Conditional Access with Intune Integration: Complete Security Guide
This guide is your step-by-step roadmap to understanding, configuring, and squeezing the most out of Conditional Access with Microsoft Intune. Here, you’ll find direct answers and actionable strategies for controlling how devices and users access your organization’s resources, wherever they may be.
Whether you’re wrangling cloud-first platforms or managing a hybrid workforce, knowing how to enforce device compliance and set up flexible security policies is non-negotiable. Expect clear guidance on everything from designing policies and monitoring their effectiveness, to tackling tricky troubleshooting scenarios and integrating with both Microsoft and third-party apps.
With more organizations embracing flexible work, the stakes around identity-based security are higher than ever. This guide is designed for IT pros and security leads looking to manage risk, keep compliance tight, and support every user—on any device, in any environment.
Introduction to Conditional Access with Microsoft Intune
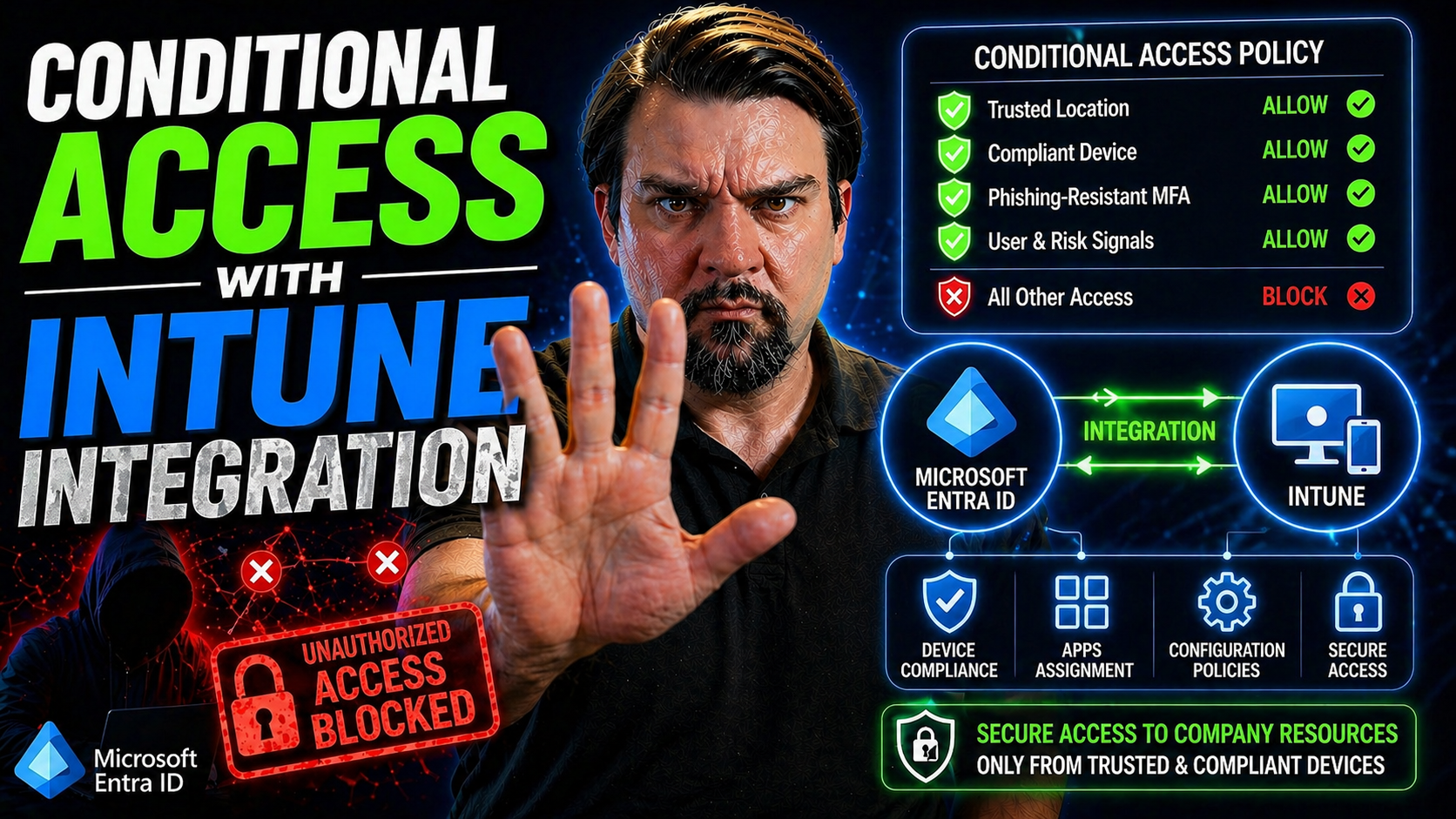
Conditional Access, in plain English, is Microsoft’s way of putting a bouncer outside your digital front door. It checks who’s knocking, what device they’re using, and where they’re signing in from before letting them inside your organization’s resources. Instead of traditional “yes or no” access, you get smart, rules-based control over who gets what, when, and how.
Microsoft Intune steps up as the device management muscle behind this operation. When you hook Intune into the picture, you’re able to set requirements—like making sure devices are encrypted, up-to-date, and not jailbroken—before they can access company data.
Organizations rely on this duo to tighten security, support remote and hybrid workers, and keep threats out without locking people down. Conditional Access doesn’t only judge users. It takes in signals like location, sign-in risk, and (especially) device compliance as reported by Intune. If a device isn’t up to snuff—say, missing patches or outside your trusted geofence—it can be blocked or challenged for additional proof, like multi-factor authentication.
This approach minimizes risky behavior, enforces compliance standards, and ensures you stay ahead of identity-based threats. It streamlines remote access, lets frontline and hybrid staff work securely, and gives admins the precision tools needed to keep pace with evolving attacks. Dive in, and you’ll soon see why Conditional Access and Intune integration are essential for modern IT environments.
How Microsoft Entra ID Powers Conditional Access Decisions
Microsoft Entra ID (previously called Azure Active Directory) sits right at the heart of Conditional Access. It acts as the ultimate gatekeeper, making the final decisions about whether a user or device gets access to your apps—cloud or on-premises—in real time.
When someone tries to log in, Entra ID gathers signals about the user, the device’s Intune compliance status, the app being accessed, and even risk information. With these details, it checks your Conditional Access rules and then decides whether to grant access, require additional proof, or block the sign-in altogether.
You’ll find real value by understanding how identity, device health, and application signals all flow into Entra ID’s policy evaluation. To explore more on managing risks like “identity debt,” layered policies, and the importance of keeping policies scalable, check out this deep-dive on identity and Conditional Access governance.
Configuring Conditional Access for Remote Access Scenarios
As remote and hybrid work becomes the new normal, organizations must address secure access for employees who are nowhere near the corporate firewalls. Conditional Access policies—especially when coupled with Intune-managed device compliance—let you strike the right balance between security and productivity, even offsite.
In this section, you’ll get an overview of how to build tailored access policies that protect sensitive resources in remote scenarios. The workflow focuses on restricting remote help features and key cloud applications so that only Intune-compliant devices can connect. This minimizes risk from unmanaged or noncompliant endpoints and keeps remote support interactions watertight.
The upcoming sections will walk through practical guidance for setting up these policies: from defining access conditions for remote assistance, to onboarding key cloud apps within Entra ID for precise targeting. Clear policies and careful cloud app selection are fundamental to supporting frontline, hybrid, and remote workforces without opening the door to compliance gaps.
To improve your Conditional Access strategies, avoid overbroad exclusions and set up an inclusive, monitored policy baseline. Learn more about building robust, trust-focused policies at this resource on Conditional Access trust issues.
Conditional Access Remote Policy Setup for Remote Help
- Identify and Scope Remote Help Needs: Start by determining which users or groups require remote assistance features (like Microsoft’s Remote Help tool). Consider both IT support staff and end users needing support, focusing on those handling sensitive information or at higher risk.
- Create a Targeted Conditional Access Policy: In the Entra ID admin center, create a new Conditional Access policy dedicated to remote help. Select the relevant user groups and scope the cloud app to the RemoteAssistanceService application to ensure the policy only applies to remote assistance flows.
- Require Device Compliance via Intune: Under access controls, select “Require device to be marked as compliant.” This ensures only devices that meet your Intune compliance standards (encryption, OS version, etc.) can initiate or receive remote help sessions.
- Add Additional Controls if Needed: For highly sensitive support scenarios, layer in additional conditions such as multi-factor authentication or requiring the sign-in to be from a trusted location or network.
- Set Up Exclusions Carefully: Exclude break-glass accounts or specific roles from the policy only when absolutely necessary. Overbroad exclusions can weaken your overall security posture, leading to policy loopholes.
- Test Policies Thoroughly: Before rolling out, use Entra ID’s What-If tool to simulate user access and validate your policy logic. This lets you catch conflicts or unintended blocks before impacting end users. For deeper insights on policy governance and avoiding “identity debt,” see this strategic podcast episode.
- Monitor and Adapt: Once live, monitor policy effectiveness using sign-in logs and Conditional Access reporting in Entra ID. Refine exclusions, review access patterns, and adjust controls based on usage and support needs to maintain security and worker productivity.
How to Import RemoteAssistanceService Cloud App in Entra ID
To apply your Conditional Access policy directly to remote help scenarios, you first need to import the RemoteAssistanceService cloud application into Microsoft Entra ID. In the Entra admin portal, go to Enterprise Applications and search for “RemoteAssistanceService.” Select and add it to your directory.
Once registered, you can assign users and target Conditional Access policies specifically to this app, ensuring that remote help features are only available to compliant, authorized devices. If you don’t see the app listed, confirm you have the latest version of Remote Help or check Microsoft’s documentation for troubleshooting onboarding issues.
Enforcing Device Compliance through Microsoft Intune
Device compliance is the backbone of secure access in a modern workplace—and Intune is the nerve center making it possible. With Intune, IT admins can define detailed compliance rules covering everything from OS version and encryption to risk posture and location.
Once set, these policies automatically check devices for compliance and keep Entra ID informed. Only devices that pass muster are seen as “trusted” and allowed through Conditional Access gates. This automated flow ensures bad actors—or unmanaged, risky endpoints—never slip in undetected.
Creating strong compliance policies isn’t a one-size-fits-all task. You might have different requirements for Windows, macOS, iOS, or Android devices based on their risk, user roles, or sensitivity of the apps in scope. The upcoming sections walk you through defining these requirements and the details of how Intune relays real-time compliance data to Entra ID, keeping your security strategy sharp and responsive.
For in-depth advice on blending these controls with other Microsoft 365 security features without frustrating users, check out this best practices guide on seamless security.
Device Compliance Policies in Microsoft Intune Explained
- Choose Device Platforms: Start by selecting which platforms—Windows, macOS, iOS/iPadOS, or Android—need compliance oversight. Intune lets you create separate policies per platform so you don’t have to compromise on standards.
- Define OS Version Requirements: Specify minimum and (if needed) maximum operating system versions. This ensures devices are patched and not running unsupported or vulnerable software.
- Set Encryption Mandates: Enforce device encryption, such as BitLocker on Windows or FileVault on macOS. Encryption is a must for protecting sensitive data if a device is lost or stolen.
- Enable Threat Protection Checks: Require Microsoft Defender or another supported threat scanner to be enabled, up-to-date, and running. This blocklist/allowlist approach helps Intune spot risky, compromised devices immediately.
- Detect Jailbreaks and Rooted Devices: Block jailbroken iPhones or rooted Androids. Such devices are more vulnerable, and compliance policies ensure they’re flagged and denied access automatically.
- Apply Additional Rules as Needed: These could include password requirements, blocking access from certain networks, or ensuring automatic updating is enabled.
- Deploy and Assign Policies: Assign your policies to device groups, user groups, or both. Bulk assignment streamlines rollout but always review the scoping before enforcing on a large fleet.
Properly configured device compliance policies form the foundation for Conditional Access. Review and update them regularly to keep pace with evolving security threats and OS updates.
Compliance Verification in Intune for Access Decisions
Microsoft Intune continuously evaluates enrolled devices against your active compliance policies. Each device checks in with Intune at regular intervals, sending up-to-date status reports reflecting its current compliance state (e.g., pass/fail per each requirement).
This compliance status is then communicated to Microsoft Entra ID in real time. When a user attempts to access a protected resource, Entra ID queries Intune to confirm the device’s status. If the device is marked compliant, Conditional Access grants access; if not, access is denied or challenged, enforcing your requirements at the gate. Accurate, up-to-the-minute compliance reporting is key to keeping your resources secure and troubleshooting access issues quickly.
Monitoring and Optimizing Conditional Access Policies
Staying in the loop on how your Conditional Access policies are performing is crucial. Microsoft Intune and Entra ID offer built-in dashboards and monitoring tools that track when and why policies are triggered, who’s getting denied, and potential compliance trends across your workforce.
Audit logs provide granular visibility into which devices met compliance, which didn’t, and the access decisions made as a result. By regularly reviewing Conditional Access triggers, compliance events, and access denials, you can spot gaps or overly restrictive rules—then fine-tune policies to balance security with end-user productivity.
Continuous monitoring, like what’s explained in this resource on automated compliance monitoring, helps prevent security drift and keeps your organization a step ahead of emerging threats.
Best Practices for Secure Access: Flexible Conditional Access Frameworks
Securing a constantly changing workforce—with their mix of devices, roles, and cloud apps—demands a robust and agile approach. Conditional Access, when paired with Intune’s device insights, lets you craft policies that support Zero Trust and future-proof your organization’s access controls.
It’s wise to structure policies that map to real-world activities and risk levels. This means leveraging role-based controls, device attributes, and application sensitivity to avoid a “one size fits nobody” approach. Flexible frameworks let you start simple (blocking access for noncompliant devices) and then layer on more nuanced conditions—like risk-based challenges, trusted location requirements, or just-in-time privilege elevation.
Modern attackers don’t care if your team works remotely or in the office, so policy agility matters. Harden your policies with continuous review and automated tools. For further design guidance and a discussion on adaptive, risk-aware access, see this Zero Trust Conditional Access podcast.
Ensuring Trusted Devices Can Seamlessly Access Corporate Resources
Make certain that only trusted, compliant devices glide through your Conditional Access gates without a hitch by applying these proven configurations. Use trusted location filters to differentiate between in-office and remote users, enabling context-aware controls. Enable Single Sign-On (SSO) for compliant devices to streamline the access experience and minimize password fatigue.
To fine-tune policy targeting, employ Conditional Access filters or device tags—this approach lets you carve out exceptions for specific device groups or user roles. When you combine these techniques, users on approved, healthy devices can access what they need, without endless prompts or disruptive hoops to jump through.
Frequently Asked Questions about Conditional Access Remote Policies and Intune
- Why is my compliant device being blocked? This usually happens if Intune hasn't synced the device status recently, there’s a mismatch in group membership, or the policy scope is off. Verify device check-in, policy assignments, and Entra ID sign-in logs to pinpoint the cause.
- How do I test policies before enforcing them? Use Entra ID’s What-If tool to simulate access attempts for specific users, devices, and apps. This tool shows which policies would apply and why, helping you spot conflicts ahead of time.
- What’s the difference between device compliance and app protection policies? Device compliance (via Intune MDM) enforces standards like encryption on the full device, while App Protection (MAM) protects data at the app level—even on unmanaged devices. Both can be paired with Conditional Access for layered security.
- Can I enforce Conditional Access on third-party SaaS apps? Yes! Register your third-party app (like Salesforce, Zoom, Dropbox) in Entra ID and target it in Conditional Access. Make sure compliance claims from Intune are used to control access.
- How often does device compliance update? Intune devices typically report compliance during regular check-ins—every 8 hours by default, or more often if manually triggered by the user or admin.
- What if users lose connectivity or go offline? Devices use cached policies, and Conditional Access allows a grace period for intermittent connectivity. Full enforcement resumes when the device next checks in.
Conclusion: Secure and Compliant Access with Microsoft Intune
Integrating Conditional Access with Microsoft Intune is a must-have for securing today’s remote and hybrid offices. By combining adaptive policy management, device compliance checks, and robust monitoring, you create an environment where only trusted users and devices reach critical resources.
Stay proactive: review and update your policies, monitor compliance status, and embrace flexible frameworks as threats evolve. If you’re looking to keep users happy without weakening defenses, check resources like this essential M365 security guide to deepen your security knowledge and keep your strategy fresh.
Author Insights and Next Steps for Microsoft Security Professionals
To keep your organization’s access management strategy sharp, it’s key to learn from experts who live and breathe Microsoft security every day. In addition to mastering Intune and Conditional Access, professionals are discovering new ways to extend these solutions across mixed device environments—and even into non-Microsoft apps and platforms.
The best pros don’t stick to basics. They dive deep into how Apple devices can be managed in harmony with Microsoft tools, using platforms like Addigy to create unified security experiences. They’re always exploring what’s next—whether that’s setting up robust policy frameworks, getting involved in content-rich communities, or learning smart ways to fill security gaps.
Stick around to get a quick look at how cross-platform strategies are transforming device management, and browse content categories spanning Microsoft security, compliance, and best practices. For guidance on preventing invisible security gaps and strengthening trust in your access policies, see this practical Conditional Access improvement guide or explore even more resources from the broader Microsoft security community.
Cross-Platform Harmony: Apple Management Transformations with Microsoft and Addigy
- Unified Management for Mixed Device Fleets: Addigy bridges the gap, allowing Intune to apply Conditional Access and compliance standards to Apple devices alongside Windows endpoints.
- Transformative Apple MDM: Enterprise organizations extend Microsoft’s reach into macOS and iOS, ensuring seamless policy enforcement, real-time monitoring, and zero-day readiness for Apple updates.
- Team-Based Controls: Role-based delegation and granular control empower IT teams to manage access, applications, and compliance at scale—no matter the device.
- Cross-Platform Harmony: Combining Microsoft and Addigy means consistent user experiences and security across iPhones, Macs, PCs, and more—all within one management framework.
Explore Content Categories for Microsoft Security, Compliance, and Device Management
- Security and Zero Trust: Delve into adaptive Conditional Access, advanced threat protection, and unified identity strategies. Stay one step ahead of cyber threats.
- Data Governance and Compliance: Learn how to leverage Microsoft Purview and policy monitoring for airtight data protection and regulatory compliance across cloud services.
- Power Platform and Enterprise Governance: See how enterprises secure rapid app development, with guidance found in this resource on Power Platform governance.
- Device Management Innovation: Explore content on MDM, Apple integrations, and best practices for managing devices in large, distributed enterprises.
- Deep Dives and Community Learning: For a curated path through essential topics, tap into these content categories and join the ongoing conversation around Microsoft security.











