eDiscovery Complete Guide For Legal Teams
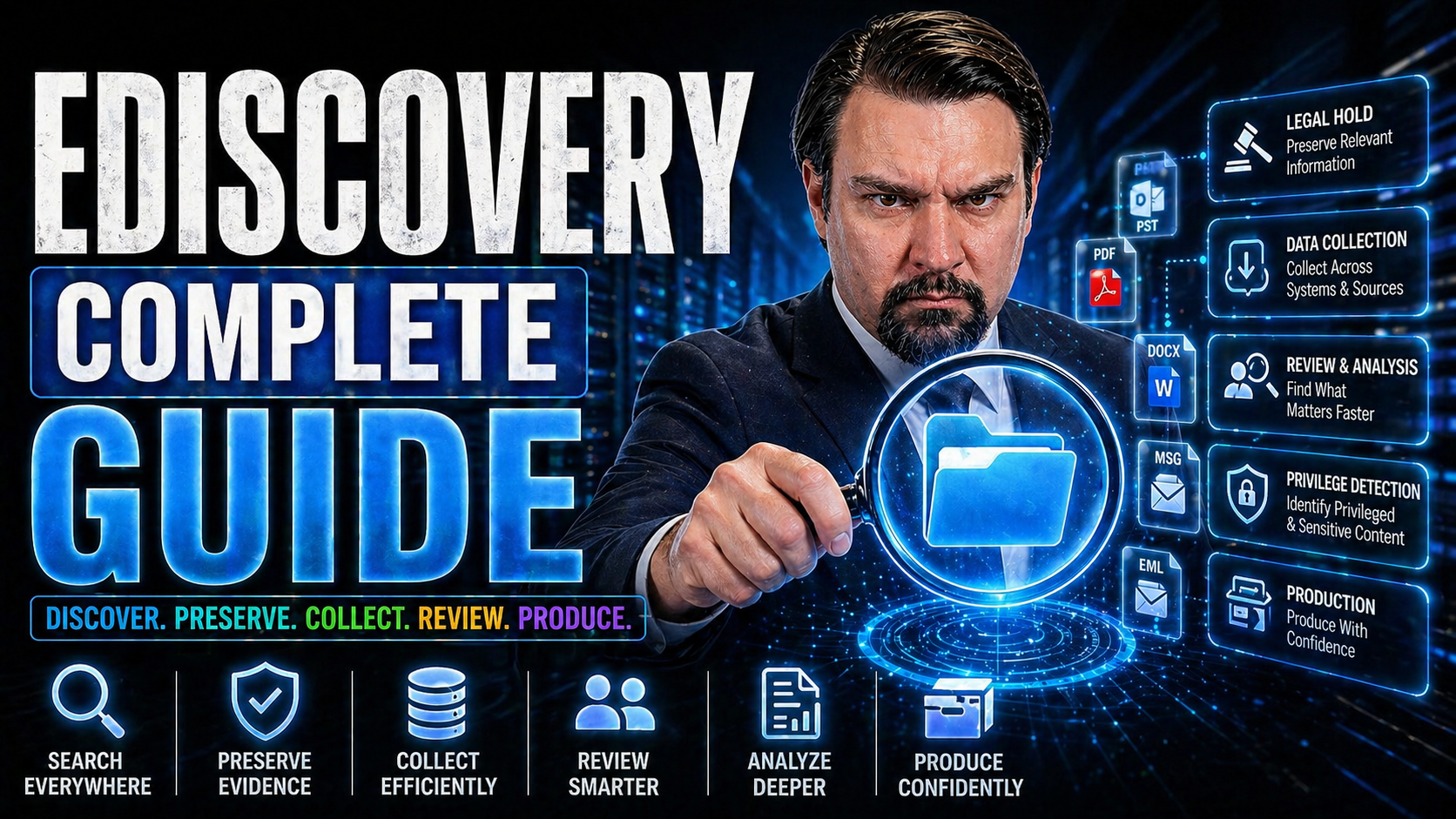
This guide gives legal professionals and organizations a comprehensive overview of eDiscovery, covering foundational concepts, practical processes, best practices, technology, compliance, and the latest trends. Readers will learn how to navigate all stages of eDiscovery, overcome common challenges, and evaluate leading solutions like Microsoft Purview. Whether you're new to eDiscovery or aiming to refine established procedures, this resource empowers you to build efficient, defensible, and future-ready digital discovery workflows.
Electronic discovery, or eDiscovery, isn't just a technical buzzword anymore—it's at the center of modern litigation, compliance, and risk management. Get ready to dig deep and get practical insight into how legal teams of all sizes can stay ahead in the fast-moving world of digital evidence and information governance.
Definition of eDiscovery
eDiscovery (electronic discovery) is the process of identifying, preserving, collecting, processing, reviewing, and producing electronically stored information (ESI) for use in legal proceedings, investigations, or regulatory matters.
Short Explanation: eDiscovery covers all steps required to handle digital evidence—from locating relevant emails, documents, databases, and multimedia across devices and cloud services, to ensuring defensible preservation and chain of custody. It combines legal strategy, technical tools, and compliance practices to reduce risk, manage large volumes of data, and deliver relevant information while protecting privileged or confidential materials. For a comprehensive overview, see the eDiscovery complete guide covering workflows, tools, best practices, and legal considerations.
9 Surprising Facts About eDiscovery
Part of any comprehensive ediscovery complete guide is understanding the unexpected realities practitioners face. Here are nine surprising facts:
- Data volume grows faster than storage expectations. Modern cases often involve terabytes of data from devices, cloud services, and IoT, making collection and review far more resource-intensive than many anticipate.
- Non-traditional sources are frequently key evidence. Chat apps, collaboration platforms, Slack threads, and ephemeral messaging can contain pivotal information not found in email or files.
- Metadata is often more valuable than document content. Timestamps, edit histories, geolocation, and access logs can prove timelines and intent even when content is ambiguous or redacted.
- Early case assessment (ECA) dramatically reduces costs when used properly. Applying targeted analytics and sampling early can narrow scope and avoid expensive full reviews.
- Privilege review still trips up many teams despite automation tools. Automated classifiers help, but human oversight is essential to avoid inadvertent disclosure of privileged materials.
- Cross-border eDiscovery faces complex legal conflicts. Data privacy laws like GDPR can restrict transfer or processing of data, forcing creative legal and technical approaches.
- Technology-assisted review (TAR) often outperforms linear review. Properly trained machine learning models can find relevant documents faster and more consistently than large manual review teams.
- Preservation over-notification can backfire. Overly broad preservation notices can create undue burden and spoliation risks; narrowly tailored holds are more defensible and practical.
- Security and chain-of-custody are increasingly scrutinized. Courts and opposing parties expect rigorous documentation and secure handling of ESI; weak practices can compromise admissibility and credibility.
Introduction to eDiscovery Foundations and Legal Significance
Before you even think about “how,” you’ve got to know “why” eDiscovery matters. At its core, eDiscovery is about managing, preserving, and producing electronic evidence—think emails, texts, documents, and databases—during legal proceedings or investigations. In today’s world, almost everything important is stored electronically. That’s why eDiscovery is no longer optional for businesses, but a legal must.
What’s driving all this? Courts and regulators expect organizations to keep digital records organized, secure, and retrievable. The rules and expectations have gotten stricter over time, so being ready for eDiscovery isn’t just about winning cases—it’s also about avoiding costly fines, sanctions, or reputational damage if you get caught unprepared.
Technology is always moving, and as it evolves, the volume and variety of data legal teams must handle grows, too. The shift to cloud platforms, collaboration tools, and mobile messaging means legal professionals must be prepared to manage electronic information everywhere it lives. That means knowing what eDiscovery is, understanding its legal roots, and grasping why it plays such a crucial role in both litigation strategy and compliance management today. The following section digs right into those fundamentals.
What is eDiscovery? Understanding Its Crucial Role
eDiscovery—short for electronic discovery—is the legal process of identifying, collecting, and producing electronically stored information (ESI) for use in lawsuits, regulatory matters, or investigations. Unlike the old-school paper discovery, eDiscovery covers emails, chat messages, documents, images, and more, all of which can make or break a case.
This practice emerged as digital communication became the norm, making ESI central to modern legal disputes. Courts require strict procedures for managing ESI to ensure evidence is accurate and trustworthy. eDiscovery’s crucial role lies in upholding fair litigation, regulatory compliance, and the resolution of business disputes in a digital age.
eDiscovery Complete Guide: Common Mistakes People Make About eDiscovery
This section of the eDiscovery complete guide outlines frequent errors organizations and legal teams make during electronic discovery and how to avoid them.
- Starting too late: Waiting until litigation or an investigation is imminent leads to rushed preservation, incomplete collections, and spoliation risks.
- Poor data preservation: Failing to issue timely litigation holds, not monitoring compliance, or allowing automatic deletions and device wipes.
- Inadequate identification of custodians and sources: Overlooking key custodians, shadow IT, mobile devices, cloud apps, and third-party systems results in missing critical evidence.
- Collecting too much data (or the wrong data): Over-collection increases costs and review time; collecting irrelevant systems or out-of-scope data creates noise and privilege risks.
- Collecting too little data: Overly narrow collections can miss responsive or adverse information and expose the organization to sanctions.
- Relying solely on manual processes: Manual preservation, collection, and review are error-prone and inefficient for large-scale eDiscovery matters.
- Poor chain of custody documentation: Failing to document collection methods, tools, timestamps, and custodial interviews undermines evidence admissibility.
- Inadequate metadata preservation: Stripping or overlooking critical metadata (timestamps, authorship, email headers) weakens context and authenticity arguments.
- Neglecting legal and compliance requirements across jurisdictions: Ignoring cross-border data transfer restrictions, privacy laws (e.g., GDPR), and local preservation obligations increases legal risk.
- Underestimating review costs and timelines: Failing to budget for review, analytics, and expert resources leads to surprises and settlement pressure.
- Misusing analytics and keyword searches: Overreliance on poorly constructed keyword lists or failing to validate search methods can miss responsive documents and produce false negatives/positives.
- Poor communication between legal, IT, and records teams: Lack of coordination causes inconsistent preservation, delayed collections, and missing data sources.
- Failing to plan for defensible processes: Not documenting standard operating procedures, protocols, and preservation/collection rationales leaves defenses vulnerable in court.
- Ignoring early case assessment (ECA): Skipping ECA prevents effective scoping, reduces use of analytics, and increases overall costs and risks.
- Poor privilege review and production controls: Inadequate privilege tagging, overproducing privileged materials, or failing to log privilege decisions can lead to waiver or sanctions.
- Neglecting security and data privacy during eDiscovery: Insecure transfers, improper access controls, and inadequate redaction expose sensitive information and regulatory risk.
- Failing to use defensible deletion and records management: Weak retention policies and inconsistent deletion practices create spoliation concerns and bloated data repositories.
- Not engaging experienced eDiscovery counsel or vendors early: Waiting too long to consult experts limits options and can increase exposure to procedural errors.
- Overlooking continuous monitoring and readiness: Treating eDiscovery as a one-time event instead of maintaining readiness and repeatable processes for future matters.
Introduction to the EDRM Framework and eDiscovery Process Phases
The Electronic Discovery Reference Model (EDRM) serves as the blueprint for handling electronic evidence in a defensible, repeatable way. Whether you’re at a big firm or a small practice, the EDRM breaks down the eDiscovery process into consecutive, logical phases everyone in the industry looks to: from identifying data all the way through presenting it in court.
Why does the EDRM matter so much? Think of it as your roadmap—helping you avoid missed steps, overlooked risks, or compliance pitfalls. Each phase of the eDiscovery lifecycle brings its own challenges and best practices: beginning with planning and data governance, moving to data identification and preservation, then diving into collection, processing, review, and ultimately, production and courtroom presentation.
Understanding this framework is essential for maintaining defensibility, showing regulators you’ve followed the right process, and keeping your legal team coordinated through every twist and turn. Up next, we’ll take a closer look at each of these critical phases, from laying the right groundwork to delivering evidence when it really counts.
Governance, Identification, and Preservation: Getting eDiscovery Right From the Start
- Develop a solid information governance policy. Set up clear policies for managing business data, including where information lives, who controls it, and how it should be handled. This proactive step helps prevent chaos down the line and shows courts you’re playing by the rules.
- Map and identify data sources and custodians. Early on, figure out all possible places your relevant data may reside—email servers, cloud drives, mobile devices, and even messaging apps. Identify key custodians (the people who own or routinely handle that data) so nothing important slips through the cracks.
- Issue and manage legal holds diligently. As soon as you reasonably anticipate litigation or an investigation, you need to send out legal hold notices to custodians. This freezes potentially relevant data, ensuring that nothing is deleted, altered, or lost—deliberately or by accident.
- Monitor compliance and defensible preservation. Keep tabs on custodians and IT to make sure the holds are actually working. Document each step, with logs and attestations if possible, so you can prove to a judge or regulator that your preservation effort was thorough and honest. This early attention to governance, identification, and preservation creates the foundation for everything else. Cut corners here and risk disaster down the line.
Collection, Processing, and Assessment: From Data Gathering to Early Case Insights
- Collect data using defensible and secure methods. Use specialized tools to extract ESI from servers, devices, cloud storage, and third-party platforms without altering metadata or file integrity. Secure, forensically sound collection keeps the evidence admissible.
- Process data efficiently to reduce volume and noise. After collection, data can be huge and messy. Use software to filter, deduplicate, and convert files to usable formats (e.g., extracting text from emails or images). Remove irrelevant system files to focus only on what matters.
- Conduct Early Case Assessment (ECA). Analyze your processed data to quickly understand potential risks, scope, and costs. ECA tools help you summarize document content, spot trends, and decide which data is actually worth reviewing or is likely to be privileged or responsive.
- Apply ESI protocols and documentation. Throughout these steps, follow any agreed ESI protocols (if you’ve got them) and keep a tight log of what you collect and process. This transparency will protect against later accusations of spoliation or missed evidence.
Review and Analysis: Document Review, Predictive Coding, and AI Advances
- Organize and prioritize document review workflows. Set up clear, logical workflows for reviewing large sets of documents. Tag files based on relevance, privilege, confidentiality, or responsiveness to the legal matter.
- Leverage advanced document analysis techniques. Use software to cluster similar documents, identify near-duplicates, and search for key terms. Automated tools help you spot hot documents and track review progress.
- Implement predictive coding and AI review technologies. Use AI and machine learning to accelerate and improve review. Predictive coding trains algorithms on samples, ranking which documents likely matter most and reducing the number of human hours needed to find responsive or privileged material.
- Safeguard against waiver of privilege and mistakes. Build review protocols that include checks for privileged or sensitive information. Automated redaction and privilege review help prevent accidental disclosure, protecting your client and keeping the process defensible.
Production and Presentation: Delivering eDiscovery Results in Court
- Format ESI according to court-accepted standards. Produce ESI in the agreed-upon or required format—native files, images, PDFs, or load files—so opposing counsel and the court can access it easily. Include any requested metadata, such as date stamps or authorship.
- Follow secure production protocols. Use secure delivery methods for transferring ESI to the opposing party or regulator, such as encrypted cloud transfers, secure FTP, or physical devices with strong security controls. Track chain of custody to avoid disputes.
- Prepare evidence for effective presentation. For court or regulatory settings, organize and label exhibits carefully (even video files or text from images) to ensure they’re clear and admissible. Work with legal technology or trial presentation specialists if needed.
- Maintain documentation to support defensibility. Keep detailed logs of how evidence was handled, formatted, transmitted, and presented. If anyone questions the process, your documentation becomes the key to defending your production’s integrity in court.
Best Practices for eDiscovery Processes and Procedures
Whether it’s your first eDiscovery project or your hundredth, having a strong set of operational best practices is what sets successful teams apart from the rest. Think of these standards as your safety net—they catch the small stuff before it becomes a crisis, helping you dodge risks, manage costs, and keep the process defensible from day one.
From drafting discovery requests and managing incoming subpoenas, to producing records that stand up in court, the right methods streamline everything. Effective communication—especially early in the process—also plays a huge role. If you haven’t talked it out with the other side, or if you neglect proportionality and cost controls, you set yourself up for battles and blown budgets.
The insights and procedures in the next sections are a practical blueprint. They draw on legal rules, industry standards, and hard-won experience to help legal teams (big or small) ensure quality, teamwork, and documented compliance every step of the way.
Essential Practices for eDiscovery Requests, Subpoenas, and Production
- Document every step of your process. Use written procedures and checklists when managing incoming discovery requests or subpoenas. This keeps details straight and ensures nothing gets missed.
- Preserve chain of custody from start to finish. Track who accesses or handles each piece of evidence, maintaining a clear and unbroken record for later review or dispute resolution.
- Check compliance requirements and deadlines early. Stay alert for production deadlines and format requirements specified by courts or opposing counsel, using reminders and shared task lists to avoid last-minute scrambles.
Communication Strategies and Proportionality Under Federal Rules
- Initiate early, proactive communication with opposing parties. Schedule a meet-and-confer session as soon as litigation is foreseeable. Early discussions help define ESI scope, deadlines, and any unique process concerns before positions harden.
- Draft and agree upon ESI protocols. These written agreements spell out how both sides will handle preservation, collection, review, and production. Clear protocols reduce confusion and argument later on.
- Apply the principle of proportionality in requests and responses. Proportionality—now required by the Federal Rules of Civil Procedure—means your discovery efforts should balance the importance of the evidence against cost and burden. Don’t overreach or spend $10,000 chasing $500 worth of data.
- Maintain thorough documentation of communication and agreements. Keep meeting notes, email threads, and draft versions of protocols. This documentation acts as insurance if disputes flare up regarding what was said or agreed.
- Share practical timelines and offer alternative solutions. If you hit a roadblock (too much data, privacy concerns, technical hiccups), communicate immediately and propose reasonable alternatives. Staying collaborative helps avoid court intervention and delays.
Technology and Tools Transforming the eDiscovery Landscape
The technology that powers eDiscovery changes fast, and what worked yesterday might not get the job done tomorrow. Staying on top of the latest tools and innovation isn’t about chasing trends—it’s about choosing the right solutions to handle growing volumes of complex, distributed data securely and efficiently.
Today’s top eDiscovery platforms aren’t just digital file cabinets. They integrate advanced analytics, robust security, and options for both cloud and on-premises deployment. Legal tech has reached a point where AI and machine learning streamline review and boost quality in ways humans alone can’t achieve.
In the next sections, you’ll get targeted advice on how to navigate a crowded eDiscovery marketplace. Learn how to prioritize features, test software hands-on, and make sense of breakthrough technologies like generative AI and Microsoft Security Copilot—all with an eye on future-proofing your legal workflows.
How to Choose eDiscovery Platforms and Software Solutions
- Evaluate leading platforms for core features. Look for secure, user-friendly interfaces; support for a broad set of ESI formats; strong review and analytics tools; and clear audit trails.
- Assess integration needs with existing systems. Make sure your eDiscovery tool connects well with your document management systems, cloud storage, and any legacy databases. Seamless integration saves plenty of time and headaches.
- Prioritize security and compliance. Check that the platform meets industry security standards, supports role-based access controls, and incorporates encryption for data at rest and in transit.
- Pilot software before full deployment. Select a few finalists and test them out with small projects. Involve end users so you don’t discover workflow “gotchas” after you’ve paid for a full rollout.
- Compare cloud-based and on-premises options. Cloud platforms offer easy scalability and remote access, while on-premises solutions may give you additional control, especially when sensitive data can’t leave your own servers.
AI, Machine Learning, and Generative AI in eDiscovery
- Accelerate document review with AI-driven workflows. Machine learning models—like predictive coding—sort and classify documents rapidly, reducing hours spent on manual review. They learn from user input to improve over time, flagging relevant or privileged files automatically.
- Increase review accuracy and consistency. AI isn’t just faster, it also reduces human errors and review fatigue. Tools can identify duplicates, detect hidden patterns, and ensure nothing critical is overlooked due to bias or oversight.
- Unlock new case insights with generative AI and analytics. Generative AI, including tools like Microsoft Security Copilot, can summarize documents, suggest key points, and even draft communications or legal memos. They help legal teams quickly get their arms around complex data sets and surface early case insights.
- Maintain regulatory and ethical compliance with AI adoption. While using AI, it’s crucial to validate outputs for defensibility. Develop checks, balances, and training to ensure algorithms don’t inadvertently breach privilege or compromise privacy. Stay current on bar guidance and court rulings on the ethical use of AI in discovery. Adopting AI is a game-changer, but safe and smart use is the only way to thrive in the evolving legal landscape.
Compliance, Risks, and Global Challenges in eDiscovery
Legal discovery doesn’t take place in a vacuum—it sits smack in the middle of complex privacy laws, global data transfers, and a world of constant business risks. Missing a key regulation or failing to lock down sensitive information can lead to regulatory penalties, reputational hits, or compromised cases.
Managing compliance in eDiscovery means weaving data privacy, security, and documentation into every step. The spread of GDPR, CCPA, and similar laws makes even local cases potentially global. Add in internal threats—accidental or not—and it’s clear why organizations need clear policies and relentless vigilance at every turn.
The following sections zoom in on how to handle data privacy requirements, practical strategies for cross-border and multilingual discovery, and what it takes to keep insider risks in check. Each phase comes with its own rules and risks—but also with proven solutions.
Data Compliance, Privacy, and Regulatory Requirements
- GDPR and global data protection laws. Handle personal data according to EU rules if you touch European subjects, including strong documentation and transfer controls.
- CCPA and U.S. privacy regulations. Know the rights California (and soon other states) give individuals to access, delete, and restrict personal data. These laws can hit you hard even if you’re not based in California.
- Industry-specific compliance (e.g., HIPAA, FINRA). If you’re in healthcare, finance, or other regulated sectors, meet sector standards for recordkeeping, breach notification, and audit readiness.
- Defensible documentation throughout the process. Document every step of handling personal and sensitive data. Keep policies, logs, and consents in order—inspectable and review-ready if the regulators come calling.
- Risk-based approach to data minimization. Limit how much personal data you collect and review. What you don’t have, you don’t need to protect, reducing your exposure in case of breach or regulatory review.
Managing Cross-Border, Multilingual, and Ephemeral Data
- Navigate international data transfer restrictions. Stay up-to-date on data transfer laws like GDPR’s restrictions, standard contractual clauses, or U.S. CLOUD Act requests. Always assess whether data you want to collect or review can lawfully cross borders.
- Implement multilingual data workflows. Use specialized software and review teams able to search, translate, and analyze ESI in various languages. Automate translation where possible to save time, but always check for nuance and accuracy with native speakers when it counts.
- Address ephemeral and mobile data sources. Don’t overlook text messages, chat apps, and collaboration tools—especially on employee-owned devices. Update policies to cover these new communication streams and ensure your collection tools are up to the job.
- Integrate global compliance controls into eDiscovery workflows. Don’t wait until the end to ask legal or IT if a data set can legally move. Build privacy, security, and regulatory checks into your collection and review from the start.
- Document all cross-border and language-specific decisions. Record your basis for moving, reviewing, or excluding data (and your translation process), so you have a defensible record ready if your choices are challenged later.
Insider Risk, Legal Holds, and Data Retention Management
- Enforce legal holds with precision. Train all staff—especially custodians—on what legal holds mean, why they’re important, and how to comply. Use technology to monitor compliance and document confirmation from employees.
- Develop comprehensive data retention policies. Align retention schedules with business, legal, and regulatory goals. Avoid keeping unnecessary data, but never delete anything under a hold or that’s relevant to foreseeable litigation.
- Educate legal teams and staff on insider risk. Regular training helps prevent accidental data loss or deliberate bad behavior. Make sure everyone understands their role in keeping evidence secure and defensible.
Leveraging Microsoft Purview for End-to-End eDiscovery
Microsoft Purview is a comprehensive platform designed to integrate information governance, regulatory compliance, and eDiscovery capabilities in one cloud-based solution. For legal teams managing ESI across Microsoft 365 and hybrid environments, Purview offers built-in tools for classifying data, issuing legal holds, and searching or reviewing content wherever it lives.
Purview streamlines the entire EDRM lifecycle. Information governance starts with automated data classification and policy enforcement, so sensitive or regulated data is always known and controlled. When litigation or investigations occur, Purview enables rapid identification of custodians, defensible preservation, targeted collection, and in-place search—all with audit trails for transparency.
AI features—including Microsoft Security Copilot—help accelerate review by summarizing documents, suggesting coding decisions, or detecting privileged information. Purview further supports production phase needs, offering export options compliant with court and regulator requirements.
Setting up Purview involves configuring compliance policies, defining retention and legal hold rules, and customizing review workflows for your legal or compliance team. Its seamless integration with other Microsoft 365 security and compliance tools minimizes risk and supports a defensible, future-ready eDiscovery posture.
eDiscovery in Small and Mid-Sized Legal Teams: Scalable Strategies for Success
For many small and mid-sized legal teams, eDiscovery feels like a high-wire act—tight budgets, minimal staff, and a need to keep up with big-firm expectations. But don’t worry, you don’t need an army of IT engineers or million-dollar platforms to run a defensible, efficient eDiscovery process.
The key is finding affordable solutions that scale to your workload and designing lean, repeatable workflows. These teams benefit most from straightforward, cloud-based tools, and practical process playbooks that make the most of limited resources. It’s about getting the job done—right size, right price, right level of complexity.
The next sections walk you through budget-friendly legal tech options suitable for small caseloads, plus actionable step-by-step checklists even the smallest teams can use to keep eDiscovery smooth, defensible, and stress-free.
Affordable eDiscovery Tools for Limited Budgets
- Cloud-based platforms with pay-as-you-go options. Solutions like Logikcull or Nextpoint offer entry-level pricing and charge by data volume, so you only pay for what you use.
- Freemium or modular eDiscovery tools. Some vendors like CaseFleet provide starter versions or modular pricing you can scale up as your needs grow.
- Microsoft Purview (with Microsoft 365 licensing). For organizations already using Microsoft 365, built-in Purview tools deliver solid eDiscovery capabilities without extra spend.
- Open-source or low-cost utilities for basic tasks. Tools like FTK Imager or bulk export scripts can help with simple collection or preservation on a shoestring budget.
Streamlined Workflows for Lean Legal Teams
- Step-by-step playbooks for key eDiscovery phases. Use prebuilt checklists to guide identification, collection, and legal hold procedures every time a new matter comes up.
- DIY document review with tagging and batching. Leverage cloud tools that allow simple, collaborative review and tagging—no full-scale document review platform required.
- Template communications for legal holds and status updates. Create and reuse standardized emails and notices, making it easy for even non-lawyers to follow protocol.
- Automated reminders and calendar tools. Use shared cloud calendars or workflow tools to track key deadlines and custodial follow-ups with the least manual chasing around.
eDiscovery Complete Guide: Purview Checklist
Use this checklist to plan and execute eDiscovery workflows in Microsoft Purview. Each item aligns with best practices for defensibility, efficiency, and compliance.
Conclusion and Resources for eDiscovery Success in 2025
Now that you’ve made it to the end of this ultimate guide to eDiscovery, take a deep breath—legal innovation isn’t for the faint of heart. The field is moving fast, with AI, generative tools, and compliance requirements making tomorrow’s eDiscovery landscape sharper, smarter, and more demanding than ever. Staying ahead means knowing how to spot trends early, getting comfortable with tech, and making smart choices for your legal team—big or small.
With regulations tightening and global communication expanding, prioritizing data privacy, risk mitigation, and efficient workflows is no longer optional. Whether your team is five strong or fifty, getting started early with streamlined processes and practical tech—like Microsoft Purview or affordable, modular tools—will save you headaches when the subpoenas start rolling in.
Don’t forget, quality eDiscovery isn’t just about ticking boxes for compliance or “good enough” productions. Measuring ROI, tracking your team’s efficiency, and clearly demonstrating results are what set standout legal teams apart. Setting a proactive training program and supporting your staff through change will help drive up adoption—no small feat, but worth every minute.
Ready to level up your eDiscovery process? Check out the downloadable resources, 101 guides, and training materials that support continuous learning. Start your next litigation project smart—plan early, request feedback from your team, and keep an eye on the tools and trends that will define eDiscovery excellence in 2025 and beyond.
Ultimate guide to ediscovery
What is eDiscovery and why is it critical in modern litigation?
eDiscovery is the process of identifying, collecting, preserving, processing, reviewing, and producing electronically stored information (ESI) relevant to a legal case. In modern ediscovery and litigation, vast amounts of data across emails, cloud platforms, mobile devices, and collaborative tools make effective ediscovery essential for meeting legal requirements, informing case strategy, and avoiding sanctions under the federal rules of civil procedure.
What are the main phases of the discovery process in eDiscovery?
The common phase of ediscovery typically includes identification, preservation (duty to preserve data), collection, processing, review, analysis, and production. Early data assessment and meet and confer process often occur early to narrow scope and costs. Modern ediscovery workflows also iterate with ongoing collection and continuous active learning during review to handle vast amounts of data efficiently.
What sources of ESI should be considered when starting eDiscovery?
Potential sources of ESI include email systems, file servers, cloud-based ediscovery platforms, collaboration tools, social media, mobile devices, backup tapes, and enterprise applications. A robust framework for ediscovery maps these potential sources of esi to preserve relevant esi and comply with legal requirements and regulatory investigations.
How does the duty to preserve data apply in eDiscovery?
The duty to preserve or duty to preserve data requires parties to take reasonable steps to prevent loss or destruction of relevant ESI once litigation is reasonably anticipated. Implementing a litigation hold and clear information governance policies ensures custodian notices, suspension of routine deletion, and documentation of preservation steps to meet ediscovery rules and avoid spoliation claims.
What are common ediscovery challenges and how can they be mitigated?
Common ediscovery challenges include managing vast amounts of data, identifying relevant ESI, cross-border data privacy issues, inconsistent custodial cooperation, and high ediscovery costs. Mitigation strategies include early data assessment, narrowing scope via meet and confer, using cloud-based ediscovery software with analytics, and following ediscovery best practices and a consistent framework for ediscovery.
How do the federal rules of civil procedure affect eDiscovery?
The federal rules of civil procedure (FRCP) set standards for preservation, proportionality, disclosure, and the meet and confer process. Parties must produce discoverable ESI, respond to discovery requests reasonably, and document privilege logs. Understanding these ediscovery rules guides preservation obligations, limitations on discovery, and motions related to spoliation or noncompliance.
What criteria should be used to choose the right ediscovery software?
Selecting the right ediscovery software depends on case complexity, sources of ESI, scalability, analytics capabilities (like clustering and continuous active learning), security, and integration with cloud-based ediscovery platforms. The right ediscovery software reduces review time, supports FRCP compliance, and helps control ediscovery costs while enabling effective ediscovery and case strategy.
When should parties engage in a meet and confer process, and what should it cover?
The meet and confer process should take place early in litigation and before extensive collection or review. It should cover scope of discovery, custodians, search terms, preservation steps (including litigation hold), timeline, format of production, and addressing proportionality and privacy concerns. Clear meet and confer communications reduce disputes and streamline the review process.
What is early data assessment and why is it important?
Early data assessment (EDA) is a rapid, initial analysis of data to estimate volume, sources, and relevance. EDA helps prioritize custodians, set realistic budgets for ediscovery costs, refine search strategies, and identify key documents to be reviewed. Conducting EDA supports proportional discovery and informed decisions about using analytics or cloud-based ediscovery software.
How can continuous active learning improve the review process?
Continuous active learning (CAL) uses iterative machine learning to rank documents by relevance based on reviewer feedback. CAL focuses reviewer effort on high-value documents, reduces review time and costs, and adapts to evolving case themes. Integrating CAL into modern ediscovery workflows enhances efficiency and supports evidence-based case strategy.
What are best practices for protecting privilege during eDiscovery?
Protecting privilege requires implementing privilege logs, using technology-assisted review to identify potentially privileged materials, applying privilege filters at collection, and documenting privilege withholding decisions. Training custodians on document handling, combining legal review with automated tagging, and clear communication during meet and confer reduce the risk of inadvertent waiver and align with protecting privilege and litigation hold obligations.
How do regulatory investigations differ from civil litigation in eDiscovery needs?
Regulatory investigations often demand rapid preservation and production, may be broader in scope regarding compliance and governance, and can involve multiple regulators with different ediscovery rules. They require fast early data assessment, cooperation with internal compliance teams, and often tighter integration with information governance and cloud-based ediscovery platforms to respond quickly while controlling costs and ensuring defensibility.
How can organizations control ediscovery costs while ensuring effective eDiscovery?
Controlling ediscovery costs involves implementing information governance to reduce unnecessary data retention, conducting early data assessment to limit scope, leveraging cloud-based ediscovery software for scalability, using analytics and continuous active learning to reduce manual review, and negotiating proportional discovery through meet and confer to focus on relevant ESI and documents to be reviewed.
What role does information governance play in a guide to eDiscovery in 2025?
Information governance is foundational to the guide to ediscovery in 2025: it streamlines data retention policies, reduces irrelevant ESI, clarifies custodial responsibilities, and enables faster preservation and collection across cloud-based platforms. Strong governance reduces ediscovery challenges, lowers costs, and ensures compliance with legal requirements as data volumes and sources expand.
How should privilege and confidentiality be handled when using cloud-based ediscovery software?
When using cloud-based ediscovery software, ensure strong encryption, access controls, audit logging, and data residency compliance. Implement privilege filters before production, maintain separate secure workspaces for privileged materials, and document chain-of-custody and privilege decisions. Combining technical safeguards with ediscovery best practices protects sensitive materials and meets legal obligations.
What are key trends shaping the field of eDiscovery and ediscovery challenges today?
Key trends include growth of cloud data and collaboration tools, AI-driven review and continuous active learning, increased regulatory scrutiny, cross-border data privacy issues, and emphasis on proportionality and cost control. These trends drive the need for modern ediscovery platforms, updated frameworks for ediscovery, and revised case strategy to manage vast amounts of data efficiently.
How do courts evaluate sanctions related to failure to preserve ESI?
Courts evaluate intent, reasonableness of preservation efforts, prejudice to the opposing party, and compliance with the duty to preserve. Documentation of litigation hold issuance, preservation actions, and meet and confer communications is critical. Adhering to ediscovery rules and following ediscovery best practices reduces the risk of sanctions for spoliation or negligence.
What should be included in a defensible collection plan?
A defensible collection plan documents custodian selection, scope, methods used for collection, chain of custody, tools (including cloud-based ediscovery platforms), and steps taken to preserve relevant ESI. It should be informed by early data assessment, align with the phase of litigation, and allow reproducibility and transparency in case of disputes over collection integrity.
How do privacy laws and cross-border data transfer concerns impact eDiscovery?
Privacy laws and cross-border restrictions can limit collection and production of ESI, requiring data localization, redaction, or use of data processing agreements. Parties must balance legal requirements with ediscovery obligations, engage privacy and IT teams early, and consider targeted collections or negotiated protocols during the meet and confer process to address regulatory investigations and privacy constraints.
What metrics should legal teams track to measure eDiscovery effectiveness?
Track metrics such as review velocity, percent likely responsive, cost per document reviewed, time to first production, volumes collected versus produced, results of early data assessment, and model precision for continuous active learning. These metrics inform case strategy, reveal bottlenecks, and justify investments in ediscovery software and cloud-based ediscovery solutions to improve outcomes.
How can in-house counsel prepare for eDiscovery before a legal case arises?
In-house counsel should implement information governance, create litigation hold templates, identify potential sources of ESI, train custodians, and establish relationships with ediscovery software vendors. Proactive policies, routine data mapping, and regular readiness exercises reduce response time and ediscovery costs when a legal case or regulatory investigation arises.
What role does technology-assisted review play in ensuring quality control?
Technology-assisted review, including continuous active learning and predictive coding, enhances quality control by prioritizing documents for review, reducing human error, and providing reproducible, defensible sampling metrics. Combined with human review for nuanced privilege or context determinations, TAR supports efficiency and defensibility in the review process.
How should teams approach producing data and meeting format requirements?
Teams should clarify production formats during the meet and confer process, comply with court orders and ediscovery rules, and use standardized load files, native files, or image formats as agreed. Metadata preservation, Bates stamping, and documentation of redactions are essential. Cloud-based ediscovery platforms can automate export and production workflows to meet specifications reliably.
How can small firms or teams access modern ediscovery capabilities affordably?
Small firms can use cloud-based ediscovery software with subscription pricing, leverage vendor-hosted platforms for scalability, perform targeted early data assessment to limit scope, and adopt analytics and continuous active learning to reduce manual review. Outsourcing parts of the discovery process or using phased engagement models helps control ediscovery costs while accessing modern ediscovery features.











