Risk Signals Explained: How Modern Fraud Detection Stays Ahead
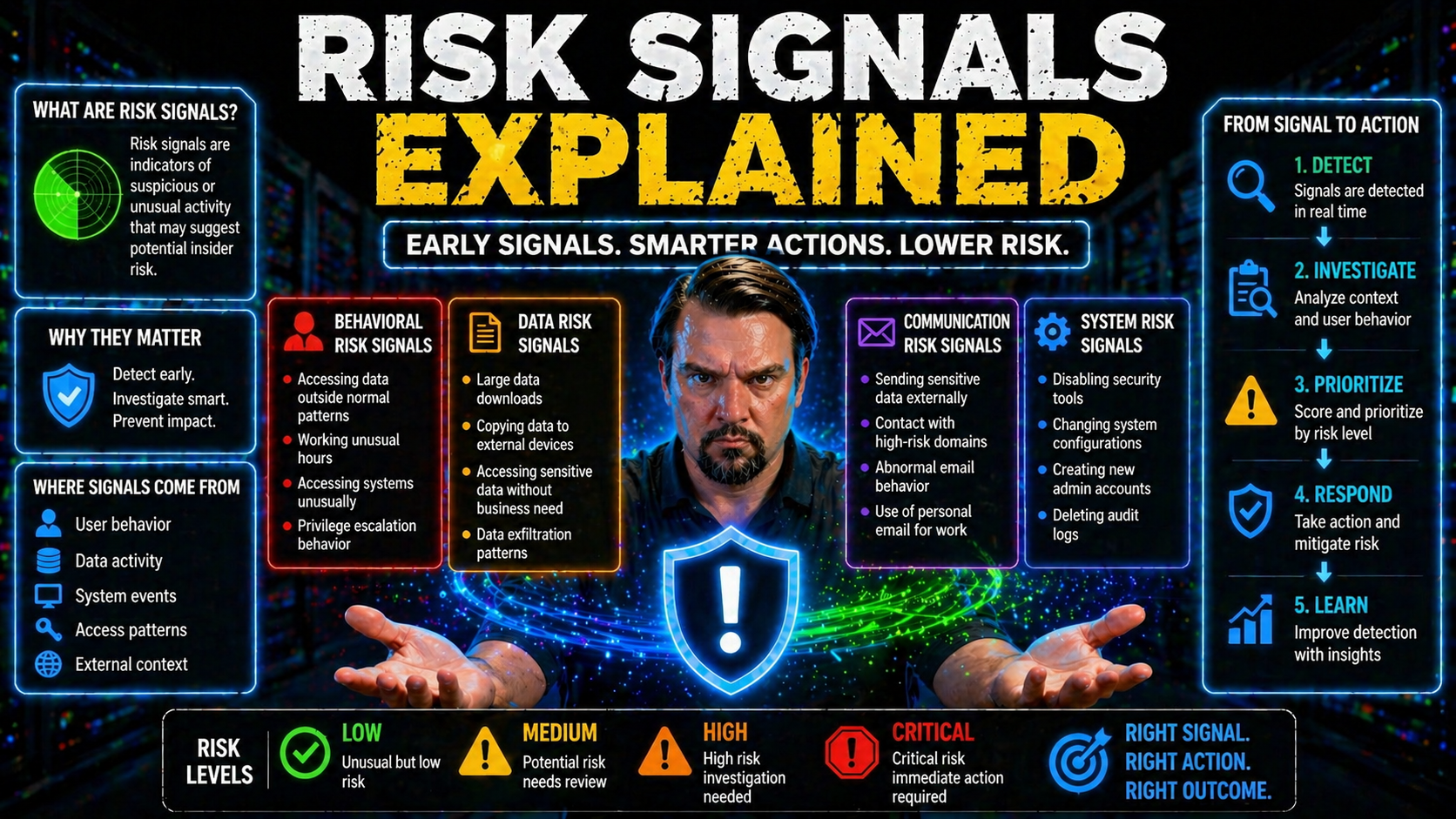
Risk signals are at the heart of how modern organizations fight fraud and keep digital environments secure. These signals come from everything you do online—whether it’s logging in, switching devices, or interacting with cloud apps like Microsoft 365. When the right data points are captured and interpreted, risk signals help businesses spot threats before they spiral out of control.
With Microsoft platforms everywhere, understanding risk signals is more than just a technical detail—it’s a non-negotiable for staying ahead of today’s evolving fraud tactics. If you can read these signals right, you can move from just cleaning up messes after the fact to stopping fraud in its tracks. This overview kicks off a deep dive into how risk signals power proactive security and why you should care.
Understanding Risk Signals and Real-Time Fraud Strategy
Risk signals represent the digital “clues” that can reveal suspicious activity long before it turns into full-blown fraud. Think of them as the early-warning system in your security stack. In a world where online threats morph daily—and bad actors get bolder—waiting to react until after fraud happens just doesn’t cut it anymore.
Organizations must now prioritize real-time fraud strategies that enable them to act on risk data as soon as it appears. This means continuously scanning for risk signals across every interaction, device, and platform. With digital landscapes like Microsoft 365 and Azure integrating everything from emails to financial transactions, there’s no room for delays or slow-footed response.
Shifting the mindset from reactive clean-up to proactive prevention has become the new baseline for enterprise security. You need to know what’s normal, spot what isn’t, and take action before risks become losses. In the following sections, you’ll see what makes up a risk signal, why real-time intelligence matters, and how adaptive systems can keep you a step ahead when fraud evolves faster than you can say “phishing attempt.”
Defining Risk Signals for Fraud Detection
A risk signal is any piece of data that hints at unusual or potentially fraudulent behavior in a digital environment. In Microsoft 365, Azure, and similar platforms, these signals might come from a login from a new device, an unexpected IP address, or even a change in user behavior patterns.
Risk signals for fraud detection build the foundation for effective threat identification, enabling automated systems to flag suspicious activities in real time. By monitoring and connecting these signals, organizations can differentiate between regular use and dangerous anomalies—making fast, accurate security decisions an everyday possibility.
Moving From Reacting Late to Acting Proactively With Real-Time Risk Strategy
- Traditional Approach: Reacting After the FactOrganizations used to rely on batch analysis or manual reviews, only investigating fraud after it occurred. By then, the damage—financial loss, data exposure, or reputational hit—was already done.
- Real-Time Risk Signals: Early Detection and ActionWith the surge in risk signals available from cloud, network, device, and user behavior, you can now spot dangerous trends and threats as they develop—not after the fact. Systems like Microsoft 365’s continuous monitoring make it possible to flag issues instantly.
- Data-Driven Fraud Prevention: Proactive vs. ReactiveOrganizations that analyze risk signals in real time can intervene before fraud happens. For example, if device signals and behavior analytics detect an account compromise, you can prompt extra authentication or lockdown access straight away.
- Continuous Learning and AdaptationReal-time risk management means your defense gets smarter over time. As fraud tactics shift—especially post-pandemic—your system learns from each new risk signal, refining its responses and detection.
- Benefits: Faster Response and Reduced LossesMaking decisions in real time slashes the window of opportunity for attackers. That means fewer security incidents progress beyond warning signs, reducing both financial and reputational harm.
Adaptive Systems and the Evolving Landscape of Fraud Tactics
Fraud tactics aren’t what they used to be—and they never stand still, especially after the pandemic pushed everyone online. Attackers adapt, finding new ways to bypass static or outdated defenses using sophisticated tools and social engineering tricks.
Adaptive, intelligent systems are now crucial for fraud prevention. Unlike old-school, rule-based setups (which fraudsters quickly outsmart), adaptive systems constantly update their threat models. They use machine learning and analytics to spot previously unseen fraud patterns, helping organizations respond dynamically instead of relying on one-and-done “fixes” that can’t keep up.
Types of Risk Signals: Passive, Active, and Behavioral Layers
Not all risk signals are created the same. Modern fraud detection weaves together several layers—passive, behavioral, and active—to form a true defense in depth. Each category plays its own role, but together they provide a much sharper lens for catching threats early (without driving users crazy with constant prompts or slowdowns).
Passive signals run quietly in the background, finding subtle clues and anomalies before anyone notices trouble. Behavioral signals come from how people interact with apps or accounts—their habits, pace, and routines. Then, when things seem off or need confirmation, active verification steps in, engaging the user directly.
A multi-tiered approach is essential because attackers are creative. The more layers you use, the harder it gets for fraud to fly under the radar. The sections ahead will break down how each signal type works and how together they create a more complete shield against ever-evolving threats.
Passive and Silent Signals in the Background
- Device Signals: Passive signals capture technical fingerprints, such as device model, browser type, and geolocation, while users operate normally. A new device or odd configuration can quietly flag higher risk—no user input needed.
- Ongoing Background Checks: Systems continuously monitor for repeat patterns—like unusual login times or session anomalies—in the background. This quiet process provides early warnings before threats escalate.
- Unobtrusive Detection: Since these signals don’t interrupt users, they let organizations identify suspicious changes quickly while legitimate users enjoy a seamless experience.
- Early Engagement: By quietly surfacing emerging risks, passive signals help teams act before a full-blown attack, reducing both the impact and scope of incidents.
Behavioral Signals and User Interaction Patterns
Behavioral signals focus on how users interact with systems. This includes typing speed, mouse movements, navigation flows, and how long sessions last. If someone suddenly types much slower, clicks in odd places, or moves through screens unpredictably, behavioral analytics may detect it as not matching their usual pattern.
These interaction patterns provide a richer context than device or network data alone. By analyzing normal versus abnormal behavior, security systems can flag actions that indicate a fraudster might have taken over the account or that a bot is in play, adding essential depth to fraud detection efforts.
Active Verification and Validating Signals Through Completion
Active verification steps up when background and behavioral signals suggest something might be off. This is when the system asks the user to do something extra—like completing a CAPTCHA, verifying a phone number, or uploading a government ID.
The move from passive monitoring to active engagement confirms identity and true intent, reducing the risk that an attacker will slip past unnoticed. Active verification is triggered only when certain risk thresholds are crossed, ensuring that escalation is used wisely and not as a routine nuisance.
Building a Robust Defense With Diverse Signal Sources
A single type of risk signal can only see so much. True fraud resilience means bringing together a range of signals from all corners of your digital environment—the device used to log in, the network it connects through, and the broader digital trail left by user activity. No one layer tells the whole story, but together, they mean much less gets missed.
Device intelligence uncovers suspicious hardware or software, network signals reveal odd locations or traffic, and digital footprint signals trace deeper relationships and histories. And that’s just the start. The power comes in joining all these signals—internally from platforms like Microsoft 365 or Azure, plus external threat feeds and fraud intelligence from outside your organization.
That’s why top organizations integrate both their own telemetry and outside intelligence engines. For Microsoft shops especially, this blend aligns with Zero Trust ideals and continuous verification models. You’ll see how each type of signal plays a critical part in the coming breakdowns, and how combining these layers gives you the strongest shield against threats. To learn more about how a Zero Trust by Design model brings unified protection across Microsoft platforms, explore further.
Device Signals and Device Intelligence in Fraud Detection
Device signals spotlight the “what” and “where” of account access. By capturing device fingerprints, IDs, and usage histories, organizations can recognize if someone’s logging in from their usual laptop or suddenly from an unfamiliar phone halfway across the globe.
Device intelligence isn’t just about hardware checks; it’s a foundation for continuous authentication and reliable risk estimation, especially across sprawling Microsoft environments. Identifying suspicious, new, or compromised devices helps teams quickly respond—before misuse becomes breach. For non-human risks, using tools like Microsoft Entra Workload Identities is key for proper device governance and auditability.
Network and Digital Footprint Signals for Stronger Detection
Network signals dig into the “how” and “from where” users connect, monitoring IP reputation, session origins, and traffic anomalies. They reveal if access requests come from risky geographies, untrusted proxies, or known malicious networks, allowing for fast threat detection even when device info looks normal.
Digital footprint signals track online history, revealing if a user’s behavior aligns with expected patterns. Layering these signals closes gaps overlooked by traditional checks. Understanding attacks like consent phishing or token theft in Microsoft 365 breach chains requires comprehensive network analysis—helping you spot threats and keep your platforms secure.
Integrating Internal and External Intelligence Engines
A robust fraud strategy combines internal telemetry—like risk signals from Microsoft 365 and Azure—with external intelligence engines that provide real-time threat data from across the cybersphere. This dual approach breaks down silos and lets security teams spot threats others might miss.
Smart intelligence engines can solve fraud challenges that older, isolated tools struggle with—automating detection, sharing insights enterprise-wide, and correlating cross-channel attacks. Want to dig deeper into how AI agents and shadow IT impact Microsoft 365 security? Explore this guide to intelligent automation and risk governance.
Reducing False Positives and Minimizing Distraction
Nothing frustrates users or security teams quite like false positives—those “guilty until proven innocent” moments when real accounts get flagged and legitimate business is blocked. While catching fraud is urgent, overzealous controls can create distractions, erode trust, and handicap productivity.
The trick is balancing pinpoint risk scoring with a smooth user experience, especially in enterprise apps and platforms like Microsoft 365. By making risk models transparent and trimming noise, you can nail high detection rates without leaving real users stranded or annoyed.
This section unpacks how reducing false positives not only makes tech teams happy (less manual review!) but keeps everyone moving along the digital highway with fewer unnecessary stops. For a guide on configuring security controls that defend without disruption, check out this practical playbook.
Transparent Risk Scoring to Reduce False Positives in Fraud Detection
Lowering false positives isn’t just about less pain for security teams—but for real, paying users too. With transparent, explainable risk scoring, security models make decisions you can trace, understand, and challenge if needed.
Explainable scoring strengthens trust on both sides of the fence: customers see fewer mistaken blocks, and organizations keep their fraud detection sharp and reliable. When you know why something was flagged, you’re much more likely to fix only what’s broken, not the whole experience.
Balancing Security and User Experience Without Adding Distraction
- Context-Aware Authentication: Only prompt for extra checks (like MFA) when risk truly calls for it, streamlining regular access for most users.
- Continuous Risk Evaluation: Use ongoing background checks to spot threats without bombarding users with constant pop-ups or interruptions.
- Smart Conditional Access: Tailor security based on user role, device trust, and session details, as detailed in this M365 security guide.
- User Feedback Loops: Allow users to appeal wrongful blocks, refining detection models without heavy-handed policies.
Technology and Analytics Powering Risk Signal Analysis
Today’s flood of risk signals can only be understood at scale with serious technology. Artificial intelligence, machine learning, and advanced analytics are now essential to make sense of thousands—even millions—of signals pouring in every minute from Microsoft-based environments and beyond.
Analytics bones up your fraud detection, especially for the tough attacks that slip right past rule-based systems. By automating the hard work—correlating data, learning from outcomes, flagging new patterns—intelligent engines deliver instant, always-on defense at the volume today’s enterprise demands.
Governance is crucial too. Without it, even the best AI systems run wild, drifting away from compliance and opening security cracks. To see how Microsoft shops keep their AI and Copilot tools aligned and controlled, check out AI agent governance best practices and explore unified analytics ecosystems with Microsoft Fabric.
AI, Essential Fraud Detection, and Analytics Strengthening Security
- Complex Attack Detection: AI spots subtle, coordinated threats beyond human reach.
- Continuous Learning: Machine learning adapts to new fraud tactics, improving over time.
- Real-Time Data Fusion: Analytics blends signals from all channels quickly, stopping emerging risks.
- Scalable Models: Automated analytics handle expanding enterprise environments with ease.
Intelligence Engines and Automated Workflows in Risk Detection
Intelligence engines orchestrate millions of risk signals, analyzing them in real-time and automating the right response—such as access controls, alerts, or escalation steps—across the Microsoft, Azure, and hybrid cloud landscape.
Automated workflows mean threats don’t linger while waiting for manual review. With the rise of shadow IT and autonomous agents in Microsoft environments, as discussed in AI agents and governance, coordinated intelligence is key to catching fraud at scale without letting exceptions slip through the cracks.
Implementing a Risk Signal Strategy and Overcoming Barriers
Developing an effective strategy for risk signals isn’t just about installing a new app or plugging in yet another dashboard. You have to start with a clear understanding of your organization’s operational rhythms and risk appetite, and then layer in the right mix of signals and controls for your unique environment, especially if you’re deep in the Microsoft stack.
Start by identifying gaps in your current fraud prevention tools and ask the tough implementation questions: How will you collect and validate signals? Who sets thresholds? What’s the right cadence for model updates and audits? Practical experience says governance is just as important as the signals themselves—without it, controls decay and exceptions pile up. You’ll want predictable, enforced policies, much like those discussed in this Azure governance strategy guide.
But watch out for common pitfalls: data silos, resistance to change, and analysis paralysis. Coordination between IT, security, and business teams is critical to make your signal strategy hum. And don’t forget training—for everyone from analysts to citizen developers using Microsoft Power Platform. For tips on balancing flexibility with control, visit Power Platform governance best practices. Overcome barriers through clear policies, shared understanding of risk, and regular tuning of your risk models to what matters most in your business.
Expert Resources, FAQs, and Next Steps
- Frequently Asked Questions: Clarify technical and business queries on integrating risk signals with Microsoft-based systems.
- Recommended Reads: For advanced compliance in Microsoft Copilot and Graph permissions, see this Copilot governance guide.
- Community and Recent Content: Stay updated and connect with others by browsing recent posts on risk and governance.
- Next Steps: Review your current signal sources, identify where automation can help, and implement small pilots before scaling up.
Compliance, Verification, and Data Quality in Risk Signal Systems
You can have the fanciest fraud detection engine in the world, but if your data isn’t verifiable and compliant, you’re asking for trouble—regulators and attackers both know where to look. Solid compliance means tying each risk signal to clear requirements—whether it’s for anti-money laundering (AML), transaction monitoring, or identity validation.
In Microsoft-heavy environments, you also need data quality frameworks to be airtight. That means making sure risk estimates come from reliable, large-enough sample sizes, with good governance to back them up. Automating compliance checks—like those highlighted in Microsoft Defender for Cloud—saves time and minimizes risk windows.
Logs, audit trails, and provenance become non-negotiables for regulated sectors, especially for forensic readiness and leadership reporting. For deep-dive auditing capabilities, see Microsoft Purview Audit guidance. As regulations keep shifting—and data gets bigger—risk signals must stay fresh, validated, and tied to precise estimation thresholds for long-term confidence in your fraud defenses.
AML Compliance, Transaction Monitoring, and Verification With Risk Signals
AML compliance depends on accurate transaction monitoring and the ability to verify user personas in real time. Risk signals—such as identity validation, transaction patterns, and anomaly detection—support regulatory reporting and spot fraudulent activity early.
By integrating AML machine learning models and maintaining valid tax controls, organizations create systems that adapt and strengthen with every new transaction. This end-to-end visibility is vital for meeting compliance standards and building comprehensive defense.
Assuring Data Quality and Setting Estimation Thresholds
Reliable fraud detection comes down to data quality and proper thresholds. This means using large, trustworthy samples—the “bedrock” of risk estimation—so your models aren’t just guessing.
Data governance ensures signals are consistently sourced, validated, and traceable, meeting both business needs and regulatory demands. Setting rational estimation thresholds streamlines risk assessment and keeps detection accurate—even as your Microsoft environment grows or regulatory frameworks such as EU VAT change. Learn more about auditable compliance in digital systems in this detailed explainer on VAT in the Digital Age.











