Conditional Access Bypass Scenarios: Understanding and Preventing Modern Identity Threats
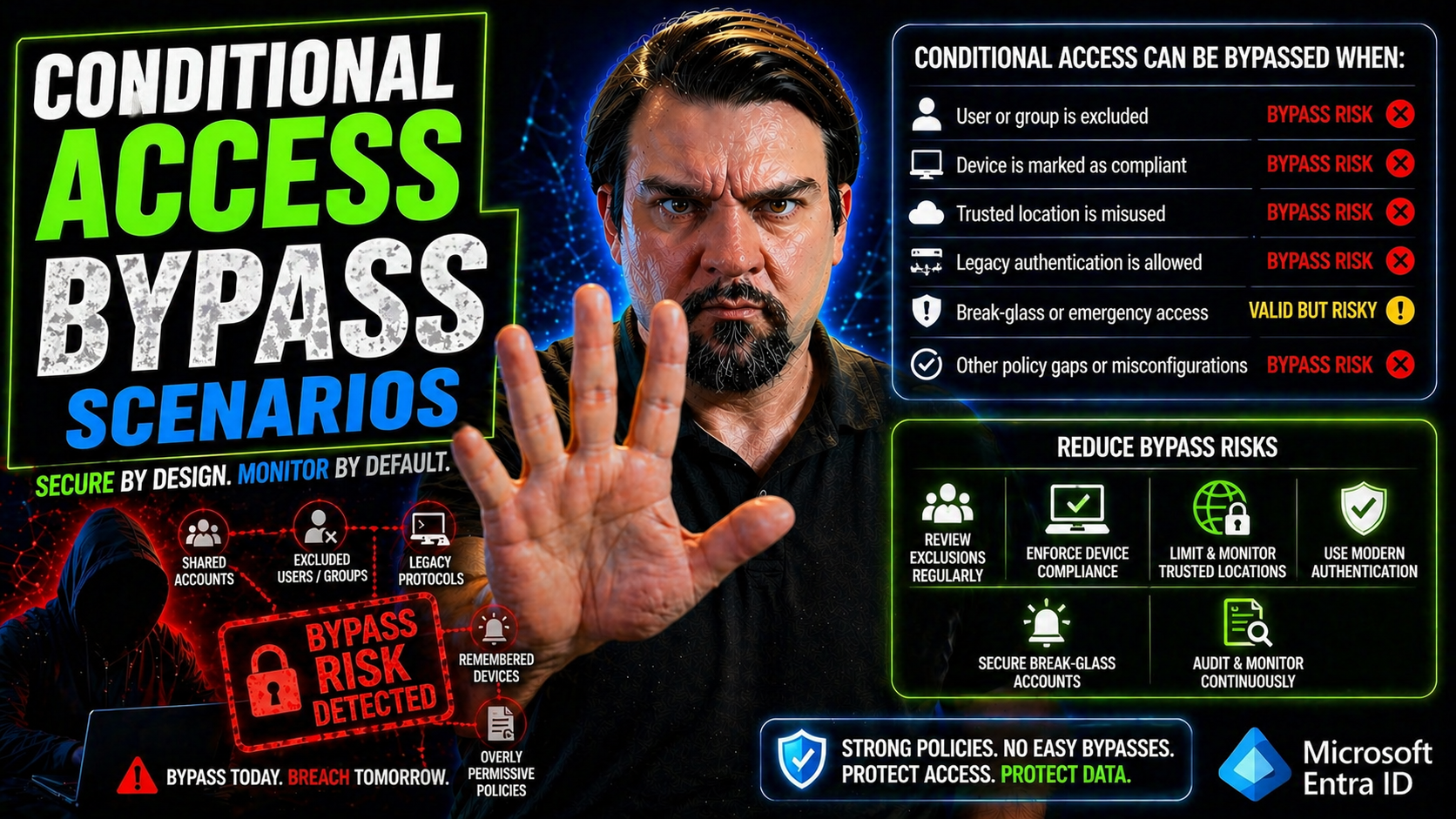
Conditional access is the front line of defense for managing who can get into your Microsoft 365 or Azure environment and under what circumstances. Whenever someone logs in or tries to access resources, conditional access policies decide if they get in, get challenged, or get blocked. This guide gives you a heads-up on how real attackers work around those policies — sometimes in ways you wouldn’t expect.
You’ll get a look at the full threat landscape, including common misconfigurations, clever attacker tricks, and advanced techniques like hybrid identity exploits. We’re not just talking theory here—expect actionable tips on detection and defense too. If you’re responsible for cloud identity, this article will show you where the cracks usually appear and how to patch them up before someone slips through.
Introduction to Conditional Access Bypass Risks and Threat Landscape
Conditional access is Microsoft’s main control gate that protects cloud identities and sensitive business data. At its heart, it lets you build rules—policies—that define who’s allowed to connect, from where, on which devices, and with what kind of security checks (like MFA or compliant hardware).
The core goal is simple: only the right people, under the right circumstances, should get access. But attackers know this too. Conditional access bypasses happen when someone finds a way to sneak around those policies. Sometimes it’s a technical loophole, other times it’s a risky decision (like excluding critical resources from checks).
These risks aren’t just theoretical. Attackers actively hunt for overlooked exclusions, misconfigured policies, and identity trust relationships ripe for abuse. In the world of Microsoft Entra ID (formerly Azure AD), access bypass can lead to breaches, data leaks, and persistent backdoors if you don’t lock things down tight.
Spotting and shutting down these bypass paths is more important than ever. You’re not just defending against password guessing, but against adversaries exploiting federation trusts, legacy services, and gaps between on-prem and cloud. Understanding the modern risk landscape will help you keep your conditional access truly conditional, and your defenses one step ahead.
How Attackers Obtain Credentials and Leverage Malicious Browser Activity
- Phishing and Social Engineering: Attackers often start with basic phishing emails or fake login pages to steal a user’s credentials. Whether it’s a clever message or just a generic “Reset your password” link, phishing is still the easiest way in.
- Password Spray and Brute Force Attacks: Sometimes, the bad guys just spray common passwords across multiple accounts, hoping for a weak link. This method checks a lot of accounts with few attempts each, to avoid lockouts and fly under the radar.
- Session Hijacking via Malicious Browsers: Advanced attackers will infect the user’s browser with extensions or malware. With their hooks in, they watch for authentication sessions, then steal security tokens right out of the browser. This lets them bypass MFA and conditional access, looking just like the legitimate user to Microsoft’s backend.
- Token Theft and Consent Phishing: Instead of traditional passwords, some campaigns use OAuth consent phishing to have the user authorize a malicious app. These apps grab permission-grant tokens, which often slip past conditional access and MFA—giving attackers persistent access without needing your password at all.
- Abusing Trust Relationships: Exploiting guest access, B2B collaboration, or legacy federated identity setups gives attackers instant legitimacy. If your policies don’t cover guest users thoroughly, attackers can ride those trust assumptions right past your access gate.
- Credential Stuffing from Data Leaks: Using usernames and passwords from recycled breaches, threat actors try them on Microsoft cloud logins, banking on password reuse. Add in a poorly maintained conditional access architecture, and this method gets dangerous fast.
Attackers blend these methods for maximum success. A phished admin account plus some browser token theft can mean full conditional access bypass, especially in environments where exceptions, legacy policies, or too much trust have crept in.
Common Misconfigurations Enabling Conditional Access Bypass
Conditional access policies are only as strong as their weakest configuration. While the technology is solid, there’s a big gap between designing airtight rules and keeping them that way. Most bypass scenarios don’t start with a fancy zero-day. They start with a boring misconfiguration, overlooked scope, or device drift.
A lot of environments develop gaps over time. Policies get exceptions, legacy groups are left out of MFA requirements, or devices are assumed to be managed but aren’t actually being checked regularly. Attackers thrive in these ambiguous zones, slipping through where enforcement isn’t consistent.
Some of the riskiest situations are tied to letting too many accounts, apps, or devices off the hook "temporarily"—and then forgetting to close the loopholes. There’s also danger in assuming device compliance equals device security. Unmanaged or misregistered devices can become Trojan horses, quietly defeating your rules from the inside out.
To get a sense of just how these loopholes open up, and why attackers love them, it’s worth looking at the common slip-ups around policy scoping, exclusions, MFA enforcement, and device management. For more on uncovering invisible security gaps, check out this deep dive on trust issues and policy drift. The next sections dig into the details behind these common pitfalls and what makes them so attractive to adversaries.
MFA Misconfigurations and Scope Bypass Risks
- Overly Broad Policy Exclusions: Accounts, groups, or applications excluded from MFA enforcement create silent gaps. Attackers know to target these exceptions, which often go unnoticed during audits.
- Non-Uniform MFA Enforcement: Policies limited to certain apps, platforms, or sign-in locations miss users operating outside those bounds. Attackers exploit these inflexible setups to gain access without triggering an MFA prompt.
- Legacy Authentication Left Enabled: Old protocols (like IMAP, POP, or SMTP) can sidestep modern conditional access—letting attackers connect with just a password. These endpoints are magnets for brute force attempts.
- Temporal or Emergency Bypass Accounts: “Break glass” admin users or temporary exclusions often get neglected once the crisis has passed. These accounts become high-value targets until properly locked down again.
For practical solutions to lock down these gaps—without crushing your user experience—see the best practices shared in this M365 security guide.
Device Compliance and Registration Vulnerabilities in Bypass Scenarios
- Unregistered Devices: Devices not registered with Intune or your company portal can often bypass device-based access checks, exposing sensitive systems.
- Compliance Drift: Even registered devices may fall out of policy compliance—due to outdated antivirus, patches, or encryption—yet still be treated as “safe” by outdated policies.
- Device Registration Workarounds: Attackers are finding creative ways to spoof or bypass device registration, especially when old methods remain enabled. Hybrid setups or incomplete Intune rollout widen the attack surface.
- Lack of Continuous Monitoring: Policies that only check compliance at sign-in, not dynamically during sessions, leave room for changes and compromise after access is granted. Learn more about real-time compliance posture at this Defender for Cloud resource.
Documented and Emerging Conditional Access Bypass Techniques in the Wild
Conditional access policy bypass isn’t just an academic concern—real attackers and security researchers are poking and prodding these systems in production daily. Some methods are documented in detail, while others emerge as new features are introduced or cloud environments grow more complex.
Two of the most dangerous categories are resource or service exclusions, and abuses of authentication flows. Exclusions—whether for legacy protocols, cloud APIs, or low-profile apps—can unintentionally act as golden keys for attackers, sidestepping your best policies entirely. At the same time, weaknesses in authentication flows, like OAuth consent or poorly controlled authorization codes, let adversaries slip in without hitting every checkpoint.
This landscape is constantly shifting as Microsoft updates features and attackers find creative loopholes. Keeping up with both the classic and cutting-edge exploits is crucial for maintaining a defense that’s not just good on paper but holds up in real-world conditions. Let’s walk through some of the most significant strategies you should recognize and guard against.
Resource Exclusion Bypass and Known Public Methods
- Legacy Auth Endpoint Exclusions: Leaving endpoints like POP3, IMAP, or SMTP AUTH out of conditional access gives attackers ripe targets. These older services often ignore MFA, letting attackers brute-force passwords without triggering modern protections.
- Graph API and App Exclusions: Conditional access often targets major user apps, but sometimes critical backend APIs (like Graph API) are unwittingly left excluded. Attackers abuse these gaps to harvest data or escalate privileges. You can see more about consent-based API attacks here.
- Non-Interactive Service Accounts: System or automation accounts with blanket exclusions from conditional access create backdoor entry points, often bypassing MFA and device checks altogether.
Reviewing policy exclusions regularly and minimizing exemptions is one of the fastest ways to close these publicized risk holes.
Abusing Authentication Flows and Claiming Authorization Codes
- OAuth2 Consent Grant Exploitation: Attackers use phishing to trick users into granting permissions to malicious apps through OAuth consent flows—often without facing conditional access or MFA. Persistent access survives credential resets. Learn more at this consent attack deep dive.
- Authorization Code Replay: By capturing or intercepting OAuth authorization codes, adversaries can claim access tokens outside of the monitored flow, sidestepping conditional access decisions at issuance time.
- Token Reuse and Replay Attacks: Stolen tokens from compromised browsers or poorly designed applications can be reused—especially if token lifetimes are overly generous—allowing access without repeated authentication or checks.
Understanding these flows keeps your defenses tight at every handoff, not just at login or consent screens.
Advanced Conditional Access Bypass: Browser Extensions and Hybrid Environment Risks
Now, let’s step into the sophisticated attack territory. As cloud access controls get sharper, so do the techniques that adversaries use. Think browser extensions quietly harvesting tokens, or attackers exploiting seams between on-premises Active Directory and cloud-based Microsoft Entra ID.
Modern attackers are no longer just guessing passwords—they’re leveraging scenarios where device, identity, and session context aren’t enforced in lockstep. Unmonitored browser plugins can carry off access tokens under the radar, while hybrid environments introduce gaps in policy enforcement (especially if ADFS or legacy federation setups are in play).
In cross-platform and hybrid setups, attackers have more windows to crawl through: weak join or sync settings, incomplete device compliance, or trust chains that aren’t uniformly protected. Protecting your org in this landscape is more than just tweaking a setting—it requires a holistic, zero-trust mindset, recognizing that identity and session boundaries can be blurred by clever, real-world attacks. Now, let’s unpack how these risks play out and what security teams need to recognize (and quickly shut down) in their own environments.
Malicious Browser Extensions and Seamless Access Execution
- Token Stealing via Extensions: Malicious browser extensions capture authentication cookies or OAuth tokens as users sign in—allowing attackers to replay valid sessions from anywhere.
- Silent MFA Bypass: Extensions operate after the user completes MFA, so attackers inherit a ‘pre-approved’ session, bypassing all conditional access and often going undetected.
- Automatic API Calls: Some malware uses extensions to automate actions directly in the browser, exfiltrating data or forwarding emails without ever needing to trigger standard access controls.
- Detection Difficulties: These attacks are tricky to spot with traditional logging, as everything looks like genuine user activity from a compliant device.
Hybrid Identity and Global Secure Access Bypass Techniques
- ADFS Bridge Exploitation: Legacy federation, like ADFS, sometimes fails to enforce cloud policy updates. Attackers passing through the bridge might avoid enforceable conditional access, especially if token rules aren’t synced tightly.
- B2B and Cross-Tenant Trust Chaining: External users or partners invited via Azure AD B2B may bypass stricter policies if guest or federated accounts aren’t held to the same standard. Attackers exploit these “trusted” relationships for lateral movement.
- Unmanaged Device Bypass: In hybrid environments, gaps in device registration, Intune compliance drift, or “trusted” OS assumptions can create routes for unmanaged endpoints to slip through.
- Cross-Platform Device Trust Issues: Policies that check only for Windows compliance may accidentally green-light access from macOS, mobile, or mixed environments—each with its own quirks and vulnerabilities. For a deep dive on achieving unified zero-trust protection, see this Zero Trust by Design resource.
Detection, Mitigation, and Remediation Strategies for Bypass Attacks
Knowing the threats is half the battle. The other half? Building and maintaining strong defenses that catch, halt, and respond to bypass attempts—preferably long before attackers reach sensitive data. It’s not just a matter of turning on a setting; it’s about ongoing vigilance and disciplined policy management.
Effective detection relies on combining security analytics, detailed logging, and a clear understanding of how traffic should look in your organization. Integrating SIEM tools, leveraging native Microsoft 365 features, and mapping to frameworks like MITRE ATT&CK can help you spot new, shifting tactics before they do damage.
On the mitigation side, organizations need a living, breathing approach to policy hardening—regularly reviewing scopes, exclusions, and device trust requirements, and automating where possible to eliminate tedious manual checks. Remediation isn’t just about fixing once, but putting controls in place so that risky changes are flagged and evaluated before they become soft spots for attackers.
The sections below will arm you with practical checklists and hunting strategies, making sure your conditional access controls aren’t just strong today but stay resilient against tomorrow’s threats, too.
Mitigation, Policy Hardening, and Securing Sensitive Data
- Regular Policy Audits: Schedule frequent reviews of conditional access policy scopes and exclusions. Identify legacy rules and overly broad leaves that have crept in over time.
- Enforce Consistent MFA: Don’t settle for partial rollout. Apply multi-factor authentication everywhere it’s supported, especially for admin accounts and third-party integrations.
- Minimize and Monitor Exceptions: Any exclusion—user, app, device—should be minimized, time-bound, and actively monitored for abuse or drift. “Set it and forget it” doesn’t work here.
- Prioritize Device Compliance: Only grant access to devices that meet current compliance standards. Use automated compliance tools to keep posture up to date and don’t just rely on initial registration.
- Data Loss Prevention (DLP) Policies: Layer your access controls with well-governed DLP strategies to limit sensitive information exposure, especially in default or collaborative environments.
- Balance Security and Usability: Avoid extremes. Achieve steady “least privilege” and adaptive policy rollouts—see practical planning advice at this user freedom vs zero trust discussion.
Threat Hunting and Detection With Graph API and Mitre Att&ck Coverage
- Leverage Microsoft Graph API Logs: Use Graph API to pull authentication, consent, and policy evaluation logs for proactive analysis and to spot irregular or bypassed events.
- SIEM Integration (Microsoft Sentinel, Splunk, etc.): Route identity, authentication, and conditional access logs to your SIEM for correlation, alerting, and forensic review.
- Map to MITRE ATT&CK Tactics: Align your detection rules and monitoring queries to MITRE’s framework, covering techniques like initial access, token theft, and lateral movement for a structured response plan.
- Audit User Activity with Purview: Microsoft Purview Audit offers tenant-wide user tracking—upgrade to premium tiers for longer retention and richer signals if handling regulated or high-risk data.
Further Research, Reading, and Documented Bypass Methods Table
Staying ahead of bypass techniques requires ongoing learning and a commitment to real-world testing. Microsoft’s official documentation is a good baseline, but threat intelligence feeds, security blogs, and public research uncover new bypass paths all the time. For a curated look at trust and policy drift challenges, visit this deep-dive discussion on overbroad exclusions and hidden drift.
Here’s a quick table summarizing some of the most prominent bypasses observed in the wild, with sources for further exploration:
- OAuth Consent Grant Abuse: Attackers gain persistence via malicious app authorization. (Read how it works)
- Legacy Authentication Gaps: Excluded IMAP/POP leads to MFA bypass and password spray risk.
- B2B/Cross-Tenant Trust Exploitation: Guest user policy misalignment opens up new lateral movement risks.
- ADFS/Hybrid Token Replay: On-prem ions or misconfigured cloud sync can create enforcement drift.
For deeper dives and continuous professional development, monitor Microsoft’s security blogs, incident reports, and emerging research publications that document new bypass routes as the threat landscape evolves.
Conclusion and Strategic Takeaways for Conditional Access Bypass Defense
Staying one step ahead of conditional access bypass isn’t about a single policy or setting—it’s about mindset, vigilance, and discipline. Attackers are innovating constantly, looking for the next forgotten exception or overlooked trust chain.
The best defense is rooted in defense-in-depth. This means layering access controls, never relying on one factor alone, and regularly revisiting policy scopes and device posture. Adaptive policies, robust monitoring, and a quick response to new threats keep your environment resilient as attack methods change.
Review your strategies often, close out “temporary” exclusions promptly, and keep an eye on new research and guidance. By treating conditional access as a living security layer—worthy of regular tune-ups—you can put real roadblocks in the way of attackers, not just speed bumps.











