Conditional Access for the Remote Workforce: Defending Modern Work from Anywhere
If there’s anything you can count on in today’s workplace, it’s that no one’s sitting in the same spot for long. Remote and hybrid work have become the new normal, unlocking a level of flexibility office folks only used to dream about. But with all this freedom comes a boatload more risk—suddenly, every kitchen table, coffee shop, and park bench could turn into a digital doorway right into your business. Pretty soon, you’re not just worrying about who’s in the office, but who’s accessing your network from a Wi-Fi hotspot three states away.
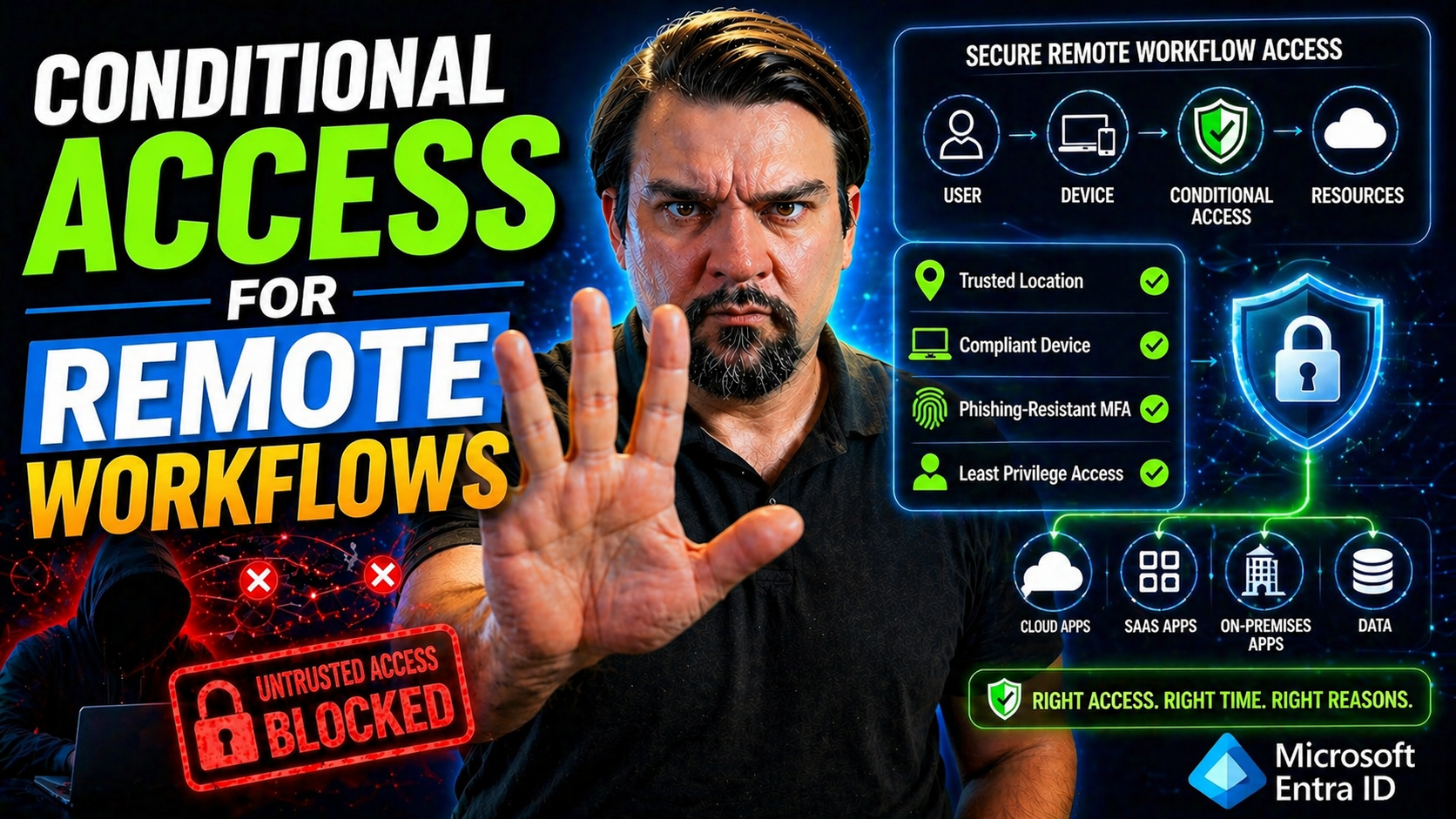
That’s where conditional access steps in as the bouncer at your company’s digital front door. It’s a living, breathing set of policies that checks every person, every device, and every location before it lets anyone peek at your sensitive resources. Whether your data lives in Microsoft 365, Azure, or a third-party SaaS app, conditional access is designed to adapt—to block what’s risky and make sure the right people get in safely, no matter where they’re working.
The rise in cloud adoption and distributed workforces has unfortunately been matched by cybercriminals who aren’t about to miss their shot. And relying solely on passwords or VPNs is like locking your car but leaving the windows down. Modern security starts with being smart about who gets access, how, and when—and making sure those rules stay consistent and predictable as your environment grows.
So whether you’re setting up your first remote-friendly policy or tightening down existing controls, conditional access isn’t just another IT checkbox. It’s the baseline for a secure, resilient organization that expects—rather than fears—the surprises remote work can bring. For practical strategies on closing gaps like token theft and device compliance, check out this discussion on improving Conditional Access trust boundaries in Microsoft 365 environments.
Understanding Conditional Access and Its Role for Remote Teams
Conditional access isn’t just a set of rules—it’s the backbone of secure, adaptive access in a world where your team could be logging in from anywhere. For remote workforces, every sign-in is a possible risk or an opportunity for business as usual. This is where conditional access comes into play, shaping how, when, and where people can tap into your company’s resources.
Picture it like a digital traffic cop, constantly scanning the situation at each moment: Who’s trying to get in? What device are they using? Are they in a safe location or somewhere they shouldn’t be? It doesn’t just let everyone in by default, and it doesn’t slam the door shut for no reason either—it weighs the risk in real time and makes smart decisions. If something feels off, extra checks kick in automatically before granting access or locking things down.
What’s game-changing for remote teams is the flexibility this brings. Conditional access can be tough when it needs to be—like blocking risky logins from an unknown device in a foreign country—but it can also be forgiving, letting trusted users glide in smoothly from managed devices at home or on the road. The real goal isn’t just to frustrate attackers; it’s to shore up defenses while still letting your people work the way they need to.
As you keep reading, you’ll dive deeper into how conditional access actually works, why it’s so essential for remote job setups, and what makes it the preferred tool for organizations protecting cloud applications, data, and people in an always-on, always-changing world. For a closer look at tightening policy design and tackling trust issues, you can check this practical guide to Conditional Access policy improvements in Microsoft 365 environments.
What Is Conditional Access and How Does It Work?
Conditional access is a security framework that decides, in real time, who gets access to which resources in your environment—and under what circumstances. Think of it as a set of always-on checkpoints that look at different factors every time someone tries to sign in or use company data. These signals might include the user’s identity, whether their device meets compliance requirements, or where they’re logging in from.
In Microsoft environments like Azure Active Directory (now Microsoft Entra ID), conditional access is enforced through policies—configurable rules that you set up. Each policy contains specific assignments (targeting users, groups, apps) and controls (actions to allow, require, or block access). When a user or device attempts to get in, these policies are triggered automatically and evaluated against the real-time context of the sign-in attempt.
Here’s the mechanics: When an employee tries to access Microsoft 365 or any cloud service, conditional access checks things like password strength, whether the device is compliant (such as meeting Intune policies), and if the sign-in location is trusted. If everything matches up to company expectations, access is granted. If not, additional steps may be required—like prompting for multi-factor authentication (MFA) or even blocking entry altogether.
Administrators can enable conditional access through the Entra ID portal, defining assignments and enforcement actions based on risk tolerance, user roles, and business needs. These policies can scale from simple (require MFA for everyone) to complex (grant access only to managed devices from known networks). The end goal? Ensuring that only the right people, on the right devices, under the right conditions, ever gain access to sensitive company resources.
How Conditional Access Strengthens Security and Embraces Zero Trust
Conditional access is central to the zero-trust security model. Instead of assuming anyone inside the network can be trusted, zero trust means trust is never assumed—period. Every access attempt is evaluated, every time. Conditional access enforces this by requiring continuous verification before anyone touches company data or systems.
Gone are the days where a username and password alone unlocked the digital gate. With conditional access, security teams can require step-up authentication, device compliance checks, or session monitoring—all based on real-time context and risk. These dynamic controls mean privileged access isn’t just handed out; it has to be earned, moment by moment.
The real advantage is flexibility. Conditional access supports the zero-trust mindset by allowing security checks to adapt as the context or risk changes. For example, a user logging in from an unfamiliar location might be required to provide MFA, while recognized, compliant users breeze through without hassle. This approach not only strengthens security trust but also reduces friction for legit users.
Industry trends are clear: Zero trust and continuous access evaluation are rapidly becoming standard, especially for organizations moving to remote work at scale. Want a deep dive into what “Zero Trust by Design” looks like in Microsoft 365 environments? Take a listen to this episode on implementing Zero Trust in Microsoft 365 or explore how to balance strict controls with user freedom in Zero Trust vs User Freedom.
Core Components: How Conditional Access Policies Protect the Remote Workforce
If you want to build an ironclad defense for the modern remote workforce, you need more than just a strong password policy. Conditional access transforms security by layering multiple signals—including who’s signing in, what device they’re on, and where they’re connecting from. Each of these components plays a unique role in making sure access is granted only under the right conditions.
Think of each signal as a filter or checkpoint. A user’s identity is checked, but that’s just the beginning. The system then inspects whether the device is compliant and managed, and if the network or location is known and trusted. By combining these checks, organizations tailor their security to match real-world risks. This is especially important when employees might be using a mix of personal and company-issued devices, connecting from all sorts of networks, or traveling between multiple locations.
Layering these components doesn’t just make attacks harder—it also ensures that legitimate users have a predictable, secure, and seamless experience. For those responsible for remote access strategies, understanding these building blocks is step one in designing, testing, and enforcing policies that protect sensitive data no matter where—or how—the workforce signs in.
Let’s break down each element in the coming sections: how we verify user identities, keep tabs on the security health of devices, and use network intelligence to keep the gates up where they need to be. By the end, you’ll have a sharper picture of how these signals work together to lock down modern work from anywhere.
Verifying User Identities and Access with MFA
- Multi-Factor Authentication (MFA) Requirement:MFA is a keystone of identity verification within conditional access. Instead of just a password, users must prove who they are with an extra step—such as a phone prompt, text code, or authenticator app. This secondary check massively reduces the chance of unauthorized access, even if passwords leak.
- Monitoring and Enforcing MFA Enrollment:Admins can track which users have registered for MFA and enforce enrollment before people get access to critical resources. Conditional access lets you require MFA for everyone or just high-risk roles, all while generating alerts if users bypass these checks or fail to meet requirements.
- Sign-In Risk Detection and Adaptive Authentication:Rather than treating every login the same, platforms like Microsoft Entra ID assess sign-in risk with AI that looks for unusual behavior (like logging in from new locations or risky devices). If sign-in risk is high, conditional access automatically triggers extra MFA or blocks access outright.
- Streamlined Exception Handling:Built-in mechanisms let trusted automations bypass MFA for certain service accounts, while policies can block or limit exceptions for most users. The goal is to keep security high without grinding productivity to a halt.
- Audit and Reporting:Conditional access tracks all MFA events and identity verifications, supporting audits and helping organizations spot suspicious patterns or compliance gaps. It’s not just about day-to-day security, but also long-term visibility and accountability.
Ensuring Device Compliance and Hybrid Joined Devices
- Device Compliance Checks:Before granting access, conditional access policies automatically verify if the device is compliant. This means checking for required encryption, antivirus, OS versions, or whether the device is jailbroken/rooted. Devices managed by tools like Intune get a thumbs-up if they match your criteria.
- Hybrid-Joined Device Validation:Hybrid-joined devices are those registered with both on-premises Active Directory and Azure AD. Conditional access recognizes these as trusted endpoints, allowing them into sensitive cloud apps if they meet all compliance standards, securing hybrid environments without slowing down access.
- Intune Policy Application:Applying Intune compliance policies ensures only healthy, managed devices get a green light. This prevents personal, unmanaged machines from accessing company data, protecting sensitive info even in bring-your-own-device (BYOD) scenarios.
- Continuous Device State Assessment:Device health isn’t checked just once—it’s reviewed every sign-in and during sessions, flagging any drift or sudden non-compliance. Conditional access can instantly block or limit access when a device drops out of compliance, preventing attacks even if things go wrong after login.
- Granular Endpoint Restrictions:Policies allow tailoring access controls down to device platforms (Windows, macOS, mobile), OS versions, or even specific encryption status. This lets businesses enforce high standards for endpoints that handle their most critical data. For a strategic lens on enforced governance by design, see Azure enterprise governance strategies.
Controlling Access by Verifying Networks and Trusted Locations
- IP Range Validation: Only allow access from corporate or known IP ranges, blocking sign-ins from risky or geofenced locations.
- Geolocation Policies: Limit access by country or region, or trigger extra checks when users log in from unexpected areas.
- Wi-Fi and Network Trust: Enforce access only from networks your company has vetted, especially when handling critical workloads.
- Adaptive Controls: Adjust requirements when users roam or move between trusted and untrusted places, maintaining security without constant disruption.
- Session Restrictions: Dynamically limit or terminate sessions started from suspicious networks, reducing risk from compromised connections.
Designing Effective Conditional Access Policies for Remote Workers
Crafting access policies for your remote team is a balancing act. You want enough security to keep threats out, but not so many hoops that your employees can’t get their work done. Today’s remote workforce brings unique challenges: devices and locations constantly change, and risk isn’t just about where someone’s logged in—it’s their behavior and the data they’re trying to reach.
Effective conditional access starts with understanding your users, devices, and typical access patterns. Granular rules—combining factors like sign-in risk, device compliance, and network type—can tailor protection to match what’s real for your business. Prioritizing risk-based controls ensures critical resources have the tightest guardrails, while less sensitive apps might get a lighter touch.
Smart organizations know it’s not enough to just turn on policies and hope for the best. Testing policies with report-only mode first can help you catch conflicts or unintended lockouts before they hit your team. And since policy sprawl happens fast in fast-moving environments, best practices like blocking outdated authentication and regular cleanup of redundant policies are just as important as any fancy technical control.
In the next few sections, you’ll see how to blend granular and risk-driven policies, safely validate changes before full rollout, and follow proven methods to keep your remote access security streamlined and effective—without adding unnecessary headaches for admins or users alike.
Combining Granular Control and Risk-Based Policies
- Layer Multiple Signals for Access Decisions:Start by combining different data points like device compliance, user risk levels, location, and sign-in risk for each access attempt. By looking at the full context, your policies adapt to both the user’s role and the risk of the moment—tightening controls when something feels off, relaxing them when everything checks out.
- Risk-Based Conditional Access:Focus resources where it matters most. For sensitive data and admin accounts, require strict measures like enforced MFA, device health, and trusted locations. Less privileged roles or common tools can have lighter touch controls but still benefit from adaptive checks.
- Dynamic Access Reviews and Machine Learning Signals:Leverage user behavior analytics to detect anomalies, like logins at odd times or new devices, and have conditional access step in with extra verification or restrictions. Integration with tools like Microsoft Purview or Defender enables near-real-time policy triggers and session controls. For practical guidance, see this approach to balancing security and usability in Microsoft 365 environments.
- Attribute-Based and Role-Based Access:Use role definitions and dynamic group memberships to set just-right access for different user types, especially for external collaborators and contractors. Attribute-based controls can even adjust policies on the fly as people move projects or change roles—no manual admin headaches required.
- Continuous Tuning and Review:Monitor conditional access policy results and adapt as threats evolve or as business needs shift. Combine policy logging with regular reviews to spot redundant rules or gaps early, fine-tuning protection without layering on complexity.
Testing Access Conditional Policies Using Report-Only Mode
Report-only mode lets you simulate conditional access policies before enforcing them. With this setting enabled, you can see which users and devices would be affected by a new or changed policy—without actually blocking anyone or forcing MFA during testing. This helps avoid accidental lockouts and catch any scope creep, so there’s no business disruption.
Admins should use report-only mode as a standard part of rollout, checking logs and reviewing impact before making enforcement live. It’s a low-risk, high-reward step for anyone looking to validate changes in dynamic remote environments. Always test, review, tweak, and only then go live with enforcement.
Best Practices: Blocking Legacy Authentication and Managing Policy Sprawl
- Block Legacy Authentication:Old protocols like SMTP, POP, and IMAP don’t support MFA, making them a prime target for attackers. Always disable legacy authentication to ensure all users are protected by modern, secure sign-in methods.
- Require Device Compliance for Sensitive Apps:Mandate compliant, managed devices for access to things like payroll, HR, and financial systems. This cuts off a broad attack avenue from unmanaged, personal devices.
- Avoid Policy Sprawl:Keep things clean and efficient by consolidating policies, using dynamic groups, and regularly retiring or updating stale rules. Excessive, overlapping policies can cause conflicts or visibility gaps—stick to a “less is more” mindset.
- Enforce MFA as a Standard:Make MFA non-negotiable for all users, not just admins. With today’s threats, it’s your most effective first line of defense.
- Regular Policy Audits:Establish a schedule to review and validate each policy—removing exemptions, tightening risky exceptions, and updating with new compliance or business requirements. For more on effective governance, see this look at why Microsoft 365 governance fails (and how to fix it).
Integrating Conditional Access with IAM and Microsoft Entra ID
Conditional access isn’t just a standalone security layer—it works best when tightly woven into your broader identity and access management (IAM) strategy. For most organizations, the hub of this integration is Microsoft Entra ID (the new Azure Active Directory), which brings centralized authentication, policy enforcement, and visibility across cloud and hybrid apps.
With robust IAM integration, companies can synchronize user directories, automate lifecycle management, and enforce policies across internal staff, contractors, vendors, and even machines. Governance capabilities, like periodic access reviews and automated offboarding, help prevent “identity debt” and stale permissions from building up—two of the biggest causes of compliance headaches and security risks.
Modern conditional access supports third-party SaaS tools and on-premises workloads through secure connectors, single sign-on (SSO), and multifactor authentication across the board. This means you maintain a consistent user experience and strong controls, regardless of where your apps or users live. And by layering in auditing, reporting, and real-time monitoring, you build an IAM security posture that’s scalable, enforceable, and ready for what’s next.
If you want to future-proof your resource access, you need a strategy that combines directory integrations, lifecycle management, access governance, and dynamic policy controls. To understand how this works from data access to lifecycle and governance, check out this walkthrough on Microsoft 365 data governance and owner accountability or learn how to eliminate risky identity sprawl in this essential episode on the Entra ID Conditional Access security loop.
Leveraging Microsoft 365, Entra ID, and Cloud Application Protection
Microsoft Entra ID (formerly Azure AD) enables conditional access across Microsoft 365, Azure, and thousands of third-party cloud apps. Through centralized policy management, it lets you enforce MFA, device compliance, and risk-based controls for both internal employees and external partners—all from one dashboard.
Integration options include SSO for SaaS applications, granular consent controls, and tenant-wide application lockdowns. Using Entra ID, organizations can protect data from OAuth grant abuse and manage consent-based threats. For tactics on defending against these risks, explore how to prevent consent-based attacks in Entra ID environments.
IAM Governance, Access Reviews, and Identity Security
- Automated Access Reviews:Schedule regular reviews to check who has access to what, prompting managers or owners to remove unneeded permissions for both employees and external users. This keeps entitlements lean and reduces accidental risk.
- Comprehensive Audit Trails:Track every access change, login event, and policy enforcement action, providing the evidence auditors and IT teams need for compliance.
- Dynamic Role Assignment:Link user access and policy assignment to roles or group membership, enabling security to adjust automatically as people move between projects, departments, or contracts.
- Behavioral Compliance Monitoring:Log and evaluate user activity beyond just access grants, focusing on behavior patterns that could indicate emerging risks. This method reveals issues traditional controls might miss. Learn more about why behavior-based compliance is crucial in explaining compliance drift in Microsoft 365.
Extending Conditional Access to Third-Party and Hybrid Workforces
- Time-Bound Access for External Users:Conditional access makes it easy to grant and automatically revoke temporary access for contractors, vendors, and guests. Policies can force expiration dates or require just-in-time approvals, reducing lingering risks after projects end. For more on guest lifecycle best practices, visit managing Microsoft 365 guest accounts.
- Role-Based and Attribute-Based Controls:Integrate RBAC or Attribute-Based Access Control (ABAC) so non-employees only get access to the specific apps and data required for their project or contract, enforcing the principle of least privilege. This limits the blast radius if a third party’s account is compromised.
- Single Sign-On and External Federation:Enable SSO across internal and external SaaS apps to deliver seamless, secure logins for third parties while retaining control. Federating with external directories preserves security boundaries without burdening admins.
- Hybrid and On-Premises Access Policies:Extend conditional access controls to cover both cloud and on-premises systems, ensuring contractors and hybrid workers pass the same checks as internal employees across any environment.
- External Sharing Governance and Auditing:Monitor and audit all external sharing and access—taking action if a guest exceeds their intended access scope, or if risky sharing occurs. Set alerts for unusual sharing activity. For advanced tactics, see auditing and controlling risky external sharing in Microsoft 365.
Securing the Remote Workforce: Strategies in Action
Security threats don’t take days off—and for distributed teams, it’s a whole new ballgame. Real-world breaches often start with credential theft, over-privileged accounts, or contractors who have more access than necessary. The art of remote security is in proactively pinpointing risks and blocking them, all while letting employees keep their edge and productivity wherever they work.
Conditional access is more than a policy engine. It’s the must-have line of defense that evolves with your threat environment, blunting the tactics of cybercriminals who prey on weak identity controls or overlooked guest and service accounts. But it’s also critical to strike a balance: too much friction, and employees look for workarounds or become less productive; too little, and you’re rolling out the red carpet for attackers.
The best strategies go beyond technical controls—layering in user behavior analytics, frequent access reviews, and a strict principle of least privilege. All the while, admins should keep watch over the full picture—making sure conditional access complements, not complicates, legitimate business workflows and user autonomy.
Up next, we’ll spotlight the main identity risks facing remote staff and show how you can use conditional access to tackle each one. You’ll also find practical, user-centric ways to maintain both security and productivity, no matter how scattered or mobile your team may be. And for the unsung hero—those non-human workload identities—find out how modern approaches are reshaping what strong zero-trust looks like in this workload identity security explainer.
Addressing Identity Risks and Conditional Access as a Must-Have Defense
- Overprovisioned Access: Employees and contractors often keep access to sensitive systems far beyond their need, raising the chances of accidental or malicious misuse. Conditional access enforces just-in-time, minimum required privileges and triggers timely reviews.
- Credential Theft: Sophisticated phishing or malware can grab user passwords. Conditional access mitigates the damage by requiring MFA and blocking high-risk sign-ins—even if the password is compromised.
- Shadow IT and Unmanaged Sharing: Apps installed outside IT’s control—or risky external sharing—can leak business data. Automated policies and integrations with tools like Microsoft Defender for Cloud Apps monitor for and block unknown OAuth scopes and external sharing. See how to tackle Shadow IT risks in Shadow IT remediation in Microsoft 365.
- Guest Access Gone Wild: Inactive or forgotten guest and contractor accounts become threats over time. Enforced expiration policies, time-based access, and periodic reviews close this gap.
Balancing Security, Principle of Least Privilege, and User Experience
- Establish a Workforce Identity Baseline:Define minimum identity verification and access controls for every user, regardless of role or location—such as always-on MFA and device compliance—as your non-negotiable starting point.
- Enforce Least Privilege by Default:Consistently apply the principle of least privilege through RBAC and ABAC, granting only the necessary permissions and immediately revoking unneeded or expired access.
- Adaptive, User-Centric MFA:Use context and risk signals to prompt for MFA only when warranted—reducing user friction and avoiding burnout from unnecessary challenges. Recognize trusted devices or regular usage patterns to streamline sign-in experiences.
- Regular Access Reviews and Self-Service Processes:Enable periodic access reviews and offer self-service tools for users to manage device and MFA enrollment, which streamlines IT workload and empowers users while maintaining security oversight.
- Continuous Data Protection Integration:Combine conditional access with governance and threat prevention tools like Microsoft Defender and Purview for layered protection without slowing business down. For more, explore this overview on ironclad security setups that don’t annoy your team.
Operationalizing Conditional Access: Monitoring and Ongoing Management
Getting conditional access up and running is only half the job. The real test is how you manage, monitor, and refine those controls day after day. Threats evolve, users change roles and locations, and your business needs may shift over time—so your access strategy must be just as agile.
Operationalizing conditional access means keeping a close eye on how policies impact the workforce. Continuous monitoring helps you spot and respond to new threats, audit logs verify compliance, and regular reviews ensure your strategies stay relevant. This isn’t just about catching breaches—it’s about proactively strengthening your environment.
Administrators also face practical, day-to-day questions: Are critical systems being protected? Are users struggling with too many prompts? Has policy sprawl introduced new gaps or conflicts? Addressing FAQs and gathering insider tips saves time and headaches by helping to demystify implementation snags before they spiral out of control.
As you look toward the future, evaluating new platforms, free trials, and feature comparisons can help maximize your organization’s investment in IAM and conditional access. To sharpen your monitoring skills, check out how to audit user activity with Microsoft Purview and review this practical guide to continuous compliance monitoring with Microsoft Defender for Cloud.
Continuous Monitoring and Auditing to Protect What Matters
- Enable Comprehensive Logging:Log every sign-in, access grant, and policy action to build an auditable record—especially for sensitive data or privileged roles. Microsoft Purview Audit delivers detailed user activity trails, from simple logons to advanced session changes.
- Automate Threat Alerts:Establish real-time alerting and automated incident response for risky behavior, suspicious sign-ins, or policy violations. Security teams stay ahead of breaches by catching threats as they unfold.
- Iterative Policy Reviews:Make policy review and tuning routine—not just a one-and-done exercise. Check for drift, dead accounts, or new business risks with regular scheduled audits.
- Integrate Compliance Monitoring:Unify security and compliance dashboards using tools like Microsoft Defender for Cloud and Power BI for a single pane of glass. This keeps business and security leaders aligned. For more tips on automation and integration, see this discussion on compliance and automation in Microsoft Defender for Cloud.
FAQs and Insider Tips for Conditional Access Implementation
- How many conditional access policies should I deploy?Start with a core baseline—usually around five to ten broad, inclusive policies. Expand or refine only as business needs evolve. Too many overlapping policies create confusion and “identity debt.”
- How do I handle emergency access or break-glass accounts?Designate at least one monitored emergency account with no conditional access restrictions, protected by strong, unique credentials and monitored for any use. Test access processes quarterly to ensure reliability.
- Can MFA prompts be reduced for regular users?Yes, adaptive authentication means trusted users and devices get fewer prompts—while risky behaviors (new device, foreign geography) require step-up verification. Always strike a balance between friction and risk.
- What are common ways attackers circumvent conditional access?Attackers exploit legacy authentication, OAuth consent grants, and unmanaged guest accounts. Audit OAuth grants and block legacy authentication to defend against these vectors. For a breakdown of OAuth consent risks, see Entra ID OAuth consent attack explained.
- Where can I get more troubleshooting help or detailed guidance?Leverage Microsoft documentation, security community forums, and in-depth podcasts or blog series—many linked throughout this guide—for targeted, actionable implementation advice.
Final Thoughts and How to Evaluate Solutions Going Forward
Conditional access isn’t a “set it and forget it” solution—it’s a living framework for defending your business as your people, data, and risks change. Prioritize platforms that offer adaptive controls, solid governance, and continuous monitoring, so your organization can tackle evolving threats without slowing down work.
Evaluate options through free trials, vendor demos, and head-to-head testing. Consider the integration of governance, role management, and data protection (including AI tools like Microsoft Copilot) in the platform you choose. For in-depth planning tips and secure rollout strategies, see this practical Copilot governance discussion at effective Copilot security and policy management.











