve weak or legacy authentication methods before attackers do.
Microsoft’s own guidance around Conditional Access emphasizes a phased rollout of inclusive policies with ongoing monitoring and regular policy reviews. You’ll want to track key metrics—such as failed logins, device compliance, and risky sign-ins—to spot early warning signs. This episode on identity as a critical control plane reveals the dangers of identity "debt" and policy sprawl, while offering remediation strategies for policy lifecycle management.
Trust mismanagement and incomplete device checks have also led to major breaches. For step-by-step guidance on closing these gaps and establishing a robust Conditional Access baseline, see this comprehensive guide to trust issues in Microsoft Conditional Access. These resources underscore the point that hardening the cloud side is just as vital as shoring up on-prem foundations.
People, Training, and Organizational Roles in Hybrid Identity Security
While technology is foundational, the people who manage, use, and oversee your hybrid identity systems are at the heart of security. Even the most advanced technical controls are only as effective as the organization’s awareness, diligence, and oversight allows. Employee training addresses social engineering and phishing risks, while clear roles for administrators and executives set the tone for policy enforcement and incident response.
Getting buy-in at every level is key. End users need to understand good security habits, from identifying suspicious login prompts to complying with MFA requirements. Administrators hold the keys to both operational effectiveness and risk—if their actions or exceptions go unchecked, exposure follows. Executives must ensure resource allocation, strategic direction, and transparency around security posture, maximizing both compliance and business ROI.
Below, we break down educational, operational, and leadership responsibilities to help you build a culture of security as strong as your technical defenses. In an ever-evolving hybrid environment, it’s the combination of people and policy that defines your resilience.
The Role of Employee Training in Reducing Hybrid Identity Risk
- Phishing Awareness: Regular training sessions reduce users’ likelihood of falling for phishing scams, which are a common entry point for hybrid identity attacks. Simulated phishing campaigns and testing reinforce lessons over time.
- Security Policy Reinforcement: Employees should understand basic policies around password management, MFA use, and incident reporting. Fast, clear communication of changes reduces confusion and improves compliance at scale.
- Targeted Education: Training programs tailored to specific roles—admins, executives, or general staff—ensure knowledge gaps are filled. Regular refreshers sustain awareness, especially as threats evolve.
- Balancing Security with Usability: As shown in this discussion on building non-disruptive M365 security, user-centric security reduces friction and maintains productivity, making controls more likely to be followed.
Administrator and Executive Responsibilities for Secure, Integrated Hybrid Identity
- Administrators: Operational EnforcementAdmins are responsible for consistent application of security controls, from onboarding to auditing privileged access. They implement and monitor policies, handle incident reports, and regularly review user account hygiene across hybrid systems.
- Executives: Oversight and ResourcesExecutives ensure security strategy aligns with business goals, budget for necessary tools, and demand regular reporting on identity posture. Their support is essential for prioritizing security, especially for cross-functional or regulatory initiatives.
- Governance Boards: As explored in this podcast episode on AI risk governance, formal boards oversee risk intake and audit processes, making them the last line of defense against process and policy drift.
Preparedness, FAQs, and Next Steps for Hybrid Identity Security
The final stage of building a robust hybrid identity security program is planning for the unexpected and knowing what to do when things go wrong. Readiness means having an incident response plan tailored to hybrid identity attacks, covering the steps for containment, investigation, and recovery. It also means ensuring everyone, from IT staff to executives, can answer the big questions—how protected are we, and where should we focus next?
This section provides actionable protocols for the ‘oh no’ scenario, areas for further learning, and a concise FAQ addressing the most common doubts around hybrid security threats, MFA, Entra ID, and SaaS app vulnerabilities. As identity attacks evolve, so must your security posture—continuous improvement, employee awareness, and regular assessments all play a role.
Whether you’re just starting out or reviewing your current approach, these practical next steps and expert resources will help you maintain vigilance, minimize damage during an incident, and keep your defenses sharp in a fast-changing threat landscape.
Incident Response Planning for the ‘Oh No’ Scenario
- Preparation and Monitoring: Deploy continuous monitoring on both on-prem and cloud directories to track user activity and detect anomalies early. Leverage solutions like Microsoft Purview Audit (detailed auditing guidance here) for granular forensic visibility.
- Incident Identification: Train your team to recognize suspicious activity—such as repeated login failures, privilege escalation, or sudden changes to MFA settings. Automated alerts accelerate threat discovery before damage spreads.
- Containment: Once an incident is detected, quickly contain the breach by disabling affected accounts or revoking compromised credentials. Cloud-first deprovisioning must sync to on-prem AD to fully shut attackers out.
- Response and Remediation: Launch an investigation using audit logs and session tracking. Assess lateral movement, reset credentials, and update policies as needed to prevent recurrence.
- Business Continuity: Prioritize critical operations—segment affected systems, keep stakeholders informed, and focus on returning to business safely. Resilience-focused design limits damage and shortens recovery cycles.
Frequently Asked Questions on Hybrid Identity Security Risks
- What are the top hybrid security threats?
- Attackers target unsynchronized credentials, over-permissioned accounts, and legacy authentication that bypasses cloud policies. Consistent monitoring and policy enforcement are essential.
- How important is MFA in hybrid environments?
- MFA is critical but must be robust and phishing-resistant to prevent token theft and consent abuse. Review your MFA methods regularly for gaps.
- What role does Entra ID play in hybrid security?
- Entra ID acts as the cross-platform identity hub, but improper synchronization and implicit permissions introduce risk. Effective governance of Entra ID is key, as explained in this episode on conditional access and identity debt.
- Should I worry about SaaS applications?
- Absolutely—destination apps like Microsoft 365 often become the target after an initial compromise. Secure API integrations and monitor app consents diligently.
- What are best practices for user access?
- Enforce least privilege, automate account lifecycle management, and use conditional access with comprehensive, inclusive policies to maintain tight control on every identity.
Conclusion: Vigilance Is Paramount—Take the Next Step
Hybrid identity security isn’t a set-and-forget exercise. As threats evolve and environments grow more complex, vigilance must be your watchword. Take proactive steps—review policies, monitor for drift, and enforce strong authentication across on-prem and cloud systems. Explore trial resources, assessment tools, and expert-led content to deepen your understanding and keep defenses sharp. For more practical next steps in M365 security, see these insights on non-disruptive protection and this breakdown of governance in the AI era. Stay prepared—your next step in hybrid identity security starts now.
Third-Party and Supply Chain Identity: Overlooked Hybrid Security Gaps
Managing third-party and supply chain identities is one of the most critical—and often overlooked—challenges in hybrid security. Vendors, contractors, and SaaS applications frequently require some form of directory access, which can span from on-prem AD groups to Entra ID external users. If these accounts are over-provisioned or not tightly governed, they create persistent attack surfaces that evade typical lifecycle management processes.
Even organizations with mature internal identity controls often fail to address the risks of external users and federated partners. Persistent vendor accounts, loosely scoped federation configurations, and unmanaged app consents all introduce new pathways for attackers. When your extended identity supply chain is just as porous as your core environment, the risk multiplies—especially in regulated or highly targeted industries.
The next sections outline why strict access governance, just-in-time controls, and clear federation boundaries are essential for every organization that lets outsiders into their hybrid directory. Addressing these external gaps is as crucial as fixing your internal hybrid identity security—and may make the difference in preventing your next major breach.
The Risk of Over-Privileged Vendor and Contractor Accounts in Hybrid AD and Entra ID
External identities for vendors and contractors often outlive their intended use, creating enduring entry points into hybrid environments. Without just-in-time access provisioning or strict role-based access control (RBAC), these accounts can accumulate excessive privileges. Attackers exploit such over-provisioned accounts to gain persistence and move laterally across both on-prem and cloud systems.
Effective monitoring of these relationships is crucial. Enterprise-grade solutions should include tenant-level auditing and automation to flag risky external sharing, as detailed in this guide to external sharing risks in Microsoft 365. Closing these gaps requires ongoing review, rapid deprovisioning, and real-time visibility across all directories.
Identity Federation Pitfalls with External Partners
Poorly scoped SAML or OAuth federation with external partners can introduce significant risk into hybrid identity systems. Misconfigured trust relationships and token validation gaps might let attackers escalate privileges or spoof identities across boundaries. In real-world incidents, token-based attacks have allowed adversaries to bypass MFA and maintain long-term access.
To reduce federation-based risks, organizations need rigorous app consent governance and secure token validation processes. This in-depth review of OAuth consent vulnerabilities in Entra ID highlights how attackers abuse poorly configured integrations. Locking down consent permissions, enforcing admin oversight, and validating tokens can prevent privilege escalation and cross-domain compromises.











